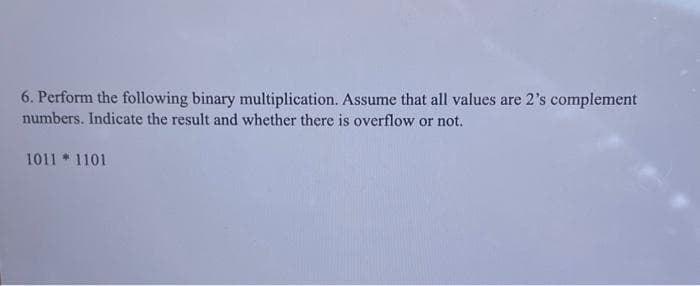
6. Perform the following binary multiplication. Assume that all values are 2's complement numbers. Indicate the result and whether there is overflow or not. 1011 1101
Q: ate a Python program that implements the following functionalities: Ensure the existence of a file…
A: Initialize class with a default filename.In a method, generate 100 random numbers and write them to…
Q: Explain the concept of the OSI model and how it relates to network protocols. Name the seven layers…
A: The OSI (Open Systems Interconnection) model is a framework used to understand and standardize the…
Q: Explain the challenges and solutions for achieving high performance and low overhead in virtualized…
A: In today’s computing landscape virtualized environments play a role by enabling the operation of…
Q: What is hypervisor virtualization, and how does it relate to the concept of virtual machines (VMs)?
A: Hypervisor virtualization, also known as virtualization technology, is a foundational concept in the…
Q: Prepare a UML diagram for register a customer complaint. prepare a UML diagram for canceling a…
A: The Unified Modeling Language (UML) is a standardized visual modeling language used in software…
Q: Martha Stewart trial: BNBPPKZAVQZLBJ The prosecution team was well aware that Martha is fond of the…
A: The encrypted message "BNBPPKZAVQZLBJ" and the provided information about Martha Stewart's public…
Q: What are some key performance indicators (KPIs) to assess the success of an outsourced website…
A: Web development is also known as website development which involves creating, building and…
Q: What are the benefits and challenges of hardware virtualization in server environments?
A: Hardware virtualization in server environments involves running multiple virtual machines (VMs) on a…
Q: Discuss the challenges and security considerations associated with virtualization and how they can…
A: Virtualization technology has revolutionized IT infrastructure, offering flexibility and efficiency.…
Q: Discuss the concept of thread safety and the challenges associated with writing thread-safe code in…
A: In concurrent programming, where numerous threads or processes operate in parallel and may access…
Q: Discuss the benefits and challenges of using virtualization in cloud computing environments.
A: Virtualization is a technology that plays a role in cloud computing environments.It allows for the…
Q: What are the advantages of using threads in a multi-threaded application?
A: "Threads" are the smallest units of execution that an operating system may arrange and carry out for…
Q: Explain the concept of HTTP (Hypertext Transfer Protocol) and its role in web communication.
A: HTTP (Hypertext Transfer Protocol) is a fundamental protocol in computer networking that forms the…
Q: (b) Provide examples of pointer declaration, assignment, and initialization in the segments below.…
A: Algorithm: Pointer Declaration, Assignment, and Initialization1. Start2. Declare a float variable…
Q: Given the following graph, please build an MST. The language is Java.
A: A minimal spanning tree (MST) of a connected, undirected graph is a subset of the edges that…
Q: Computer ethics question: Let's assume CSULB has a student retention department that keeps track of…
A: Data science practice is the systematic and multidisciplinary approach to extracting insights,…
Q: What is the fundamental concept of a thread in computer science and how does it differ from a…
A: Thread:A thread, in the context of computer science, is the smallest unit of execution within a…
Q: Given this imperative Python snippet, please re-write it to be more functional: people = [{'name':…
A: Here's the algorithm for the code that calculates the average height of people with recorded heights…
Q: Computer ethics question: An amber alert is activated in your hometown (this is when a child…
A: In the world of data science and ethics, the scenario you presented involving an Amber Alert is a…
Q: How does virtualization technology work, and what are the different types of virtualization (e.g.,…
A: Virtualization technology is a crucial concept in the world of computing, enabling multiple virtual…
Q: Explore the challenges and solutions related to live migration of virtual machines in a virtualized…
A: Virtualization is a technology that enables the creation of a virtual (rather than actual) version…
Q: Explore the concept of virtual networks and their role in virtualized environments.
A: In the world of computer science and IT infrastructure, virtual networks play a role in virtualized…
Q: How does multithreading relate to parallelism, and what are the benefits of parallel execution using…
A: Within the field of computer science and software development, parallelism and multithreading are…
Q: Define the concept of the Internet Protocol (IP). What role does it play in computer networking, and…
A: The Internet Protocol (IP) is a fundamental arrangement of decisions and shows that oversees the…
Q: How does the operating system manage threads in a multi-threaded application
A: In step 2, I have provided complete answer to the question...
Q: inter-thread
A: In multi-threaded programming, inter-thread communication and synchronization are essential to…
Q: Using the priority list T2, T3, T7, T6, T₁, T4, T5, schedule the project below with two processors.…
A: Scheduling tasks is a fundamental concept in computer science that involves assigning them to…
Q: Define virtualization and describe its fundamental principles, including the concept of a virtual…
A: Virtualization is a game-changing technology that has completely changed how we allocate and control…
Q: Define virtualization and its significance in modern computing.
A: Virtualization :It is a technology that allows multiple virtual instances to run on a single…
Q: Explain the Second Normal Form (2NF) and how it relates to the concept of partial dependencies in a…
A: Relational databases aim for the Second Normal Form (2 NF) in order to minimize data redundancy and…
Q: Discuss the significance of routing protocols in the operation of the Internet and networking.
A: Routing protocols are of paramount significance in the operation of the Internet and networking.…
Q: Describe the User Datagram Protocol (UDP) and its advantages over TCP in certain scenarios.
A: User Datagram Protocol (UDP) stands as a fundamental transport layer protocol in computer…
Q: Describe the OSI (Open Systems Interconnection) model and its role in understanding the layering of…
A: The OSI (Open Systems Interconnection) model is a conceptual framework. The OSI model standardizes…
Q: Discuss emerging network protocols and technologies, such as IPv6, MQTT, and HTTP/2, and their…
A: In the ever-evolving landscape of networking and communication, emerging and cutting-edge network…
Q: Describe the benefits of hardware virtualization for server consolidation and resource optimization.
A: A technique known as hardware virtualization enables the operation of several virtual machines (VMs)…
Q: What are the challenges of debugging and detecting race conditions in multithreaded applications,…
A: Debugging and detecting race conditions in multi threaded applications can be quite challenging, for…
Q: Construct a PDA that simulates
A: Given the context-free grammarS -> aB | bAA -> aS | bAA | aB -> bS | aBB | b
Q: Describe the relationship between threads and CPU cores. How can you utilize multiple CPU cores…
A: The relationship between threads and CPU cores is a fundamental concept in the field of parallel…
Q: Explain the concept of the OSI model and how it categorizes various network protocols into seven…
A: The OSI (Open Systems Interconnection) model is a framework that organizes the functions of a…
Q: Describe the basic attributes of a thread, such as thread ID and thread state.
A: Threads serve as the core units of execution in multi-threaded applications, enabling concurrent…
Q: True Or False: P->(QVR) equivalent to Pn~Q -> R Notes from Student: For P->(QvR) equivalent to…
A: Equivalent denotes the same in terms of value, function, etc. In mathematics, equivalent numbers are…
Q: What is the OSI model, and how does it relate to the concept of network protocols? Briefly explain…
A: The Open Systems Interconnection (OSI) model serves as a fundamental framework in the field of…
Q: Describe the role of containerization in virtualization and compare it to traditional…
A: Virtualization refers to the process of creating a virtual representation, rather than an actual…
Q: Operating a robot without the use of a teach pendant via a computer using Fanuc software to have the…
A: High levels of automation and precision can be achieved in a variety of applications by controlling…
Q: Explore the concept of nested virtualization and its use cases. What are the challenges and…
A: Nested virtualization is a technology that allows us to run machines (VMs), inside other VMs.It…
Q: Discuss the concept of thread priority and how it influences thread execution in a multi-threaded…
A: In this question we have to understand about the concept of thread priority and how it influences…
Q: Explain the advantages of using threads in concurrent programming.
A: Concurrent programming uses threads, which help build reliable, responsive, and scalable software…
Q: What is live migration in virtualization, and what are the challenges associated with it?
A: Migration in virtualization is the process of shifting a running virtual machine (VM) from one…
Q: How do threads help improve the performance of a multi-core processor?
A: Threads are essential in computer science and operating systems, optimising multi-core processor…
Q: Discuss the evolution of computer architectures from the early mainframes to modern microprocessors.
A: The journey of computer architecture throughout history is truly captivating as it has significantly…
Note:-
sign extend
Please refrain from offering handwritten solutions. Please ensure that your response maintains accuracy and quality to avoid receiving a downvote.
Take care of plagiarism.
Answer completely.
You will get up vote for sure.
Step by step
Solved in 3 steps

- ___________ occurs when the result of an arithmetic operation exceeds the number of bits available to store it.6. Perform the following binary multiplication. Assume that all values are 2’s complementnumbers. Indicate the result and whether there is overflow or not.1011 * 1101Perform the following binary multiplication. Assume that all values are 2’s complement numbers. Indicate the result and whether there is overflow or not. 1011 * 1101 Perform the following binary division. Assume that all values are unsigned positive numbers. 10100 / 11
- Please write all the process. 1.. Perform the following multiplications. Assume that all values are unsigned numbers. (No problem with unsigned (always positive) numbers, just use the same standard techniques as in base 10.) a.1010 * 0110 2.Perform the following multiplications. Assume that all values are signed 2’s complement numbers. c.11101 * 1110111. Perform the following hexadecimal additions and subtractions. Assume the numbers are stored in 32-bit 2’s complement binary numbers. Indicate the sign of the answer and whether overflow occurs. c. E9B20F5D – FE605C8D11. Perform the following hexadecimal additions and subtractions. Assume the numbers are stored in 32-bit 2’s complement binary numbers. Indicate the sign of the answer and whether overflow occurs. a. 74F – D63E
- Perform the following arithmetic operations in both decimal and twos complement. Use a word size of 8 bits for the twos complement representations. Use indirect subtraction by addition rather than subtraction for the subtraction problems. c) –16 – (–4) I keep getting 111101100 and I know that is wrong but I can't quite get it. I must be missing something. I appreciate the help. Thank you.Find the two’s complement of the following decimal integers using an 8-bit memory location or indicate if an overflow condition occurs a)+5210 b)−5910Evaluate the following by converting to decimal, performing the arithmetic operation, and converting to binary to express the results. Please note. the answer must be expressed in binary to be correct! when bertormina number conversion. use a precision of eight (8) fractional bits.
- 8. Perform the following additions. Assume that all numbers are in 8-bit 2’s complement notation. State the carry-in and carry-out, whether overflow or not, and if the result is correct. c. 10011001 +101110117. Perform the following binary division. Assume that all values are unsigned positive numbers.10100 / 1149. Find the two’s complement of the following decimal integers using an 8-bit memory location or indicate if an overflow condition occurs a. +5210 b. −5910

