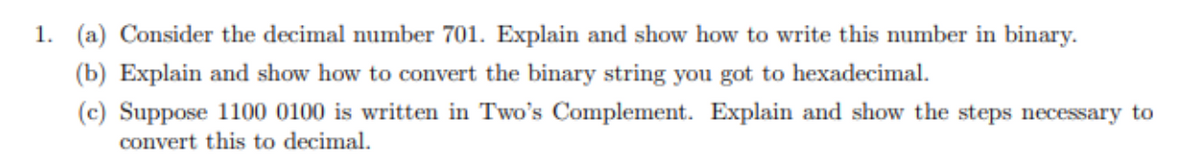
(a) Consider the decimal number 701. Explain and show how to write this number in binary. (b) Explain and show how to convert the binary string you got to hexadecimal. (c) Suppose 1100 0100 is written in Two's Complement. Explain and show the steps necessary to convert this to decimal.
Q: 2-Displaye the name Nd department number of all employees working in departments 10 and 30 in…
A: According to the Bartleby guideline, we are supposed to answer only first 3 similar question at a…
Q: Why are people of all ages and from all walks of life so interested in computer science?
A: Among the rapid pace of technical progression, computer science comprise turn into more and more…
Q: This Microsoft Baseline Security Analyzer is what you need to use.
A: Introducing the Microsoft Baseline Security Analyzer (MBSA)The Microsoft Baseline Security Analyzer,…
Q: Low-resource consumers need cloud-based database services. Customers have the resources to maintain…
A: When low-resource consumers rely on cloud-based database services, it becomes crucial to protect…
Q: computers change in terms of several factors including their size, form, availability, cost and…
A: Over the years, computers have undergone significant changes in terms of size, form, availability,…
Q: Develop a database table with sample data based on the System Capability ‘Service Request’ and the…
A: Database design and modeling is the process of creating a conceptual and logical representation of a…
Q: I would really appreciate it if you could list the top six reasons why people should learn how to…
A: With the increasing digitization of every industry and social sector, computer literacy has become…
Q: What are the three different types of computers that a neighbourhood bank uses, and how would you…
A: Personal Computers (PCs) are the nearly all and sundry widespread types of computer used in a…
Q: If you use cloud computing instead of running your own computers and networks, there are a number of…
A: Cloud computing offers numerous advantages over traditional methods of running individual computers…
Q: Explain briefly how digital certificate can verify a user's authenticity.
A: A digital certificate is an electronic document that verifies the authenticity and identity of a…
Q: There must be a record of the FTP port numbers. Is it true that FTP sends "out of band" (away from…
A: FTP (File Transmission Protocol) is a frequently employed protocol for file transmission over a…
Q: Instead of shared memory, shared structures could be stored locally and recovered by talking to…
A: In certain systems, instead of utilizing shared memory, shared structures can be stored locally and…
Q: discuss how to creat a non-executable stack and disuss the stack's exploitable veaknesses
A: Non-executable stack (NX) is a virtual memory protection mechanism to block shell code injection…
Q: Compare and contrast different usability evaluation methods such as usability testing, heuristic…
A: Web evaluation refers to the process of assessing and analyzing the effectiveness, usability, and…
Q: want a flow chart represent how the sensor work according to the code (this code for sensor +…
A: 1- A flowchart is a photograph of individual actions in a manner in sequential order. 2- It is a…
Q: Write in algo a program which displays the following series: a) 12345678910 b) 1 3 5 7 9 11 13 ΓΛΜΗ…
A: The algorithm and JAVA code for both the series are given in the below step
Q: Are access points switches or hubs when it comes to bandwidth? Explain
A: What is bandwidth: Bandwidth refers to the maximum data transfer rate of a network or internet…
Q: Exists anything that could impede a satisfactory performance compromise among the central processing…
A: The CPU, the heart of a computer system, shows a substantial role in determining the system's…
Q: A logic circuit is required to control traffic lights. The circuit consists of two inputs A and B,…
A: All the answers are given below
Q: Write a php program to take the current room temperature from the user in degree celsius and try to…
A: Required:-Write a PHP program to take the current room temperature from the user in degree celsius…
Q: Multitasking simplifies the process of switching between multiple active applications. Can multiple…
A: Yes, multiple operating systems can exist on an identical computer. This is often accomplished via a…
Q: Which of the following would be the variable result value, after the following set of statements?…
A: first is initialised as 1, First is initialised as 100, second is initialised as 5, Second is…
Q: Where do traditional cards with magnetic stripes fail to provide enough security, while current…
A: Traditional cards with magnetic stripes have been widely used for various purposes, such as credit…
Q: Do software workers all work towards the same goal? So, I have to ask, "What do you mean exactly by…
A: Software is a general term. "software" refers to a collection of instructions, data, or programs…
Q: Which kind of network design would you choose if your business had a small office but needed to…
A: The right network design must be chosen when connecting a small workplace with Forty PCs to the…
Q: Given a weighted digraph, find a monotonic shortest path from s to every other vertex. A path is…
A: We may use a modified version of the Bellman-Ford technique to determine a monotonic shortest path…
Q: How are computers different?
A: 1) Computers are electronic devices that process and store data, perform calculations, and execute…
Q: ell me about the business method you plan to use.
A: A business method or strategy is a plan of action that a company implements in order to attain its…
Q: Write a program in python to get the lossing probability after taking the winning probability from…
A: In step 2, I have provided PYTHON CODE------------In step 3, I have provided CODE…
Q: These are some of the most important ways in which HDDs and SLAs are different.
A: A hard Disc Drive is an abbreviation for typical computer storage. One or more stiff, quickly…
Q: I just want to main call (It is only one question) Look at the code below. You have four classes…
A: A class diagram is a type of structural diagram in software engineering that represents the…
Q: Why are people of all ages and from all walks of life interested in the field of computer science?
A: The extent of computer science has broadened to comprise fetching vital in modern life, influence…
Q: Could you tell me more about KPIs for software development? Please make everything clear.
A: Software development alludes to the method involved with making, planning, programming, testing, and…
Q: Cybersecurity Analyst- What is the job description, education/traiing requirements ( any special…
A: The duties of a cybersecurity analyst typically include:Security Monitoring: Monitoring computer…
Q: Multitasking simplifies the process of switching between multiple active applications. Can multiple…
A: Yes, multiple operating systems can exist on an identical computer. This is often accomplished via a…
Q: To explain what a real-time operating system is, you can use examples. How is this operating system…
A: An operating system is a product that goes about as an intermediary between PC hardware and client…
Q: Which of the following actions will improve database performance???? A) Cache data in memory…
A: The answers are given below with explanation
Q: What does the following string do to given string str1. String str1 =…
A: We need to identify what does the following string do to given string str1.String str1 =…
Q: If you have time, can you explain how measures change the process of making software? Give specifics…
A: If you have time, can you explain how measures change the process of making software? Give specifics…
Q: How can you avoid the pitfalls of company-wide networking? Please address the issues as well as…
A: Company-wide network is a unsafe asset in today's digital earth, as it give the spine for business…
Q: Question 4 The following method should return the text variable three times, combined together side…
A: Dear Student,The simplest way for this method to return the text variable three times combined…
Q: How do you shorten the phrase "computer output" when talking about data that is saved on optical…
A: What is computer output: Computer output refers to the result or information produced by a computer…
Q: Where is the screenshot of the terminal? How do I know whether this code works completely? I need to…
A: The code is changed a bit to show an output in the terminal.Also screenshot is attached
Q: Include information about the most popular VPN services, software, and gear.
A: In today's digital age, online privacy and security have become major concerns for individuals and…
Q: How does dynamic memory placement mean "memory leaks?"
A: dynamic memory placement refers to the process of allocating and deallocating memory at runtime.…
Q: Discuss how the future schedule management system will store and retrieve files.
A: The future of schedule management systems holds great promise in terms of efficiency and…
Q: Why does a reader sometimes need to "look" at the characters that
A: Answer is explained well in detail below
Q: i want to calculate trapezoidal rule using matlab but the code a little bit wrong i think. can you…
A: The code you provided for calculating the trapezoidal rule looks fine, except for a small logical…
Q: Make code in Python with its classes and inheritances Suppose Juan wants to bring flowers to a…
A: Code:class Person: def __init__(self, name): self.name = name def receive_flowers(self,…
Q: I'd want some real-world examples to assist me comprehend the distinctions between digital piracy…
A: Understanding the distinctions between digital piracy and intellectual property infringement is…
Subject : computer science
Step by step
Solved in 5 steps

- The following is a string of ASCII characters whose bit patterns have been converted into hexadecimal for compactness: 73 F4 E5 76 E5 4A EF 62 73. Of the eight bits in each pair of digits, the leftmost is a parity bit. The remaining bits are the ASCII code. Convert the string to bit form and decode the ASCII.Assume a 24-bit word on a computer. In these 24 bits, wewish to represent the value 295.1. a) How would the computer represent the decimal value295?2. b) If our computer uses 8-bit ASCII and even parity, howwould the computer represent the string 295?3. c) If our computer uses packed BCD with zero padding, howwould the computer represent the number +295?The following is a string of ASCII characters whose bit patterns have been converted intohexadecimal for compactness: 73 F4 E5 76 E5 4A EF 62 73. Of the eight bits in each pairof digits, the leftmost is a parity bit. The remaining bits are the ASCII code.(a) Convert the string to bit form and decode the ASCII.(b) Determine the parity used: odd or even?
- Is the set of infinite bit strings with an equal number of 0s and 1s countable or uncountable?Is the set of infinite bit strings with an equal number of 0s and 1s countable or uncountable?Bit strings consist of 0 and 1. How many bit strings of length 7 either start with “1” or end with the 3 bits “000”? A.80 B.72 C.64 D.168. Add the following two 8-bit binary numbers, producing an 8-bit result. Indicate the status of the carry and overflow bits at the end of the addition by circling the appropriate choices. The space in between is only for readability. 1111 0010 + 1101 0110 ----------- Overflow? Yes or No Carry? Yes or No
- A 36-bit floating-point binary number has eight bits plus sign for the exponent and 26 bits plus sign for the mantissa. The mantissa is a normalized fraction. Numbers in the mantissa and exponent are in signed-magnitude representation. What are the largest and smallest positive quantities that can be represented, excluding zero?(b) How many 8-bit strings have either 5 1 bits or 6 1 bits in them?with the given positive integer, find the all n-digit binary numbers, along with the their decimal representation in C++ VS example: Input: nDigits = 4Output:0000 -> 00001 -> 10010 -> 20011 -> 30100 -> 40101 -> 50110 -> 60111 -> 71000 -> 81001 -> 91010 -> 101011 -> 111100 -> 121101 -> 131110 -> 141111 -> 15
- How many eight-bit binary strings contain exactly 3 1s? How many eight-bit binary strings contain at least three 1s? How many eight-bit binary strings contain an equal number of 0s and 1s? How many eight-bit binary strings contain at most three 1s?Kindly answer the following questions. d. How are the ASCII codes for the decimal digits obtained? What is the relation between the ASCII codes for the capital letters and lowercase letters?1) Draw the Insert(o) TM, which changes the tape contents from yz to yoz. Here ye (20(A))*, σ € ZUIA), and ze 2. Assume that 2 = (a, b). 2) Draw a transition diagram for a TM with input alphabet (0,1) that interprets the input string as the binary representation of a nonnegative integer and adds 1 to it. You can use a TM INSERT (0).

