Virtua address sp= er page table entry imum size of addr
Q: When deadlock detection identifies a situation in which resources are needed, they are delivered to…
A: Foundation: A deadlock happens when two computer programmers that share the same resource get…
Q: What are the first three factors that lead to a deadlock? Please, no handwritten responses, no…
A: Deadlock: A deadlock occurs when two computer programmes that share the same resource effectively…
Q: Design a class named Account that contains: a. An int data field named id for the account. b. A…
A: Given data, Design a class named Account that contains: a. An int data field named id for the…
Q: Locate and organise the many pieces of data that are stored on your personal computer or personal…
A: A microcomputer that can be used for various tasks is known as a personal computer (PC), and its…
Q: Do you want to increase not only your comprehension of cloud computing and other important themes,…
A: NOTE :- Below i explain the answer in my own words by which you understand it well.…
Q: What is one of the advantages of switching away from bash and making use of another shell, instead?
A: A Shell is a graphical user interface for interacting with the Unix system and performing commands.…
Q: Cloud computing and social networking blogs may help you learn.
A: Please find the detailed explanation in the following steps.
Q: Acquire a deep and comprehensive grasp of social networking. What precisely is meant by the term…
A: Introduction: Acquire a deep and comprehensive grasp of social networking. What precisely is meant…
Q: A software solution to be used by a large organisation (let us say 1000 users) can be provided by a…
A: According to the information given:- We have to describe software solution to be used by a large…
Q: (74) Name something sharp PLAY NOW Ice cream ES 8
A: Program must be done in Java; Program must contain programmer comments explaining all aspects of the…
Q: Q1/what is the best way to get paths of the following items change resolution-1 shut down system-2…
A: There is the following step for changing this kind of task. 1) Change Resolution Actually for…
Q: 2. Assume that the population of the world in 2020 was 7.8 billion and is growing at the rate of…
A:
Q: ategories of security control families, and how do they
A: There are 18 security control families for federal information systems and organisations, each with…
Q: Give an example of how a neural network with a large number of layers could present a problem. In…
A: Introduction An ANN is a computer system fashioned after the biological neural networks that make up…
Q: What is big data and how can it benefit you?
A: Big data Big data are the collection of huge volume data that can be structured and unstructured and…
Q: Structured English in non-systems analytic methodologies should be explored further.
A: NOTE :- Below i explain the answer in my own words by which you understand it well. The system…
Q: Cloud computing and social networking blogs seem to be popular these days.
A: let us see the answer:- Introduction:- Cloud computing: Cloud computing is the on-demand,…
Q: Differentiate between multiplexing based on frequency and multiplexing based on time (According to…
A: let us see the answer:-
Q: Look at the top cloud-mobile connections. How can cloud computing help mobile devices?
A: Cloud computing is the trend in which resources are provided to a local client on an on-demand…
Q: Developing a new word processor with more features than any of its rivals Which of these approaches…
A: Word Processor: A word processor, sometimes known simply as a word processor, is either a piece of…
Q: In the OSI model, the presentation layer is responsible for a variety of tasks, including…
A: The application layer of the OSI model performs much of the same functions as the presentation…
Q: What exactly are the "rules of inference"? Provide an explanation of "ahead chaining" and "reverse…
A: Ahead chaining: Filters. (Theory of proof, logic) A rule for merging (changing) well-formed formulae…
Q: A GSM system uses 124 channels and each channel is divided into 8 time slots. What is the maximum…
A: The answer is
Q: By taking this course, not only will you improve your knowledge of social networking blogs, but also…
A: The social networking blog is the process of writing in a place where readers already existed.…
Q: Q1/what is the best way to get paths of the following items change resolution-1 shut down system-2…
A: Change Resolution 1 - Open Display Settings 2- In the Display resolution row, select the list and…
Q: Separate authentication from responsibility
A: Please find the answer below :
Q: At the time of runtime, the attribute of a control, in the same way that the attribute of other…
A: Introduction: Attribute Control Charts are a kind of control chart that was specifically designed to…
Q: Classify and explain with example the instruction that used to transfer .the data between the…
A: Instructions to transfer data between processor and system in 8085 are: Classification:- MOV M, Sc…
Q: Give an explanation of the advantages and disadvantages of using pre-made software packages rather…
A: Introduction: Although the advantages of building a completely customized vehicle seem enticing,…
Q: :the output of (Print "a", "b", "c") is abc O ab c abc O O O
A: Answer in step 2
Q: What are the advantages that virtual private networks (VLANs) provide to an organization's business…
A: Introduction: Employ private Virtual Local Area Networks to isolate a user from the rest of the…
Q: What component of hardware is responsible for a device's ability to connect to the Internet?
A: What component of hardware enables a device's physical network connection? Solution: In the network,…
Q: Private Sub Form_Click() Dim Speed!, Fee Speed = 75 If (Speed > 75) Then Fee = 60 Else If (Speed >…
A: VBA DIM statement stands for "declare". It is used to declare a variable before we can use it in our…
Q: A technician with a PC is using multiple applications while connected to the internet. How is the Pc…
A: A computer is able to keep track of the data flow between application sessions and has the ability…
Q: What exactly is meant by the term "dynamic memory," and how does it contr
A: in programming, memory allocation is important for storing values when assigned to variables.…
Q: In areas other than systems analysis, see whether Structured English may help to describe processes.
A: => The Answer start from step-2.
Q: Given F(w, x, y, ) = w'x'y'z' + w'x'y'z + w'xyz' + w'xyz, express F’(w,x,y,z) in minterm list form.…
A: Given F(w, x, y, z) = w'x'y'z' + w'x'y'z + w'xyz' + w'xyz F(w, x, y, z) = w'x'y'(z'+z) + w'xy(z'+z)…
Q: Cloud computing's commercial implications Can you collaborate
A: Please find the answer below :
Q: oblems associated with networking in the enterprise? Describe the problems as well as some of the…
A: Introduction: An enterprise-wide network is that connects computers with a company, including…
Q: It is important that research be done on the application of Structured English to the description of…
A: Systems analysis: Systems analysis is the process of a person (s) studying a system to assess,…
Q: 3) Locate three sites on the internet that deal with web security. Use whatever means you want and…
A: 1) Dark ReadingDark Reading is packed with information for a growing information security community.…
Q: Conduct research on whether or not there is currently being tested for penetration being done. As an…
A: Introduction: Testing for insecurity Penetration testing is a method of determining the security of…
Q: What exactly do you mean when you talk about "network security," and how would you express it to…
A: The safety of a network "Network security" encompasses various technologies, equipment, and…
Q: What do we maen by addressing mode. Explain 8085 adressing mooe
A: HI THEREI AM ADDING ASNWER BELOWPLEASE GO THROUGH IT THANK YOU
Q: Q2 What is the mode and I/O configuration for ports A, B, C of an 82C55 after its control register…
A:
Q: A savings account is opened with £100000 at the beginning of January. A deposit is then made of…
A: A savings account is opened with £100000 at the beginning of January. A deposit is then made of…
Q: What are the benefits and drawbacks of having global connection to the cloud?
A: Answer the above question are as follows
Q: Provide a condensed explanation of how Wavelength Division Multiplexing works.
A: Wavelength Division Multiplexing(WDM) works as following: In this technique, there is a multiplexer…
Q: representation Find the circuit state below; (100)+101) + |10) + |11)) ½½ (−|00) + |01) + |10) +…
A:
Q: What difficulties are there in implementing networking throughout a whole organisation? Please…
A: Given: What are some of the challenges that come with implementing a company-wide network? Describe…
Step by step
Solved in 2 steps with 2 images

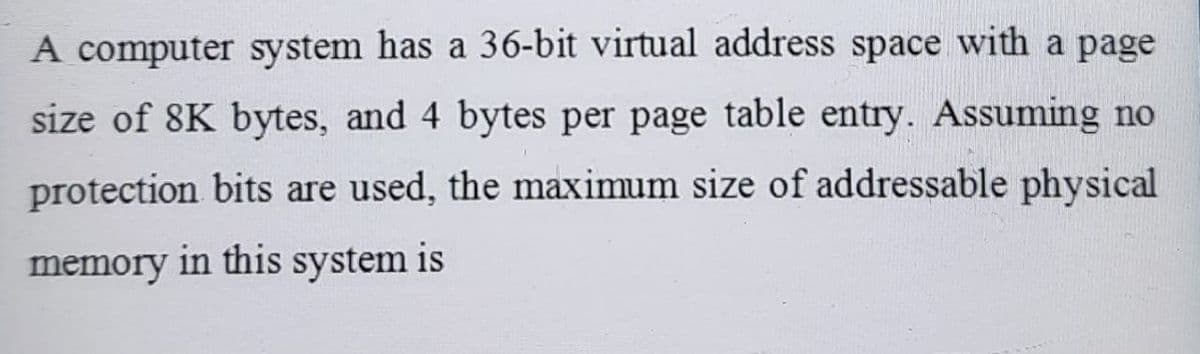
- If a microprocessor has a cycle time of 0.5 nanoseconds, what’s the processor clock rate? If the fetch cycle is 40% of the processor cycle time, what memory access speed is required to implement load operations with zero wait states and load operations with two wait states?Consider a computer system with a 64-bit logical address and 32-KB page size. Thesystem supports up to 4096 MB of physical memory. How many entries are there ineach of the following?a. A conventional single-level page table?b. An inverted page table?Consider an operating system using memory mapping on a page basis and using a single level page table. Assume that the necessary page table is always in memory. The system takes 200 ns to make a memory reference, how long does a paged memory reference take? Group of answer choices 400 ns (nanoseconds) 809.2 ms (microseconds) 200 ns (nanoseconds) 1638.4 ms (microseconds)
- 1. Consider a computer system with a 30-bit logical address and 4-KB page size. The systemsupports up to 512 MB of physical memory. How many entries are there in each of the following?Assume that each page table entry is 4 Bytes.c. A conventional single-level page table?d. An inverted page table?e. A two-level hierarchical page table? 2. Consider a virtual memory system with a 50-bit logical address and a 38-bit physical address.Suppose that the page/frame size is 16K bytes. Assume that each page table entry is 4 Bytes.a. How many frames are in the systems? How many pages in the virtual address space for aprocess?b. If a single-level page table is deployed, calculate the size of the page table for each process.c. Design a multilevel page table structure for this system to ensure that each page table can fitinto one frame. How many levels do you need? Draw a figure to show your page systemsSuppose you have a byte-addressable virtual address memory system with 32 virtual pages of 32 bytes each, and 8 page frames. Assuming the following page table, answer the questions below: | Page # | Frame # | Valid bit ||--------|---------|-----------|| 0 | 4 | 1 || 1 | 3 | 1 || 2 | - | 0 || 3 | 0 | 0 || 4 | 1 | 1 || 11 | 6 | 0 || 13 | 7 | 1 || 17 | - | 0 | a) How many bits are needed to address this virtual memory? b) What is the size of the Page field? c) What is the size of the Offset field? d) What is the size of the Page Frame field? e) What is the maximum number of the entries in this Page Table? f) What Physical address corresponds to the Virtual address 0x22? Answer should be in hexadecimal number. (if the address causes a page fault, answer as "page fault" with the proper reason) g) What Physical address corresponds to the…Suppose you have a byte-addressable virtual address memory system with 32 virtual pages of 32 bytes each, and 8 page frames. Assuming the following page table, answer the questions below: | Page # | Frame # | Valid bit ||--------|---------|-----------|| 0 | 4 | 1 || 1 | 3 | 1 || 2 | - | 0 || 3 | 0 | 0 || 4 | 1 | 1 || 11 | 6 | 0 || 13 | 7 | 1 || 17 | - | 0 |a) How many bits are needed to address this virtual memory? b) What is the size of the Page field? c) What is the size of the Offset field? d) What is the size of the Page Frame field?
- Consider a logical address space of 32 pages of 1024 words each, mapped onto a physical memory of 8 frames. How many bits are there in logical address and how many bits are there in physical address?Assume a 32-bit address system that uses a paged virtual memory, with a page size of 2 KB. Answer the following questions, assuming a virtual address 0x00030f40 A. What is the virtual page number (VPN) and the offset in binary for the given virtual address? B. How many virtual pages are there in the system?Suppose a byte-addressable computer using set-associative cache has 216 bytes of main memory and a cache of 32 blocks, and each cache block contains 8 bytes.Q.) If this cache is 4-way set associative, what is the format of a memory address as seen by the cache?
- Suppose that a machine has 42-bit virtual addresses and 32-bit physical addresses.{a} How much RAM can the machine support (each byte of RAM must be addressable)?{b} What is the largest virtual address space that can be supported for a process?{c} If pages are 2 KB, how many entries must be in a single-level page table?{d} If pages are 2 KB and we have a two-level page table where the first level is indexed by 15-bits, then how many entries does the first-level page table have?{e} With the same setup as part {d}, how many entries are in each second-level page table?{f} What is the advantage of using a two-level page table over single-level page table?A computer has a 32-bit virtual address space and 1024 byte pages. A page table entry takes 4 bytes. A multilevel page table is used because each table must be contained within a page. How many levels are required?Suppose a byte-addressable computer using set associative cache has 2^24 bytes of main memory and a cache size of 64K bytes, and each cache block contains 32 bytes. a) If this cache is 2-way set associative, what is the format of a memory address as seen by the cache, that is, what are the sizes of the tag, set, and offset fields? b) If this cache is 4-way set associative, what is the format of a memory address as seen by the cache?



