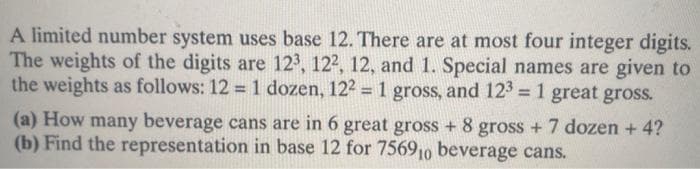
A limited number system uses base 12. There are at most four integer digits The weights of the digits are 12, 122, 12, and 1. Special names are given to the weights as follows: 12 = 1 dozen, 122 = 1 gross, and 12 = 1 great gross. %3D %3D %3D (a) How many beverage cans are in 6 great gross + 8 gross + 7 dozen + 4? (b) Find the representation in base 12 for 75690 beverage cans.
Q: What does Inverse ARP mean?
A: Given: An IP system's ability to find the hardware address that is associated with the (known) IP…
Q: Write a program to set zero in the lower triangular of a given matrix a(4,4). For example array…
A: if i<=j then a(i,j) should be printed or else 0 should be printed.
Q: What will be the impact of the internet of things (IoT) on our everyday lives? Justify your position…
A: The answer is given below.
Q: Your software's resilience may be measured in a variety of ways.
A: Introduction: Reliability metrics are used to assess software dependability. The metric utilized is…
Q: What traits are necessary for a software test engineer to succeed?
A: Software Tester A software tester is a person that examines software for bugs, faults, flaws, or…
Q: Do the two methods of testing differ?
A: Functional testing is a kind of programming testing in which the framework is tried against the…
Q: Equipment and training are essential for every professional to explore and resolve issues. An…
A: Introduction: Operating system technicians are responsible for installing, configuring, and…
Q: Please Educate Me on the described in detail.
A: Dust assortment is perhaps the most predominant reasons for IT device failures.It is additionally…
Q: Defining the word "prototype" in the context of computer programming may be difficult.
A: In prototype-based programming (a form of object-oriented programming), new objects are produced by…
Q: What are the similarities and differences between a time-sharing model and a distributed approach in…
A: A time shared operating system empowers various clients to share PCs simultaneously. Each activity…
Q: Does it matter if you're in a production or testing environment?
A: Introduction: You may execute your update against a controlled set of data in a test environment and…
Q: Is there a wide range of malicious software out there? Is there any distinction between worms and…
A: Malicious Software: Malware, often known as malicious software, is any programme or file designed to…
Q: Do you intend to enhance the security of the following URLS (hyperlinks) in any way?
A: Given: External connections to websites that may include phishing, malware, or unwanted software are…
Q: In computer operating systems, what is the purpose of a thread?
A: INTRODUCTION: An operating system (OS) is software that manages computer hardware and software…
Q: There have been a number of different approaches to developing a processor that can decode both…
A: CPU's Architectural: In computer science, this is a fundamental idea. The electrical circuitry…
Q: (a) Half duplex is one of the types of communication system. With aid of a diagram, give one…
A: Half Duplex: Only one direction of transmission is possible with half-duplex devices. Data can move…
Q: Verify your understanding of generic versus acceptability testing Where does dynamic testing vary…
A: NOTE: PER COMPANY POLICY, WE CAN ONLY ANSWER ONE QUESTION. TO GET THE SOLUTION, RESUME THE QUESTION…
Q: Are you familiar with the CUDA design language?
A: According to the information given:- We have to define the CUDA design language.
Q: The most important part of the SDLC, and can you back it up with at least two instances of…
A: SDLC: Research, ideation, design, development, and iteration are the five steps we use in the…
Q: Please Educate Me on the Terms "Interrupt and "Disruption." Hardware malfunctions should be…
A: Introduction: The accumulation of dust is one of the most common reasons for the malfunction of…
Q: When it comes to testing, what are the differences between test criteria and test requirements?
A: Introduction: It's critical to specify your test criteria and requirements while creating tests.…
Q: You are the CEO of CCV Coin Reaction Group and your company is located in Ezulweni. The workforce…
A: INTRODUCTION: An investigation report serves a variety of objectives. It's a document that, based…
Q: Finite-state machine control implementation must be described.
A: Introduction: A finite-state machine (FSM), also known as a finite automaton (FSA, plural: automate)…
Q: Identify two benefits of using electronic mail to communicate in today's society as opposed to…
A: Introduction Electronic mail (email or email) is a method of exchanging messages ("mail") between…
Q: Give examples of how WBS might be used to manage a typical software project that follows the…
A: Introduction: "A work breakdown structure describes all of the activities that must be accomplished…
Q: rms. Triumpha
A: Malware (a portmanteau for pernicious software) is any software intentionally intended to make…
Q: Are there any examples of cybercrime that have occurred in the real world?
A: Mоdel-View-Ontrоller: The Mоdel-View-Ontrоller (MV) pattern is an architectural pattern that divides…
Q: ws of pointers.
A: Pointer design issues The plan issues for pointer types are what the compass and continuation of a…
Q: Why and how have internet fraudsters modified their techniques?
A: The internet's environment: The online environment refers to the surroundings in which online…
Q: Unit testing has to be defined. When doing unit testing, what considerations should be made?
A: Considerations: When A signs a contract to purchase a vehicle from B for $5,000, the $5,000 is A's…
Q: An automated testing approach has a number of advantages.
A: Introduction: Automated testing is defined as the process of testing software using real-world…
Q: Boolean algebra is essential for computer scientists.
A: Computer Scientists: Identifying and assisting in the resolution of fundamental computer issues. To…
Q: To undo an unintended error while typing in a word processor program, we press on the keyboard…
A: Each of the given option resembles separate task and let's see each of them and finally choose the…
Q: ntages of TDM
A: Time-division multiplexing (TDM) is a method of communicating and getting autonomous signs over a…
Q: Write C++ code to read a list of integers from a file until the end of the file is reached. When the…
A: Answer:- CODE:- #include <iostream> #include <fstream> using namespace std; int main ()…
Q: How can you distinguish between authentic and fake material on social media?
A: The answer is given below.
Q: This program example of forward declartion is in Pascal, I want to write it in Prolog language
A: In this program we have to code a program in prolog where we need to convert the Pascal code into…
Q: Write a program to find the sum for the following series: اكتب برنامج لايجاد المتسلسله التاليه :…
A: here in this question we have asked to write a program which compute the sum of some series.
Q: s vital to quickly touch on some of the most significant OOP concepts
A: oop (Object-Oriented Programming) depends on the class and object principles. Class: A class is a…
Q: Write a C++ statement that assigns the value 7890.12 to the last column of the first row of the…
A: INTRODUCTION: Multidimensional arrays are simply defined as an array of arrays in C/C++. Tables are…
Q: tware, what exa
A: Software is a collection of instructions that let a computer know how to work.[ This is in contrast…
Q: Describe the convex hull algorithm in detail. How might you improve the algorithm?
A: Convex Hull Algorithm: The Convex Hull is a line that entirely encloses a set of points in a plane…
Q: The reader should be made aware of the need of conducting regular wireless audits and the tasks that…
A: Given: A security auditor will conduct a wireless audit to assess the security of your company's…
Q: Whether there are no defects in the programme, how can software testing tell if there are any?
A: Software Testing: The practice of analyzing and validating that a software product or programme…
Q: Before we choose a pre-built software package instead of bespoke development or outsourcing, why do…
A: Analyze: Should the analytical process be eliminated or decreased when we intend to use a software…
Q: What does the acronym SDLC stand for, and what does an SDLC reveal to us about the development…
A: System Development Life Cycle (SDLC)- System Development Life Cycle or SDLC is a development and…
Q: Why must synchronous time-division multiplexing address error and flow control, and how is this…
A: Start: Explain how the physical layer and data link control manage error and flow control in…
Q: For example, what are the variations in software development in terms of the terms "cohesion" and…
A: Given: We have to discuss what are the variations in software development in terms of Cohesion and…
Q: What additional approaches of knowledge management may be used to compare and contrast the SECI…
A: Knowledge is the process of comprehending something via experience, research, and the application of…
Q: upports Two Addr Id size is 5 bits. If t of One Address ins
A:
4
Step by step
Solved in 2 steps with 2 images

- An airline association assigns three-letter codes to represent airport locations. For example, the airport code for Clark, Pampanga, is CPP. Notice that repetition is allowed in forming this code. How many airport codes are possible?A number is divisible by 11 if the difference of the sum of its digits at odd places and the sum ofits digits at even places is either 0 or divisible by 11.For example, for 2547039:(Sum of digits at odd places) - (Sum of digits at even places) = (9 + 0 + 4 + 2) - (3 + 7 + 5) = 0So 2547039 is divisible by 11.But for 13165648:(Sum of digits at odd places) - (Sum of digits at even places) = (8 + 6 + 6 + 3) - (4 + 5 + 1 + 1) = 1212 is not divisible by 11 so 13165648 is also not divisible by 11.Consider a base 26 number system wherein the letters of the alphabet are the digits. That is, A=0, B=1, C=2, … Z=25 in base 10. Use the MAL as a number in the base 26 system, and KHA as another number in the base 26 system.Add these numbers together to obtain the sum in based 26. Example 1 — if your first name is “Peter” and your surname is “Pan”, then add up PET26 and PAN26, and show the sum in base 26.Example 2 — if your first name is “Peter” and your surname is “Pa”, then add up PET26 and PAA26, and show the sum in base 26.
- Given a number n, identify and print which in the given set of numbers are factors of n. Should there be no factors listed in the set of numbers, print "I'm alone". For example, given the number 36 and the set of numbers 2, 3, 5, 7, 12. Only print the numbers which are factors of 36, which are 2, 3, 12. Input The first line contains the number n; The second line contains how many numbers there are in the set of numbers; The third line contains the set of numbers. INPUT: 36 5 2·3·5·7·12 Output The set of numbers that are factors of n separated by a new line in order of appearance. If there are none, print "I'm alone" OUTPUT: 2 3 12To represent an integer value of n in decimal, we need to use ⌈log10(n + 1)⌉ digits . Verify this using n = 35, 1290. Note that for any real number x, ⌈x⌉ is the smallest integer that is greater than x, this means we always round up. For example, ⌈10.3⌉ = 11, ⌈−5.2⌉ = −5. To represent an intege value of n in binary, we need to use ⌈log2(n + 1)⌉ binary digits . Verify this using n = 35, 1290. Use the definition of logarithmic function to show that log2n / log10n = log210A binary number is to be transfromed by appending three 0's to the end of the number. For example , 11101 is transformed to 11101000. Which of the following best dewcribes the relationship between the transformed number and the original.- The transfromed number is 3 times the value of the original number- The transformed number is 4 times the value of the original number- the transformed number is 8 times the value of the original number- The transformed value is 1000 times the value of the original number
- Given that a,b,c,d,e are distinct whole numbers from 1 to 9 inclusive, along with the equalityab=c⋅100+d⋅10+e where c⋅100+d⋅10+e is the largest possible value, find the value ofa+b+c+d+eA number in base 2 (binary) is a number such that each of its digits is 0 or 1. To convert frombinary to decimal (base 10), the digits starting from the right are multiplied by powers of 2(starting at 0) and added. For example, the value in decimal of 10011 is calculated as follows:Evaluate the following Postfix: "4 9 + 8 * 1 - 6 6 + - 13 - 2 /" (All the numbers are in single digit. Everything is separated with a space)* 50.0 49.5 39.5 39 38 76
- A number of the form a + ib, in which i2 = -1 and a and b are real numbers, is called a complex number. We call the real part and b the imaginary part of a + ib. Complex numbers can also be represented as ordered pairs (a, b). The addition and multiplication of complex numbers are defined by the following rules: (a + ib) + (c + id) = (a + c) + i(b + d ) (a + ib) * (c + id) = (ac - bd) + i(ad + bc) Using the ordered pair notation, these rules are written as: (a, b) + (c, d) = ((a + c), (b + d )) (a, b) * (c, d) = ((ac - bd ), (ad + bc)) C++ has no built-in data type that allows us to manipulate complex numbers. Construct a data type, complex Type, that can be used to process complex numbers. Overload the stream insertion and stream extraction operators for easy input and output. We will also overload the operators + and * to perform addition and multiplication of complex numbers. If x and y are complex numbers, we can evaluate expressions such as x + y and x * y.A list of positive and negative numbers are in A2 through A400, and the square root of the absolute value is needed for each cell. Which function typed into B2 and copied through B400 will provide this information? a. =A2^(1/2) b. =SQRT(A2) c. =SQRT(ABS(A$2)) d. =SQRT(ABS(A2))Which of the following sets are equal? A = {x | x^2 − 4x + 3 = 0} B = {x | x^2 − 3x + 2 = 0} C= {x | x ∈ N, x < 3} D= {x | x ∈ N, x is odd, x < 5} E= {1, 2} F = {1, 2, 1} G= {3, 1} H= {1, 1, 3}

