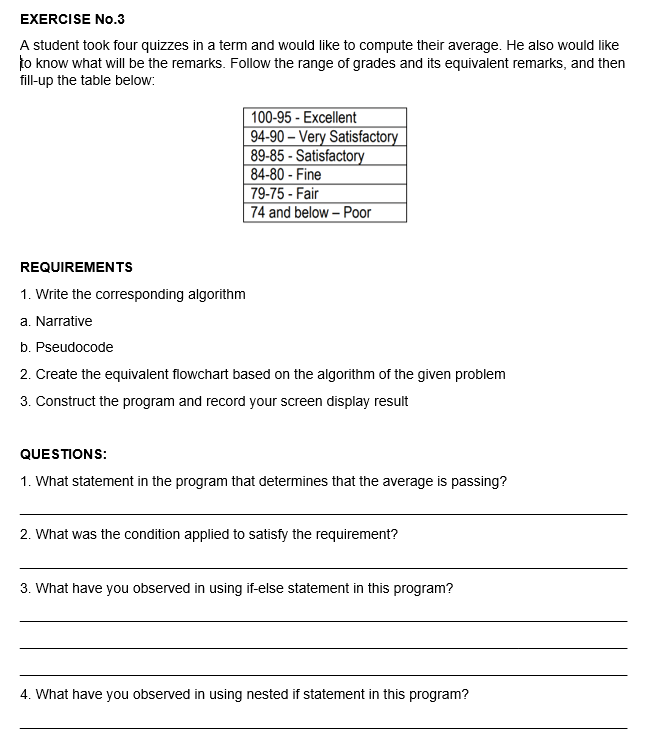
A student took four quizzes in a term and would like to compute their average. He also would like to know what will be the remarks. Follow the range of grades and its equivalent remarks, and then fill-up the table below: 100-95 - Excellent 94-90 – Very Satisfactory 89-85 - Satisfactory 84-80 - Fine 79-75 - Fair 74 and below – Poor
Q: Show that if L is a cfl, then Suffix(L) = {v : uv E L} is also a cfl.
A:
Q: Physical or logical arrangement of network is O A. Routing О В. Тороlogy
A: Answer is Topology Topology refers to layout of a network and how different nodes in a network are c...
Q: Compare and contrast the benefits and drawbacks of using the symbolic math toolbox with MATLAB alone...
A: Introduction: If you already have the Symbolic Toolbox, you may download MATLAB and install it along...
Q: Explain how the waterfall system development paradigm controls the modifications that can happen dur...
A: Actually, SDLC stands for Software Development Life Cycle.
Q: Describe the data conversion and changeover operations.'
A: The answer is given in the below step
Q: Explain when and why batch processing might be preferable than time-sharing processing.
A: Introduction: Time-sharing is a kind of data processing in which several users with various programm...
Q: create buying / selling books online website using php, html, sql, javascript and css
A: 1. Create a Database, Table, and Dump Sample Data 1 CREATE DATABASE allphptricks; To creat...
Q: Apply the improved version of Dijkstra's Algorithm to find the shortest path from A to D in the grap...
A: Below is the answer to above question. I hope this will helpful for you...
Q: How do you anticipate and prepare for the many cyber security dangers that may occur when developing...
A: The Answer is in step-2.
Q: Are there two distinct categories of high-resolution displays or is there a single integrated catego...
A: Introduction: For professional applications, high-resolution monitors are employed since they provid...
Q: A local area network (LAN), as the name implies, is a kind of networking technology that connects de...
A: Let's see the solution
Q: When are user-level threads superior than kernel-level threads?
A: Introduction: The main distinction between User Level and Kernel Level Threads is that User Level Th...
Q: Using MSI (i.e. functional blocks), show how can you design a circuit that has two n-bit unsigned in...
A: The Code for the given question is in step-2.
Q: Consider a project and map it both without and with the inclusion of architecture. How it will affec...
A: Significance of Architecture: => The purpose of architecture is to provide a physical environm...
Q: List the features that cellphones, PDAS, and portable media players have in common with computers, a...
A: Similarlities They all contain a CPU, memory, display functionality and use an operating system th...
Q: The protocol describing standard rules for Internet communication is: О А. ТСР/P
A: Internet communication follow some protocol which ensures reliable transfer of data. It makes sure ...
Q: What is the difference between centralized and paralle/distributed databases when it comes to databa...
A: 1)A centralized database is a kind of data set that contains a solitary data set situated in one are...
Q: What are the key distinctions between the ARM and Core i3 architectures? ARM:
A: Introduction: ARM: Advanced RISC Machines (ARM) is a family of older 32-bit processor cores mainly ...
Q: How do you anticipate and prepare for the many cyber security dangers that may occur when developing...
A: Please find the detailed answer in the following steps.
Q: What precautions should we take to prolong the life of a dot matrix printer?
A: Introduction: Place your printer on a flat, sturdy surface that is free of vibrations and shocks, su...
Q: Needed asap. ONLY PROGRAM/CODE IN THE LANGUAGES BELOW PROGRAM IN EITHER MATHEMATICA OR SCHEME Writ...
A: Volume of sphere = (4 / 3) * PI * radius3 Programming language used : SCHEME Value of PI used = 22 /...
Q: Thus, what is the ideal encoding scheme that is sufficiently thorough to represent all of the charac...
A: Unicode is a universal character set or a standard that specifies all of the characters required to ...
Q: Guice is a popular dependency injection library for the Java programming language. However, there ar...
A: Guice Dependency Injection resolves issues, for example, how an application or class might be autono...
Q: A terminal that is capable of doing local computations is referred to as an intelligent terminal.
A: Given that, A terminal that is capable of doing local computations is referred to as an intelligent ...
Q: How can email communication be improved? Kindly elaborate on your examples.
A: Introduction: At some point, every software becomes obsolete. Replace the software with a new, more...
Q: Vrite and execute a query that returns the maximum or highest list price roduction.Product table fro...
A: Lets see the solution.
Q: Why is it necessary to utilize APIS rather than system calls?
A: Lets see the solution.
Q: What is ARIMA modelling, and why is it so popular in data analytics?
A: let us see the answer:- Introduction:- The acronym ARIMA stands for "autoregressive integrated movin...
Q: Demonstrate how to utilize Microsoft Excel's Goal Seek function by creating a spreadsheet.
A: Seek a goal: When only the source knows the correct input value, goal searching is the way of discov...
Q: Operating Systems includes four different memory allocation mechanisms, which are mentioned and desc...
A: Introduction: Here are four well-known memory management techniques.
Q: RTP (Real-time Transport Protocol) is a protocol that allows you to send and receive data in real-ti...
A: Answer :
Q: Consider the following set F of functional dependencies on the relation schema (A, B, C, D, E, G): ...
A: Introduction Consider the following set F of functional dependencies on the relation schema (A, B,...
Q: What techniques may be used to enhance email communication? Kindly offer specific examples.
A: Introduction: The following technique was beneficial in email communication: Email communication is ...
Q: Is batch processing a feasible alternative in the modern era? If it is the case, why or why not?
A: Batch Processing: Batch processing is a typical idea utilized for frameworks with insignificant huma...
Q: Is it possible to have a computer network? What are the several components that comprise the whole n...
A: Users can use computer networks to access remote applications and databases from within their own bu...
Q: What Industries does Computer Engineering serve? Give samples and a brief description:
A: Introduction: Computer engineering is nothing more than a subject that incorporates the science and ...
Q: How do you anticipate and prepare for the many cyber security dangers that may occur when developing...
A: In order to implement few immediate measures to effect positive changes , Cyber security professio...
Q: List the features that cellphones, PDAS, and portable media players have in common with computers, a...
A: 1) Cellphones is a cell phone which is based on a working framework, having further developed regist...
Q: In a hypothetical situation, you have been tasked with the responsibility of planning and delivering...
A: Introduction: Begin your session by giving a quick review of the major aspects of the training topic...
Q: The uniprocessor and multiprocessor systems must be compared and contrasted. Computers are availab...
A: Introduction: A single computer processor is used in a uniprocessor system, while two or more are us...
Q: Why is it necessary to utilize APIs rather than system calls?
A:
Q: Write an algorithm (pseudocode, or java, or python) which takes as input the adjacency matrix of an ...
A: code: def fun(adj): no_edges = [] for i in range(len(adj)): if sum(adj[i])==0: ...
Q: Consider a project and map it both without and with the inclusion of architecture. How it will affec...
A: Introduction: Software architecture defines the relationship between strategic needs and architectur...
Q: Which theories of criminal conduct do you believe best explain cybercriminals' activities, and which...
A: Introduction: Actually, criminal conduct is the goal that is put up or the social behaviours that co...
Q: Why is it necessary to utilize APIs rather than system calls?
A:
Q: Distinguish the three layers of data modeling.
A: - They three steps of data modelling must be highlighted. - The distinctions: - Data modelling is d...
Q: Show the process to define the costs of the domain of F using Dijkstra's algorithm. 5 A В 3 |4 D E F...
A: DIJKSTRA’S ALGORITHM 1. Make a zero-distance mark on the finishing vertex. Make this vertex the curr...
Q: RTP (Real-time Transport Protocol) is a protocol that allows you to send and receive data in real-ti...
A: INTRODUCTION: RTP is a network protocol for transferring audio or video data that is tailored for th...
Q: Given the array declaration below, list the steps that an Insertion Sort function would perform in s...
A: We need to list the steps that an Insertion Sort function would perform in sorting the array. for nu...
Q: What is the purpose of networking software's where instructors and fellow students are communicating...
A: Network Software: Networking software is a primary component for any organization. It assists heads ...
Step by step
Solved in 2 steps with 1 images

- Please assist me with these questions.(for the 1st part just complete the bolded area. All other areas have been completed. Then complete the 2nd part 1. Devise an algorithm to receive a positive number, n, and output all prime numbers that are smaller than n and have the digit 5. For example, if n is 100, the program should output 5, 53 and 59. Your solution should have a main algorithm and two sub-algorithms, let's call them prime(num) and has5(num). Trace your algorithm and sub-sub-algorithm for the input 15. You should provide pre- and post-conditions for all your 3 (sub)algorithms. Now, let's trace this algorithm for the input n = 15: For i = 2 to 14, we check if i is prime and if i contains the digit 5. The prime numbers less than 15 are 2, 3, 5, 7, 11, 13. Among these, only 5 contains the digit 5. So, the output for n = 15 is [5]. 2. I also need help with creating JavaScript code for the flowchart provided below. Note: You will have to implement several functions that…A circus is designing a tower routine consisting of people standing atop one another'sshoulders. For practical and aesthetic reasons, each person must be both shorter and lighter thanthe person below him or her. Given the heights and weights of each person in the circus, write amethod to compute the largest possible number of people in such a tower.Task 2: Find the terms of any linear sequence given by the rule Term = a*n + b, where a and b are integers specified by the user and n is a positive integer and print them in order (for example if the user inputs a=3, b=-4, the first few terms that should be printed are -1, 2, 5, 8, 11…). The user also will specify how many terms the program should print. In addition, the program should print the sum of terms found and a count of how many odd terms were found. display aid of a flowchart
- Write an algorithm that computes the Body Mass Index (BMI) given the heights and weights of students. The algorithm should first read the total number of students and then read the height and weight of each student to calculate and print the BMI category A student is considered Underweight if the BMI is less than or equal to 18.5; Normal Weight if between 18.5 and 24.9; Overweight if between 25 and 29.9; and Obese if greater than or equal to 30.For the end of year administration of Programming for History of Arts students you are to write a program that can do 2 things: calculate a final grade print a small graph of similarity scores and, if applicable, list the students under investigation The input is structured as follows: Piet van Gogh___5 6 7 4 5 65=20=22=10=2=0=0=1=0=1;Vincent Appel,Johannes MondriaanKarel van Rijn___7 8 6 62=30=15=8=4=3=2=0=0=0; The first line should be interpreted as follows: You have to calculate the final grade of the student. All grades have the same weight. The final grade is rounded as follows: a grade that is >= 5.5 AND < 6 should be noted as a "6-" otherwise, a grade will be rounded to the nearest half The second line should be interpreted as follows: <10 numbers separated by '='>;<zero or more names separated by ','> The first 10 numbers are the similarity scores. These scores represent the number of programs matching a certain percentage of the current program in steps…For the end of year administration of Programming for History of Arts students you are to write a program that can do 2 things: calculate a final grade print a small graph of similarity scores and, if applicable, list the students under investigation The input is structured as follows: Piet van Gogh___5 6 7 4 5 65=20=22=10=2=0=0=1=0=1;Vincent Appel,Johannes MondriaanKarel van Rijn___7 8 6 62=30=15=8=4=3=2=0=0=0; The first line should be interpreted as follows: You have to calculate the final grade of the student. All grades have the same weight. The final grade is rounded as follows: a grade that is >= 5.5 AND < 6 should be noted as a "6-" otherwise, a grade will be rounded to the nearest half The second line should be interpreted as follows: <10 numbers separated by '='>;<zero or more names separated by ','> The first 10 numbers are the similarity scores. These scores represent the number of programs matching a certain percentage of the current program in steps…
- For the end of year administration of Programming for History of Arts students you are to write a program that can do 2 things: calculate a final grade print a small graph of similarity scores and, if applicable, list the students under investigation The input is structured as follows: Piet van Gogh___5 6 7 4 5 65=20=22=10=2=0=0=1=0=1;Vincent Appel,Johannes MondriaanKarel van Rijn___7 8 6 62=30=15=8=4=3=2=0=0=0; The first line should be interpreted as follows: You have to calculate the final grade of the student. All grades have the same weight. The final grade is rounded as follows: a grade that is >= 5.5 AND < 6 should be noted as a "6-" otherwise, a grade will be rounded to the nearest half The second line should be interpreted as follows: <10 numbers separated by '='>;<zero or more names separated by ','> The first 10 numbers are the similarity scores. These scores represent the number of programs matching a certain percentage of the current program in steps…The manager of Mama Calari’s Pizza Palace wants a program that calculates and displays the number of pizza slices into which a circular pizza can be divided. The manager will enter the radius of the entire pizza. For this exercise, use 14.13 as the area of a pizza slice, and use 3.14 as the value of pi. Desk-check your solution’s algorithm using 10 as the pizza’s radius; then desk-check it using 8. (Hint: For the first desk-check, the number of pizza slices should be a little over 22.)2. Write an algorithm (pseudocode) that inputs three positive real numbers x, y, z and outputs the smallest. How would you modify the algorithm in item # 2 above if some or all of the real numbers are allowed to be negative?
- Q1. a) The Little Man Computer (LMC) is an instructional model of a computer used to teach students all of the basic features of a modern computer in a simplified way. The following Little Man program is supposed to add two input numbers and output the result, i.e., OUT = IN1 + IN2 Mailbox Mnemonic code Numeric code 00 IN 901 01 STO 99 399 02 IN 901 03 ADD 99 199 04 OUT 902 05 COB 000 i) Change the program above to add the numbers 157 and 13. (Hint: these numbers are constants and therefore can pre-exist into memory before the execution of the program). No need to write both mnemonics and numeric codes (opcodes), either one is fine. Please refer to the instruction set provided for all the LMC instruction mnemonics and opcodes.Question #1. Product in the Range [N...M]Write a Program that reads a starting number (N) and ending number (M) and prints all the numbers product betweenthe rangesFor instanceN= 2 M= 6 X=7202*3=6 6*4=24 24*5=120 120*6 =720 Solve with C#Question 16 Rk.Write down an algorithm that checks if a system of x linear equations in y unknowns has a solution or not. Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line

