(a) Alice chooses the secret key a = 4. Compute the public key Agº (mod p) Alice sends A to Bob. (b) Bob chooses the secret key b = 3. Compute the public key B = gb (mod p) Bob sends B to Alice. (c) Use Diffie-Hellman key exchange to compute the secret key that Alice and Bob share.
(a) Alice chooses the secret key a = 4. Compute the public key Agº (mod p) Alice sends A to Bob. (b) Bob chooses the secret key b = 3. Compute the public key B = gb (mod p) Bob sends B to Alice. (c) Use Diffie-Hellman key exchange to compute the secret key that Alice and Bob share.
Elements Of Modern Algebra
8th Edition
ISBN:9781285463230
Author:Gilbert, Linda, Jimmie
Publisher:Gilbert, Linda, Jimmie
Chapter2: The Integers
Section2.5: Congruence Of Integers
Problem 51E: In the congruences ax b (mod n) in Exercises 40-53, a and n may not be relatively prime. Use the...
Related questions
Question
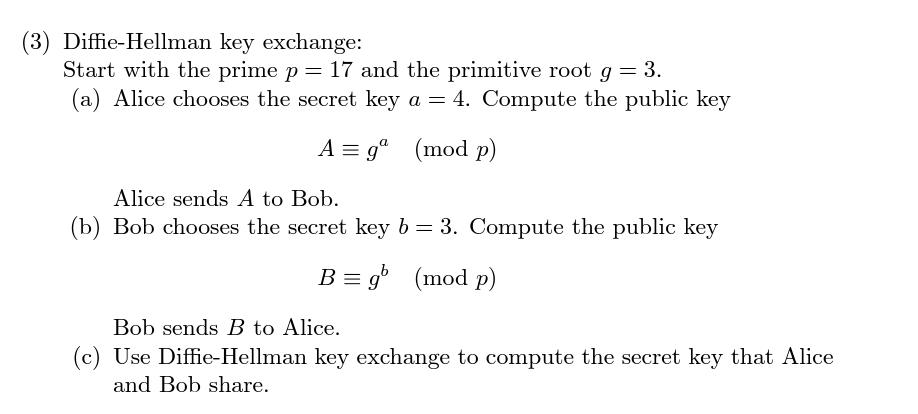
Transcribed Image Text:(3) Diffie-Hellman key exchange:
Start with the prime p = 17 and the primitive root g = 3.
(a) Alice chooses the secret key a = 4. Compute the public key
A = gº (mod p)
Alice sends A to Bob.
(b) Bob chooses the secret key b = 3. Compute the public key
B = gb (mod p)
Bob sends B to Alice.
(c) Use Diffie-Hellman key exchange to compute the secret key that Alice
and Bob share.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 5 steps with 3 images

Recommended textbooks for you

Elements Of Modern Algebra
Algebra
ISBN:
9781285463230
Author:
Gilbert, Linda, Jimmie
Publisher:
Cengage Learning,

Algebra & Trigonometry with Analytic Geometry
Algebra
ISBN:
9781133382119
Author:
Swokowski
Publisher:
Cengage

Elements Of Modern Algebra
Algebra
ISBN:
9781285463230
Author:
Gilbert, Linda, Jimmie
Publisher:
Cengage Learning,

Algebra & Trigonometry with Analytic Geometry
Algebra
ISBN:
9781133382119
Author:
Swokowski
Publisher:
Cengage