7. Consider the problem of recovering from host crashes (i.e., Fig. 6-18 of textbook; see below). If the interval between writing and sending an acknowledgement, or vice versa, can be made relatively small, what are the two best sender-receiver strategies, for minimizing the chance of a protocol failure? Explain why. Strategy used by receiving host Strategy used by sending host Always retransmit Never retransmit Retransmit in SO Retransmit in S1 First ACK, then write AC(W) AWC C(AW) OK OK DUP OK LOST LOST DUP LOST OK LOST OK OK OK DUP LOST Protocol loses a message First write, then ACK C(WA) OK LOST LOST OK = Protocol functions correctly Protocol generates a duplicate message WAC WC(A) DUP DUP OK OK OK DUP DUP OK
7. Consider the problem of recovering from host crashes (i.e., Fig. 6-18 of textbook; see below). If the interval between writing and sending an acknowledgement, or vice versa, can be made relatively small, what are the two best sender-receiver strategies, for minimizing the chance of a protocol failure? Explain why. Strategy used by receiving host Strategy used by sending host Always retransmit Never retransmit Retransmit in SO Retransmit in S1 First ACK, then write AC(W) AWC C(AW) OK OK DUP OK LOST LOST DUP LOST OK LOST OK OK OK DUP LOST Protocol loses a message First write, then ACK C(WA) OK LOST LOST OK = Protocol functions correctly Protocol generates a duplicate message WAC WC(A) DUP DUP OK OK OK DUP DUP OK
Principles of Information Security (MindTap Course List)
6th Edition
ISBN:9781337102063
Author:Michael E. Whitman, Herbert J. Mattord
Publisher:Michael E. Whitman, Herbert J. Mattord
Chapter6: Security Technology: Access Controls, Firewalls, And Vpns
Section: Chapter Questions
Problem 2RQ
Related questions
Question
Alert : Dont't submit
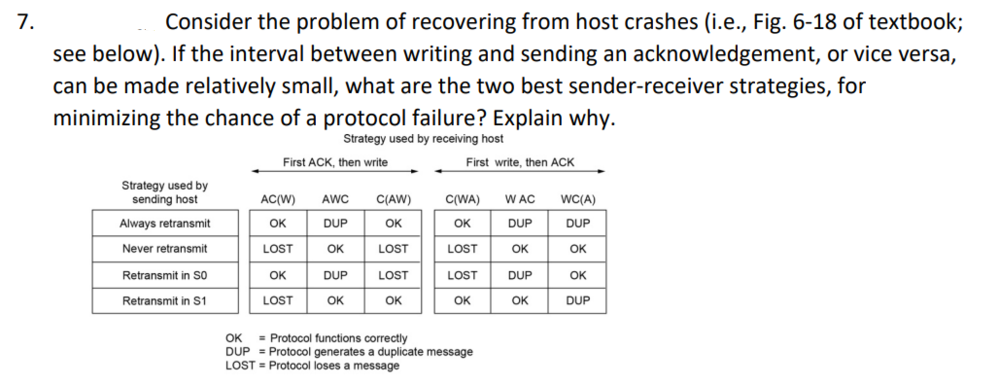
Transcribed Image Text:7.
Consider the problem of recovering from host crashes (i.e., Fig. 6-18 of textbook;
see below). If the interval between writing and sending an acknowledgement, or vice versa,
can be made relatively small, what are the two best sender-receiver strategies, for
minimizing the chance of a protocol failure? Explain why.
Strategy used by receiving host
Strategy used by
sending host
Always retransmit
Never retransmit
Retransmit in SO
Retransmit in S1
First ACK, then write
AC(W) AWC
C(AW)
OK
OK
LOST
DUP
OK
LOST
DUP LOST
OK
OK
OK
LOST
First write, then ACK
C(WA) WAC
DUP
OK
DUP
OK
LOST
LOST
OK
OK
= Protocol functions correctly
DUP Protocol generates a duplicate message
LOST Protocol loses a message
WC(A)
DUP
OK
OK
DUP
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning