A Firewall log showing an attack is shown in Figure Q5. Answer the following questions based on the log. July 20 14:45:11 %PIX-4-400034: IDS: 6050 DNS host info request from ATTACK.123 to BANK.7 on interface outside July 20 14:42:01 %PIX-4-400036: IDS: 6052 DNS high zone transfer request from ATTACK.123 to BANK.7 on interface outside Figure Q5 Firewall log. (a) Explain why firewall plays a central role in network forensic investigation? (b) (c) (d) What attack is detected by the firewall as shown in Figure Q5? Why a hacker would like to launched this attack? Based on the alert as shown in the figure, did the firewall block the attack? Why or why not? Based on the alert as shown in the figure, did the DNS misconfigured? Explain your answer.
A Firewall log showing an attack is shown in Figure Q5. Answer the following questions based on the log. July 20 14:45:11 %PIX-4-400034: IDS: 6050 DNS host info request from ATTACK.123 to BANK.7 on interface outside July 20 14:42:01 %PIX-4-400036: IDS: 6052 DNS high zone transfer request from ATTACK.123 to BANK.7 on interface outside Figure Q5 Firewall log. (a) Explain why firewall plays a central role in network forensic investigation? (b) (c) (d) What attack is detected by the firewall as shown in Figure Q5? Why a hacker would like to launched this attack? Based on the alert as shown in the figure, did the firewall block the attack? Why or why not? Based on the alert as shown in the figure, did the DNS misconfigured? Explain your answer.
Principles of Information Security (MindTap Course List)
6th Edition
ISBN:9781337102063
Author:Michael E. Whitman, Herbert J. Mattord
Publisher:Michael E. Whitman, Herbert J. Mattord
Chapter6: Security Technology: Access Controls, Firewalls, And Vpns
Section: Chapter Questions
Problem 2E
Related questions
Question
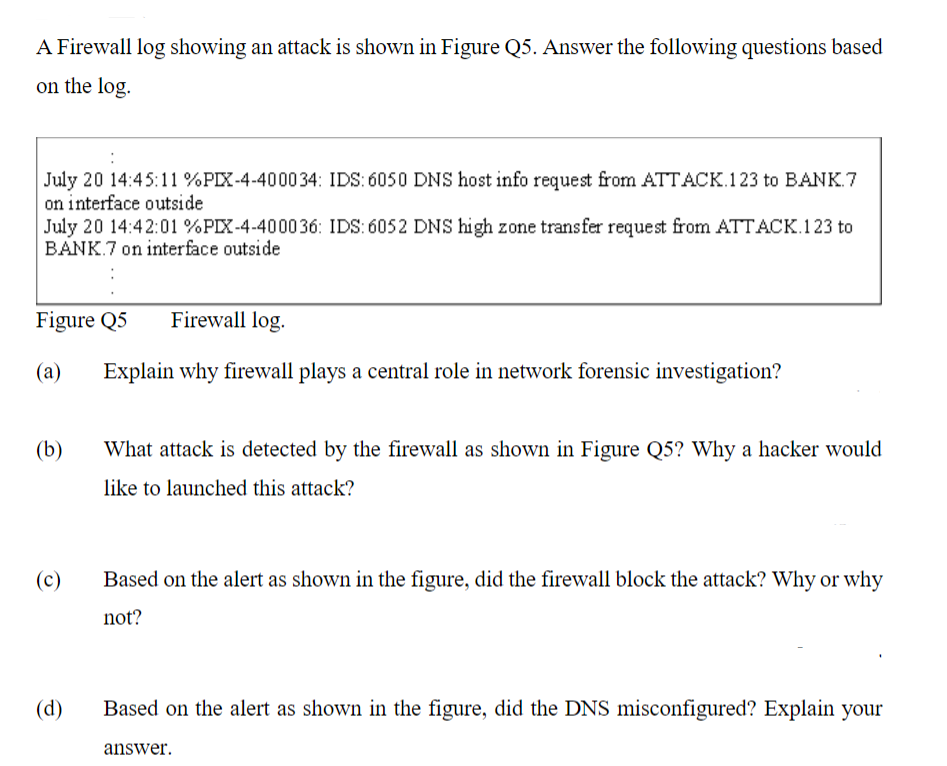
Transcribed Image Text:A Firewall log showing an attack is shown in Figure Q5. Answer the following questions based
on the log.
July 20 14:45:11 % PIX-4-400034: IDS: 6050 DNS host info request from ATTACK.123 to BANK.7
on interface outside
July 20 14:42:01 %PIX-4-400036: IDS: 6052 DNS high zone transfer request from ATTACK.123 to
BANK.7 on interface outside
Figure Q5 Firewall log.
(a)
(b)
(c)
(d)
Explain why firewall plays a central role in network forensic investigation?
What attack is detected by the firewall as shown in Figure Q5? Why a hacker would
like to launched this attack?
Based on the alert as shown in the figure, did the firewall block the attack? Why or why
not?
Based on the alert as shown in the figure, did the DNS misconfigured? Explain your
answer.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 5 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Management Of Information Security
Computer Science
ISBN:
9781337405713
Author:
WHITMAN, Michael.
Publisher:
Cengage Learning,

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Management Of Information Security
Computer Science
ISBN:
9781337405713
Author:
WHITMAN, Michael.
Publisher:
Cengage Learning,

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L