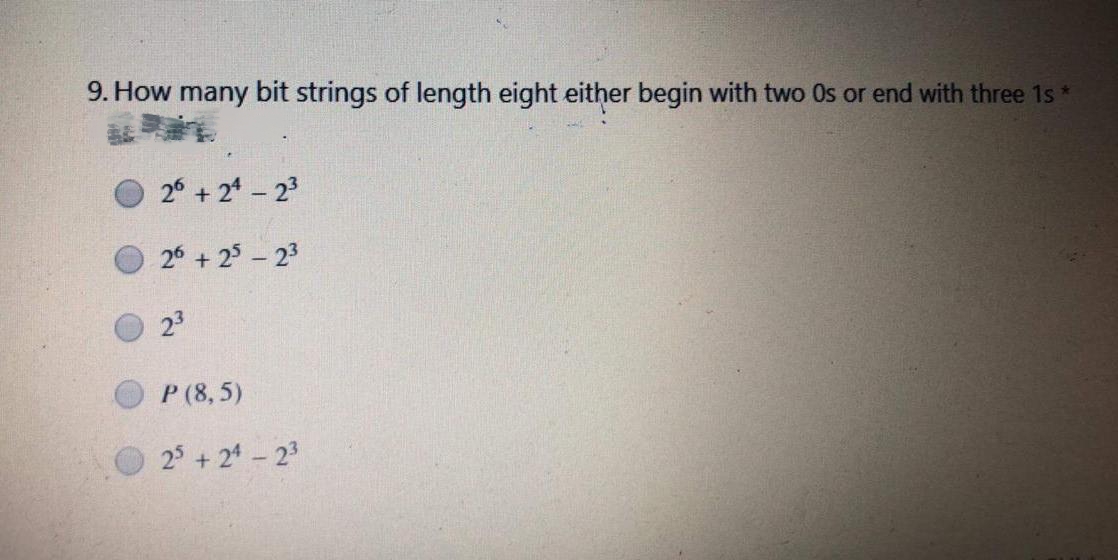
9. How many bit strings of length eight either begin with two Os or end with three 1s* 26 +24-23 26 + 25-23 23 P (8,5) 25 +24-23
Q: Is It Possible to Bring Virtual Reality to Market?
A: Virtual reality: The utilization of computer innovation to establish a reproduced climate that can…
Q: Convert the following Deterministic Finite Automata (DFA) to the equivalent regular expression. க்…
A: DFA (Deterministic finite automata) DFA alludes to deterministic limited automata. Deterministic…
Q: What is the most effective way to backup user data? Your solution has to be proficient, quick, and…
A: Use cloud storage to backup your data One of the greatest ways to backup your data is to buy cloud…
Q: software development projects?
A: The expectations in a product improvement venture can incorporate everything from the underlying…
Q: Please describe the downsides of cloud computing for students and teachers. Can we get out of this…
A: Introduction: The best method for delivering enterprise applications is now cloud computing, which…
Q: The operating system places file blocks on hard drives in a sequential manner. What use does doing…
A: Introduction Start: At the very bottom of the stack is where you will find all of the physical…
Q: Nearly every endpoint operating system is required to be completely transparent while using TCP. Can…
A: A transport layer protocol, TCP stands for Transmission Control Protocol. It is a more connected and…
Q: Name three different types of semiconductor memory and briefly describe each one's key…
A: RAID(Redundant Array of Inexpensive Disks) Redundant Array of Inexpensive Disks, or RAID, is an…
Q: Cost Benefit Analysis (CBA) is a method of economic evaluation and assessment that determines all of…
A: A cost benefit analysis, often known as a CBA, is a method of economic evaluation and assessment…
Q: Which of the following is most likely to be removed at the conclusion of a line? What justifies the…
A: Programmers frequently have to delete whitespaces in order to store only the necessary data and…
Q: 2. Develop a JAVA program which performs all basic arithmetic operations.
A: “Since you have asked multiple question, we will solve the first question for you. If you want any…
Q: Note down the steps we take to stop the system from restarting when the dashboard identifies an…
A: AMI BIOS beeps threetimes means there is a pause and occur when the power on to the computer…
Q: What if a virus was present on your tablet or smartphone? Identify the kind of malware you may be…
A: Malware is a file or piece of software that is intended to do harm. computer code that is generally…
Q: TEST INPUT: I Love C Programming Write a program to count the number of occurrences of any two…
A: Program Plan: In the Main function, do the following: Get a line of text from the user and store it…
Q: Many companies use cloud storage services to house all of their important data. Why do you think…
A: Cloud storage can save several economies. Cloud vendors acquire storage and pass the savings on to…
Q: Using AND gates and OR gates only, the minimum number of gates required to implement the function G…
A: G(A,B,C,D,E,F)=(A+B+C+D)+(A+B+C+E)(A+B+C+F) By Idempotent Law A.A=A B.B=B C.C=C…
Q: What uses of the Internet of Things are now being made? Where did the concept for it originate? .
A: They can do this thanks to software and other technology. actual physical objects (or collections…
Q: With a team of seven to nine individuals working on a large project with a solid architecture and…
A: The answer is given in the below step.
Q: Which forensic recovery techniques are available for data saved on solid-state drives?
A: The technique used by forensic investigators to recover deleted information from solid-state drives…
Q: What are the most recent advancements in information systems, information technology, and…
A: Infrastructure: The outcome of an information field image search for "infrastructure". The purpose…
Q: What role does a security key, sometimes referred to as a trusted platform module (TPM), play in the…
A: Introduction: Encrypting the entire contents of a disc is known as full disc encryption. No one can…
Q: How do you feel about the idea of cloud computing? Do you believe it to be a good idea? Why?
A: Cloud computing is on-demand access to PC assets like data. storage and computing power, without…
Q: What precisely are the distinctions between backup and cloud storage when it comes to online…
A: Here both Date storage and Backup is done on cloud. Cloud Storage basically makes file/Data…
Q: Create a file named method_override.py and follow the following instructions: Take user inputs that…
A: CODE:- class Adult: def __init__(self, name, age, hair_color, eye_color): self.name = name…
Q: You may find out more information about the metrics used in the software development process if…
A: The Answer is in given below steps
Q: Consider the time_slot relation. Given that a particular time slot can meet more than once in a…
A: I have mentioned answer in below step , please find in below
Q: What are some of the advantages and disadvantages of storing your company's data on the cloud for a…
A: Advantages \s Accessibility: accessible over the Internet from any place cloud files may be viewed.…
Q: Why was early Internet research so crucial, and what was its main purpose? Is there a fix for these…
A: Computers all around the globe are connected by a huge global network called the Internet.Why was…
Q: How does the term "interdependence" does it signify specifically in reference to system concepts?…
A: Introduction: Interdependence defines the international system. Despite its obscurity,…
Q: The Internet is often used as an example of a disruptive technology because of the significant…
A: The Internet connects billions of gadgets and those using a standardized set of rules (called…
Q: Is it possible to assess the quality of software when the customer often changes what the product is…
A: Check the following statement to see whether it's true: Is it really feasible to evaluate the…
Q: why is a work breakdown structure important? Do you need to use the software development lifecycle…
A: The above question is solved in step 2 :-
Q: Do you believe that the production of the final product is the most crucial step in software…
A: No, As First For building software requirements are to be clearly understand and what and how that…
Q: For the language L = {anbm:n,m ≥ 0, n ‡ m} a) Generate CFG grammar for L b) convert the grammar from…
A: Below I have provided the solution to the given grammar
Q: A Voltage Event Recorder is a device used to keep track of voltage changes.
A: Your answer is given below.
Q: To what extent do you believe it is possible to foresee the factors that may cause an information…
A: Introduction: Developing a system for information: Information System Design is used to fulfil the…
Q: What exactly does it mean to have a virtual drive? When does it occur, and what triggers it? Please…
A: A trigger is a collection of SQL statements with particular names that are stored in system memory.…
Q: Describe the several Windows versions that are available, including the important and novel features…
A: In 1981, Microsoft released the MS-DOS operating system. The default operating system for…
Q: javascript
A: function edit() { var code = prompt("Enter the unique code"); if (code == user.random-generated…
Q: Give an example of how a packetized data stream and a firewall are similar
A: Option 1 is the right choice in the introduction. Important Points With the source Routing Feature,…
Q: Doesn't it make sense to briefly highlight the two most vital aspects of an OS?
A: Operating system An operating system is a piece of software that controls and keeps up with…
Q: To what extent do you believe it is possible to foresee the factors that may cause an information…
A: Making an information system: Information System Design is used to complete the task. A project is…
Q: Describe the several Windows versions that are available, including the important and novel features…
A: In 1981, Microsoft released the MS-DOS operating system. The default operating system for…
Q: Which technological advancements in information systems, IT infrastructure, and information…
A: Introduction: The facilities and services that a country's infrastructure consists of business need.…
Q: By employing a firewall, your computer is shielded from possible outside attacks. It's crucial to…
A: A firewall acts as a network's gatekeeper by prohibiting unauthorized users from accessing or…
Q: Please describe the negative effects of cloud computing on teachers and pupils. Exists a way out of…
A: The above question is solved in step 2 :-
Q: Construct an AVL tree by inserting following nodes: 35, 50, 40, 25, 30, 60, 78, 20, 28
A: Dear Student, The AVL trees are height-balancing binary search trees. The AVL tree ensures that the…
Q: Modify the following program to which you have to add the amplitude (A) frequency (f) energy (E)…
A: In Step 2, I have provide above code ( error free ) with output screenshot------------- In Step 3,…
Q: Which forensic recovery techniques are available for data saved on solid-state drives?
A:
Q: In K-map, you might find some cells filled with the letter d (or X). This d is called “Don’t care”.…
A: In order to achieve the best result, it may be required to replace the d's with the following…
5
Step by step
Solved in 2 steps

- Can you tell me how many address bits are required for 1024K words?What is the minimum number of address bits required to represent 1024K words with no additional information?55. Suppose a digitized voice channel is made by digitizing 8 kHz bandwidth analog voice signal. It is required to sample the signal at twice the highest frequency (two samples per hertz). What is the bit rate required, if it is assumed that each sample requires 8 bits? a. 32 kbps b. 64 kbps c. 128 kbps d. 256 kbps
- Consider the following segment table (all expressed and addressed in bytes) Segment Base Length 0 500 1000 1 4500 1500 2 7000 3000 3 11000 2400 4 15000 875 What are the physical addresses for the following logical addresses? a. 0,430 b. 1,1520 c. 2,500 d. 3,400 e. 4,11201. Compact discs record two channels (left and right) of music at a sampling frequency of ??=44.1kHz for each channel. If each sample is encoded with 16 bits, and one byte is 8 bits, how many bytes are required to store 48.1 seconds of music? 2. Consider a system that uses 8-bit ASCII codes to encode letters. How long (in microseconds) will it take to transmit the bit sequence encoding Hello-World! if we use a bit time of 4 samples per bit, and transmit samples at a rate of 1MHz? 3. The ASCII table below gives the ASCII codes for common alphanumeric characters and symbols listed from MSB to LSB. What is the bit sequence encoding the message 113? Assume that we transmit the codes of each character in sequence with the LSB first.Consider the 64-bit binary number 11010000 00000100 00001000 00000101 10001001 00110000 10000001 00000001, stored in the doubleword with address 2000. For big-endian architecture, what value is stored in byte 2004?

