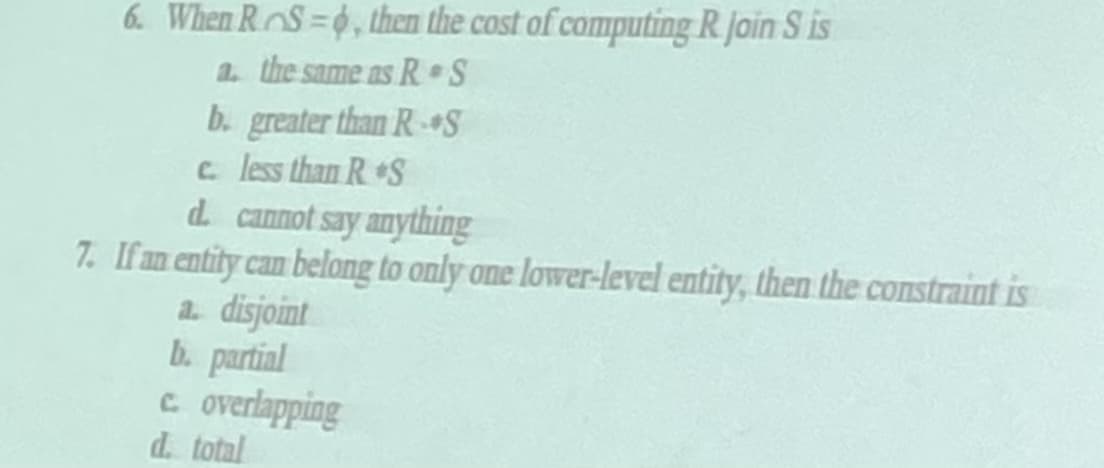
6. When RS=0, then the cost of computing R. Join S is a. the same as R S b. greater than R-S c. less than R. S d. cannot say anything If an entity can belong to only one lower-level entity, then the constraint is a. disinint
Q: In the 802.11 variant known as frequency hopping spread spectrum, the duration of each station's…
A: No, as far as we know, the Bluetooth frame has a fixed dwell time of 625p sec for the basic data…
Q: Where do people run into problems when trying to adopt cryptocurrency on a global scale?
A: The adoption of bitcoin faces a number of challenges worldwide. A few of them are as follows:…
Q: When trying to test the Firebase app on iOS, what are some of the challenges you face?
A: Firebase is a Google-backed application development platform that enables the creation of iOS,…
Q: Experts in the area of information technology are worried about Linux's impending rollout. They want…
A: Considering the information provided: We must suggest a Linux distribution. Answer: Undoubtedly,…
Q: How about we invent a situation where the CIA's holy trinity of Secrecy, Trust, and Vigilance can…
A: CIA: It's easy to protect certain data that only has value for you. You can store photos, thoughts…
Q: Find the complexity of the following blocks of code or algorithm's description. [Note: your answer…
A: The correct answer for the above mentioned question is given in the following steps for your…
Q: I the lower bound for the number of boxes required the first fit decreasing algorithm to estimate…
A: (a) As it is given that the maximum weight that a box can hold is 90 Kg and there are various…
Q: Are there any moral concerns that must be addressed when creating a database? The question of…
A: There are other difficulties that are connected to the database as well as the owners of the…
Q: Search online for an instance of a failed information system development project. Why did we go over…
A: Many information systems fail because of the difficulties of managing the organizational change…
Q: Lab exercises 2 Task 1 Reminder: You must analyse the questions by identifying the input, output and…
A: PROGRAM STRUCTURE: Include the required header files. Declare the required variables. Take the…
Q: What is a database, and how can it be useful
A: In step 2, I have provided ANSWER WITH BRIEF EXPLANATION---------------
Q: The computer Siobhan uses has 8 GB of memory. In addition to the 8GB used by her programs, her…
A: Random Access Memory (RAM): RAM is a storage-related memory device. The data stored in memory is…
Q: A remote item may be activated to be loaded into a server whenever it's needed using a technique…
A: Introduction When it come back to why activation then, trust massive numbers of remote objects (e.g.…
Q: Think about the information stored on your hard drive. Look up each of these terms and write down an…
A: Think about the information saved on your computer. Find examples of each of the above words and…
Q: After conducting a zone transfer and running security tools on the Alexander Rocco network, you’re…
A: Internet of things:- The Internet of things is a philosophy that emphasizes the interconnection of…
Q: Break out the restrictions placed on the stack and its unrestricted counterpart.
A: Stack: A linear data structure called a stack adheres to a certain sequence for adding and removing…
Q: Find the gcd using Euclidean Algorithm 30031 and 2311
A: The process of creating a set of instructions that tells a computer how to perform a task is known…
Q: To what end does a router serve?
A: Router: A router is a real-world or virtual device used to receive, process, and send incoming…
Q: using Mafiaboy's web-based research methodologies The question was when and how he completed his…
A: The FBI detained mafiaboy after he claimed to have shut down the DELL website. 8 months "open…
Q: Assume you are in your homedirectory with a $ prompt. You want to search for a file using the…
A: Command that can be used to search for a file using mlocate database will be locate * "module15"
Q: Java - Polymorphism Create a class named “Shape” that has the abstract methods getArea() and…
A: Class Shape: package com.bartleby; public abstract class Shape { public abstract double getArea();…
Q: Exactly what is a computer network, and how does it function? How many different parts does the…
A: A computer network is a system of interconnected computers, which can communicate and share data…
Q: Comparatively to the previous generation, the fourth generation of networks (4G) supports both voice…
A: Explanation: Mobile network spectral efficiency refers to the rate at which information may be sent…
Q: Define and explain the functions of firewalls, IDSs, and IPSs. I'm interested in hearing your…
A: The function of firewalls: A firewall is a "network security device" capable of monitoring (or…
Q: Write a java application which initializes an array with ten random integers between 1 and 6. Write…
A: The following are steps that need to be taken for the given program: Using Math.random() function,…
Q: A document is represented as a collection paragraphs, a paragraph is represented as a collection of…
A: #include <stdio.h>#include <stdlib.h>#include…
Q: The swap replacement policy the replaces the newest page in memory is Least Recently Used (LRU) Last…
A: As per policy, first three subparts can be answered once. Ans.1 The swap replacement policy the…
Q: Can you explain the various approaches to software architecture? There should be at least 5 lines of…
A: Software Design: In the first phase of SDLC, software design involves translating user requirements…
Q: Do not copy from other websites Q. Explain creating desired colors for a specific pixel on LCD…
A: The pixel is a word created from picture component is the fundamental unit of programmable variety…
Q: Question 1 Given the logic expressions for a set of digital circuits with four inputs (a, b, c, and…
A: Solution : Note: Since you have posted questions with multiple sub parts, we will provide the…
Q: If the CFO signs documentation that indicates you should be given permission to delete sensitive…
A: Security is very important to restrict illegal user within a system. Once a user gets right to login…
Q: A new family is moving into a new house. They hope to use it for both academic and recreational…
A: Home network: A Local Area Network (LAN) is a collection of computers and peripheral devices…
Q: First, let's define "technical documentation." Is there a list anywhere that outlines the four key…
A: A product, system, or service's use, functionality, or architecture are all described in technical…
Q: Write a C++ code that compare the times to traverse a list (containing a large number of elements)…
A: Introduction A linked list is a group of randomly stored items in memory, conjointly referred to as…
Q: Identify the most common uses of stacks in code and defend their relevance.
A: A Stack is a popular linear data structure in modern computers that allows for element insertions…
Q: Abstraction is a key idea in computer architecture and design, and its application in instruction…
A: Abstraction is the process of taking away or eliminating qualities from something in order to reduce…
Q: Consider the language L of strings over the alphabet Σ = {a, b} which contain an equal number of a’s…
A: Introduction A formal grammar called context-free grammar is used to produce every conceivable…
Q: What is a benefit of using an HTML text editor?
A: The answer to the following question:-
Q: Discuss the pros and cons of utilising a cloud storage app as opposed to a traditional client…
A: In the cloud: A service called "cloud storage" allows for the remote management, maintenance, and…
Q: Give four examples of cryptographic techniques used by firewalls to control access and enforce…
A: Cryptography is the science of encrypting and decrypting data. Cryptography is used to ensure…
Q: uters to send UDP packets to each other in the first place for the firewalls on both sides to permit…
A: Introduction: TCP and UDP are the standard transport protocols that ride above the IP layer. UDP…
Q: How about we invent a situation where the CIA's holy trinity of Secrecy, Trust, and Vigilance can…
A: Concerning the Confidentiality of the Situation: The C.I.A. (Confidentiality Integrity Availability)…
Q: ll" apply to computer systems design and
A: Introduction: A general-purpose PowerPC core with modest performance is combined with optimised…
Q: To illustrate, pretend for a moment that you own a business that will shortly launch an online…
A: Information disclosed: Assume you are the business owner of a firm that is set to begin advertising…
Q: This article will examine four distinct logical security methods that, if put into place, would…
A: Introduction: Logical security measures are those that limit system users' access rights and prevent…
Q: Can you explain the concept of technical documentation? How do technical and user documentations…
A: Technical Reporting Technical documentation refers to a variety of publications that include data…
Q: In a few sentences, please explain why memory mapped files are preferable to the more conventional…
A: The answer to the question is given below:
Q: When it comes to people's safety and personal information, how does data mining play a role?
A: Data mining explores and analyses new, unanticipated, previously unknown, and possibly relevant…
Q: If a network has two servers and twenty workstations, where should an anti-virus programme be…
A: A network consists of two or more interconnected computers to share resources (such as printers and…
Q: • Create a JavaFX application that displays the following window: 2345 And shows the array contents…
A: I attached your answer below.
Step by step
Solved in 3 steps

- Which of the following defines a relationship in which data can have multiple occurrences in each entity? one-to-one one-to-many many-to-many none of the aboveConsider the following relation with functional dependencies as shown below. R{sno, sname, age, cno, cname, group) R(A, B, C, D, E, F) Divyansh sharma AB, C C F D-E In which normal form is the relation R is in ? (A) First normal form (B) Second normal form (C) Third normal form (D) Boyce Codd normal formWhich one of the following is defined as" the requirement that actions of an entity may be traced uniquely to that entity"?
- Which of the following statements are correct about EER model for this requirement? Book, Periodical, DVD, ReferenceItem, BorrowingItem, RegisteredUser, and TemporaryUser are set as entities. RegisteredUser and TemporaryUser can be generalized into a User entity. The specialization/generalization hierarchy for users is overlapping for disjoint constraint. Book, Periodicals, DVD, ReferenceItem, and BorrowingItem can be generalized into an Item entityan invoice is written by one sales rep but a sales rep writes many invoices a vendor sells many products but a product is bought from one vendor an invoice has one or many products and a product is found on zero, one or many invoices ● Identify the entity ● Identify the entity’s attribute ● Identify the primary and foreign Keys ● Identify relationship between Entities ● Identify the Cardinality constraints ● Draw ERDdef distance_between_entities(entity1, entity2):"""compute the haversine distance between the two entitiesAn entity is a tuple: (ID, City, State, Latitude, Longitude):param entity1::param entity2::return: the distance (in miles) between the entities"""pass ENTITES LOOK LIKE THISID,City,State,Latitude,LongitudeA45419E,Plattsburgh,NY,44.704021,-73.471148A19312D,Aiken,SC,33.554433,-81.69588A90172S,Tuscaloosa,AL,33.170238,-87.616169A19394D,Alexandria,VA,38.819853,-77.059645A27218D,Pittsburgh,PA,40.47441,-79.950968A68626D,Meadville,PA,41.611599,-80.114891A17494D,Allentown,PA,40.602658,-75.469236A86034S,Tonawanda,NY,42.99704,-78.878659A45142D,Asheville,NC,35.602711,-82.567281A38298S,Atlanta,GA,33.844371,-84.47405A14497Y,Roswell,GA,34.055198,-84.370475A25954D,Austin,TX,30.326374,-97.771258B46374X,Fairhope,AL,30.480713,-87.861306B52199S,Cedar…
- Which of the following functional dependencies are satisfied (and not satisfied) by this relation and Why? (d) C → D Why? (e) B → A Why? (f) BD → AC Why?Consider the following relation with functional dependencies as shown below.R{sno,sname,age,cno,cname,group}R(A,B,C,D,E,F)A-B,CC-FD-Ewhich normal form is the relation R is in?Q3: Emp (Eno, Ename, Title, City) Project(Pno, Pname, Budget, City) Works(Eno, Pno, Resp, Dur) SELECT Ename, Pname FROM Emp e, Works w, Project p WHERE e.Eno = w.Eno AND e.city = p.Eno AND p.city = Newark AND w.Dur > 40 Given the database schema and the query above and knowing that only 1% of the employees work on a project for 40 months or more, propose an optimized query plan and discuss the indexes needed
- identify and discuss the functional dependenciesa) Referring to the company database, which relations have the same set of attributes for their default superkey and primary key? b) Referring to the company database, which relations have a reasonable candidate key that is not its primary key? C) Referring to the company database, specify an update operation to the department relation that will violate a primary key constraint constraint. D) Referring to the company database, what constraints to the database would be violated if Smith were deleted from the employee relation? Include the relevant relations and attributes in your answer.Suppose that the following are true:- all id column are primary keys in whichever table they are- the dept_id in course table is foreign key that is referencing the id column in the department table- the foreign keys stud_type_id, stud_cat_id in the student table are referencing the id columnsin the student_type and student_category tables respectively.- the coursecode and stud_id columns in the registration table are foreign keys in the courseand student tables respectively.1. Design an Entity Relationship Diagram for the system above.2. Write query that would return the names and contacts of all Local students.3. Write a query that would return names, contact and locations of all departments that has alocation text with Ave 3 as part of it. [hint: use the LIKE clause with “_” or “%”]4. What would be the result returned for the following query:SELECT first_name, last_name, student_type.name,student_category.nameFROM student, student_type, student_categoryWHERE stud_type_id =…

