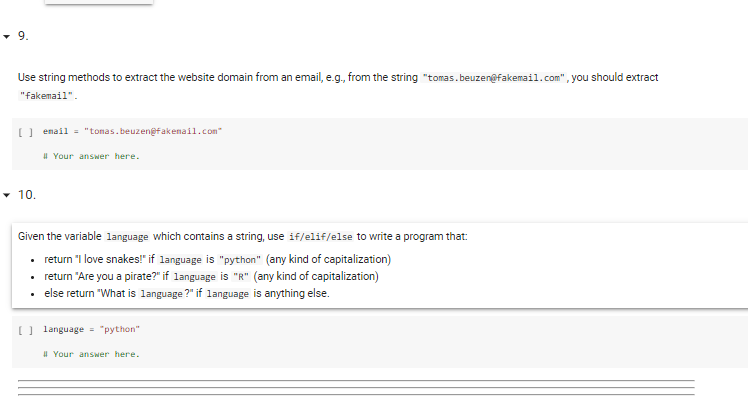
- 9. Use string methods to extract the website domain from an email, e.g., from the string "tomas.beuzenefakemail.com", you should extract "fakemail". ) email = "tonas.beuzenefakenail.com I Your answer here.
Q: For the SIC/XE object code given below in hexadecimal format, answer the question that follows SICXE...
A: 1) Instruction format is format 3 instruction since it is 3 bytes because the given object code 754...
Q: What is the value of a good reputation?
A: Introduction: Reputation: A person's subjective qualitative belief in a brand, person, organisation,...
Q: An incident response (IR) is a set of activities aimed at anticipating, detecting, and resolving the...
A: Incident Plan: The primary goal of an Incident Response Plan is to provide prompt assistance in the ...
Q: Read the string "I am James Bond" and assign it to a variable a. Count the length of string. Count t...
A: #1.a = input()#Count the length of string.length = len(a)print("Length:", length)#Count the occourna...
Q: Give regular expressions that describe the following languages containing the set of all strings ove...
A: A.) { w | w a word in which 3rd symbol from RHS is ‘a’ and 2nd symbol is 'b' }. aaa , aab , aaab , a...
Q: Consider the following flow in the s, t-network D. 5,1 3,0 10,1 10,5 6,2 7,4 4,3 8,6 2,1 3,1 4,2 (a)...
A: According to the information given:- We have to have to find the flow is feasible and maximum flow a...
Q: Use a request for proposal to gather information on hardware and system software, and explain why it...
A: A request for proposal (RFP) is a document that asks vendors to submit proposals for hardware and sy...
Q: As CISO, you are in charge of developing an information security programme that is backed by a frame...
A: Information security program consists of 3 principles:confidentialityintegrityavailability:We will h...
Q: What is the difference between embedded computers and general-purpose computers?
A: Given: We have to discuss What are the fundamental differences between embedded and general-purpose ...
Q: In a DDS, what is stored in ROM?
A: DDS stands for Direct Digital Synthesis DDS is a frequency Synthesizer technique and enhancing the ...
Q: Discuss a concurrent processing issue in an operating system.
A: Introduction: Concurrent processing is a kind of processing in which numerous processors work togeth...
Q: Is it easier for you to identify someone using their fingerprints, speech intonation, face features ...
A: INTRODUCTION: Individuals may be uniquely identified via the use of biometrics, which are measures o...
Q: (a). Computers understands human instructions using low-level machine codes. Machine codes are actua...
A: C++ code to convert decimal number to binary: #include <bits/stdc++.h>using namespace std; i...
Q: What are the 3 main regions of a process in user space memory regions? What are the 3 main component...
A: Asked:- The three main regions of a process in user space memory regions. The three main components...
Q: What are the disadvantages of using the SSTF disc scheduling algorithm?
A: Here in this question we have asked that what are the disadvantage of SSTF disk scheduling algorithm...
Q: Write a program that asks the user for a negative number, then prints out the product of all the num...
A: Solution: Since any specific language for the above question is not mentioned, we have solved thi...
Q: Exercise 2: Write a program that calculates the cost per square inch of a circular pizza, given its ...
A: import java.util.*;import java.text.*;public class Main { public static void main(String[] args) { ...
Q: Create a list – l1 with element 1,2,3,4,5. Convert this list into an array name ar. What is the dime...
A: The solution is given below for the above given question:
Q: What's the difference between symmetric and asymmetric key cryptography?
A: Cryptography is a process of securing the information while transferring the data from sender to rec...
Q: Which search engines are lawful and ethical?
A: Introduction: Which search engines are lawful and ethical?
Q: Flow chart and User Interface design ("Prototype") for snake and ladders: Functional requirements: ...
A: Write user interface design and flowchart of snake and ladder game.
Q: Use a request for proposal to gather information on hardware and system software, and explain why it...
A: Request for Proposal (RFP) is an acronym for Request for Proposal. RFPs for construction and cleanin...
Q: What is wrong with the following HTML code segment: Lorem ipsum dolor sit amet, consectetur adipis...
A: 1. If you want that the line after comma will appear in the next line then you have to use the break...
Q: Why isn't virtual memory utilised more often in embedded systems?
A: Virtual memory: Virtual memory is a layer of indirection. The use of virtual memory in OS can load p...
Q: What are the different stages of the overall structural testing procedure?
A: Given Write about different level of structural testing procedure.
Q: Use f_strings to output variables. This program requires the main function and a custom value-return...
A: Code: from tabulate import tabulate import randomrandomlist = []for i in range(0,50): n = random....
Q: It's exactly what it sounds like: a jump drive.
A: There are many devices which are used to store information. Jump drive is one of them. It is highly...
Q: Computer Science Using C++ Write a template function called insertElement that given a value a...
A: In the function array A it will insert the given value into the sequence so that the sequence remain...
Q: In terms of emphasis, what distinguishes the TPC from the SPEC?
A: Answer: Instead of focusing just on performance, TPC assesses the following features of a system: r...
Q: Computer Science Please answer the following question: A person would like to renew his c...
A: Three types of risks encountered during own web application development project Budget Risk:- Budge...
Q: Convert the numeral to a numberal in base ten BBB7 sixteen
A: BBB716in decimal ANS :- 4805510
Q: A social network company called Feta makes its profit t know whether in a group of people there is s...
A: The algorithm is about a social network company called Feta which makes its profit by spreading rumo...
Q: Script 1: create a JavaScript program that defines, as an array, a list of 10 of your favorite thing...
A: Note: I have given answered as asked in the question Solution: forEach: The name itself says each wh...
Q: In a field where an expert system could help you, provide at least five rules for the knowledge base...
A: Introduction: Working memory is a limited capacity cognitive apparatus that can briefly store inform...
Q: What exactly is cybersecurity, and why is it so important?
A: Introduction: Cybersecurity is important because it protects all types of data from theft and loss. ...
Q: Variables
A: Given: What are Variables?
Q: Write an SQL query to report the movies with an odd-numbered ID and a description that is not "borin...
A: 1. To get moving we use where clause with condition and order by. 1. first we filter id by MOD inbu...
Q: Explain why, in MARIE, the MAR is 12 bits wide and the AC is 16 bit wide.
A: MARIE: Machine Architecture that is Really Intuitive and Easy, is a simple architecture consisting o...
Q: A list of five common network topologies should be included. Which one do you think is the most trus...
A: Answer : Network Topology : The arrangement of the network w...
Q: Given that both cache memory and random access memory (F unclear why cache memory is required becaus...
A: given - Given that both cache memory and random access memory (RAM) are transistor-based, it'sunclea...
Q: Write a program, in python, that checks if the last data item entered appears earlier in the list. O...
A: Answer: I have done code and also I have attached code and cod screenshot as well as output
Q: 1. Files and folders; we all use them today on our varying computer devices. Discuss two reasons to...
A: Given The answer is given below,
Q: Filter programmes such as sed and awk are often used to format data in pipelines. Is this a true or ...
A: Explaination As the name suggest filter programs . We already know what is filtering right ? Filter...
Q: We believe Flynn's taxonomy should be expanded by one level. What differentiates a higher-level comp...
A: Introduction: Michael J. Flynn developed Flynn's taxonomy in 1966, a categorization of computer arch...
Q: 2. Decode (get base 10 value of) the following bit patterns using the floating-point format describe...
A:
Q: Prove this by vsing the truth tuble ) Zェ+スjェ=まえ+お ) xyt元ス+ま =2y+正送 Ce) ey+てそ = C2+z](元+y)
A: As per our company guidelines, we are not supposed to answer more than one question per post and kin...
Q: You need to show detail work on how you get the answer. Dont use answers from other websites please...
A:
Q: A list of five common network topologies should be included. Which one do you think is the most trus...
A: Introduction: The arrangement of a network's connections and nodes, or its topology, is referred to ...
Q: نقطة واحدة Press the key on your .10 keyboard to delete text to the left of the insertion point 1. D...
A: let's see the correct step by step solution
Q: What is a distributed denial of service attack, and how can it be carried out by a single individual...
A: DDoS (distributed denial of service) attack: Following the discovery of the limits of single-system ...
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 2 images

- Mad Libs are activities that have a person provide various words, which are then used to complete a short story in unexpected (and hopefully funny) ways. Write a program that takes a string and an integer as input, and outputs a sentence using the input values as shown in the example below. The program repeats until the input string is quit and disregards the integer input that follows. Ex: If the input is: apples 5 shoes 2 quit 0 the output is: Eating 5 apples a day keeps you happy and healthy. Eating 2 shoes a day keeps you happy and healthy.Assume nextWord is a String variable that has been given a String value that is entirely made up of letters. Create Java code that displays the message "First half of the alphabet," assuming that nextWord comes before "N" in alphabetical sequence. If nextWord does not precede "N" in alphabetic ordering, the code should output "Second half of the alphabet". (Note that "N" uses double quotes to produce a St Answer 117Mad Libs are activities that have a person provide various words, which are then used to complete a short story in unexpected (and hopefully funny) ways. Write a program that takes a string and an integer as input, and outputs a sentence using the input values as shown in the example below. The program repeats until the input string is quit and disregards the integer input that follows. Ex: If the input is: apples 5 shoes 2 quit 0 the output is: Eating 5 apples a day keeps the doctor away. Eating 2 shoes a day keeps the doctor away. user_text word = "" while True:user_text = input().split()word = (user_text[0])if word == 'quit':breaknumber = (user_text[1]) print('Eating {} {} a day keeps the doctor away.'.format(number, word))
- Mad Libs are activities that have a person provide various words, which are then used to complete a short story in unexpected (and hopefully funny) ways. Write a program that takes a string and an integer as input, and outputs a sentence using the input values as shown in the example below. The program repeats until the input string is quit and disregards the integer input that follows. Ex: If the input is: apples 5 shoes 2 quit 0 the output is: Eating 5 apples a day keeps the doctor away. Eating 2 shoes a day keeps the doctor away.Q2) Write a program that reads a one-line sentence as input and then displays the following response: If the sentence ends with a question mark (?) and the input contains an even number of characters, display the word "Yes". If the sentence ends with a question mark and the input contains an odd number of characters, display the word "No". If the sentence ends with an exclamation point (!), display the word "Wow". In all other cases, display the words " you always say "followed by the input string enclosed in quotes" ". Your output should all be on one line. Be sure to note that in the last case, your output must include quotation marks around the echoed input string. In all other cases, there are no quotes in the output. Your program does not have to check the input to see that the user has entered a legitimate sentence. Sample Input#1: Please enter a one line question or statement. How are you? Sample Output#1: Yes Sample Input #2: Please enter a one line…French Articles: French country names are feminine when they end with the letter e, masculine otherwise, except for the following which are masculine even though they end with e: le Belize le Cambodge le Mexique le Mozambique le Zaïre le Zimbabwe Write a program that reads the French name of a country and adds the article: le for masculine or la for feminine, such as le Canada or la Belgique. However, if the country name starts with a vowel, use l’; for example, l’Afghanistan. For the following plural country names, use les: les Etats-Unis les Pays-Bas
- capCount.py make a program called capCount.py that has a function that takes in a string and prints the number of capital letters in the first line, then prints the sum of their indices in the second line. The string "hEllo, World" would should look like this: 28InitialsWrite a python program that gets a string containing a person’s first, middle, and last names, anddisplays their first, middle, and last initials. For example, if the user enters John William Smith,the program should display J. W. S.Help? Using python, write a program that lets the user enter a string and displays the character that appears most frequently in the string. Should i start with string lower?
- Need Python code: Mad Libs are activities that have a person provide various words, which are then used to complete a short story in unexpected (and hopefully funny) ways. Write a program that takes a string and an integer as input, and outputs a sentence using the input values as shown in the example below. The program repeats until the input string is quit and disregards the integer input that follows. Ex: If the input is: apples 5 shoes 2 quit 0 the output is: Eating 5 apples a day keeps the doctor away. Eating 2 shoes a day keeps the doctor away. Thankspublic static String pancakeScramble(String text) This nifty little problem is taken from the excellent Wolfram Challenges problem site where you can also see examples of what the result should be for various arguments. Given a text string, construct a new string by reversing its first two characters, then reversing the first three characters of that, and so on, until the last round where you reverse your entire current stringUSE SCHEME IN DRRACKET.In the language of an alien race, all words take the form of Blurbs. A Blurb is a Whoozitfollowed by between zero or more Whatzits. A Whoozit is the character 'x' followed bybetween one or more 'y's. A Whatzit is a 'q' followed by either a 'z' or a 'd', followed by aWhoozit. -The program should ask the user to “Enter an alien word:”, read the inputas a string, and check whether or not it is a valid word (Blurb). If it is valid, it prints"The word is fine.", otherwise it prints "The word is a mess!". -The program should loop and ask the user for new input until they enter avalid blurb.For Scheme, it is suggested that you review the “input_and_output.rkt” sample program from the first module on functional programming. This program shows how to perform a “loop” that reads in data and processes it. You may find the following forms useful: a. (read) to read a string b. (string->list) to convert the string into a list of characters, c. (display “Hello”) to write…



