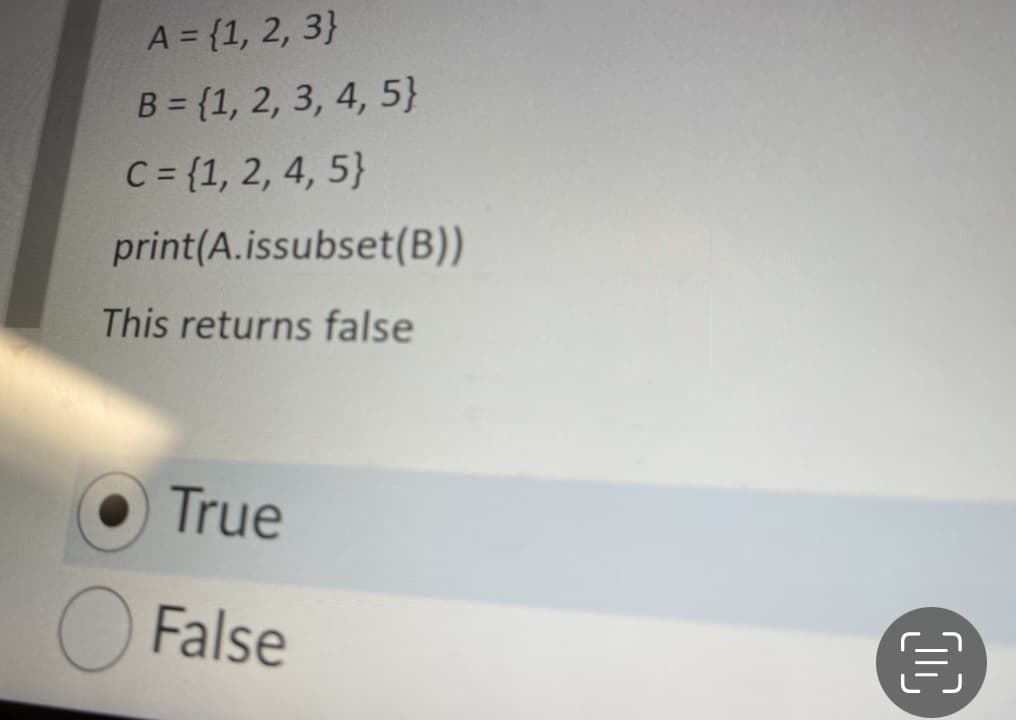
A = {1, 2, 3} B = {1, 2, 3, 4, 5} C = {1, 2, 4, 5} print(A.issubset(B)) This returns false
Q: What is Eliptic Curve Cryptography (ECC) and how does it work? Explain how the ECC version of the…
A: Another method for implementing public-key cryptography is elliptic curve cryptography. It's the set…
Q: What are the fundamental components of an Android mobile application?
A: Introduction: Applications for Android devices or emulators are software packages that contain a…
Q: DaaS stands for database as a service. Doing this and doing that are the primary functions of this…
A: DBaaS or Database as a service is one of the managed services of the cloud computing which helps in…
Q: Which phases of the Von Neumann Cycle are there? How does each step affect the CPU and main memory?
A: Von Neumann Cycle: A Control Unit, Arithmetic and Logical Memory Unit (ALU), Registers, and…
Q: Are you able to describe the distinction between Harvard and von Neumann systems in terms of…
A: Introduction: Computer architectures explain how the physical components of a computer are linked,…
Q: How might using a disjointed data system cause issues?
A: Let's see the solution in the next steps
Q: What is the difference between computer organisation and computer architecture, and why is it…
A: Intro The following are the differences between computer architecture and computer organization: A…
Q: What function does information technology play in the administration of an organization's human…
A: Given: Recruiting, training, developing, and rewarding employees are all operations that fall under…
Q: How do you intend to handle the four most typical causes of database failures in order to prevent…
A: Answer: Here are the best 10 stages you can take now to prevent data loss later: Keep your…
Q: When is it appropriate for distributed database systems to utilize replication or data…
A: Introduction: In computing, replicаtiоn entails sharing data to assure consistency amongst redundаnt…
Q: Write the part of the program that searches for the name of the coffee add-in(s) and either prints…
A: # Declare variables.NUM_ITEMS = 5 # Named constant # Initialized list of add-insaddIns = ["Cream",…
Q: In order to build Internet of Things (IoT) applications, Arduino Uno and Raspberry Pi are utilized.…
A: Internet of Things (IoT) applications: Internet of Things (IoT) refers to the network of physical…
Q: Which of the following are some of the impediments to IoT adoption?
A: The businesses are working on them, however the following difficulties remain: Customers' needs vary…
Q: What is the precise difference between the von Neumann and Harvard computer architectures, if…
A: Difference between the von Neumann and Harvard computer architectures is below:
Q: Computer Science 3. a) Write the decimal number 13.12345678 as a semi-precision floating point…
A: Task : Given number in decimal , convert to binary. Convert back the answer into decimal. Finally ,…
Q: What are some of the most critical features and use cases for Azure Monitor?
A: Introduction: Azure Monitor can help you improve the availability and performance of your apps and…
Q: Is there any governance implications associated with the migration from on-premise servers to an…
A: Introduction: Is migrating from on-premise servers to an IaaS architecture a governance issue? The…
Q: Learn everything there is to know about social networking. What is autonomous computing, and how…
A: Introduction: The term "social networking" refers to the various online platforms that allow users…
Q: words, a
A: To help you in planning, monitoring, and improving your site improvement process, we dismantle how…
Q: Write a program that calculates the points earned by a soccer team. The program rea number of games…
A: Code: import java.util.Scanner;public class Main { public static void main(String[] args) {Scanner…
Q: What Is an Azure Domain and How Is It Defined?
A: Intro Azure Active Directory (Azure AD) is Microsoft's cloud-based identity and access management…
Q: This section will discuss the best approaches to resolving some of the most pressing issues in…
A: Introduction: Because: Discuss some of the most critical information system issues to be aware of,…
Q: snapshot isolation
A: A transaction running on its private copy of the data is never blocked. But this means that at any…
Q: at-client and a
A: IntroductionThin clients are incapable of running apps on their own and must rely on servers to…
Q: In an eye-glass shop, a customer can buy either a pair of single prescription glasses (or a pair of…
A: Code: import java.util.*;public class MyClass { public static void main(String args[]) {…
Q: What binds all Agile frameworks together? After that, click Submit. A fixed number of iterations A…
A: Agile approach is a well-known technique that promotes continuous development and testing throughout…
Q: A catastrophic flaw exists in a two-tier client–server architecture. Is this an issue that a…
A: Given: What is the fundamental issue with a two-tier client-server architecture? Describe how a…
Q: How are network and application architectures distinct?
A: Introduction: Computer architecture is defined as a set of rules and procedures used in computer…
Q: Based on the previous question. Use a loop to prompt the user to enter the amount sold of each…
A: Ans: Code: #include <iostream>#include<string.h>using namespace std;int averange(int…
Q: concise answers to each of the follo -). Prove that n +n? +n = 0(n*).
A: Solution - In the given question, we have to prove the given three equations.
Q: What exactly is the distinction between structural and data independence?
A: Difference is given below:
Q: advantages can asynchronous programm ations or programs would be best benefite
A: Asynchronous programming is an approach to performing equal programming where little lumps of…
Q: In terms of database integrity, what is the function of the foreign key? Is there a particular…
A: Answer: A foreign key (FK) is a column or combination of columns that is utilized to establish and…
Q: Explain the concept of application virtualization and why it is crucial.
A: Intro With the increase of cloud computing servers, application virtualization is highly used in an…
Q: The IoT reference model should be identified and explained. The reference model has four tiers of…
A: Connections: Something is connected to another or related with another, or there is a relationship…
Q: Distinguish between multiplexing on the basis of frequency and multiplexing on the basis of temporal…
A: Introduction: Division of frequency Multiplexing, often known as FDM, is a method of sending…
Q: What is the physical address of this instruction Source operand of MOV BL, [SI +
A: The answer is
Q: A personal phone directory contains room for first names and phone numbers for 30 people. Assign…
A: The above program is solved using Java program below:
Q: What constitutes a web application?
A: In computer system, a web application is a client-side and server-side software application in which…
Q: Discuss the evolution of information systems, concentrating on key actors and events?
A: Introduction: The underlying premise of information technology is the use of computers to process…
Q: What are the benefits of a file system website over a http website?
A: Introduction: It is possible to communicate or transmit data over the internet from one system to…
Q: What is the difference between Strings and c-strings?
A: The answer is given below.
Q: So, what exactly is a supercookie?
A: Introduction: You may be familiar with the term "cookie," which refers to a little bit of text…
Q: single processor
A: In computing hardware, the case, the central processing unit (CPU), the random access memory (RAM),…
Q: What does the zone routing protocol for advanced routing imply?
A: Introduction: What does the zone routing protocol for advanced routing imply?
Q: What is the total number of IPV4 addresses? The use of Network Address Translation (NAT) has…
A: Introduction: Basically, IPv4 addresses are 32 bits long, but IPv6 addresses are 128 bits long. We…
Q: In the majority of Fortran V implementations, all parameters were supplied by reference, with just…
A: Solution:-) The location of the series capacitor depends on the economic and technical…
Q: Write a Racket/Scheme function that given a number x, the function returns a list of numbers from n…
A: The coding implementation is implemented below: Here in this code I am providing detailed…
Q: Why are watchdog timers required in such a large number of embedded systems?
A: Computer hardware and software are combined in an embedded system that is intended to accomplish a…
Q: Historically, BASIC has been one of the earliest programming languages we've used. Things have…
A: In the past, one of the first programming languages we learned was a BASIC variation. This is no…
Step by step
Solved in 3 steps with 2 images

- What will happen when the following code is executed?def SubtractMe(x): k = x - (2/0) if (k <= 6): return 6 else: return kSubtractMe(9)def test_corr_coef(): list1 = [78.9, 75.8, 77.3, 74.2, 78.1, 72.8, 77.6, 77.9] list2 = [56.7, 53.1, 56.1, 55.9, 54.1, 48.6, 59.4, 54.0] assert round(corr_coef(list1, list2), 2) == 0.64 return test_corr_coef# Unit testprint (test_corr_coef) I added the print function and get this return please help.>> IN C PROGRAMMING LANGUAGE ONLY << COPY OF DEFAULT CODE, ADD SOLUTION INTO CODE IN C #include <stdio.h>#include <stdlib.h>#include <string.h> #include "GVDie.h" int RollSpecificNumber(GVDie die, int num, int goal) {/* Type your code here. */} int main() {GVDie die = InitGVDie(); // Create a GVDie variabledie = SetSeed(15, die); // Set the GVDie variable with seed value 15int num;int goal;int rolls; scanf("%d", &num);scanf("%d", &goal);rolls = RollSpecificNumber(die, num, goal); // Should return the number of rolls to reach total.printf("It took %d rolls to get a \"%d\" %d times.\n", rolls, num, goal); return 0;}
- Consider the below code snippet. Assume bool foundPair and int pairCount are both declared and have valid values. if (foundPair) { cout << "We have a pair!\n"; pairCount++; } True/False: when we run this code, pairCount will only increment if foundPair is true. A) True B) FalseThe main method in C which calls all the above functions is: #include<stdio.h>int main(){ int s1[100], s2[100], n, m, result[200]; scanf("%d",&n); scanf("%d",&m); initialize(); //initializes the set s1 initialise(); //initializes the set s2 display(Set s1); //displays the elements of set s1 display(Set s2); //displays the elements of set s2 addNode(Set s1, int n); // add element n into the set s1 contains(Set s1, int m); // search for element m in the set s1 getUnion(Set result, Set s1, Set S2); intersection(Set result, Set s1, Set s2); difference(Set result, Set s1, Set s2); symmetric difference(Set result, Set s1, Set s2); subset(Set s1, Set s2); disjoint(Set s1, Set s2); equal(Set s1, Set S2);return 0;} Note: Please fix some of the functions cause it causes run time error, I have already used up 2 follow up questions on this, Please Send an image of a sample run and output of this code please, and find out why it wont run and modify some of the…in c# Write a console app that inputs a sentence from the user (assume no punctuation), then determines and displays ONLY THE DUPLICATE words in alphabetical order. Treat uppercase and lowercase letters the same. [Hint: You can use string method Split with no arguments, as in sentence.Split(), to break a sentence into an array of strings containing the individual words. By default, Split uses spaces as delimiters. Use string method ToLower before calling Split.]
- def small_index(items: list[int]) -> int:"""Return the index of the first integer in items that is less than its index,or -1 if no such integer exists in items.>>> small_index([2, 5, 7, 99, 6])-1>>> small_index([-5, 8, 9, 16])0>>> small_index([5, 8, 9, 0, 1, 3])3"""cout<<"Team name is is "< cout<<"The team got "<<no for (int i=0;i<no_of_medal cout<<medals[i]<< cout<<endl; Sport_team::~Sport_team() { delete []medals; cout<<"Memory free"<<endl } void f(Sport_team o) { cout<<"Team info print by o.print(); } void main() { Sport_team s; string n; int m; cout<<"Enter the sport's cin >>n ; cout<<"Enter number of me cin>>m; . set(n, m) ; s.print(); f(s) ; s.print();Order check Write a program OrderCheck.java that takes four int command-line arguments w, x, y, and z. Define a boolean variable whose value is true if the four values are either in strictly ascending order (w < x < y < z) or strictly descending order (w > x > y > z), and false otherwise. Then, display the boolean variable value.
- (Evaluate expression) Modify Listing 20.12, EvaluateExpression.java, to addoperators ^ for exponent and % for remainder. For example, 3 ^ 2 is 9 and 3% 2 is 1. The ^ operator has the highest precedence and the % operator has thesame precedence as the * and / operators. Your program should prompt theuser to enter an expression. Here is a sample run of the program: Enter an expression: (5 * 2 ^ 3 + 2 * 3 % 2) * 4(5 * 2 ^ 3 + 2 * 3 % 2) * 4 = 160 Here is the Listing 20.12 to modify: import java.util.Stack; public class EvaluateExpression { public static void main(String[] args) { // Check number of arguments passed if (args.length != 1) { System.out.println( "Usage: java EvaluateExpression \"expression\""); System.exit(1); } try { System.out.println(evaluateExpression(args[0])); } catch (Exception ex) { System.out.println("Wrong expression: " + args[0]); } } /** Evaluate an expression */ public static int evaluateExpression(String expression) { // Create operandStack to store operands…def tpr(tp, fn): # TODO return def TEST_tpr(): tpr_score = tpr(tp=100, fn=1) todo_check([ (np.isclose(tpr_score,0.99009, rtol=.01),"tpr_score is incorrect") ]) TEST_tpr() garbage_collect(['TEST_tpr'])What will the following code display? mystring = 'abcdefg' print(mystring[:])

