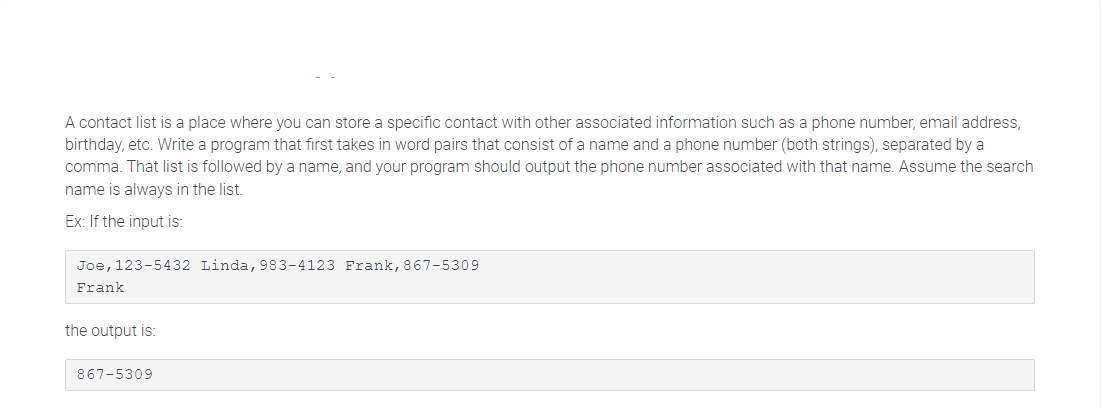
A contact list is a place where you can store a specific contact with other associated information such as a phone number, email address, birthday, etc. Write a program that first takes in word pairs that consist of a name and a phone number (both strings), separated by a comma. That list is followed by a name, and your program should output the phone number associated with that name. Assume the search name is always in the list. Ex: If the input is: Joe, 123-5432 Linda, 983-4123 Frank, 867-5309 Frank the output is: 867-5309
Q: Describe the benefits and drawbacks of utilizing the internet to look for a jon.
A: Start: Describe the benefits and drawbacks of utilising the internet to look for a job. The Internet…
Q: Find out about the most recent ten cyber-attacks on computers, networks, and information security,…
A: Given: An attack is any effort to obtain unauthorized access to or utilise assets in order to…
Q: What are the key distinctions between HRM, Intranet and Internet in terms of domain and network…
A: Introduction: The internet is a worldwide wide area network that allows computers to communicate…
Q: When transitioning from an older system to an integrated ERP system, discuss the importance of…
A: Encryption: An integrated ERP system enables you to oversee every area of your business from a…
Q: Complete the following use case description for a University Management System. When a student…
A: Use-case diagrams Use-case diagrams describe the high-level functions and scope of a system. These…
Q: Identify and briefly analyze five factors that have contributed to the continuous rise of…
A: Your brand serves a certain purpose.Whether you realise it or not, your e-commerce business has a…
Q: What is the aim of reflection in C#? Describe some of the uses for which reflection is required.
A: In the given question Reflection is used when you want to determine or modify contents of an…
Q: What is it about the information system design process that leads to so much scope creep?
A: In simple terms, the scope of a project refers to all the work required to complete a project. You…
Q: Briefly describe the security engineering methods you would use to examine this DDoS assault…
A: According to the information given:- We have to describe the security engineering methods you would…
Q: The majority of the machines feature a 2-way capability, which means you may copy them both from and…
A: Given: Most machines have a two-way capacity; they can be copied from another register or to another…
Q: delay) A Create class Property. B. Create class Flat that inherith from the class Property. C.…
A: Java Program: Main.java import java.util.ArrayList; public class Main { public static String…
Q: Create, compile, and run a recursive program. Choose one of the labs listed below and program it.…
A: As per our guidelines, we are supposed to answer only 1st three parts. Kindly repost the remaining…
Q: Consider the difference between the E2 CMOS cell in a GAL and the fusible link in a PAL.
A: Define: Because of this, In a GAL, compare the E2 CMOS cell to the fusible link in a PAL. Monolithic…
Q: What impact has the personal computer/laptop had on the trajectory of people's lives today? What are…
A: Technology : What impact has the personal computer/laptop had on people's lives today? What are your…
Q: Which PIC operating characteristic enables it to reset, particularly when the power supply voltage…
A: Here the question is PIC operating system characterstic enables it to reset, particularly when the…
Q: List three instances of deadlocks that are not tied to a computer system.
A: Answer
Q: A number of switches link two hundred workstations and four servers on a single LAN. You're…
A: Please find the answer below:
Q: There are a number of differences to be noted between desktop computing and ubiquitous computing,…
A: Please find the answer below :
Q: pose you are given an alphabet consisting of several symbols as well as the uencies with which the…
A: Here in this question we have given some alphabet with some frequency and we have asked to apply…
Q: What exactly is the computer brain?
A: Computer brain: To put it simply, a computer is an electronic machine that receives input data,…
Q: Find out about the most recent ten cyber-attacks on computers, networks, and information security,…
A: Explanation: An attack is any effort to obtain unauthorised access to or utilise assets in order to…
Q: A number of switches link two hundred workstations and four servers on a single LAN. You're…
A: Explanation: The solution is below: Broadcast storms are a serious concern now: To control them, do…
Q: Using Java
A: As per the requirement program has been developed. Algorithm: Step 1: Write the main() method Step…
Q: Discuss the importance of maintaining a good relationship while transitioning from a legacy system…
A: Enterprise resource planning (ERP): Enterprise resource planning (ERP) is a term that refers to a…
Q: Why are information systems so important for today's corporate operations and management?
A: Answer
Q: Please provide a short explanation of why the long-term costs of software engineering approaches and…
A: In general, programming's lifespan is dependent upon the use of software engineering methods.
Q: We have seen the fast spread of Artificial Intelligence as an intelligent machine in numerous…
A: Clarification: Artificial intelligence is having an influence on the future of almost every sector…
Q: Why are information systems so important for today's corporate operations and management?
A: Information systems: Information systems convert unstructured facts or data to useful data. The…
Q: Complete the following use case description for a University Management System. When a student…
A: Answer
Q: Lwhat are the different types of session state modes? i. List several ASP.net session state modes.
A: Session State Modes: The session object maintains information about each user enrolled in to the…
Q: The internet has had an influence on system architecture, but how has it done so
A: Answer:
Q: Find out about the most recent ten cyber-attacks on computers, networks, and information security,…
A: Introduction: Any offensive action that targets computer information systems, computer networks,…
Q: When compared to a centralised computer system, why do some companies choose for a dispersed one?
A:
Q: Comparing top-down and bottom-up approaches to information security, what are the benefits of each?
A: Top-down and bottom-up: Despite the fact that these two models represent two opposite tactics, they…
Q: When it comes to information and communication technology, how is the internet considered to be at…
A: Development: The internet is the most powerful tool of the twenty-first century, and it has helped…
Q: What is the best way to set up a network for people who are always on the go?
A: Let's see the solution in the next steps
Q: What is the best way to set up a network for people who are always on the go?
A: Explanation: Computing devices that are linked to one other and may exchange data and resources.…
Q: Consider the difference between the E2 CMOS cell in a GAL and the fusible link in a PAL.
A:
Q: 4. The moment generating function of the random variable X is given by 10 Mx (t) = exp{2e¹-2) and…
A: Please find the handwritten answer of the question below in second step:
Q: When transitioning from an older system to an integrated ERP system, discuss the importance of…
A: Define: ERP is implemented as part of a larger organizational transformation. An organizational…
Q: The design team for a simple, single-issue processor is choosing between two pipelined…
A:
Q: If money wasn't a problem. Describe your dream computer's attributes. What would you do with it?…
A: According to the information given:- We have to describe the dream computer as per the personal…
Q: What are the advantages of using a packet sniffer software program?
A: Origination: A packet sniffer, also a known as a packet analyser, allows network managers to…
Q: What is Windows 10's level of security?
A:
Q: Examine the differences between pixel graphics and object graphics, as well as the benefits and…
A: Pixel graphics are made of pixel bits are used for creating raster images.
Q: Propose an approximation algorithm for solving the independent-set problem where an independent set…
A:
Q: Describe the process by which analog sound is converted into digital sound in a computer system.
A: Answer: In a digital audio system, an analog electrical signal representing sound is converted by an…
Q: Why is scope creep so common throughout the information system design phase?
A: In the given questionS cope creep refers to how a project’s requirements tend to increase over a…
Q: Benefits of information system in the control and management of Covid
A: Please find the answer below :
Q: Which PIC operating characteristic enables it to reset, particularly when the power supply voltage…
A: Built-in Power-on-reset is used to reset the device when the power is turned on, not when the…
Happy weekend:)
I will upvote
Step by step
Solved in 3 steps with 1 images

- A contact list is a place where you can store a specific contact with other associated information such as a phone number, email address, birthday, etc. Write a program that first takes as input an integer N that represents the number of word pairs in the list to follow. Word pairs consist of a name and a phone number (both strings). That list is followed by a name, and your program should output the phone number associated with that name. Ex: If the input is: 3 Joe 123-5432 Linda 983-4123 Frank 867-5309 Frank the output is: 867-5309 Your program must define and call the following function. The return value of GetPhoneNumber is the phone number associated with the specific contact name.string GetPhoneNumber(vector<string> nameVec, vector<string> phoneNumberVec, string contactName) #include <iostream>#include <vector>using namespace std; string GetPhoneNumber(vector<string> nameVec, vector<string> phoneNumberVec, string contactName) {} int main()…A contact list is a place where you can store a specific contact with other associated information such as a phone number, email address, birthday, etc. Write a program that first takes as input an integer N that represents the number of word pairs in the list to follow. Word pairs consist of a name and a phone number (both strings), separated by a comma. That list is followed by a name, and your program should output the phone number associated with that name. Output "None" if name is not found. Ex: If the input is: 3 Joe,123-5432 Linda,983-4123 Frank,867-5309 Frank the output is: 867-5309 Your program must define and call the following function. The return value of GetPhoneNumber is the phone number associated with the specific contact name.string GetPhoneNumber(vector<string> nameVec, vector<string> phoneNumberVec, string contactName) Hint: Use two vectors: One for the string names, and the other for the string phone numbers.A contact list is a place where you can store a specific contact with other associated information such as a phone number, email address, birthday, etc. Write a program that first takes in word pairs that consist of a name and a phone number (both strings). That list is followed by a name, and your program should output the phone number associated with that name. Ex: If the input is: Joe 123-5432 Linda 983-4123 Frank 867-5309 Frank the output is: 867-5309 please make it simple im a starter at python
- Solve in Python: A contact list is a place where you can store a specific contact with other associated information such as a phone number, email address, birthday, etc. Write a program that first takes in word pairs that consist of a name and a phone number (both strings), separated by a comma. That list is followed by a name, and your program should output the phone number associated with that name. Assume the search name is always in the list. Ex: If the input is: Joe,123-5432 Linda,983-4123 Frank,867-5309 Frank the output is: 867-5309I very much need help with this problem A contact list is a place where you can store a specific contact with other associated information such as a phone number, email address, birthday, etc. Write a program that first takes in word pairs that consist of a name and a phone number (both strings), separated by a comma. That list is followed by a name, and your program should output the phone number associated with that name. Assume the search name is always in the list. Ex: If the input is: Joe,123-5432 Linda,983-4123 Frank,867-5309 Frank the output is: 867-5309Using C++, A contact list is a place where you can store a specific contact with other associated information such as a phone number, email address, birthday, etc. Write a program that first takes as input an integer N that represents the number of word pairs in the list to follow. Word pairs consist of a name and a phone number (both strings). That list is followed by a name, and your program should output the phone number associated with that name. Ex: If the input is: 3 Joe 123-5432 Linda 983-4123 Frank 867-5309 Frank the output is: 867-5309 A. Create a struct in your program called ContactInfo to store a name and a phone number. B. Define and call the following function. The return value of GetPhoneNumber is the phone number associated with the provided contact name. If the name is not found, the function should return "not found". string GetPhoneNumber(ContactInfo contacts[], int size, string contactName) C. Your main function should declare an array of ContactInfo structs of size…
- I am having a difficult time with this problem I need help. A contact list is a place where you can store a specific contact with other associated information such as a phone number, email address, birthday, etc. Write a program that first takes in word pairs that consist of a name and a phone number (both strings), separated by a comma. That list is followed by a name, and your program should output the phone number associated with that name. Assume the search name is always in the list. Ex: If the input is: Joe,123-5432 Linda,983-4123 Frank,867-5309 Frank the output is: 867-5309You have a list of student ID’s followed by the course number (separated by a space) that the student is enrolled in. The listing is in no particular order. For example, if student 1 is in CS100 and CS200 while student 2 is in CS105 and MATH210 then the list might look like this:1 CS1002 MATH2102 CS1051 CS200Write a program that reads data in this format from the console. If the ID is −1 then stop inputting data. Use the HashMap class to map from an Integer (the student ID) to an ArrayList of type String that holds each class that the student is enrolled in. The declaration should look like this:HashMap<Integer, ArrayList<String>> students =new HashMap<Integer, ArrayList<String>>();After all data is input, iterate through the map and output the student ID and all classes stored in the vector for that student. The result should be a list of classes organized by student ID.*in java* A contact list is a place where you can store a specific contact with other associated information such as a phone number, email address, birthday, etc. Write a program that first takes as input an integer N that represents the number of word pairs in the list to follow. Word pairs consist of a name and a phone number (both strings), separated by a comma. That list is followed by a name, and your program should output the phone number associated with that name. Assume that the list will always contain less than 20 word pairs. Ex: If the input is: 3 Joe,123-5432 Linda,983-4123 Frank,867-5309 Frank the output is: 867-5309 Your program must define and call the following method. The return value of getPhoneNumber() is the phone number associated with the specific contact name.public static String getPhoneNumber(String[] nameArr, String[] phoneNumberArr, String contactName, int arraySize) Hint: Use two arrays: One for the string names, and the other for the string phone numbers.…
- I really. need help with this problem please. A contact list is a place where you can store a specific contact with other associated information such as a phone number, email address, birthday, etc. Write a program that first takes in word pairs that consist of a name and a phone number (both strings), separated by a comma. That list is followed by a name, and your program should output the phone number associated with that name. Assume the search name is always in the list. Ex: If the input is: Joe,123-5432 Linda,983-4123 Frank,867-5309 Frank the output is: 867-5309In Java: When analyzing data sets, such as data for human heights or for human weights, a common step is to adjust the data. This can be done by normalizing to values between 0 and 1, or throwing away outliers. For this program, adjust the values by subtracting the smallest value from all the values. The input begins with an integer indicating the number of integers that follow. Assume that the list will always contain less than 20 integers. Ex: If the input is: 5 30 50 10 70 65 the output is: 20 40 0 60 55 For coding simplicity, follow every output value by a space, even the last one. Your program must define and call a method:public static int getMinimumInt(int[] listInts, int listSize) import java.util.Scanner; public class LabProgram {/* Define your method here */ public static void main(String[] args) {/* Type your code here. */}}In C++. When analyzing data sets, such as data for human heights or for human weights, a common step is to adjust the data. This can be done by normalizing to values between 0 and 1, or throwing away outliers. For this program, adjust the values by subtracting the smallest value from all the values. The input begins with an integer indicating the number of integers that follow. Assume that the list will always contain less than 20 integers. Ex: If the input is 5 30 50 10 70 65, the output is: 20 40 0 60 55 For coding simplicity, follow every output value by a space, even the last one. Your program must define and use the following function:int GetMinimumInt(vector<int> listInts)

