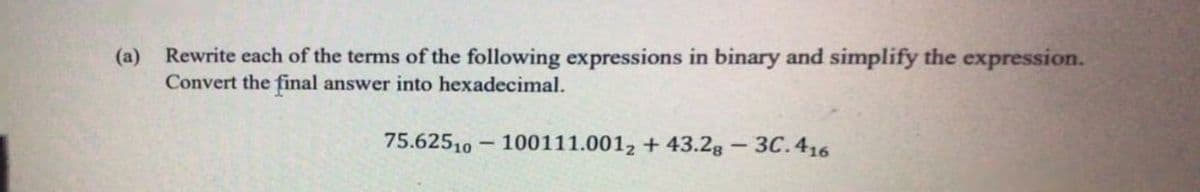
(a) Rewrite each of the terms of the following expressions in binary and simplify the expression. Convert the final answer into hexadecimal. 75.62510 - 100111.001, + 43.2g - 3C.416
Q: data scientist who works in the headquarter of a local bank. Assuming that you have sum model to hel...
A: Lets see the solution.
Q: From where does the following command get its input? tr 'a-z' 'A-Z' |tee file1 >file2 files a-z and ...
A: Tee command is named because of T splitter used in plumbing. Syntax:- Tee [option] [file]
Q: Develop a fictional ethical hacking scenario. Describe the scenario in enough detail that someone ca...
A: Answer: I have given answered in the brief explanation
Q: For learning a predictive model describe the coefficient of determination and explicate its usefulne...
A: COEFFICIENT OF DETERMINATION: When forecasting the outcome of a particular event, the coefficient o...
Q: In what ways does multicore architecture work?
A: A multi-core architecture (also known as a chip multiprocessor) is refers to a general-purpose proce...
Q: How to compute and display the total 2010 census population (CENSUS2010POP). Disregard the first ent...
A: since no csv file is attached I am just giving the code to read a csv file in python and then findin...
Q: LOOP _ProcessArray ;auto-decrement reg2, jump to more if reg2 + 0 If the initialization code has alr...
A: The answer is
Q: Explain, why legacy systems evolve as time passes.
A: The Answer is in Below Steps
Q: Write a regular expression for the given language and construct the NFA using that regular expressio...
A: Here, we have to write regular expression first and then construct the NFA. As per given language, w...
Q: Essay How technology changing our lives?
A: The answer as follows
Q: Early versions of UNIX were available only with a command-driven interface. In more recent years, gr...
A: A GUI or a graphical user interface which comprises of icon, mouse and many other graphic oriented a...
Q: consider an application to support buying and selling vintage musical instruments. Create a CRC card...
A: DESCRIPTION: Relational Database Design: Customer(SSN, Title,First_Name,Middle_Name, Last_Name, Ad...
Q: def only_evens(lst: List[List[int]]) -> List[List[int]]: """Return a list of the lists in lst th...
A: The objective is to write the code for the given data.
Q: Elaborate on the system call which is used for process creation with a neat diagram
A:
Q: Write a program called Question1.java to store some details of computer boxes (serial number, manufa...
A: Program Explanation- Create an array of Computer references, initially empty i.e size 0. A loop tha...
Q: eate an anonymous block that returns the number of students in a section. Prompt for section id. Nam...
A: Lets see the solution.
Q: In terms of data backup and recovery, what should be the top priorities?
A: Introduction : Backing up and recovering data defines the process of generating and archiving duplic...
Q: Suppose the window of a data stream is as shown below. (Most recent bit is on the right side) . 10 1...
A: DGIM Method, estimate the number of 1s in the last k position .
Q: Generate a Project Management Report with financial aspects for the establishment of a wireless LAN ...
A: INTRODUCTION: With the high-speed internet network everywhere, the local network at the campus is st...
Q: 2. Choose the assembler codes to move the value 5678h from physical memory location: 1234h to accumu...
A: Given 5678h is present at physical memory location 1234h. We need to store the data present at memo...
Q: What is lonic Native? Why do we have to load the ionic models and the Cordova plugins for each compo...
A: Ionic Native is indeed a TypeScript wrapper around Cordova/PhoneGap plugins that makes it simple to ...
Q: Part (c) [30 points]. Evaluate each of the following formulas to TRUE or FALSE, and explain your rea...
A: According to the Bartleby guidelines we are suppose to answer only 3 sub part of the question. Kindl...
Q: What are the three stages during the startup of an Oracle database? If a copy of the control file is...
A: Since you have asked multiple questions, we will solve the first one for you. If you want any specif...
Q: write a function arr_to_str in Python that takes in an array of integers and returns a string. exam...
A: The answer is given below:-
Q: What was it that John von Neumann achieved in his lifetime?
A: Von Neumann, John: John von Neumann was born in Budapest, Hungary, on December 28, 1903. His talent ...
Q: Procedure 3. - Define a function named procedure3() that will be called from main() function, the fu...
A: //both c and cpp codes are provided #include <stdio.h>//function procedure3 takes start,end an...
Q: In classification learning, a classifier is presented with a set of Instances that are already class...
A: Decision tree A decision tree is a very specific type of probability tree that enables you to make a...
Q: Octal String: 010 110 101 010 101 111 010 111 111 101 011 011 011 011 010 100 1. Hex String: 1. Base...
A: Octal to hex is. 0B557AFEB6D4
Q: Problem 2 String Generator Write a Python generator that yields all possible strings formed by using...
A: def string_generator(s): a = sorted(s) n = len(a) - 1 while True: yield ''.join(a) ...
Q: 192.168.30.0/24 192.168.10.0/24 IS331 Raer ISR1 Roera POPT PC26 POPT 29TT witc 296024TT Switch4 POPT...
A: Use concept DHCP,Static Routing and VLAN
Q: ms boundary
A: Autonomous System Boundary Router An Autonomous System Boundary Router (ASBR) is a router that run...
Q: Given a graph with 14 edges. What is the missing value 'k' in the following degree sequence, 1, 2, 3...
A: Dear learner, hope you are doing well , I will try my best to answer this question. Thank You!!
Q: Who created the first flash drive?
A: Introduction: Flash Drives: Almost every college student nowadays has a flash drive in their bag. ...
Q: In what year did the first programmed computer come into existence?
A: The Automatic Computing Engine, often known as the Turing Machine, was invented by Alan Turing, the ...
Q: Use the following data type to store data which includes special characters, letters, and numbers wh...
A: Use the following data type to store data which include special character, letter , and number which...
Q: Write an algorithm and draw a flowchart to check whether a person has been vaccinated. If vaccinatio...
A: algorithm and draw a flowchart to check whether a person has been vaccinated. If vaccination with a ...
Q: What is a system unit
A: What is a System Unit and what are the common components inside the system unit? (watch the video in...
Q: Topic: Cryptographic Active Attack Kindly discuss the Modification of Messages in simple terms.
A: Here in this question we have asked to discuss the modification of message attack in cryptography.
Q: ustrative example.
A: given - Discuss bubble sort algorithm. Give an illustrative example
Q: ve num
A: We write the pseudocode and a c++ program for the given problem statement. The explanation of its wo...
Q: mple to illustrate your
A: given - What is Enumerated Integer providing an example to illustrate your point
Q: Defintion: What is a workstation keyboard, and how does it work?
A: A workstation keyboard is an ergonomic keyboard designed to decrease strain and enhance posture. It ...
Q: What are the benefits of using output devices?
A: - We need to talk about the benefits of output devices.
Q: Monitor is a concurrency technique. Is it generally software, hardware, or firmware, or none of the ...
A: An computer monitor is a display device that displays information on a computer. The computer monito...
Q: I was tasked with decoding this right here. It's for bonus points please helppp! It was given in tha...
A: Answer: I have given answered in the brief explanation
Q: Which of these is the largest unit of measurement for data storage capacity?
A: INTRODUCTION: There are several data storage units, and each larger unit includes a certain number o...
Q: This is what l did but not sure if it is correct DATABASE MANAGEMENT ABC Walk-in Clinic is located...
A: Answer: I have given answered in the brief explanation
Q: Let’s think about Kayak with respect to all our design principles: - Learnability - Simplicity -...
A: **Since you have asked multiple questions, we will solve the first three question for you. Heuristi...
Q: multiclass cla
A: Multi class classification: It means classifying the task into more than two classes. To solve this ...
Q: Which mathematicians were influenced by John von Neumann's achievements?
A: The minimax theorem, which he developed in 1928, was a fundamental contribution to mathematical econ...
Computer Science
Step by step
Solved in 2 steps with 2 images

- Show the printout of the following codes with only one character per cell.Indicate the running times of the following codes:Select the correct condition for block size in RSA. a. Must be Greater than log2 ( n ) + 1 b. Must be Greater than or equal to log2 ( n ) + 1 c. Must be Less than or equal to log 2( n ) +1 d. Must be Less than log2 ( n ) +1
- Perform the following subtractions. Assume that all numbers are in 2’scomplement notation. State the carry-in and carry-out, whether overflow or not,and if the result is correct. 11101101 – 00101010Convert the following equations from infix notation to reverse Polish (postfix) notation by using the following formula.Kindly answer the following questions. b. Verify. that the 6-3-1-1 code is a weighted code. Note that for some decimal digits, two different code combinations could have been used. For example, either 0101 or 0110 could represent 4. In each case the combination with the smaller binary value has been used.
- Fill in the blank question: Q. Abbreviation of TPDU is __________________.) Using booth algorithm, find out the following signed multiplications: 7 x (-5) 2) Convert the following decimals to standard floating-point representations: 22.62510 3) Convert the infix expression to postfix expression. Z = (X+Y) + (W/U)PLEASE USE MATLAB (Linear Block Code) Design a (5, 1) code that can correct 2 error bits in each codeword.a. Please write down the generator matrix G, the standard table, and thesyndrome look-up table.b. Please also use an example received word with 2 error bits to demonstrate thedecoding procedure

