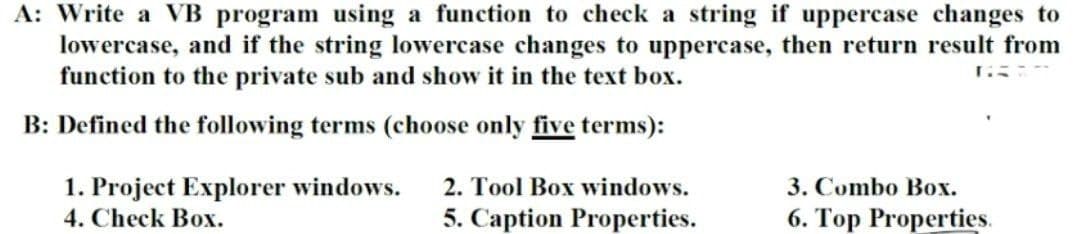
A: Write a VB program using a function to check a string if uppercase changes to lowercase, and if the string lowercase changes to uppercase, then return result from function to the private sub and show it in the text box.
Q: Why do programmers choose to write code with notepad++ as opposed to other text editors? 5 sentences
A: Introduction: Notepad++, on the other hand, is a powerful source code editor and text editor for…
Q: Are you in agreement with the statement that "there is no concept of client and server sides of a…
A: For a P2P file-sharing programme, there is no idea of client and server sides of a communication…
Q: Make a distinction between the constraints placed on the integrity and the authorization…
A: Intro
Q: A time-consuming procedure for selecting the most suited programming language
A: Inspection: A programming language is nothing more than a collection of instructions for writing…
Q: Explain why video data takes and makes use of a bigger amount of storage space than other sorts of…
A: Introduction: The request is to explain why video data requires and consumes more storage space than…
Q: What are the advantages of having proficiency in computer use? The growth of technology is…
A: Introduction Individuals with computer literacy may improve their professional performance,…
Q: When you mention "network security," what exactly do you mean? Describe the operation of the…
A: Introduction : Network security is a board term that covers a multitude of technologies, devices…
Q: What is the main difference between federated and homogenous distributed database systems?
A: Federated Distributed Database systems is a type of heterogeneous database system. These systems are…
Q: What are the advantages of using CUDA and GPU computing?
A: CUDA Compute unified device architecture(CUDA) are the application programming interface(API) and…
Q: puter systems, on the other hand, use fewer layers than the OSI model specifies. What's the point of…
A: Introduction: There are seven layers in the OSI model. TCP/IP is made up of four levels. The…
Q: Suppose that we add n unique random integers into a PriorityQueue by calling add. After that, we…
A: Below I have provided the solution of the given question:
Q: It is necessary to have the ability to build programs not just for the web but also for local…
A: Given: A programmer must be fluent in at least one programming language in order to create a website…
Q: Is it possible to have an effect on cloud security and make a difference after a data breach has…
A: With the multiplication of online action, increasingly more data is saved as information…
Q: Compilers and assemblers can be utilized to optimize assembly language instructions, which will, in…
A: Introduction: A pipeline executes many instructions concurrently. A pipeline processor consists of…
Q: Determine the four most frequent types of software licencing. Which method ensures the most…
A: Licenses for software: A software license is a legally binding document that governs the use or…
Q: How do the rows in a table in a database organize the data that is stored in them?
A: A database is an organized collection of data for easy access and control. You can organize data…
Q: Do you have any previous experience with anything that's been referred to as a "poison packet…
A: Introduction: ARP Poisoning on a Local Area Network (LAN) is a kind of cyber attack that involves…
Q: Explain various types of service categories specified in ATM networks.
A: The Atm network services are of various types. Some of them are listed as under:
Q: Which of the many programming languages are used while creating software for computers? Please offer…
A: Dear Student, C,Python,Java,Ruby,Perl,LISP are some of the programming languages used while creating…
Q: What is the difference between the protocols UDP and TCP?
A: Introduction: The Transmission Control Protocol (TCP) is a transport-layer protocol that establishes…
Q: :means dismantle O adjust O service
A: Maintenance service basically means the Routine repair and replacement of the facilities or the…
Q: What approaches do various operating systems utilise to protect the system's resources?
A: Introduction: An operating system (OS) is a piece of software that controls all computer functions;…
Q: What is dynamic scoping, when and when is it utilized, and what are the performance costs associated…
A: With dynamic scooping, a worldwide identifier alludes to the identifier related with the latest…
Q: Is it feasible to distinguish between different methods of authentication in terms of security?
A: Intro Distinguished: Being distinct implies appreciating someone. It is not unusual for exceptional…
Q: + 0101 0100 0011 1001 0100 0101 0110 1010
A: The addition of the above to binary numbers will be
Q: What are some of the views and opinions that you have towards the use of technology and computers in…
A: Encryption: Computers change our life. Regular internet usage has affected people's behaviour. New…
Q: What have been your generation's most significant communication breakthroughs?
A: ans : - their are two major significant communication breakthroughs for today's generations : - 1…
Q: Explain the significance (or lack thereof) of a TuringEquivalent machine/system or language.
A: The Answer is in step2
Q: What precisely does the word "phishing" imply, and how can its meaning be summed up in a single…
A: The word Phishing: Phishing (pronounced "fishing") is an assault that tries to steal your money or…
Q: Given the recent data breaches that have been publicized, is it possible that cloud security might…
A: Definition: Is it possible that a data breach might have a major impact on cloud security? What are…
Q: When may we make use of more than one sort of mathematical operator?
A: There are two sorts of operations that are often used:- Unary Binary Unary operations include:-…
Q: What are the advantages of software engineers abiding to the code of conduct that is specific to…
A: Answer to the given question: Advantages of software engineers abiding to the code of conduct that…
Q: Why getting an education is so important to the overall health of our society This section of…
A: Given: The computer was a 20th-century innovation.Computer and information technology have altered…
Q: If an application must be connected to the internet in order to work properly, how can its…
A: Introduction: According to some estimations, the agile app business will be worth $100 billion by…
Q: What is the purpose of the remote interface, and what are the requirements that it must fulfill in…
A: A remote interface is necessary for the implementation of RMI, which consists of: A remote interface…
Q: It would seem that notebook computers and mobile devices are quite different from one another in…
A: Introduction; The most obvious distinction between a mobile phone and a personal computer is their…
Q: Define the terms "scope creep" and "feature creep."
A: Introduction: The following is the distinction between scope creep and future creep:
Q: It is really necessary to be aware of the purpose of the verification procedure. What makes certain…
A: It is really necessary to be aware of the purpose of the verification procedure. What makes…
Q: How does an E-Book Reader work? What makes this distinct from past types of technology, like…
A: Inspection: A device that reads electronic books, such as the Amazon Kindle, is known as an…
Q: The process of designing a website may be broken down into a number of parts. Which characteristics…
A: A website design acts as the front cover of an organization based on which users first perception is…
Q: ated that a recursion function be called several times? What ty
A: Introduction: To evaluate recursive functions, most compilers and interpreters employ a data…
Q: Employ various forms of technology and information research in order to carry out investigations…
A: Introduction: The following are some of the difficulties concerning information systems: A loss of…
Q: Describe how the arithmetic operators really function.
A: Arithmetic Operator is used to performing mathematical operations such as addition, subtraction,…
Q: Explain how to use the Microsoft Smart Purchaser platform to add power paid folders.
A: Introduction : Microsoft's Intelligent Purchasing Platform: Microsoft's Power Platform is a…
Q: When you claim that the objectives of authentication are many things, what precisely do you mean by…
A: Introduction: process of authenticating a user's identity is known as authentication:
Q: Packet Switching and Circuit Switching
A: Answer: Packet switching Switching the package to transfer small pieces of data to all different…
Q: What does the acronym PAID stand for when it's being used to refer to the process of creating…
A: Given: PAID (Predictable, Atomic, Independent, and Deterministic) is the acronym for Predictable,…
Q: his category includes features of database designs such as program separation, support for numerous…
A: Task : The task is to write about the database design features that all program separation, support…
Q: Make a clear distinction between procedural programming languages and object-oriented programming…
A: The use of procedural programming: It is characterized as a structured programming language that is…
Q: When the MTTR approaches 0, how does availability change? Is this a scenario that could happen?
A: As MTTR approaches 0, the bottom of the percentage approaches MTTF, bringing the entire proportion…
Step by step
Solved in 3 steps with 1 images

- Function Name: compliments Parameters: answer1 - a boolean (True or False) representing whether the user is "smart" answer2 - a boolean (True or False) representing whether the user is "awesome" answer3 - a boolean (True or False) representing whether the user is "fun" Description: Write a function that outputs a string of compliments based on the adjectives selected by the inputs. Use the inputs True and False. The function should return the string “You are” concatenated with the compliments that are true. The three compliments should be: "smart" "awesome" and "fun". If none of the compliments are true, print the string “Goodbye.” instead. Test Cases: >>>compliments(True, True, True) You are smart awesome fun. >>>compliments(False, True, False) You are awesome. >>>compliments(False, False, False) Goodbye.A function that receives a string value, the function determines the type of the value inside the string whether it is a string, an integer or a double, and then returns the type of the value inside the string public static String inputType(String value) {// write your code here}Visual Studio 2022 - Visual Basic - Windows Forms App (.NET Framework) Put the text "I love Lucy" in a label. Add a button btnChange. Add another lable lblNumber Use string functions to do the following separately when clicking on the button. (use the label text changed event and a string function to show in the lblNumber the number of characters of the string displyed in the first label when the chnages occur) : 1. Remove "I" from the label text 2. Substitute "I" with "You" 3. Add "very much" at the end 4. Substitute "love" with "hate"
- capCount.py make a program called capCount.py that has a function that takes in a string and prints the number of capital letters in the first line, then prints the sum of their indices in the second line. The string "hEllo, World" would should look like this: 28A 3-character string, userString, is read from input. Replace the first character in userString with '=' if the first character is alphabetic. Replace the second character in userString with '$' if the second character is alphabetic. If neither condition is true, userString is not changed. Ex: If the input is gwv, then the output is: =$v #include <iostream>#include <string>#include <cctype>using namespace std; int main() { string userString; getline(cin, userString); /* Your code goes here */ cout << userString << endl; return 0;}excel vba Program a function that removes all occurrences of the selected character from the text string. Therefore, the function will have two parameters, one for entering a cell with text and the other for entering a character that needs to be omitted.
- Python question please include all steps and screenshot of code. Also please provide a docstring, and comments throughout the code, and test the given examples below. Thanks. Develop function fingerprint() that takes text (as a string) as input and creates andreturns the text “fingerprint” obtained as follows: replace each word in the text by itslength (i.e., the number of letters) and concatenate these numbers.>>> fingerprint('This is a secret message')'42167'>>> fingerprint('This message has a different fingerprint')'4731911'>>> fingerprint('Very Short')'45'9- In the following figure, there is one (combobox), one (textbox), one (button) and one (label). There are two function options in the ComboBox called "Cos" and "Sin". The numeric value entered in degrees in the text box is subjected to the function selected from the drop-down box, and the result is written in the "result" section. Type the program that performs this function. (Tip: you can use math.Cos and math.Sin functions. These functions use the type radian value as a parameter.)C program Write 2 functions that can convert an input string to all lowercase and to all uppercase. Write a program to illustrate the use of these 2 functions. Test Data: Input the string: ComputerEngineering Output: Lowercase: computerengineering Uppercase: COMPUTERENGINEERING
- Make a flowchart based from these code /* The program is all about string manipulation wherein the user will enter a string. The program will format the string to upper case -> lower case letters alternately, disregarding the spaces. For example, the user input is masbate. The output must be MaSbAtE.*/ #include <iostream>#include <string>#include <cctype>#include <fstream>using namespace std; void manipulateString(string myInput) { ofstream outFile; int mySpaces[5]; int myCount = 0; // make string in lowercase for (int i = 0; i < myInput.length(); i++) { myInput[i] = tolower(myInput[i]); } // count the number of spaces in the string and get the index of each of those spaces for (int i = 0; i < myInput.length(); i++) { if (myInput[i] == ' ') { mySpaces[myCount] = i; myCount++; } } // erase the spaces in the string for (int i = 0; i <…which functions you would use to read the following string from a users input: "This is a fun day" A. cin >> B. cin.get function c. getline function d. all of the above(Printing a Question Mark) Write a program that determines whether ? can be printed aspart of a printf format control string as a literal character rather than using the \? escape sequence.

