_1. It is the core of computer security in all aspect. _2. True or False. Securing program is a difficult task and it's really required a professional personnel with high level of experience. _3. A fault that occurs only intermittently and can be much more difficult to diagnose.
_1. It is the core of computer security in all aspect. _2. True or False. Securing program is a difficult task and it's really required a professional personnel with high level of experience. _3. A fault that occurs only intermittently and can be much more difficult to diagnose.
Database System Concepts
7th Edition
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Chapter1: Introduction
Section: Chapter Questions
Problem 1PE
Related questions
Question
The question is in the image below.
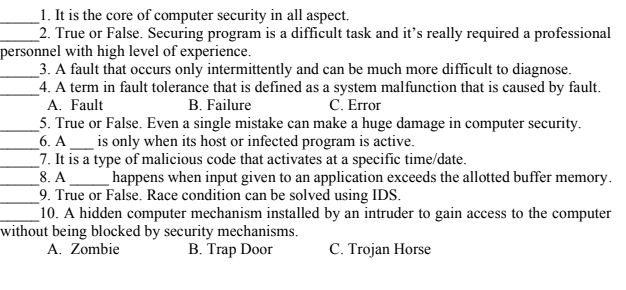
Transcribed Image Text:_1. It is the core of computer security in all aspect.
_2. True or False. Securing program is a difficult task and it's really required a professional
personnel with high level of experience.
_3. A fault that occurs only intermittently and can be much more difficult to diagnose.
_4. A term in fault tolerance that is defined as a system malfunction that is caused by fault.
A. Fault
_5. True or False. Even a single mistake can make a huge damage in computer security.
6. A__ is only when its host or infected program is active.
7. It is a type of malicious code that activates at a specific time/date.
8. A
_9. True or False. Race condition can be solved using IDS.
10. A hidden computer mechanism installed by an intruder to gain access to the computer
without being blocked by security mechanisms.
A. Zombie
B. Failure
C. Error
happens when input given to an application exceeds the allotted buffer memory.
B. Trap Door
C. Trojan Horse
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:
9780133976892
Author:
Paul J. Deitel, Harvey Deitel
Publisher:
PEARSON

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781337627900
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:
9780073373843
Author:
Frank D. Petruzella
Publisher:
McGraw-Hill Education