a value of 2. Problem 1.7: In virtually all systems that include DMA modules, DMA access to main memory is given higher priority than processor access to main memory. Why?
a value of 2. Problem 1.7: In virtually all systems that include DMA modules, DMA access to main memory is given higher priority than processor access to main memory. Why?
Chapter11: Operating Systems
Section: Chapter Questions
Problem 23VE
Related questions
Topic Video
Question
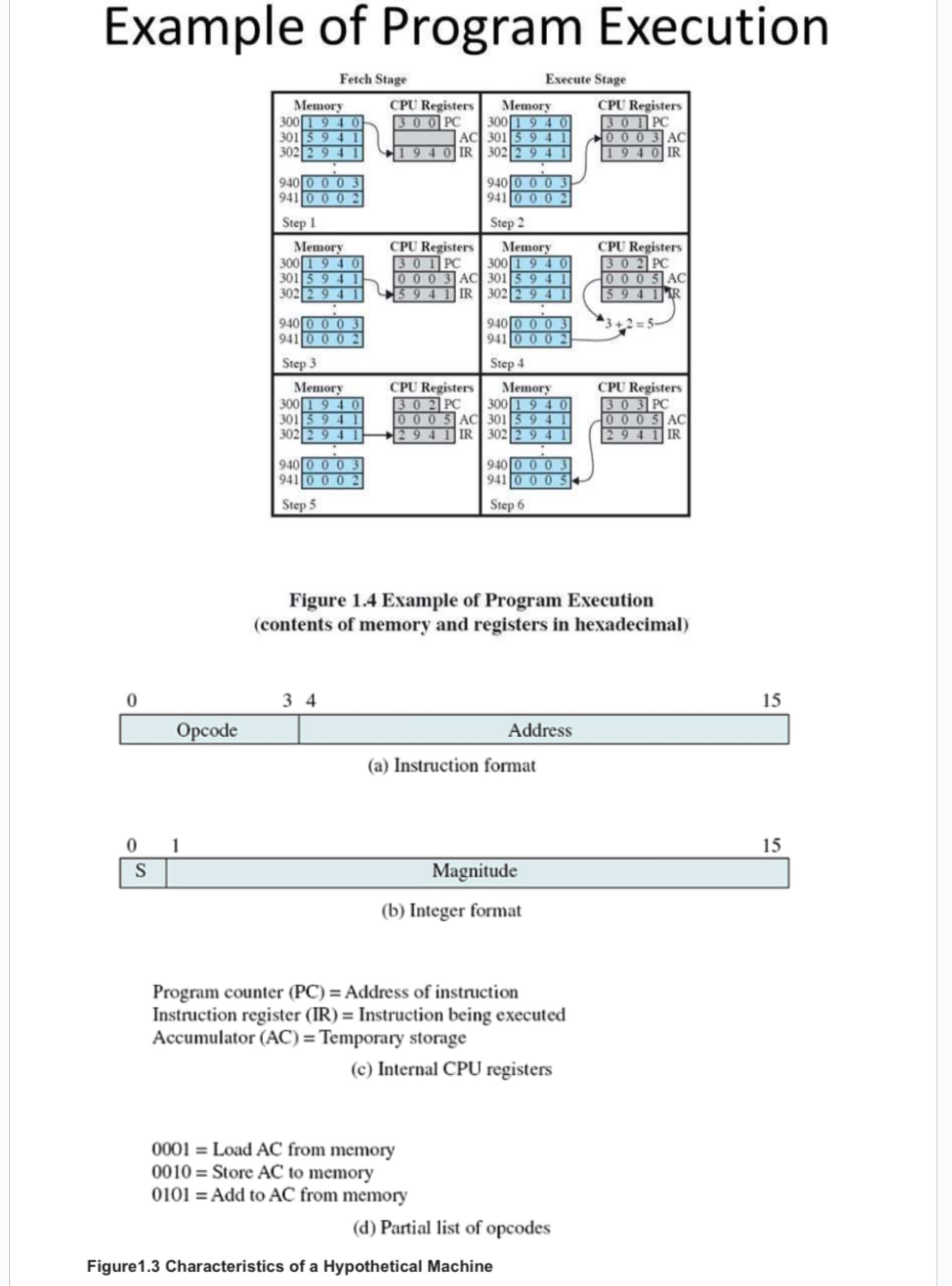
Transcribed Image Text:Example of Program Execution
Fetch Stage
Opcode
01
S
Memory
300 1940
301 59 41
302 2941
940 0 0 03
941 0 0 0 2
Step 1
Memory
300 1940
301 5 941
302 2941
940 0 0 0 3
941 0 0 0 2
Step 3
Memory
300 1940
301 5941
302 2941
940 000 3
941 0 0 0 2
Step 5
CPU Registers
300 PC
34
AC
940 IR
CPU Registers
301 PC
0003 AC
5941 IR
CPU Registers
302 PC
0005 AC
2941 IR
Memory
300 1940
301 5 9 41
302 294
940 0 0 03
941 0 0 0 2
Step 2
Memory
300 1940
301 59 41
302 2 9 4
Execute Stage
940 0 0 0 3
941 0 0 02
Step 4
0001= Load AC from memory
0010 Store AC to memory
0101 Add to AC from memory
Memory
300 1940
301 594 1
302 2 9 41
940 0 0 03
941 0 0 05
Step 6
(a) Instruction format
Figure 1.4 Example of Program Execution
(contents of memory and registers in hexadecimal)
Magnitude
(b) Integer format
Address
Program counter (PC) = Address of instruction
Instruction register (IR)= Instruction being executed
Accumulator (AC)= Temporary storage
(c) Internal CPU registers
Figure 1.3 Characteristics of a Hypothetical Machine
(d) Partial list of opcodes
CPU Registers
301 PC
0003 AC
940 IR
CPU Registers
302 PC
0005 AC
5941 R
CPU Registers
303 PC
0005 AC
2941 IR
15
15
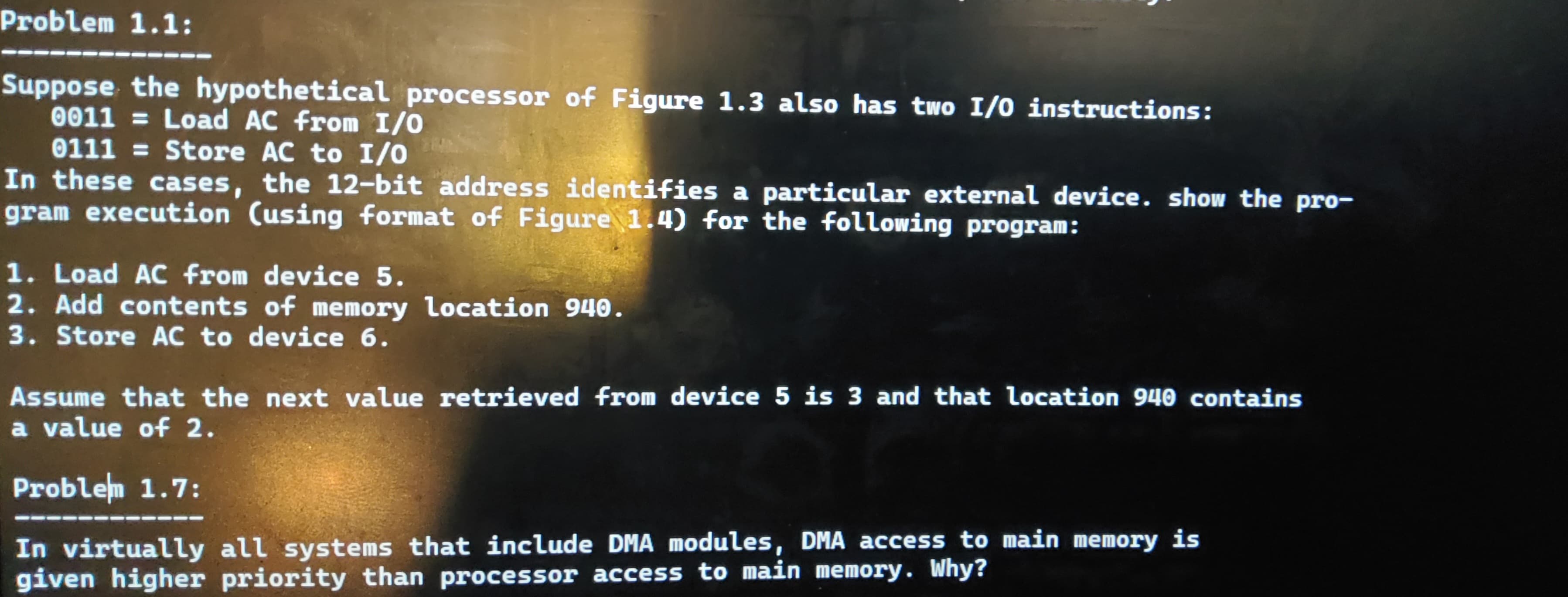
Transcribed Image Text:Problem 1.1:
Suppose the hypothetical processor of Figure 1.3 also has two I/O instructions:
0011= Load AC from I/O
0111 = Store AC to I/O
In these cases, the 12-bit address identifies a particular external device. show the pro-
gram execution (using format of Figure 1.4) for the following program:
1. Load AC from device 5.
2. Add contents of memory location 940.
3. Store AC to device 6.
Assume that the next value retrieved from device 5 is 3 and that location 940 contains
a value of 2.
Problem 1.7:
In virtually all systems that include DMA modules, DMA access to main memory is
given higher priority than processor access to main memory. Why?
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning