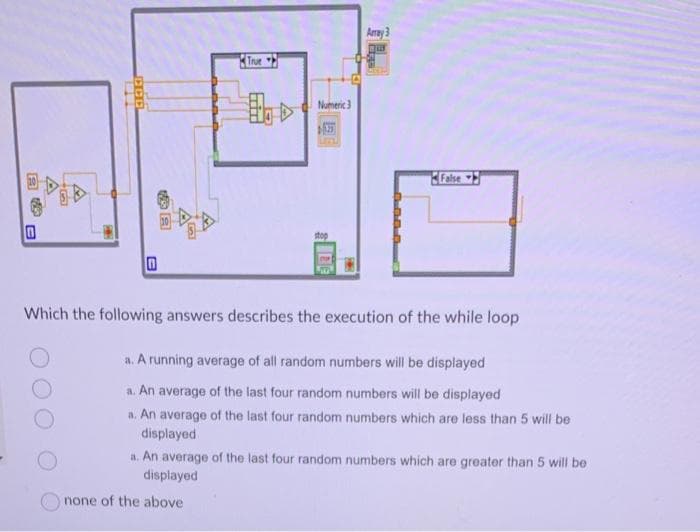
A A E 0 B B True Bo Numeric 3 stop DE Amay 3 Bur False Which the following answers describes the execution of the while loop a. A running average of all random numbers will be displayed a. An average of the last four random numbers will be displayed
Q: When and where did the idea of an interconnected network of everyday objects initially emerge, and…
A: The Internet of Things (IoT) came into existence after the first connected network, ARPANET.
Q: eed to convertr
A: We need to convert following question . In computing, base 2 or binary is a numbering system that…
Q: 1. In this program you will produce an output of the total tax based on your income and marital…
A: NOTE: Since there are multiple subparts, the first three sub-parts are answered for you as per…
Q: How well versed are you in the various computer languages? I'd appreciate it if you could provide a…
A: Programming languages enable computer systems to communicate. We know computers only interpret…
Q: Craps is a classic casino game in which players bet on the outcome of rolling 2 six dice (2d6).…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: Explain the procedure through which a computer program operates.
A: A set of instructions that tell a computer what to do is known as a computer programme. The central…
Q: Write a Python function that takes a string as input and returns the length of the longest…
A: Coded using Python 3. Make sure you are on latest version of Python.
Q: What types of enhancements may be made to the computer network system so that it remains free from…
A: How to Prevent Viruses from Spreading Via a Computer Network System Installing the most recent…
Q: Please describe what an entity-relationship model is as well as how it functions.
A: Dear Student, The detailed answer to your question is given below -
Q: in this android app package com.example.myapplication; import…
A: You can add an exit button to the top right corner of the PlayerActivity2 by adding a new Button to…
Q: How to input the following code # Open the input file and read the dictionary with…
A: The solution is given in the below step I am using OnlineGDB to run the code
Q: Why is it that installing a RISC CPU on a computer is easier than installing a CISC processor?
A: Why is RISC installation easier than CISC? RISC computer: This computer has less Cycles Per…
Q: Why does a computer work when you switch it on, and what parts are responsible for that?
A: Your computer comes to life when you turn it on thanks to a number of hardware and software elements…
Q: The dates variable (created at the top of this notebook) is a list of dates represented as strings.…
A: In this question, it is asked to provide the python code to output the list of strings in…
Q: rite a function that calculates the mean, median, variance, standard deviation, minimum and maximum…
A: SOLUTION- I have solved this problem in python code with comments and screenshot for easy…
Q: What are some of the restrictions that the Tor network has in place?
A: - We have to talk about some of the restrictions for Tor network.
Q: Name three separate types of semiconductor memory, and then provide a short discussion of the most…
A: Memory: RAM: RAM is a semiconductor memory type. technology for reading and writing data in whatever…
Q: Popular methods for mining images and texts include computer vision, face recognition, and sentiment…
A: Robotic eyeballs Information extraction from digital pictures is the primary focus of computer…
Q: 1.Data pre processing 2.Data visualization
A: Data Pre-processing: Data pre-processing is the process of cleaning, transforming, and preparing…
Q: Where did this concept of the internet of things first emerge, and what problems does it solve…
A: Introduction :- The IoT has the potential to transform numerous industries and significantly enhance…
Q: 1. Show the ListStackADT interface 2. Create a ListStackDataStrucClass with the following methods:…
A: Algorithm: Define a BaseNumber class to represent a number and its base. Define a ListStackADT…
Q: Why do so many people think the internet is the most cutting-edge medium of communication and…
A: Yes, that's correct to say that the internet is the most cutting-edge (most recent) medium of…
Q: How does the word "interdependence" differ from other vocabulary used to express the same notion,…
A: Interdependence is a fundamental concept that pervades many different fields, from ecology and…
Q: What exactly is meant by the term "system analysis"?
A: Information Base(s) + Applications + Interfaces = Information System Using file, database, or web…
Q: What are some of the telltale signs that a software project is on the verge of failing? Why even…
A: The warning signs that a software project is going to fail include the following: The necessary…
Q: Please share your thoughts on the limitations of cloud computing that classrooms and universities…
A: Cloud computing has drawbacks. Know these before moving your company to the cloud. Cloud data…
Q: Investigate the factors that led to the development of many versions of the same programming…
A: Introduction: Programming languages have been a crucial tool for developers to create software and…
Q: has anybody tried to open a file, copy a function inside the program, and use it for a current…
A: Yes, it is possible to open a file, copy a function inside the program, and use it for a current…
Q: Learn all you can about social networking blogs and cloud computing.
A: Learn about cloud computing and social media blogging. Social media is essential for bloggers. It…
Q: Python Why am I still getting an error? # Problem 1 # Implement a hashtable using an array. Your…
A: Answer is
Q: A local area network, or LAN, is referred to as the following:
A: Answer: Introdution A local Region Network (LAN) is a network of linked devices located inside a…
Q: Parallel attempts are made to write sections of a file to separate hard drives. Is there a reason…
A: Introduction The use of multiple hard drives in computing systems is an important tool for ensuring…
Q: What would you do if a virus invaded your mobile device, such as a smartphone or tablet? Identify…
A: Introduction: Mobile devices, such as smartphones and tablets, are incredibly useful tools in our…
Q: The Internet is crucial in creating a global network of information. Global networks based on the…
A: Everyone linked to the internet may interact and use computers from any location at any time. Since…
Q: Let's pretend the developer of an online banking system conceals a feature that alerts him to the…
A: What is an encryption: Encryption is the study of secure communication techniques that allow only…
Q: It is necessary to provide dependability and other TCP features on UDP in order for the QUIC…
A: Answer is TRUE
Q: What do you think are the most fundamental concepts that CS majors should know?
A: Computer science studies computing and its theoretical and practical applications. Computer science…
Q: How come watchdog timers are required in a wide variety of embedded systems, and what are some of…
A: Dear Student, The detailed answer to your question is given below -
Q: Create a table of values for y=4(2)^(x), starting at 0 and increasing by 1 . Full explain this…
A: The given equation is y = 4(2)^x. To create a table of values for this equation, we can substitute…
Q: What precautions should I take to prevent unauthorized access to my online information?
A: Introduction : In today's digital age, protecting personal information of customers is critical for…
Q: What does it guard against when it's turned on? A predetermined set of guidelines governs the…
A: The most crucial function of a firewall is to protect your network by filtering traffic and…
Q: Provide an example of a situation where the use of FCFS to distribute a limited resource caused a…
A: Answer is
Q: Write a function numRolls that simulates the following dice game: a player repeatedly rolls a pair…
A: Define a function named numRolls() which returns the number of rolls it takes to get two consecutive…
Q: vert the accompanying NFA to a DFA. For full credit, your DFA states ought to be named demonstrating…
A: The conversion of a nondeterministic finite automaton (NFA) to a deterministic finite automaton…
Q: store data for the foreseeable future?
A: Introduction Data storage is a critical component of any business, especially in the digital age.…
Q: Provide an explanation of what "optimum performance" means in the context of computing.
A: Computing has become an integral part of our daily lives, from the smartphones we use to the…
Q: Talk about the numerous different versions of Microsoft Windows that are available, as well as the…
A: Microsoft Disk Operating System, or MS-DOS (1981) The default operating system for IBM-compatible…
Q: If the clock rate is 3.5Ghz, and data transfer unit size is 2 bits, calculate bus DTR(data transfer…
A: Dear Student, The detailed answer to your question along with step by step explanation is given…
Q: describes your experience with uninstalling software?
A: Uninstall software on your computer: An uninstall is the process of uninstalling a software and all…
Q: As a computer scientist, I'm curious about the types of data for which you should not use the…
A: Introduction: Arithmetic mean, also known as the average, is a measure of central tendency that is…
Please written by computer source
Step by step
Solved in 2 steps

- 9. You are given some coins. You have to take some coins from the given coins such that the sum of the coinsyou took have a value strictly larger than the sum of the rest of the coins. However, you have to takeminimum number of coins while satisfying this conditionInputIn the first line, you are given n (n<=100), the number of integer numbers. In the next line, you will be given nintegers, separated by spaces.OutputOutput one number, the minimum number of coins you need to take to have a larger sum than the sum of thecoins you did not take.Input Output23 3 232 1 2 264 2 1 2 1 1 2In the first sample you will have to take 2 coins. If you take 1 coin, you get sum 3, 3. If you take 0 coins, you getsums 0, 6. Those variants do not satisfy you as your sum should be strictly more than the other sum.In the second sample one coin isn't enough for you, too. You can pick coins with values 1, 2 or 2, 2. In any case,the minimum…Create the generated machine code from snippet code as follow: int i=10, j, x;for (a=10; a>0; a--) {if (a % 2 == 1) i += a;else i /= 2;j = i*2;}x = i+j; please solve max in 30 minutes thank uevenly divides num1gcd (num1, num2) is gcd(num2, num1) if num1 < num2gcd (num1, num2) is gcd(num2, num1%num2) otherwiseCreate and execute a program to find the greatest common factor of two positive integers using Euclid's method. The largest common divisor is the highest integer that divides both numbers without leaving a remainder. In the DivisorCalc class, define a static method called gcd that accepts two numbers, num1 and num2. Create a driver to put your program through its tests. The repeated procedure is as follows: gcd (num1, num2) is num2 if num2 <= num1 and num2 evenly divides num1gcd (num1, num2) is gcd(num2, num1) if num1 < num2gcd (num1, num2) is gcd(num2, num1%num2) otherwise
- what are the values of the variables when runned? int j,kboolean mj = 1k = j++m = (++k == j++) ------------------ int x = 3if (x == 2)x= 0if (x==3)x++elsex+=2 --------------- how many times will it be looped for(int x = 0; x== 2; x++){//body of the loop}If the user chooses to generate a Pentagon o This is a combination of a triangular shape and a square shape -- a symmetric triangle sits on top of a rectangle. o The triangular shape must be symmetric about the vertical axis. There must be exactly one character in the first line, and the number of characters increases by 2 in every successive lineo The rectangle shape must have LENGTH lines of height and all lines are 13 characters wide. o Make sure to add delay to view a progressively growing pentagon, otherwise you will just see the final shape. Code for triangle: for (int i = 1; i <= length; i++) { sleep (1); for (int j = length - i; j > 0; j--) cout << " "; for (int b = 1; b <= i; b++) cout << char(rdm) << " "; cout << endl; } Code for square: for (int row = 1; row <= length; row++)…8.In this exercise you will create a program that will be used in a digital library to format and sort journal entries based on the authors last name. Each entry has room to store only the last name of the author. Begin by removing the first name "Isaac" from the string variable journal_entry_1 by using the string function erase. Do not forget to also remove the whitespace so that the string variable journal_entry_1 will then contain the string "Newton" with no whitespaces. The journal entries should be sorted alphabetically based on the authors last name. For example, the last name "Brown" should come before the last name "Davis" Create an if statement so that if the last name contained within journal_entry_2 is alphabetically less than the last name contained within journal_entry_1, then the string values are swapped using the string function swap. You may use either of the comparison operators < > in the if statement but remember that following ASCII, "A" is lexicographically…
- Total OccurranceGiven two integer numbers input1 and input2, find the total number of occurrences of input1 in aseries of natural numbers from 0 till input2.Note:1. input1 will be within 1-9 and1. input2 will be within 1 – 100.Prototype: public int findTotalOccurrence(int input1, int input2)Example 1:input1 = 2input2 = 20output = 3Explanation: Number 2 is repeated 3 times in the series of natural numbers from 0 - 20 ie at 2,12, 20.Example 2:input1 = 2input2 = 30output = 13Explanation: Number 2 is repeated 13 times in the series of natural numbers from 0 – 30 i.e. at 2,12, 20, 21, 22 (occurred twice), 23, 24, 25, 26, 27, 28, 29NEED HELP ASAP PLEASE! THANK YOU! Consider a game with three dice, namely, A, B and C. Each die, when rolled, generates a number between 1 and 6 (inclusive) independently and uniformly at random. In each play, the three dice are rolled, then a monetary return is computed according to the values for dice A, B and C, using the following algorithm. ThreeDice(A, B, C) { money = -9; if (A == B and B == C) { money = money + 81; } else if (A == B or B == C or C == A) { money = money + 21; } return money; } Analyze this game by answering the following questions: (a) What is the largest possible return value of ThreeDice? (b) What is the probability of ThreeDice returning the largest possible value? Choose one from below. A. 1/18 B. 1/3 C. 1/216 D. 1/2 E. 1/6 F. none of these is correct G. 1/36 H. 1/12 (c) What is the smallest possible return value of ThreeDice? (d) What is the probability of ThreeDice returning the smallest possible value? Choose one from below. A. 5/54 B. 1/18 C. 5/9 D. 4/9…Java code Ever wondered how change is disbursed to customers in certain stores? In country X the following notes exists 200,100,50,20,10 and following coins: 5, 1, 50c, 10c, 5c. For the sake of this exercises let us only consider change below 50 see below example: Sample run 1: Enter item name: Apples Enter QTY of Apples: 2 Enter price per item N$: 3.25 Amount tendered N$: 50 Your change is: N$ 43.50 Disbursed as follows: 2 x N$20; 0 x N$10; 0 x N$5; 3 x N$1; 1 x 50c; 0 x 10c; 0 x 5c [Hint: make use of % and / operators to determine the values needed]
- Make a program that prints the table of contents of a book where each chapter has the same number of sections, and each section has the same number of subsections. Example: Please enter the number of chapters 3Please enter the number of sections 3Please enter the number of subsections 3Chapter 1-Section 1.1--Subsection 1.1.1--Subsection 1.1.2--Subsection 1.1.3-Section 1.2--Subsection 1.2.1--Subsection 1.2.2--Subsection 1.2.3-Section 1.3--Subsection 1.3.1--Subsection 1.3.2--Subsection 1.3.3Chapter 2-Section 2.1--Subsection 2.1.1--Subsection 2.1.2--Subsection 2.1.3-Section 2.2--Subsection 2.2.1--Subsection 2.2.2--Subsection 2.2.3-Section 2.3--Subsection 2.3.1--Subsection 2.3.2--Subsection 2.3.3Chapter 3-Section 3.1--Subsection 3.1.1--Subsection 3.1.2--Subsection 3.1.3-Section 3.2--Subsection 3.2.1--Subsection 3.2.2--Subsection 3.2.3-Section 3.3--Subsection 3.3.1--Subsection 3.3.2--Subsection 3.3.3Write this using java Write a complete version of the Bresenham Midpoint algorithm to handle ALL slope values. m = 0 m > 0 m < 0 m = 1 m > 1 swap the rolls of x and y m < 1 m = infinity ( needs special test case) Include appropriate tests for ‘special case’ conditions. Insteadof “WritePixel” write to the screen the coordinates of the pixel that would be drawn. Please provide photos that it works and so I can understand the code betterDebug the program in orderfor it to run as stated in its specification (Note: No adding of lines of code, noneed to write comments). Underline the entire line that contains the bug. There should be 2 files to be uploaded. The .java file and the word/pdf/image file that contains the underlined codes. The program in the next page, when ran, will let the user roll a pair of dicen-times (i.e. generate a number between 1 and 6), where n is a positive integer entered by a user. The program then outputs the pair of numbers rolled by the dice, as well as the sum of the numbers rolled by each pair of dice. The pairs of numbers are stored in a 2-dimensional array, and the sumof each pair is stored in a single-dimensional array.

