A matrix of characters schematically represents a swamp. The swamp is composed of muddy areas, represented with the character, and rocky areas, represented with the *' character. The matrix size can be defined using #define, however it should be no greater than 25 rows and 80 columns. Example of swamp: Write a C program that searches a path in the swamp, from the left to the right, without jumps, only including consecutive rocky areas. Suppose that each rocky area can have at most one other rocky area on its right (there are no branches), i.e., either on the same row, or in the previous row, or in the following one. The program shall print the row sequence of the path (the columns are implicit – there shall be a rocky area for each column), or report that no path exists. For example: 1 3 4 Path: 23 43 43 2 3 4 3 4 Hint: in a preliminary version, use a predefined matrix of strings and test the program; then modify the program and read the swamp from the keyboard input (in the future it would be possible to read it from a file).
A matrix of characters schematically represents a swamp. The swamp is composed of muddy areas, represented with the character, and rocky areas, represented with the *' character. The matrix size can be defined using #define, however it should be no greater than 25 rows and 80 columns. Example of swamp: Write a C program that searches a path in the swamp, from the left to the right, without jumps, only including consecutive rocky areas. Suppose that each rocky area can have at most one other rocky area on its right (there are no branches), i.e., either on the same row, or in the previous row, or in the following one. The program shall print the row sequence of the path (the columns are implicit – there shall be a rocky area for each column), or report that no path exists. For example: 1 3 4 Path: 23 43 43 2 3 4 3 4 Hint: in a preliminary version, use a predefined matrix of strings and test the program; then modify the program and read the swamp from the keyboard input (in the future it would be possible to read it from a file).
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:James Kurose, Keith Ross
Chapter1: Computer Networks And The Internet
Section: Chapter Questions
Problem R1RQ: What is the difference between a host and an end system? List several different types of end...
Related questions
Question
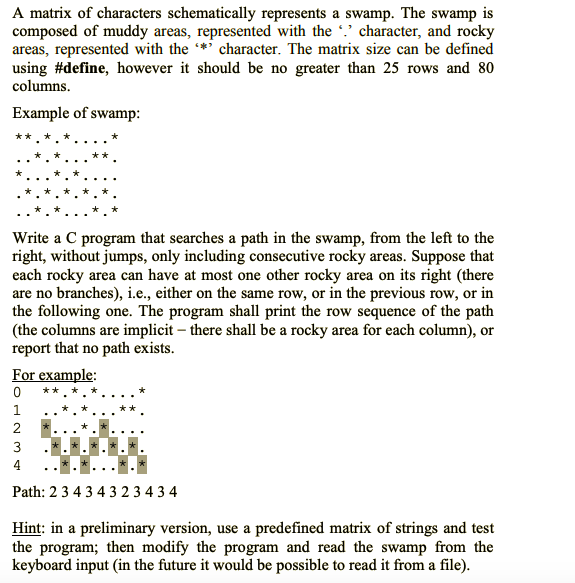
Transcribed Image Text:A matrix of characters schematically represents a swamp. The swamp is
composed of muddy areas, represented with the character, and rocky
areas, represented with the *' character. The matrix size can be defined
using #define, however it should be no greater than 25 rows and 80
columns.
Example of swamp:
Write a C program that searches a path in the swamp, from the left to the
right, without jumps, only including consecutive rocky areas. Suppose that
each rocky area can have at most one other rocky area on its right (there
are no branches), i.e., either on the same row, or in the previous row, or in
the following one. The program shall print the row sequence of the path
(the columns are implicit – there shall be a rocky area for each column), or
report that no path exists.
For example:
1
3
4
Path: 23 43 43 2 3 4 3 4
Hint: in a preliminary version, use a predefined matrix of strings and test
the program; then modify the program and read the swamp from the
keyboard input (in the future it would be possible to read it from a file).
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

Recommended textbooks for you

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:
9781337093422
Author:
Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:
Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:
9780133750423
Author:
VENIT, Stewart
Publisher:
Pearson Education

Sc Business Data Communications and Networking, T…
Computer Engineering
ISBN:
9781119368830
Author:
FITZGERALD
Publisher:
WILEY