8 Q6. (.. *) Apply the backtracking algorithm for the 3-coloring problem on the graph below, processing the vertices in alphabetical order, to determine whether it is 3-colorable or not, finding the 3-coloring of the graph, if it exists. Make sure you show all intermediate steps. b d a с f
Q: comparison or distinction between IoS and OSI There's also the question of TCP vs. IP to consider.
A: Introduction: The following is the difference between ISO and OSI: The International Organization…
Q: What is a system model, exactly? What factors should be considered when creating basic models?
A: System model refers to creation of a conceptual solution to a business problem. This means that…
Q: firewalls are critical for network security and cybersecurity, thus it's important to understand…
A: Let's start by asking, "Why firewall: I have a computer, and it works well. I'm doing a fantastic…
Q: To write a main code that calls a function the main code and the function should be:
A: Answer for both mcqs given below with explanation
Q: Write a C++ program to find Square Root of a Number. I
A: write a C++ program to find square root of a number
Q: Emphasize the differences between microservices and service-oriented architecture (SOA) and how they…
A: Differences between microservices and service-oriented architecture (SOA)
Q: When working with dynamic data, explain the function of the heap. Why would a coder choose to work…
A: When working with dynamic data, explain the function of the heap. following is the heap creation…
Q: Choose the right output of the following code: x= [0,3] y=[3,3] plot (x, y) hold on x= [0,3] y=[4,4]…
A: 1. Given code: x=[0 3] y=[3 3] plot(x,y) hold on x=[0 3] y=[4 4] plot(x,y) This…
Q: Write a program that determines if the input letter is a VOWEL or CONSONANT. Your program must be…
A: The five letters A , E , I , O and U are called vowels. All other alphabets except these 5 vowels…
Q: o be weighe
A: Introduction: Data storage and access through the Internet is referred to as "cloud computing". It…
Q: ]Determine whether the statement is true or false. 1. . If AB = AC, then B = C. 1 2. If A = 3). then…
A: 1.True because AB=AC then AB-AC=0 => A(B-C)=0 A=0 AND B-C=0 ===> B=C. 2.True sqaure the…
Q: #include #define ROW 4 #define COL 4 int M[ROW][COL] = {1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11, 12, 13,…
A: Given statements are #include<java.util.*>#define ROW 4#define COL 4int M[ROW][COL] = {1, 2,…
Q: A fingerprint reader, rather than a username and password, is the new way that your organization…
A: Reader of fingerprints: Instead of typing a user name and password, a fingerprint scanner is a…
Q: produces both interior and exterior paints from two raw materials, MI and M2. The following table…
A: a) From the diagram, it is very clear that the optimality condition will change only when the…
Q: Provide an overview of Internet Protocol Version 6, as well as IPv6, VPNs, and VoIP. In addition,…
A: Introduction: IPv6 is the most recent version of the Internet Protocol (IP), which identifies and…
Q: What is the correct command to find square root of any number, x. sqrt(x) O What is the output of…
A: Answer:
Q: prepare a use case scenario for social activity with your friends.
A: prepare a use case scenario for social activity with your friends.
Q: plemenation powershell security cmdlet
A: 1.Get-CommandGet-Command is an easy-to-use cmdlet that displays all available commands for you to…
Q: Consider the benefits of a step-by-step approach to software development over a waterfall model.
A: GIVEN: What are the three advantages of incremental development over the waterfall model?
Q: What is the correct command to find square root of any number, x.
A: Answer for both mcqs given below with explanation.
Q: What is database protection? Describe any two strategies for database protection.
A: Answer:
Q: Discuss the five specific applications of graph theory in artificial intelligence.
A: Answer to the above question is in step 2.
Q: On the Internet, how do you feel about the difference between genuine and bogus information?
A: Introduction: The internet is a terrific information resource. It enables us to communicate with…
Q: Write the Java code to calculate your 'CGPA'. Th Consider your ID as Database and Table Name.
A: import java.util.Scanner; class CGPACalculation { double sum=0; CGPACalculation(double…
Q: Thank you but the code has to input a float and print out a float.
A: Code: #include<stdio.h>void ftoa(float n){ char str[20]; //create an empty string to store…
Q: Is there a substantial difference between a DLL and an EXE in the.NET Framework?Is there a…
A: In .NET framework, you have two choices to make a .EXE or .DLL file. These two both contain…
Q: f the corresponding part of the electromagnetic spectrum, as given in the following table. Using if…
A: the program is an given below :
Q: Where can you get reliable information on the Internet
A: Types of resources Three types of sources exist: Primary, secondary, and tertiary
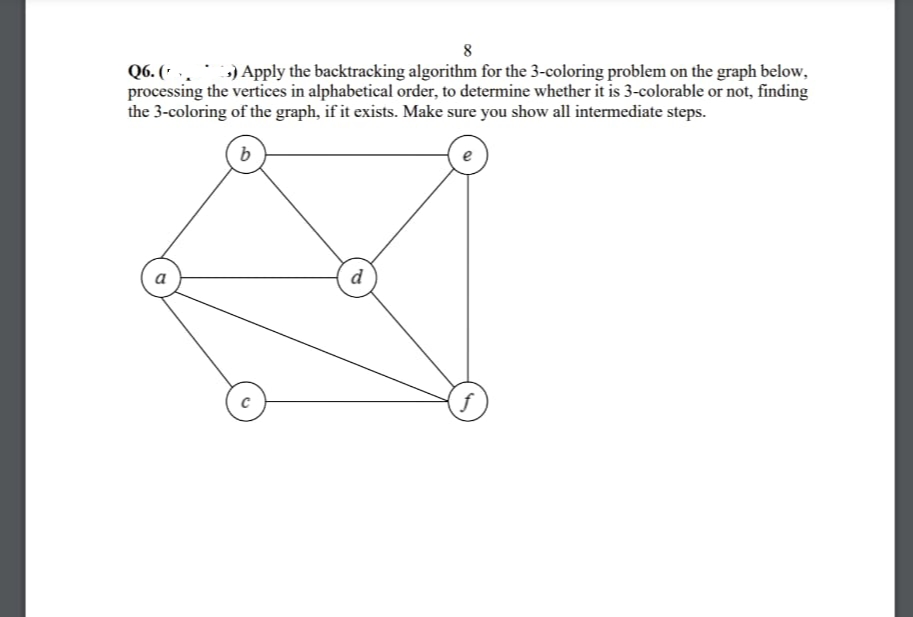
Q: Q6. (.. ») Apply the backtracking algorithm for the 3-coloring problem on the graph below,…
A: The Answer is in step-2.
Q: we can execute a saved function by writing the function name in the : figure window O work space O…
A: Answer:
Q: Identify and explain several internet of things (IoT) applications.
A: Actually, IoT stands for Internet Of Things.
Q: *.the maximum number of hosts in class C 127 O 128 O 255 O 254 O
A: In tiny networking areas like LANs, Class C is typically used. The answer is in the step after.
Q: To display 'Question 2'in the command :window,the correct command is disp(Question 2) O…
A: The command window gives the instructions or the provide the informations that allows us to enter…
Q: Distinguish between speech and presentation.
A: Differentiate between speech and presentation are:- A speech is an event where a speaker stands…
Q: Arduino Due and Arduino Mega have the same number of Digital Input/Output, ........ which is equal…
A: The question is to select the correct option for the given questions.
Q: A(n) ____ is a piece of programming code that replaces or changes some of the code that makes up the…
A: A patch or fix is a quick repair job for a piece of programming designed to resolve functionality…
Q: What is a reverse proxy server, and why would you need one for your network?
A: A proxy server is a server that acts as a go-between or middleman, forwarding content requests from…
Q: The vast majority of the time, networked surveillance cameras are not in danger.
A: Answer:
Q: A embedded system with four tasks with task IDs T₁, T₂, T3 and T4 with estimated completion time 10,…
A: A embedded system with four tasks with task IDs T1, T2, T3 and T4 with estimated completion time 10,…
Q: Tablet and mobile phone use in the office has to be discussed.
A: Introduction: Electronic gadgets are parts for controlling the progression of electrical flows with…
Q: che memory
A: Introduction: Faster access to data is made possible via cache memory, a high-speed CPU memory. The…
Q: TCP/IP is a paradigm of networking that is distinct from the OSI model. Use proof and facts to back…
A: Given: There are four levels to the TCP/IP paradigm: the network access layer, the internet layer,…
Q: What is the key difference between a.NET Framework DLL and an executable file (EXE)?
A: DLL and an Executable file: EXE is the extension for executable files, whereas DLL is the extension…
Q: Why would you utilize a menu instead of enabling the user to type in their own content in your…
A: A menu is defined as the set of options presented to the user of a computer application which is…
Q: Describe the fundamentals of the various routing protocols and ideas.
A: Introduction: Layer 3 (or network layer) devices employ routing to send packets by calculating the…
Q: What is type casting? Explain implicit and explicit type conversion with example.
A: Typecasting is converting one data type into another one. There are two types of type casting/ type…
Q: How is it feasible for a single individual to coordinate a distributed denial of service attack?
A: Distributed denial of service attack : DDoS Attack means "Distributed Denial-of-Service Attack" and…
Q: If someone tried to get into your computer, where would you look?
A: Windows Task Manager: Windows Task Manager, you may see whether any programmes have been started on…
Q: What are three choices that may be applied to a project based on a decision tree structure? The…
A: Introduction: A decision tree is supervised learning approach that serves as a decision-making aid.…
Q: What is the mechanism through which Blazor works? What distinguishes Razor from similar…
A: The use of event handlers in Blazor allows you to manage HTML events such as on Click events.You can…
1
Step by step
Solved in 2 steps with 2 images

- EXERCISE 2 Based on the image attached, represent the directed graph by listing all the vertices that are the terminal vertices of edges starting at each vertex of the graph.Create a y vector such that y = ex where x = [1,2,3,4,5,6,7,8,9]. Plot the result on an xygraph. Label the x- and y-axes and place a title on the graph.Use MATLAB.Let G be an undirected graph whose vertices are the integers 1 through 8, and let the adjacent vertices of each vertex be given by the table below: look at the picture sent Assume that, in a traversal of G, the adjacent vertices of a given vertex are returned in the same order as they are listed in the table above. Which statement of the following is correct? group of answer choices a) The sequence of vertices visited using a DFS traversal starting at vertex 1: 1, 2, 3, 4, 6, 5, 7, 8. b) The sequence of vertices visited using a BFS traversal starting at vertex 1: 1, 2, 3, 4, 6, 5, 7, 8. c) Both sequences are wrong. d) Both sequences are correct.
- Consider the graph depicted below. Answer the following questions: What is the degree of vertex a? What is the sum of degrees of all vertices? Who are the neighbors of vertex f? [Please, give the list in alphabetical order, separating letters with only a comma. Do not insert blank spaces] How many zeros does the adjacency matrix of the graph above contain? What is the value on row g and column d of the adjacency matrix?Question 9 Create a graph, if possible, with the following attributes, then find the index matrix of your graph. 6 vertices 5 edges One vertex with a degree of 3 All vertices are connected in some way, but it does not have to be a direct connectionVertices should be named by the letters in the alphabeth : A, B, C, D, EEdges should be named : e1,e2, e3, e4, e5, e6, e7, e8, e9 Draw or Make a Directed graph with 9 edges and 5 vertices
- A. Let G be a graph on 17 vertices. We know that G contains at most one cycle. How many edges can G contain at the most? B. The expression r is written in post-order notation (also referred to as RPN). What value does r evaluate to? r = 1 6 7 + - 5 3 + 2 * +1.) Draw a graph described by the following and determine the number of edges each should have.a.) 1 node of order (3)3 nodes of order (2)3 nodes of order (1)Question 13 sum .Skelch the araph of the function. Labet the vertex of the V-shape. f(x)=7|x-1| Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line
- Please help... Adding one more vertices... highlighted with with bold... Let A, B, C, D be the vertices of a square with side length 100. If we want to create a minimum-weight spanning tree to connect these four vertices, clearly this spanning tree would have total weight 300 (e.g. we can connect AB, BC, and CD). But what if we are able to add extra vertices inside the square, and use these additional vertices in constructing our spanning tree? Would the minimum-weight spanning tree have total weight less than 300? And if so, where should these additional vertices be placed to minimize the total weight? Let G be a graph with the vertices A, B, C, D, and possibly one or more additional vertices that can be placed anywhere you want on the (two-dimensional) plane containing the four vertices of the square. Determine the smallest total weight for the minimum-weightMark Zuckerberg, the CEO of Facebook, has hired you to lead the Facebook Algorithms Group. He has asked you to use various graph algorithms to analyze the world's largest social network. The Facebook Graph has 2.8 billion vertices, with each vertex being a Facebook user. Two vertices are connected provided those two users are "friends". The first decision you need to make is how you want to model the Facebook graph. Determine whether you should use an adjacency-list representation or an adjacency-matrix representation.R-13.7 - Let G be a graph whose vertices are the integers 1 through 8, and let the adjacent vertices of each vertex be given by the table below: Vertex: 1 2 3 4 5 6 7 8 Adjacent Vertices: (2, 3, 4) (1, 3, 4) (1, 2, 4) (1, 2, 3, 6) (6, 7, 8) (4, 5, 7) (5, 6, 8) (5, 7) Assume that, in a traversal of G, the adjacent vertices of a given vertex are returned in the same order as they are listed in the table above. a. Draw G. b. Give the sequence of vertices of G visited using a DFS traversal starting at vertex 1. c. Give the sequence of vertices visited using a BFS traversal starting at vertex 1.

