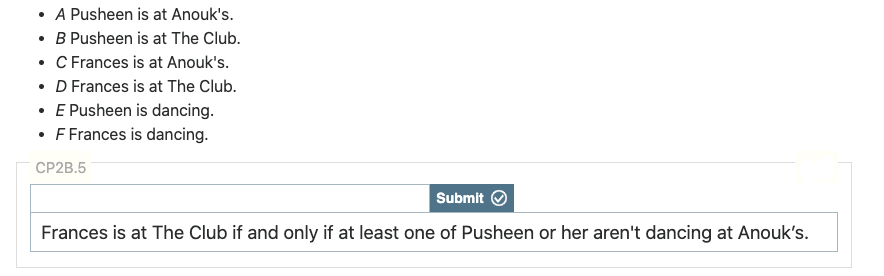
• A Pusheen is at Anouk's. • B Pusheen is at The Club. • C Frances is at Anouk's. • D Frances is at The Club. E Pusheen is dancing. F Frances is dancing. CP2B.5 Submit Frances is at The Club if and only if at least one of Pusheen or her aren't dancing at Anouk's.
Q: What's the dissimilarity between logical and physical data flow diagrams?
A: 1. A database management system (or DBMS). 2. It is essentially just a computer-based data storage…
Q: A DSS is an informational tool designed to help businesses settle matters of judgment, resolve…
A: Let's look at the answer to the aforementioned issue. The following list includes many DSS (Decision…
Q: A machine specifically designed to store and deliver web pages is called a web server.
A: A machine that manages websites is referred to as a web server. A computer software is responsible…
Q: What outputs might you expect from conceptual data modeling
A: Dear Student, The answer to your question is given below -
Q: Which way do you feel about Data Model?
A: Although the data model has several drawbacks, the two most significant ones are listed below:…
Q: a.What makes VPN distinct from MAN? Give some instances of each. In a virtual private network (VPN),…
A: Redundancy: Data redundancy occurs when the identical piece of data is stored in two locations. This…
Q: An I/O controll method where the devices tell the CPU they have data to send is... Input I/O O…
A: Disclaimer: “Since you have posted multiple questions, we will provide the solution only to the…
Q: Are OSes primarily intended to perform a certain function?
A: Operating system handles the working and maintenance of hardware components in an application.
Q: When using a MAC, an attacker attempts to change both the Tag (the MAC) and the ciphertext (message…
A: INTRODUCTION: The acronym for the tag is MAC. It is a piece of information that the sender and the…
Q: Identifying the most common network topologies is essential. Which do you think is the most…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: Using the BFS algorithm as an example, please explain the role that color codes play in the process.…
A: Algorithm for Breadth First Search (BFS): It is a graph traversal method that begins at the root…
Q: Give a concise description of model calibration as an iterative process and provide an example
A: Solution: Given, Give a concise description of model calibration as an iterative process and…
Q: What is the purpose of using a hash value to verify a message? In order to exploit a MAC algorithm,…
A: The transmitter generates a hash function by concatenating a message with a symmetric key. The…
Q: b. The CPU is idle for the bulk of the time when the computer is being utilized optimally, which is…
A: Introduction The central processing unit (CPU) is a computer's brain since it has all the hardware…
Q: In software development, what are the pros and cons of doing static analysis on the code itself?
A: Pros:1. Software development can help businesses become more efficient and productive.2. It can help…
Q: Q. ________ is the process of dividing the disk into tracks and sectors A.Tracking B.Formatting…
A: A disk is secondary memory storage medium which stores data permanently into it. Tracks and sectors…
Q: Just
A: Computer programming is a way of communicating with computer using a language which is…
Q: video data sequences When and where would you want to utilize storage dafa eype? maximize the…
A: In most cases, the video data is presented in the form of continuous analogue impulses. In order to…
Q: Please I need an explanation of the code package lap; class Employee { private String…
A: Java is a high-level programming language. It is an object-oriented programming language that…
Q: The way information is stored in centralized and decentralized version control systems is distinct.…
A: When dealing with several developers on the same project, many of us are acquainted with version…
Q: Two non-financial examples should be given to illustrate the ACID paradigm in database design.
A: Introduction: RAID (redundant array of independent discs) is a technique for protecting data in the…
Q: Need this in C++ Combinatorics Inputs: positive integer n (number of letters in a password),…
A: These question answer is as follows,
Q: Transporting a big file using block chaining or feedback modes requires a comparable amount of…
A: Dear Student, The answer to your question is given below -
Q: Import the text file PB Participants.txt as a table, using Tab delimiters and the General column…
A: Open excel and create the participants name list and save it as tab delimiters txt file. (like…
Q: How to write a calculator that using _getch() (or getch(), getchar()) in C++
A: Dear Student, The required source code implementation and expected output of your program is given…
Q: However, even after completing the debugging process, the issue still persists. At this point, what…
A: There is no one-size-fits-all way to fixing your code's problems, but there are debugging techniques…
Q: To what extent may and why are keys shared across block and stream ciphers?
A: INTRODUCTION: Plaintext information is subjected to a series of modifications that change over time…
Q: Provide definitions for all terms associated with data quantification, including but not limited to…
A: The above question is solved in step 2 :-
Q: Create an algorithm for the monotonic evaluation function, algorithm A*. Graph G = (V, E); start…
A: given data: Graph G = (V, E); start vertex s; target vertex r; A-Star(G, s, r) in; out: maps as: V…
Q: A good loop invariant would be “The entire tree is a heap except that nodei might not be greater or…
A: pre-cond: The balanced binary tree rooted at A[r ] is such that its left and right subtrees are…
Q: Check out how Structured English can be used in analyses that don't rely on a system.
A: Introduction: A systems methodology is a procedure that uses instruments for system thinking,…
Q: Where do relational, conceptual, and conceptual data modeling diverge?
A: RDM: Data tables provide relations in a relational data paradigm. These models assume each table has…
Q: Please explain in detail what it is that the AWS database can perform for me
A: AWS (Amazon Web Services) is a comprehensive, ever-evolving cloud-computing platform offered by…
Q: Investigate the results of Web 2.0 and cloud computing.
A: Web 2.0 aims to increase the interconnectivity of Web applications while enabling customers to…
Q: If you say "web pages," please explain what you mean.
A: Web pages are a kind of hypertext document (a collection of text, images, audio, and video, among…
Q: In today's world of rapidly developing technologies, how should we characterize the concept of…
A: The ability of people and organisations to manage the gathering, use, and disclosure of private or…
Q: If a system works well technically, why does it sometimes fall short when it comes to internal…
A: Certain software products and projects with high technological promise fail commercially when they…
Q: these two models—the Vector Space Model (VSM) or Latent Semantic Analysis (LSA)—offers distinct…
A: 1. The process of creating a set of instructions that tells a computer how to perform a task is…
Q: Explain the drawbacks of symmetric key management.
A: Data may be encrypted and decrypted using the same key using symmetric key encryption. Asymmetric…
Q: Your thoughts on this inquiry? Changes in procedure and environment
A: Breed: Process spawning is a method/technique in OS that creates child processes by asking another…
Q: e following method that returns the smallest element in an ArrayList: public static > E m
A: I have coded below:
Q: Can the whole exchange (connection + data) be encrypted? For what purpose? Give an example when any…
A: Yes, The entire connection and data exchange can be encrypted. The process of encrypting plaintext…
Q: Given the parallels between network sniffing and wiretapping, which of the following is the most…
A: Introduction: Network sniffing and wiretapping have some similarities. Wiretapping and network…
Q: When do we say something is "debugged?" I don't see how this relates to actual testing.
A: Debugging: What is it? Why does it matter for testing? Answer: Finding and fixing weaknesses in…
Q: Answer in C++ only Ron opened his new restaurant and prepared the first free meal for everyone! You…
A: I have completed the code using C++.
Q: de should form it eklg Basic list structure, python code. Can you explain this while using…
A: 1. Taking a variable employee_name and asking the user to enter the employee name input() is used to…
Q: es followed by " seconds". End with a newline. Example output for ounces = 7: 42 seconds import…
A: Code:
Q: Using python Create 2 functions, iterative and recursive approach, with parameter n which generates…
A: algorithm using loop:- set first=0 set second =1 if n>=1 display first,second iterate in…
Q: Some argue network neutrality prevents innovation and discourages telecommunications companies from…
A: Introduction Network neutrality is the principle that all Internet traffic should be treated…
Q: Where do centralized and decentralized version control systems differ? Which are the top two…
A: Control software: Control software is a type of software designed to control the operation of a…
Step by step
Solved in 2 steps with 1 images

- A school has 100 lockers and 100 students. All lockers are closed on the first day of school. As the students enter, the first student, denoted as S1, opens every locker. Then the second student, S2, begins with the second locker, denoted as L2, and closes every other locker. Student S3 begins with the third locker and changes every third locker (closes it if it was open and opens it if it was closed). Student S4 begins with locker L4 and changes every fourth locker. Student S5 starts with L5 and changes every fifth locker, and so on, until student S100 changes L100. After all the students have passed through the building and changed the lockers, which lockers are open? Write a program to find your answer and display all open locker numbers separated by exactly one space. (Hint: Use an array of 100 Boolean elements, each of which indicates whether a locker is open (true) or closed (false). Initially, all lockers are closed.)Pleaae answer all subparts....either dislike is ready....this is the information that has to be hard-coded: # hard-coded calls jim = User(first_name='Jim', last_name='Bob', user_id=1000, last_login='June 12, 1998', password='password123') jim.describe_user() jim.greet_user() joe = User('Joe', 'Bob', 1001, 'July 4, 2001', 'babygirl') joe.greet_user() joe.describe_user()
- school has 100 lockers and 100 students. All lockers areclosed on the first day of school. As the students enter, the first student, denotedas S1, opens every locker. Then the second student, S2, begins with the secondlocker, denoted as L2, and closes every other locker. Student S3 begins with thethird locker and changes every third locker (closes it if it was open and opens it ifit was closed). Student S4 begins with locker L4 and changes every fourth locker.Student S5 starts with L5 and changes every fifth locker, and so on, until studentS100 changes L100.After all the students have passed through the building and changed the lockers,which lockers are open? Write a program to find your answer and display all openlocker numbers separated by exactly one space.An employee uses the following coding logic for the company’s resource access: String result = authenticate( . . . ) ; if(result.equals (ACCESS DENY) ) // do stuff after authentication fails e l s e // do stuff after authentication succeeds Suppose values returned by the authenticate function include ACCESS OK and ACCESS DENY. Is there a security flaw in the program? If so, explain and rewrite the code.E5.2.7 Display the total amount HAFH spends on manager salaries (as TotalSalary) and the total amount HAFH spends onmanager bonuses (as TotalBonus).
- Exercise A: In this exercise, you are asking the user to set a alpha numeric password for any website. Put some conditions. Password must be 8 characters long. There must be at-least one uppercase letter There must be at least one number. Then show the user, you have set the correct password or not. Exercise B: This exercise is the extension of the above Exercise. In this exercise we are not checking all the criteria of having a good password. Here ask the user to enter his/her password twice. If both matches, thanks the customer otherwise loop your code until user enters both passwords same.P1 - Loan Payment Schedule Main Street Bank is offering an annual interest rate discount based on the client’s credit score. The discount for each credit score level is provided in the table below. The lowest credit score is 300 while the highest credit score is 850. For example, the new interest rate for a client with a credit score of 755 and a current interest rate of 4.25% would be 4.25 – 0.75 = 3.50% interest rate Credit Score Rating Interest Rate Discount 300 - 579 Very Poor 0.00 580 – 669 Fair 0.25 670 - 739 Good 0.50 740 - 799 Very Good 0.75 800 - 850 Exceptional 1.00 Use modular programming concepts Create a program that includes a WHILE loop to generate a payment schedule for loans that are paid in equal monthly payments Input the loan number and retrieve required loan account from MS_LOANS table Output is shown below Monthly interest is calculated by dividing the yearly interest rate by 12 to get a monthly interest…One of the following items is a run-on (or fused) sentence, another contains a comma splice, and another is correct. Choose the item that is correct. One of the following items is a run-on (or fused) sentence, another contains a comma splice, and another is correct. Choose the item that is correct. The food in that diner is awful besides the service is slow. The food in that diner is awful, besides the service is slow. The food in that diner is awful; besides, the service is slow.
- In cell I8, enter a nested logical function to display Need to Remodel if the apartment is unoccupied (No) AND was last remodeled more than 10 years ago (H3). For all other apartments, display No Change. Although Unit 101 was last remodeled over 10 years ago, the recommendation is No Change because the unit is occupied.Customers who belong to an online retailer’s Free Ship club receive free shipping on all of their purchases. Customers who do not belong to the club must make a minimum purchase of $50 to receive free shipping. If subcondition1 is strClubMember = "Y" and subcondition2 is dblPurchase >= 50, which logical operator should you use to combine both subconditions: AndAlso or OrElse?Question 4.2: Write the client program that sends a number to a server and displays the square root of thesent number as calculated by the server.





