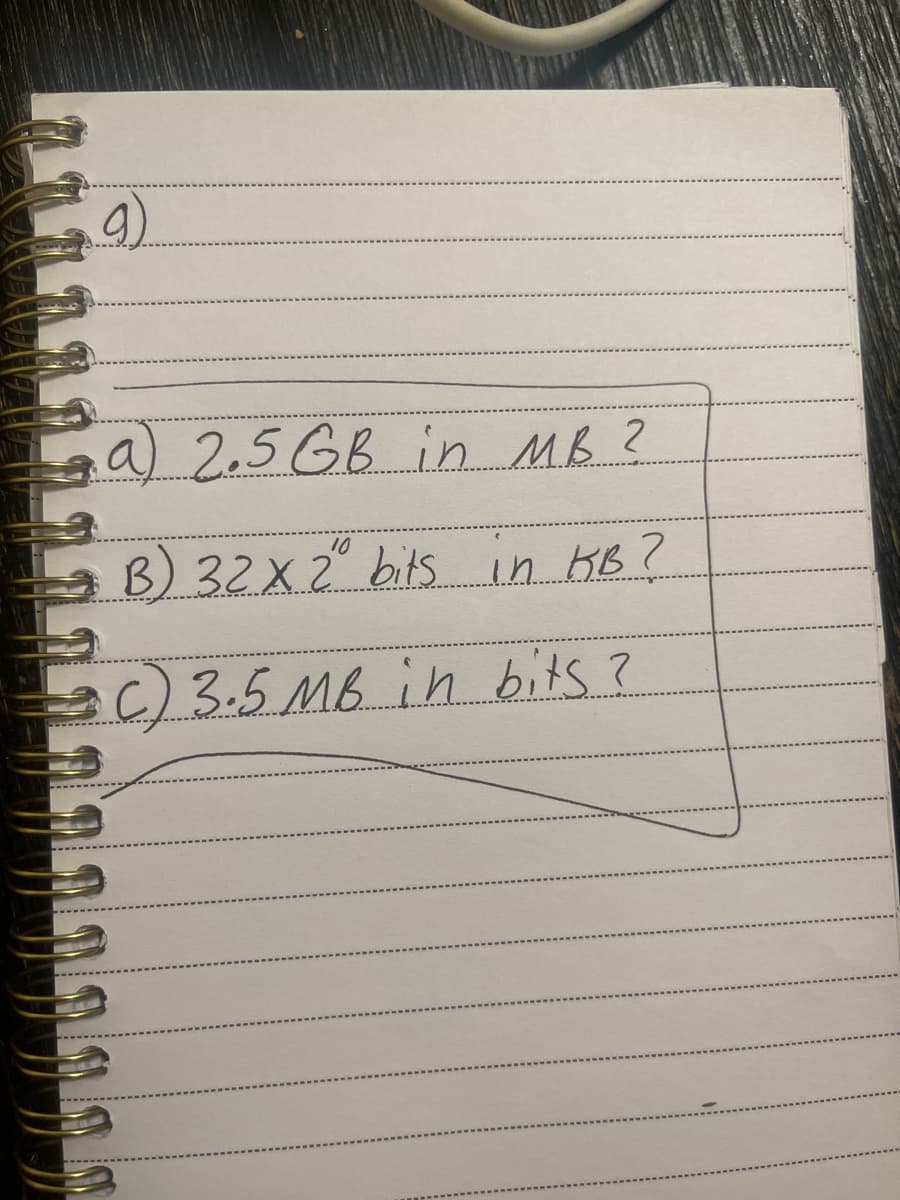
a 2.5 GB in MB ? 10 = B) 32X 2" bits in KB? :C) 3.5 MB in bits ?
Q: What defines a transitive dependency in a database table? A. One non-key attribute is…
A: Defined a transitive dependency in a database table
Q: Write a python program to get a string as input from the user and print the third character from the…
A: We will write a python code which will prompt the user to input a string and then print the third…
Q: How does MVC fit into the broader web application framework? What are the advantages of an MVC…
A:
Q: RAM and Register refer to two different types of memory.
A: RAM Stands For Random Access Memory.
Q: rite two user epics with persona and one scenario associated with each. Epic,Persona and Scenario 1…
A: Epic reprsents the whole story or in other words whole functioning of the website that assist people…
Q: Explain with example The Updated Node Class for Adding Doubly Linked List Support.
A: r node class now has the ability to track the next element in the container as well as the previous…
Q: What does it mean to say "information technology"?
A: IT solution: IT encompasses all company computer usage. Information technology builds firm…
Q: A database administrator is necessary to guarantee proper operation. What does this mean exactly?…
A: Any company's IT department needs a database administrator, especially those that work with…
Q: Are you acquainted with a database administrator's responsibilities?
A: Data is stored and managed by database administrators using dedicated software. Tasks like designing…
Q: What information must a set of instructions include? Provide a brief overview of the SRC.
A: Set Of Instructions: The instruction set is a computer's programming. Instruction set tells the…
Q: Create a summary of the adoption of agile based on annual surveys and surveys funded by agile…
A: Introduction: Agile approach is a concept that encourages continuous development and testing…
Q: In order for a distributed database to function correctly, what are the key differences between a…
A: Given: we have discuss In order for a distributed database to function correctly, what are the key…
Q: Create the gray code representation of the following binary numbers. i) 11101 ii) 01101 iii)…
A: Binary code:- base is two. Gray code:- unit distance code. apply x-or operation.
Q: Adding a level to Flynn's taxonomy would be beneficial, in our opinion. What differentiates premium…
A: start: We propose adding one level to Flynn's taxonomy. What is it about computers at this level…
Q: What is the purpose of the Data Definition Language? What can I do to assist you?
A: Data Definition Language: SQL commands that construct and delete locations, databases, and database…
Q: What is the objective of debugging and how does it operate? What does this have to do with testing??
A: What is debugging? What exactly is the connection to the testing? Answer: Finding and fixing errors…
Q: What distinguishes database programming from other languages? What specific examples can you provide…
A: Introduction: Every database management system has management and administrative features. It states…
Q: What is the Search for Extraterrestrial Intelligence (SETI) and how can the distributed computing…
A: Answer is in next step.
Q: What risks are involved in moving databases from one server to another?
A: Potential for Data Loss Data loss may occur at any point in the data migration process. Some data…
Q: Using Python code, write a program to compute (and output to the screen) the (total) amount of water…
A: First Generate a random number between 60 and 180 and store it in some variable say x Then Multiply…
Q: What does Oracle RAC's Cache Fusion serve?
A: Introduction: What is the purpose of Cache Fusion in Oracle RAC? Cache Fusion uses a high-speed IPC…
Q: Please assist us in finding our check. The query CPU on the database server is rather expensive in…
A: SMS CPU usage: Once you have a connection established to your SQL Server or Azure SQL instance, go…
Q: You have been hired to develop the One-Time Pad cipher for a company. You can use any languages such…
A: According to the information given:- we have to follow the instruction in order to get desired…
Q: What risks are there when moving a database off of a server?
A: Introduction Data migration: Data migration refers to the procedure of transferring data using a…
Q: Which part of a client/server architecture is responsible for storage?
A: The answer is given below step.
Q: 1. Write the formal English description of each set described by the regular expression below.…
A: A Turing machine is an abstract computational model that performs computations by reading and…
Q: es to the adopti
A: Solution - In the given question, we have to specify the obstacles to the adoption of IoT.
Q: Describe your day-to-day usage of databases and/or apps that are related to databases. Think about…
A: Introduction: Database: A collection of server-stored data. The data is readily retrievable,…
Q: What connects all Agile frameworks? Following that, click Submit. A set number of cycles…
A: Given: Work may be planned, managed, and carried out according to a certain methodology known as an…
Q: What computer-related terms and components are included here?
A: Introduction: Central Processing Unit (CPU) Here, computers handle data. It manipulates, calculates,…
Q: What dangers come with moving a database across server
A: Database is basically collection of information/data. Here moving means migrating. Their are many…
Q: Thank you, but what is your answer for (a) .. Like what is the number that is the base 8…
A: Conversion steps: Divide the number by 8. Get the quotient for the next iteration. Get the…
Q: Is migrating from on-premises servers to an laaS architecture a governance issue?
A: Introduction: Architecture for IaaS: With the IaaS model, cloud providers host infrastructure such…
Q: Question 110 Write a Python program which accepts the length I and the width w of a rectangle from…
A: The answer of the question is given below
Q: What is a system transition inside the realm of computers?
A: The term "transition" refers to a paradigm in computer science that explains the modification of…
Q: What is the difference between DLL and EXE files in.NET
A: What is .Net: .NET is a cross-platform, free, open-source for developers that may be used to…
Q: What differentiates a fat-client system design from a thin-client system design?
A: Introduction: All other layers are implemented on the server, except the presentation layer, which…
Q: How important is it to be acquainted with the compiler?
A: Introduction: Compilers convert programmes from one language to another.Compilers create machine…
Q: What are the pros and downsides of global connection in cloud computing?
A: Introduction Cloud computing: When easier for the organization to a network of cloud-based servers,…
Q: What are the top six reasons why individuals want to study compilers?
A: Introduction: Compilers: A compiler modifies the programming language or a program's type.] Certain…
Q: Use the sacramento.csv file( I cant upload it its a excel file) to complete the following…
A: Simple regression towards the mean K-NN is not the only kind of regression; another quite useful and…
Q: The layer between a database and a client server is known as the "intermediary layer."
A: Introduction: The "intermediary layer" is the layer that is located between a client server and a…
Q: implement following funtions: std::vector> return_table(int number_of_vars);…
A: Hello there, Assuming that every variable has 2 values. You want to implement a function that first…
Q: 3-2 Relative asymptotic growths Indicate, for each pair of expressions (A, B) in the table below,…
A: Please refer to the below table for the solution A B O 0 Ω ω Θ a) lgk n nε Yes Yes No No…
Q: 1. Display all Junior 2. Display all Male 3. Display all Female 4. Display all 18 and above years…
A: 1. SELECT * FROM demo WHERE Level='Junior'; SELECT is used to display all(*) or specified…
Q: The database is for a portion of a healthcare organization that tracks the tests performed on…
A: The entity-relationship diagram of patient management system shows all the visual instrument of data…
Q: How to Evolving Network Architectures?
A: Here is the answer below:-
Q: (e) Based on the type of hacker you select, explain whether a hacker should be legally prosecuted in…
A: Answer :-
Q: What dangers come with moving a database across servers?
A: Introduction: Transferring data across storage systems or computing environments is known as data…
Q: Phishing is a technique for impersonation and other forms of cyber fraud. What are the most…
A: Introduction: Spoofing involves altering an email address, sender's name, phone number, or website…
Step by step
Solved in 2 steps

- 6) Find a,b,ca) 2.5 GB in MB?b) 32 x 210 bits in KB?c) 3.5 MB in bits?Last solution had mistakes For a 5,000 RPM disk, assume its average seek time is 7 msec, and it has 100 MB/sec bandwidth; assume the sector size is 512 bytes. (In this problem, MB means 1,000,000 bytes.) How long does it take to access 2,048 bytes of contiguous data on average? What is the average throughput (bytes per second) if the user accesses 512 bytes for each I/O? Assume the data is perfectly aligned on the disk. How long does it take to access 1 MB of contiguous data (on average)? What is the average throughput (bytes per second) if the user accesses 1 MB for each I/O operations? Assume the data is perfectly aligned on the disk. Suppose a user expects his or her average throughput to reach 50% of the disk’s maximum bandwidth. Find the minimum I/O size needed to achieve this.A- What is the wrong in the following statements? Correct it. 1- MOV 2222, BX 2- SUB BL, AX3- MOV DS,2352h 4- INC SI,25- MUL CL, AL B- Explain the Addressing modes in details.
- 3- What is the difference between: a- MOV BX,[1234H] and LEA BX,[1234H] b- LDS AX,[200H] and LES AXX,[200H] 4-Use MOV to load address of memory MEM1.b. How many bits are required to address a 4M × 16 main memory if main memory is byte-addressable?c. How many bits are required to address a 1M × 8 main memory if main memory is byte-addressable?1. A manufacture wishes to design a hard disk with a capacity of 60 GB or more (using the standard definition of 1GB = 230 bytes). If the technology used to manufacture thedisks allows 512-bytes sectors, 1024 sector/track, and 60% tracks/ platter, how many platters are required?
- Assume a 2^20 byte memory (2^20 x 8):A. What are the lowest and highest addresses if memory is byte-addressable?B. What are the lowest and highest addresses if memory is word-addressable, assuming a16-bit word?C. What are the lowest and highest addresses if memory is word-addressable, assuming a32-bit word?At a minimum, how many bits are needed in the MAR with each of the following memory sizes? a. 1 million bytes b. 10 million bytes c. 100 million bytes d. 1 billion bytesSUBJECT: COMPUTER ORGANASATION 1. a. How many address bits are required to access 256K words of memory? b. How many bytes of memory can be addressed by 24 address bits?
- Need Logisim(.cric) file. Assume, a 12-bit ISA where the op-code is 3-bit wide. 1. Design a 10-bit ALU using a 1-bit ALU with specific set of instructions which arecorrespondingly Add, Sub, And, Or, and also Incorporate equality and overflowcheck.a- Write a program which adds the values D8H, F5H and E9H. Put the sum in file register 15H for (low byte) and file register 16H for high byte. b- What is the content of (low byte) and (high byte) registers in Hex?(Practice) a. Using Figure 2.14 and assuming the variable name rate is assigned to the byte at memory address 159, determine the addresses corresponding to each variable declared in the following statements. Also, fill in the correct number of bytes with the initialization data included in the declaration statements. (Use letters for the characters, not the computer codes that would actually be stored.) floatrate; charch1=M,ch2=E,ch3=L,ch4=T; doubletaxes; intnum,count=0; b. Repeat Exercise 9a, but substitute the actual byte patterns that a computer using the ASCII code would use to store characters in the variables ch1, ch2, ch3, and ch4. (Hint: Use Appendix B.)

