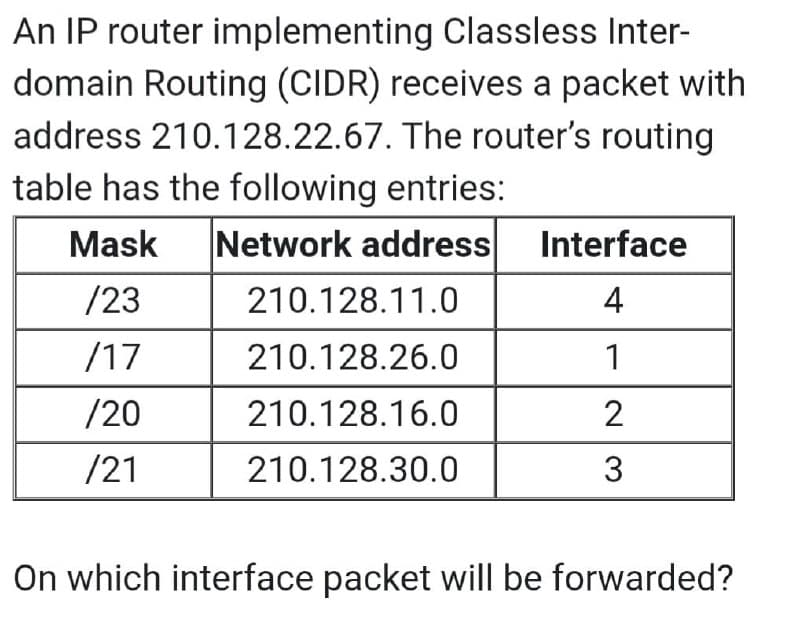
67. The router's rou ng entries:
Q: The data breach might potentially have a substantial impact on the security of the cloud; however,…
A: Solution: Yes, it has an impact. As a consequence of a data breach, an unauthorised person acquires…
Q: You bought a computer with a ram (main memory) of 4 GB. You have a C-code in which a calloc is…
A: Yes, my code will run correctly on my computer. for reason : C calloc() method -"calloc" or…
Q: What changes did computer technology undergo in the 1950s?
A: Introduction: Significant advances in computer technology were made between 1950 and 1959.
Q: Bias Assume that the activation function used for all neurons is "logistic function and the Bias is…
A: The answer is
Q: The effect that quantum computing will have on programming is not entirely understood.
A: Introduction: Quantum computing looks to open up new avenues for dealing with very difficult…
Q: Understanding privacy in the context of information security may be a challenging endeavour.
A: Understanding privacy in the context of information security may be a challenging endeavour. The…
Q: The notion of OOP is based on real-world examples, but how can we verify this? In what ways may this…
A: Beginning: Based on real-life instances, OOPSThe goal of object-oriented programming is to represent…
Q: To better understand the relationship between PACS and the Internet of Things, please provide some…
A: PACS (Physical access control system)The software that is used in the physical access control system…
Q: Why is it essential that the compilers that we work with be optimised? If you were a software…
A: Optimising the compiler: Compiler optimisation may be constructed in such a manner that it becomes a…
Q: What contingency plans are in place to deal with the possibility that the project's scope may need…
A: Introduction: To address shifting demands, use a new approach and work in Agile-style two-week…
Q: hamming codeword (v) If during transmission, the 5th bit is flipped. Explain the process of recov…
A: The answer is
Q: You have to 2 ints from the user( a and b) & print their sum on the console. However, sums in the…
A: Please find the answer below :
Q: # PART 1 - Complete the function below to deocompose # a compound formula written as a…
A: In the following step, part 3 of the given Python programe has been coded. Note:- Per Bartleby…
Q: Distinguish between the processing of structured data and the processing of Big Data. What are the…
A: Introduction: Structured data is well-organized data that may be offered directly for anticipating…
Q: When it comes to the management of firewalls, what are some of the best practises that may be…
A: A Firewall is an organization security gadget that screens and channels approaching and active…
Q: 8. Write a C program that has the following statements: int a, b; Imeni b = a + fun(); P…
A: Here is the explanation of code First of all we define two datatype of int name as a and b…
Q: Data transmission standards and protocols TCP and UPD both provide their own set of difficulties and…
A: Data Transmission Standards DEFINITION: A method of phase-shift keying (PSK) known as staggered…
Q: Recursive function that returns the minimum of the numbers in C PROGRAMMING LANGUAGE PLEASE AND…
A: #include <stdio.h>//recurisve function to find and return the minimum of the numbers//input…
Q: Create a list of all the parts that go into a quantum computer and describe how they fit together to…
A: Introduction: Essential cloud storage is a distributed computing technique in which data is stored…
Q: What is an opcode and which information is stored inside an opcode? What are the different ways to…
A: In computing, an opcode (abbreviated from operation code) is the portion of a machine language…
Q: Which components of building a compiler need to be prioritised in order to guarantee that the end…
A: Compiler optimization: An optimizing compiler is a piece of computer software that aims to minimize…
Q: Can you illustrate the value of employing the Work Breakdown Structure (WBS) idea using any SDLC of…
A: The Answer is in given below steps
Q: 7 4 2 6 5 3 1 8 Start State Goal State ● States: Location of each of the 8 tiles in the 3x3 grid…
A: import java.io.*;import java.util.*; class GFG{ public static int N = 3; public static class Node {…
Q: What would it take for a business to operate its own private cloud?
A: Introduction When a private cloud is properly designed and implemented, it may give many of the…
Q: What do you name a piece of software that performs a certain task, such as virus scanning, data…
A: Introduction: A collection of instructions and documentation that tells a computer how to carry out…
Q: What is the process through which SaaS operates? Could you kindly elaborate on what you mean?
A: The Basics of SaaS: A software as a service (SaaS) approach enables customers to access information…
Q: True Start Read raw = 0, boiled = 0 min = 0, max = 0 userGuess, random_Num userGuess = get next…
A: Given Flowchart:
Q: The question "What are the top six reasons people want to learn about compilers?" is one that is…
A: Compilers A compiler is a software program that converts program code into a more basic machine…
Q: Educators should understand the benefits and cons of adopting educational information systems.
A: Educational information systems may be defined as a collection of pieces or components that are…
Q: There is a possibility that malicious traffic that was routed from one VLAN to another was the root…
A: Start: VLAN hopping, also known as virtual LAN hopping, is a network exploit that allows users on…
Q: Describe the importance of using a wide variety of testing approaches across the different phases of…
A: Given: Explain the necessity for different software testing methodologies at different phases.…
Q: What is the central processing unit's function and what does it do? How do you feel about this?
A: Introduction: In order to provide a solution to the question, we will need to explain the goal and…
Q: Give atleast 3 real life example of minimum stienner algorithm
A:
Q: Recognize and describe the five primary areas or fields that are concerned with internet governance,…
A: The response is: A network of links connecting the different institutions, organisations, and…
Q: It is essential to have a solid understanding of which aspects of the Compiler Phases are the most…
A: Compiler operates in various phases and in each phase it will transform the source program from one…
Q: Have you ever given any consideration to the plethora of diverse applications that SSH may be used…
A: SSH: Contamination is a possibility in computer science. SSH, also known as Safe Shell or Secure…
Q: reg, mem; 4 clock cycles ADD reg, reg ;3 clock cycles ADD reg, immed; 2 clock cycles LOOR LabelName…
A: The answer is
Q: What is a common language that computers use to talk with one another on a network? A. Client
A: What is a common language that computers use to talk with one another on a network?A. ClientB.…
Q: Has anybody ever successfully managed to conduct a distributed denial of service attack?
A: The GitHub DDoS assault in February 2018 GitHub, a famous online code management site used by…
Q: What exactly is SDLC? What are the different stages called?
A: SDLC: Evolution of systems The life cycle is a systematic strategy for delivering a quality system…
Q: A: For the three input timing diagram shown below, do the following logic operations and draw the…
A: As per our guidelines, only 3 sub parts will be answered. So, please repost the remaining questions…
Q: When compared to other possible solutions for network security, such as application layer securi
A: Introduction: The advantages and disadvantages of using IPSec are listed below.
Q: dvantages of process isolat
A: Introduction: Process isolation is a hardware and software combination that protects each phase of…
Q: What are the top six reasons why someone should educate oneself about compilers?
A: We should since, in order to be effective at programming, we need to understand how everything…
Q: What is the most significant difference between mainframe operating systems and operating systems…
A: Introduction: The following are the key distinctions between two categories of operating systems:
Q: When a process is terminated, what does it mean?
A: Introduction: When a process has finished its execution, we say that it has died or that it has been…
Q: What should you bear in mind while migrating from one system to the next? Why don't you go into…
A: Introduction: A single organisational component change has no impact on hierarchical execution.
Q: What are the key differences between a traditional computer and a quantum computer? In the field of…
A: Quantum computers: Quantum computers process quantum data. It uses quantum mechanical phenomena like…
Q: An adversary makes use of a MAC in an effort to modify both the Tag (the ciphertext) and the MAC…
A: Given: The solution to the above question is as follows. MAC is the abbreviation for the tag. It's a…
Q: Give an example that you will prefer Python over C as your choice of programming language and…
A: There are many reasons why we should prefer python Languages over C program. Ease of development –…
Step by step
Solved in 2 steps with 2 images

- A router running Classless Interdomain Routing (CIDR) has the following entries in its routing table: Address/mask Next hop 135.46.56.0/22 Interface 0 135.46.60.0/22 Interface 1 192.53.40.0/23 Router 2 Default Router 3 How does a CIDR router work to route the packets it received? For each of the following IP addresses, what will the router do if a packet with that address arrives? (a) 135.46.63.10 (b) 135.46.58.16 (c) 135.46.52.2 (d) 192.53.40.7 (e) 192.53.56.7Using packet tracer, implement a network that has the following components: 1- At least five routers 2- At least 7 subnets 3- At least 12 PCs 4- At least 4 switches 5- Use RIP routing protocol To assign IP addresses of the routers and PCs, use the IP address from your ID as follows Assume your id is 118zyxw, Consider the numbers z, y, x and w as deciemal You have the subnet 118.0.0.0/24 If your ID is 1181234 then the IP is 118.0.0.0/24 Use this subnet to get at least 7 subnets.There is a routing table in the figure on a router. If packets with the following destination IP addresses arrive at the router, where are they routed? a) 198.52.61.10b) 198.53.40.201c) 198.52.60.89d) 198.52.63.113 Show your work and reasoning for each option.
- Assume that you have two computers and a router (default gateway) that have the following TCP/IP configuration and that Computer A wants to send data to Computer E. Match the addresses that will be used in the IP packet and the ethernet frame sent from Computer A. Computer A IP address: 178.23.43.12 Netmask: 255.255.0.0 Default gateway address: 178.23.17.1 MAC Address: 34:2A:C6:C6:55:C3 Computer E IP address: 178.23.54.23 Netmask: 255.255.0.0 Default gateway address: 178.23.10.1 MAC Address: 34:2A:C6:76:3E:12 Default Gateway MAC Address: 65:D3:C9:11:C5:99 Items to Match: IP packet Source IP address: IP packet Destination IP address: Ethernet frame Source MAC address Ethernet frame Destination MAC address Possible Values: 178.23.17.1 178.23.10.1 178.23.43.12 178.23.54.23 34:2A:C6:C6:55:C3 65:D3:C9:11:C5:99 34:2A:C6:76:3E:12A router has the following entries in its routing table: 135.46.56.0/22 Interface 0 135.46.60.0/22 Interface 1 192.53.40.0/23 Interface 2 Default Interface 3 For each of the following IP addresses, what does the router do if a packet with that address arrives? a. 135.46.63.10 b. 135.46.57.14 c. 135.46.52.2 d. 192.53.40.7 e. 192.53.56.7A network configuration of a modem is given as following:LTE interface IP = 77.110.156.22 MASK 255.255.252.0Default GATEWAY = 77.110.156.1Masquerade NAT, and DNS address = 1.1.1.1Local IP setup: 192.168.128.1 MASK 255.255.255.0And, ip route 192.168.128.0 255.255.252.0 192.168.128.254 Devices numbered R1, R2, R4, R5 are routers. PC is a computer.Image of network with interface names such as f1/0 are added. You must use only static IP addreses and static IP routes to configure the network and make PC able to connect (ping) to Modem.
- . Assume: Your laptop's Ethernet address is 0a:0b:0c:0d:0e:0f, DHCP server address is 131.111.7.3, your IPv4 address will be 131.111.7.121, the gateway's IP address is 131.111.7.1, and Ethernet address is 00:01:02:03:04:05, the network subnet mask is 255.255.255.0.Write the series of protocol/packet exchanges that occur on the wired Ethernet link, up until you can send a single packet to 128.232.0.20. You do not need to describe packets after this packet has left the link. Include ARP and DHCPA network system has 5 protocol layers. Applications generate messages of length M bytes. At each of the layers, an h-byte header is added. What fraction of the network bandwidth is filled with headers? a. 5h/(5h+M) b. M/(5h+M) c. M/(4h+M) d. 4h/(4h+M)4. A router receives a packet with destination address 196.77.26.206 Show how it finds the network and the subnetwork address to route the packet. Assume the number of subnetworks required is four. Please solve it using the keyboard, not using the hand, and quickly, and I hope that the solution is correct.
- Assume that there are four routers (R1, R2, R3, and R4) and four hosts (H1, H2, H3, and H4) in a network (N1). H1 sends an email to an instructor H3 at SEU.EDU.SA. (192.168.1.1) and the router path is R1, R3, R2, and R4, but the H3 host find a parameter problem and dropped the packet. Explain how ICMP protocol can be used as a debugging tool and draw a diagram to illustrates the traceroute process for this scenario? PART 2 || Characteristics The Transport-layer Protocol It is a simple connectionless protocol with neither flow nor error control. The size of the send window must be less than 2m; the size of the receive window is always 1. Each time a single packet is lost or corrupted, the sender resends all outstanding packets, even though some of these packets may have been received safe and sound but out of order. Both the sender and the receiver use a sliding window of size 1. The sender sends one packet at a time and waits for an acknowledgment…Suppose a user from Taman Jatt Kata Kinabalu is working from a machine at home with IP address 10. 0. 0.10 on a local network attached to a router connected to the Internet The user requests a web page through a Web browser. Show using illustration when and why each of the following aspects of networking are involved. Be as precise as possible. i ARP ii NAT iii DNS iv UDP v TCP.For example, let say that your Network 1 needs 30 hosts and you are in a class C network, you would start with 192.168.0.1 till 192.168.0.32 because the closest you can get to 30 that is more is 32 (2exp5) so my begin address would be 192.168.0.1, end address would be 192.168.0.32 (not 192.168.0.30 because we only need 30 hosts) and subnet mask would be 255.255.255.224. The next range will start at 192.168.0.33!!! Use the example to answer: We are going to use the private range for a class A network. What is its standard subnet mask? A) Network 1 needs 250 hosts B) Network 2 needs 230 hosts











