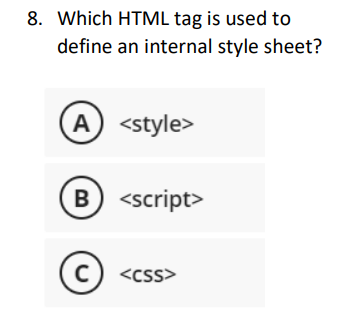
8. Which HTML tag is used to define an internal style sheet? A)
Q: Output is nearly correct, but whitespace differs. See highlights below. Special character legend…
A: Algorithm of the code: 1. Ask the user to input a highway number2. Create a variable to store the…
Q: How fast does a computer clock?
A: Introduction: Your CPU—your computer's "brain"—performs in a significant way to decide how quickly…
Q: Determine the specific type of addressing mode (SMALL LETTERS only) and compute for the address/es.…
A: Addressing mode specifies how to calculate the effective memory address of an operand by using…
Q: 1. Describe the emerging trends and technologies that will have an impact on the
A:
Q: (2) Convert the following Binary numbers into Decimal. SHOW ALL WORK. (2.1) 10111 (2.2) 10101011…
A: Introduction: To convert a binary number to a decimal number, execute a multiplication operation on…
Q: Flash drives should be inserted into this slot. How were the drives mapped in the operating system?
A: Operating system An operating system is a product that fills in as a mediator between end-client and…
Q: What is the main difference between a centralized repository and a distributed repository A. In a…
A: Please find the answer below :
Q: void Discard (std::string food) std::cout << "Some food got spoiled. Discarding } int main() { }…
A: Algorithm: 1. Start2. Declare a function named Discard which accepts a string parameter.3. Inside…
Q: The numerous methods of data concealment provide unique difficulties for law enforcement, thus it's…
A: Answer:
Q: python: def character_gryffindor(character_list): """ Question 1 You are given a list of…
A: In this question we have to write a program in python in one line to do the filtering of harry…
Q: Discuss the personal significance of multimedia.
A: Definition:- Multimedia, as its name implies, is a mix of several sorts of media, such as text,…
Q: 4.4. Suppose maximum was defined as: public static > E maximum (E x, E y, E z) Which definition for…
A: The Comparable interface is an interface in the Java API that is used to define the natural ordering…
Q: Describe the considerations that must be made by a web designer.
A: One should employ or adhere to these five fundamental procedures in order to construct a website.…
Q: Language/Type: Related Links: vector C++ vector collections STL Write a function named addStars that…
A: Here is your solution step by step -
Q: In what way did the partnership between Facebook and Cambridge Analytica lead to a data breach?
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: When comparing datagram networks and virtual circuit networks, what are the key distinctions?
A: Answer : Comparing datagram networks : 1) It is a connection less network. 2) In terms of…
Q: What do the many components of a computer system include, and how do they collaborate to accomplish…
A: The following are the primary elements that make up a computer system: • A central processing unit •…
Q: Write a program to solve the H problem for general values of n > 0 and k ≥ 0. Your program must read…
A: C++ is a fast and strongly typed programming language. In the C++ language, the program can be…
Q: 3.2.2: Read and format integers. C++ Jump to level 1 First, read in an input value for variable…
A: The above question is solved in step 2 :-
Q: Write a program to find the most common words in a file. attach snapshot of output.
A: Introduction: We'll use the file's content as input. After eliminating spaces and punctuation from…
Q: When it comes to a successful criminal investigation, why is documentation so critical? Identify the…
A: Documentation is critical to a successful criminal investigation as it provides a clear and concise…
Q: Please refer to the table in the dreamhome database. Which statement is TRUE if we run the following…
A: According to the information given:- We have to choose the correct option to satisfy the statement.
Q: ake the following scenario into consideration: Is it necessary to have a recovery manager for the…
A: Having a recovery manager for a database system is important, even if the system operates perfectly,…
Q: Draw a System Diagram of a GUI Checkers game (Java) where the player can choose to play either…
A: Introduction: System Diagram: A systems diagram is a visual model of a system, its components, and…
Q: It is essential to have a clear understanding of the difference between a vulnerability screening…
A: Vulnerability Scanning: Vulnerability scanning identifies known vulnerabilities in the system or…
Q: The corporation has assigned you the task of developing a plan to mitigate potential threats. The…
A: The following describes the relationship between impact, vulnerability, and threat: When a company…
Q: What characteristics set apart domain-specific software architecture?
A: Introduction Any piece of software should be compelling to find true success. It should be equipped…
Q: Using laws of logic, determine the negation of the following statement (PQ) → (PVQ)
A: Laws to apply in determining the negation of the given statement: 1) p<->q = (p∧q) ∨ (¬p∧¬q)…
Q: F Source For the network shown below, the arc capacity from node i to node j is the number nearest…
A: For example, using Dijkstra's algorithm, you can start at node 1 and find the shortest path to node…
Q: To help the system designer, here are five ways to ease the user's mind.
A: Introduction System designers are individuals responsible for fostering the documentation for an…
Q: data mining is a method that facilitates the creation of business information and its related…
A: Introduction : Data mining is the process of discovering patterns in large data sets involving…
Q: The components of a computer system may be broken down into two categories: hardware and software.
A: Hardware: A computer's physical components. Sometimes called the computer's machinery or system.…
Q: Write pseudocode for Floyd’s algorithm for the all-pairs shortest path problem
A: Introduction : Pseudo code is a type of informal high-level description of a computer program or…
Q: Which of the following does git add do? For example: git add MyClass.java A. Stages MyClass.java so…
A: The "git add" is a Git command that stages changes to be committed. It adds changes in the working…
Q: What functions do intranets, extranets, and the internet serve in today's workplaces to facilitate…
A: Introduction Intranets are internal networks that are used exclusively by an organization to…
Q: Do you believe Trevor Noah should have been asked the same question on how to protest three times?…
A: Given: Why does Trevor Noah ask about protesting three times? Lahren's response satisfies? Answer.
Q: How to Finding the Optimal Vehicle Routes for a Delivery Problem Explain with code. use a network…
A: Introduction: Vehicle Routing Issue: The Vehicle Routing Problem (VRP) is a graph theory…
Q: What exactly is a dependency diagram, as well as the purpose it serves?
A: A dependency diagram is the graphical display of all tasks in a workflow that are necessary to…
Q: 8.13. In discussing a page replacement algorithm, one author makes an analogy with a snowplow moving…
A: Page replacement: Page replacement algorithm decides which page needs to be replaced when new page…
Q: During the first iteration of the BubbleSort algorithm, how many times does the inner loop execute?
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: Write a function named Cumulative that accepts as a parameter a reference to a vector of integers,…
A: The source code of the function void cumulative(vector<int> &v){ for (int i = 1; i <…
Q: Explanation of three cases when it makes sense to create a secondary key instead of the main one in…
A: The three cases when it makes more sense to create a secondary key instead of using the main key in…
Q: 8.19. The UNIX kernel will dynamically grow a process's stack in virtual memory as needed, but it…
A: The Unix kernel is the central component of a Unix-like operating system. It is responsible for…
Q: To what end does a computer's central processing unit (CPU) work
A: A computer is a digital electronic machine that can be programmed to automatically perform a series…
Q: What does it signify when a Microsoft Excel column is completely stuffed with hashtags?
A: 1. A Database Management system (or DBMS). 2. It is essentially nothing more than a computer-based…
Q: SECI model's concepts of so
A: Solution - In the given question, we have to tell about the SECI model's concepts of socialization…
Q: What is the Big-O of the following? Read code carefully. Q3.1 1 Point n+ 100log n O 0(1) ● O(log n)…
A: Q1. (c) O(n) Q2. (d) O(n^2)
Q: Explaining the need of using firewalls is an important step in maintaining the confidentiality of a…
A: Firewall is a network security device which is used monitor and filters the network traffic whether…
Q: get three numbers and display the number with the highest value.
A: In the given problem, concepts of programming have to be used to get three numbers from the user and…
Q: Can You Explain the Various Components of a Computer?
A: CPU is the brain of the computer. Its main job is to carry out the instructions of computer programs…
CSS
Step by step
Solved in 2 steps

- Explain how the style of an HTML page that makes use of inline style sheets takes priority over the style of the content being shown on that page.99.HTML code to create following table. Also set its border color to “red”. Dislike for incorrect also. . Mm.write HTML 5 code applying the use of headings and style attribute. I want the topic of the site about the University of Jordan groups
- Create and test an HTML document for yourself. This document must use several headings and <em>, <strong>, <hr/>, <p>, and <br /> tags. Need the steps to create a document with the headings.Describe how inline style sheets take precedence over the HTML document's style.Write html code and attach screenshot of form
- Describe the process through which inline style sheets supersede the style of an HTML page.Describe how inline style sheets take priority over the style of the HTML page.when should HTML CODE primarily be used for a webpage? 1) when the background color of an input box needs to be yellow. 2) When the column width of a table needs to be adjusted for a larger screen. 3) when the image for an advertisement needed to be added to a web page 4) when the header for a section need to continuously change size

