7. Which of the following will evaluate to false? i. false AND (true OR NOT (false) ii. true AND (NOT (true AND false)) iii. NOT (false OR (true OR false)) (A) i and ii (B) ii and iii (C) i and iii (D) i, ii, and iii
7. Which of the following will evaluate to false? i. false AND (true OR NOT (false) ii. true AND (NOT (true AND false)) iii. NOT (false OR (true OR false)) (A) i and ii (B) ii and iii (C) i and iii (D) i, ii, and iii
Programming Logic & Design Comprehensive
9th Edition
ISBN:9781337669405
Author:FARRELL
Publisher:FARRELL
Chapter4: Making Decisions
Section: Chapter Questions
Problem 8RQ
Related questions
Question
Please answer questions 7-9 and show work and explain how u got the answer!! Not an graded assignment!!
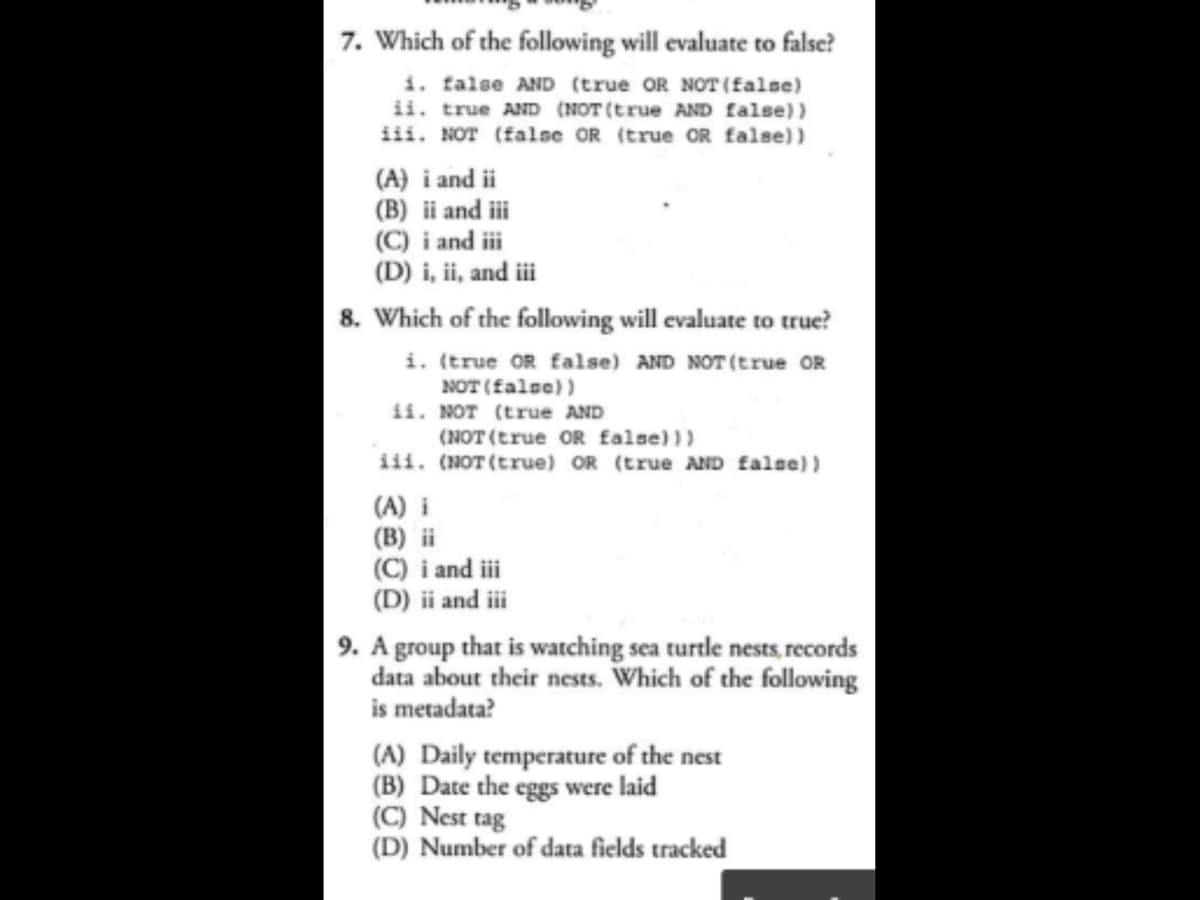
Transcribed Image Text:7. Which of the following will evaluate to false?
i. false AND (true OR NOT (false)
ii. true AND (NOT (true AND false))
iii. NOT (false OR (true OR false))
(A) i and ii
(B) ii and iii
(C) i and iii
(D) i, ii, and iii
8. Which of the following will evaluate to true?
i. (true OR false) AND NOT (true OR
NOT (false))
ii. NOT (true AND
(NOT (true OR false)))
iii. (NOT (true) OR (true AND false))
(A) i
(B) ii
(C) i and iii
(D) ii and iii
9. A group that is watching sea turtle nests, records
data about their nests. Which of the following
is metadata?
(A) Daily temperature of the nest
(B) Date the eggs were laid
(C) Nest tag
(D) Number of data fields tracked
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage