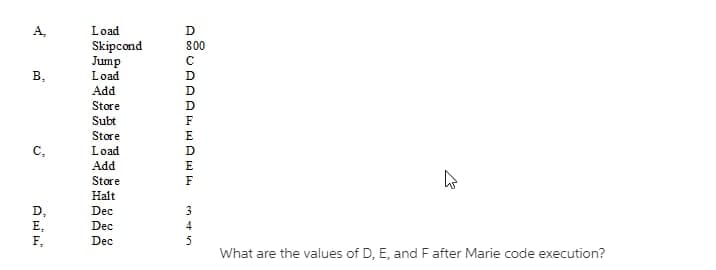
A₂ B, C₂ D₂ E, F Load Skipcond Jump Load Add Store Subt Store Load Add Store Halt Dec Dec Don ASUAAAA D 800 с D F m 4 5 h
Q: Write a C program using only stdio.h library that prints asterisk (*) on the screen according to the…
A: Code implementation: #include<stdio.h>#include<conio.h>int main() { int e,g; int…
Q: Examine how consumers react to computer and mobile application issues. Investigate techniques for…
A: Intro Mobile Application: A mobile application is software that runs on a mobile device such as a…
Q: ques.. Write Code to make Number queising game in python (also take input from user).
A: The code implementation in python is given below. Algorithm: Generate a random number between 0 and…
Q: How can you tell if your laptop's operating system has been hacked?
A: The following are some signs that the integrity of an operating system on a laptop may have been…
Q: How do the components of the abstract machines taught in class correspond to the components of the…
A: The Von-Neumann architecture describes the stored-program computer where instructions and data are…
Q: (2) Write a Java application that asks the user to enter the length and width of a room and the cost…
A: Please find the answer below :
Q: After the fifteenth collision, what is the maximum and minimum waiting time for a node on a 10 Mbps…
A: Introduction: Ethernet: Ethernet is a commonly used software and hardware networking protocol. The…
Q: A computer's operating system serves the following four purposes:
A: The motivation behind operating system is to oversee PC memory, processes and the activity of all…
Q: Describe how to use inline comments.
A: The uses of inline comments are as follows.
Q: The use of computer languages is used in the production of web-based applications by a significant…
A: Explanation: Provide details on the following three programming languages that are used to describe…
Q: Choosing between a colour and a monochrome monitor might be a little confusing.
A: Monochrome Monitor: While color monitors use varying intensities of red, green, and blue phosphors…
Q: Using expansion cards, peripheral devices may be connected to the CPU through the expansion bus and…
A: Introduction: An extension bus is a kind of computer bus that moves data between the internal…
Q: You can learn more about cloud computing, social networking, and other important topics by reading…
A: Introduction: Enhance your knowledge of social networking blogs and cloud computing, and other…
Q: What are the top five design principles for source documents?
A: Source document: Source document is a paper that provides information about the transaction. The…
Q: Convert the grammer into a PDA and check whether the string aaa is accepted by the PDA. S → aAA A →…
A: The answer is given in the below step
Q: Create a dataset that contains 3 objects and 4 attributes by filling the following table. Type of…
A: We know, In Nominal attribute, the data is only categorized, no ordering. So, here "Student's name"…
Q: Can you tell me the name of the modulation method that is used by computer networks that make use of…
A: Modulation method: The process of transforming data into electrical signals that are best suited for…
Q: Write the triple, for the expression, - (a*b)+(c + d) - (a+b+c+d).
A: ANSWER:
Q: Create a channel where the I/O processor optimises many input/output devices at the same time.
A: The DMA idea was further developed into what is now known as the I/O Channel concept. It can execute…
Q: Someone preparing for a marathon trains by running laps on a track which is ¼ mile per lap. The…
A: The Answer is given below step.
Q: What is the fundamental idea behind mobile applications?
A: INTRODUCTION: Mobile application development is the process of writing code for digital assistants…
Q: Write Code to Split Even and Odd Numbers in Separate List using this list : [22,8,7,0,13,99,38,63])…
A: Step-1: Start Step-2: Create a list Num with values [22, 8, 7, 0, 13, 99, 38, 63] Step-3: Declare…
Q: As part of your research, go deep into the worlds of cloud computing and social networking blogs.
A: Social network members may access shared resources from any place thanks to cloud computing. Most…
Q: (Java) Identify the statements that are true about arrays. Select all that apply; -Once created,…
A: The statements that are true about arrays are represented in Step 2.
Q: When does a user need to provide a password into the UAC box in order to proceed?
A: Intro The User Account Control (UAC) box is used to safeguard the system from harmful background…
Q: The solutions provided didn't work for any of the questions. Please provide different…
A: TASK 10 - SELECT FROM information_schema.tables WHERE table_schema = 'information_schema' AND…
Q: 3. With the help of program show how to declare and initialise a string in C++ without using the…
A: Step 1 : Start Step 2 : In the main function , Declare a string variable and in the braces inside…
Q: With an internal video card and an empty PCI Express video slot, you'll have a better gaming…
A: Introduction: A graphics card is an extension card that sends pictures to a display device such a…
Q: Ques.3 create a font art using python namely Mark Zuckerberg.
A: In the python program which is given below, font art has been created using dots(.) and asterisks…
Q: What is the "Hybrid Approach" in data warehousing?
A: Introduction: The hybrid approach to data warehousing recommends spending two weeks designing an…
Q: Computer science: An accurate definition of a project
A: Introduction: In a computer science project, information processes or programs are developed using…
Q: How to print something by searching on multiple files in Linux? 18:39
A: NOTE :- Below i explain the answer in my own words by which you understand it well. The grep…
Q: Write a C program using only stdio.h library that prints asterisk (*) on the screen according to the…
A: The code is given in the below step
Q: When it comes to computer operations, what are the most important features to look for?
A: Computer operations: On a fundamental level, the OS is responsible for the operation of a PC. In…
Q: What is the function of the authorised official? What three elements of the system must that person…
A: Answer: The Authorizing Officer (AO) is the operational official in charge of the mission and has…
Q: I need this script written for Linux/Ubuntu in Vi Editor, not for Python. Can you redo it using…
A: In this question we have to write a code in Linux shell script which can work in vi editor for…
Q: Form a multimedia project team with various skills, determine the number of teams, job names and…
A: Introduction Media Team (Project administrator, Multimedia Designer, Interface Designer, Writer,…
Q: How frequently does Windows automatically defragment a hard drive?
A: Defragmentation of disc: Defragmentation expands PC execution. Defragmentation, also recognized as…
Q: . Ordinary Intelligence B. C
A: Explanation: Beginning in 1982, the Fifth Generation Computer Systems (FGCS) project by Japan's…
Q: What distinguishes IT security solutions hosted in the cloud from traditional on-premises data…
A: An IT solution refers to all those methods and ways that are software related and provide better…
Q: Question 2 Let say an Array consist of String names as follow: [i] [0] [1] [2] [3] [4] [5] [6]…
A: answer is starting from step 2
Q: ut cloud com
A: Cloud computing: Cloud computing is the on-demand availability of PC system assets, especially data…
Q: How can you tell if your laptop's operating system has been hacked?
A: The following are some signs that the integrity of an operating system on a laptop may have been…
Q: Which of the following distributions has the lowest variability? frequency mean Distribution 2 1…
A: Computer performance variability can be defined as the how far is the data points from one to other…
Q: Ques.23 Write python code to count number of files and directories in your system (you can give path…
A: In this python program we need to write a code for counting the total number of files and directory…
Q: Load the diamonds.csv file, and make 80% of the data in the order of the data as the training data.…
A: The code is given as follows:
Q: Describe briefly the non-free Linux firewall that was described in the presentation.
A: According to the information given:- We have to describe a non-free Linux firewall.
Q: Learn as much as you can about cloud computing and blogging on the internet.
A: inspection: Social networking involves interacting with loved ones, friends, and others with similar…
Q: What exactly does an adaptive mutex do?
A: Introduction: An adaptive mutex is used to safeguard any important data item that is accessible with…
Q: Q1. For the giving dataset (X) below, calculate the following X= (455.2, 676.7, 784.7, 349.1, 437.5,…
A: The range is nothing but the difference between the smallest and the largest element in the dataset…
4.9
Step by step
Solved in 2 steps

- Please if could, typed solution Consider a logical address space of 32 pages of 1024 words each, mapped onto a physical memory of 64 frames. How many bits are there in the logical address? How many bits are there in the physical address?In the Von Neumann paradigm, which of the following components: flash memory, DVD-RW, ROM, hard disk, and CPU belongs to which?Suppose that a RISC machine uses five register windows.Q) How deep can the procedure calls go before registers must be saved in memory? (That is, what is the maximum number of “active” procedure calls that can be made before we need to save any registers in memory?
- Assume that relocatable software code does not exist. How can the paging mechanism in memory be made more complex?The instruction below was given to a computer to execute. Kindly identify the possible outcome of the instruction set after execution. Briefly describe if any possible problem(s) or bugs can occur and explain how to correct these bugs. Remove the burned-out bulb Insert a new bulbFor the assembly language instructionsshown below, the initial value of r2 =Ox0000_0012 and r3 = 0x0000_0034. Show the contents of r2 and r3 after theinstructions execute. Explain whichconditional instructions execute or do notexecute and why. CMP R3,#-1MOVGT r2,#OxBEADDEQ r3,r3,r2
- Computer A has an overall CPI of 1.3 and can be run at a clock rate of 600MHz.Computer B has a CPI of 2.5 and can be run at a clock rate of 750 Mhz. Wehave a particular program we wish to run. When compiled for computer A, thisprogram has exactly 100,000 instructions. How many instructions would theprogram need to have when compiled for Computer B, in order for the twocomputers to have exactly the same execution time for this program?Provide neat answers. Show all necessary steps. Translate the following code snippet written in C programming language into an instructionsequence written in MIPS Assembly language. You may assume that the values of the variables x,y, a, b, and c are in the general-purpose registers $s0, $s1, $s2, $s3, and $s4. if(x == y) {c = a - b;} else {c = b - a;}x = x + c;y--;fgnghnmghmhmgbjh,j
- Let's pretend for a moment that we have a byte-addressable computer with 16-bit main memory addresses and 32-bit cache memory blocks, and that it employs two-way set associative mapping. Knowing that each block has eight bytes, please calculate the size of the offset field and provide evidence of your calculations.Computer Science Assume the options of the access time and cycle time of a memory system to retrieve a word (4 bytes) are 10 and 12 nanoseconds. a. What would be the transfer rate of the memory system when considering the memory access time (in terms of bytes per second)? b. If memory cycle time were used, how much time per byte would be wasted?A Von Neumann model includes which of the following elements: flash memory, DVD-RW, ROM, hard disc, and microprocessor?

