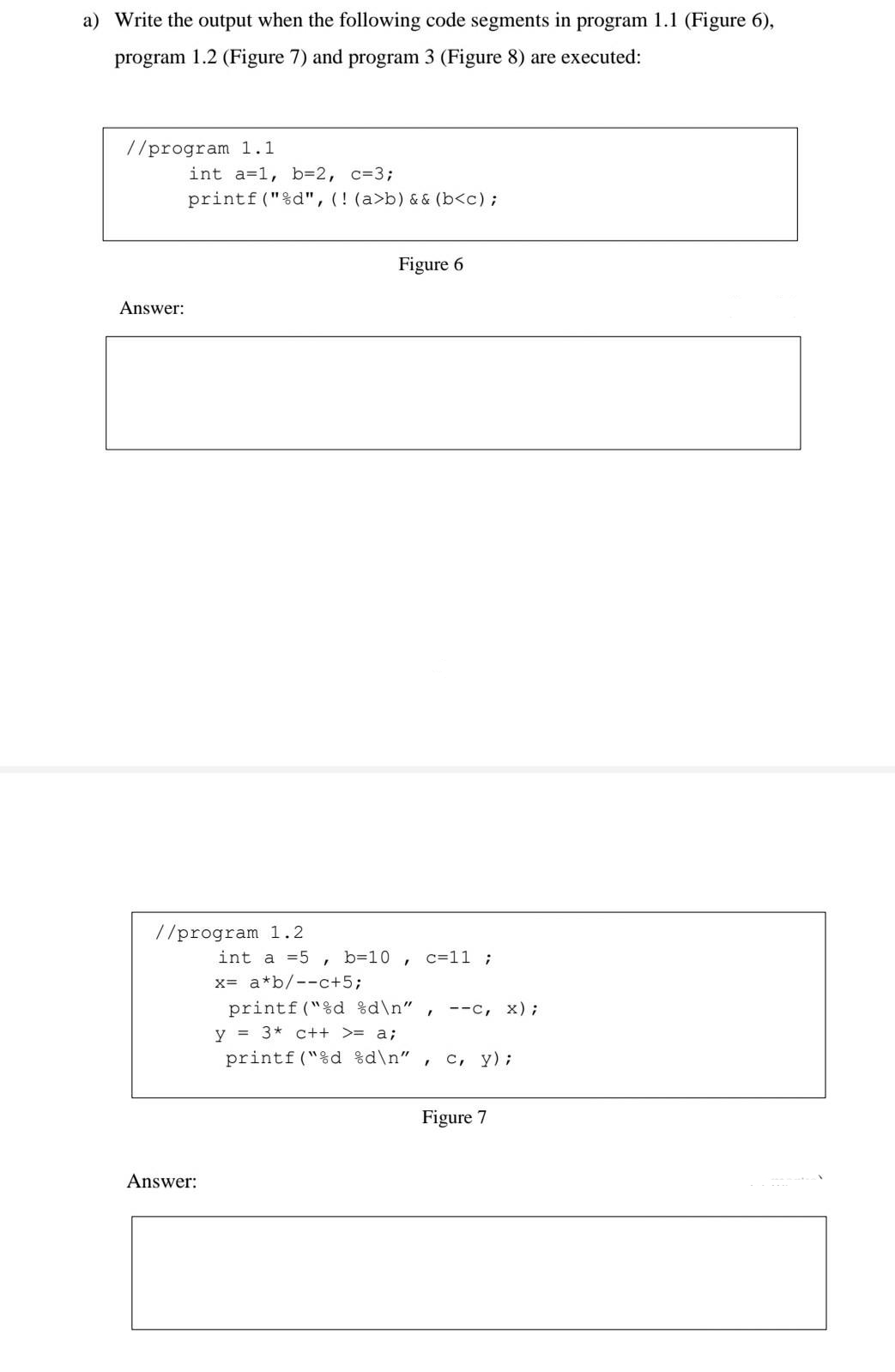
a) Write the output when the following code segments in program 1.1 (Figure 6), program 1.2 (Figure 7) and program 3 (Figure 8) are executed: //program 1.1 int a=1, b=2, c=3; printf ("%d", (! (a>b) && (b
Q: Make a note of all the significant steps you completed to identify classes while using a class-based…
A: Analysis is an attempt to build a model that describes the application domain -- developers do this…
Q: How do IP addresses work? What functions do mnemonic addresses serve? How many domains can a 32-bit…
A: DEFINITION: This page has a number of questions for you to answer. The top two queries will be the…
Q: What is transfer function?
A:
Q: WHY WE USE AMPLIFIER IN CASE OF LONG DISTANCE COMMUNICATION?
A: Transferring information from one location, person, or group to another is the act of communication.…
Q: WHY WE USE AMPLIFIER IN CASE OF LONG DISTANCE COMMUNICATION?
A: Answer: We need to write the why we use amplifier in case of long distances . so we will se in the…
Q: Can defects be eliminated by clever software design? Is there a good or bad explanation for this?
A: A bug is a mistake, defect, failure, or fault in a computer programme or software system that…
Q: Which PDPA principle forbids the transfer of your personal information without your permission?
A: Definition: The Personal Data Protection Act is referred to as PDPA. The PDPA regulates the…
Q: rotocol is a term widely used to describe diplomatic interactions. According to Wikipedia,…
A: The answer is given below.
Q: What objectives did early Internet research seek to achieve? And what were the ultimate answers to…
A: The recruiting and data collection procedure was hindered by four primary factors: The role of…
Q: Does the data deletion algorithm affect Symbian, Android, or iOS in any way?
A: This question addresses Symbian, Android, and iPhone data-erasing algorithms. The Detection…
Q: The following three components are necessary for an effective network: What is a good illustration…
A: Hi please find the solution below and I hope it would be helpful for you.
Q: When web pages are uploaded, a "MIME" header is included to help identify them from email messages.…
A: Definition: It is common practise in the Internet sector to include the MIME header to web pages…
Q: hich protocols can I use with SSL? What differentiates a secure socket layer (SSL) connection from…
A: Secure Socket Layer (SSL) provides security to the data that is transferred between web browser and…
Q: nd that during the transit phase of the TCP/IP protocol suite, packet reordering and reassembly take…
A: According to the question Keep in mind that during the transit phase of the TCP/IP protocol suite,…
Q: Why OPAMP called direct coupled high differential circuit?
A: Please refer below for your reference: OPAMP is called direct coupled high differential circuit…
Q: will using digital gadgets endanger our data security and priva
A: Introduction: Most of these gadgets are small and serve a simple purpose. Nonetheless, they are most…
Q: What feature(s) from the list below is/are NOT present in CASE tools? Establish a data repository.…
A: The answer for the above question is given in the below step for your reference.
Q: Describe the steps involved in implementing intra-AS routing. Give a routing protocol example and…
A: Intra- is short for inside and refers to everything found within.An intranet differs from the…
Q: Why is it difficult for someone to understand the semantic importance of a scenario from a…
A: Given: In your own words, describe why it is challenging for a person to understand the semantic…
Q: Why OPAMP called operational Amplifier?
A:
Q: A network must have both effectiveness and efficiency in order to function successfully. Please…
A: Network effectivness and efficiency is important factor for successful functionality
Q: Changes in business policies are usually required by changes in the workplace, which may require the…
A: Answer is in next step.
Q: oping an efficient network, a variety of important factors, including cost, time, scalability, and…
A: Let's see the answer:
Q: Professors are abundant at universities. Administrative leaders (such department heads) are not…
A: Given: The person or thing that we now have access to is Professor Course.There is no limit to the…
Q: What factors may cause a network to slow down?
A: In point of fact, a network is a means through which all devices connect with one another.
Q: public class App { public static String convertToUpperCase(String str) {…
A: To complete the given functions.
Q: Can u help create just a XOR, OR, AND circuits gate please. ( no code)
A: Logical gates AND Gate : One of the easiest multiple-input gates to understand is the AND gate,…
Q: HOW DOES A CLASS INHERIT THE CONSTRUCTORS OF ITS SUPER CLASS ?
A: We need to discuss, how a class can inherit the constructors of its superclass.
Q: Which PDPA principle forbids the transfer of your personal information without your permission?
A: Introduction: PDPA: Complete Thai data privacy legislation to date is the PDPA. It increases the…
Q: A flowchart is precisely what?
A: Explanation : What is Flow chart : A flowchart is a "formalised pictorial representation" of a…
Q: The following 5 states of Evard's machines should be explained. Off in a New, Clean Configuration…
A: Definition: The five states of Evard's machines are a representation of a machine's life cycle and…
Q: Describe why deep packet inspection cannot be used with the SSL and SSH protocols.
A: The first byte of an SSH connection varies from the first byte of an SSL connection. Basically, with…
Q: What does POPC's computer-compatible compressed version look like
A: Introduction- POP stands for Post Office Protocol in Computers in its compressed version. In a…
Q: What facets of the physical and cultural development of man have influenced his or her own learning?
A: Introduction: Reflects the grade level depending on the intricacy of the word the science concerned…
Q: What are stress tests, and why are they required?
A: Introduction: The heart, the lungs, and the blood arteries make up the three primary components that…
Q: 5.WHAT IS CONTRUSTOR OVER LOADING ?
A:
Q: What physical storage and access is there for the schedule management system?
A: Schedule Management: A process requires the foundation of strategies and documentation to keep up…
Q: what transport layer protocol is used by the point-to-point tunneling protocol?
A: There are two transport layer protocols in an OSI model , TCP and UDP , let's discuss which is used…
Q: How will using digital gadgets endanger our data security and privacy?
A: Answer is
Q: Using suitable example/s differentiat
A: The answer is
Q: Two computers must be in contact with one another in order to send and receive data through a…
A: Definition: There are two different sorts of addresses that are utilised for network communication.…
Q: If your disk is not blocked, when does Windows plan to run the Chkdsk program for file system…
A: Given: The next time the system is launched, a programme will execute in addition to various system…
Q: Consider how to handle passwords for the system you are designing, as well as the idea of strong…
A: Passwords are a good technique to secure an application: A password is a string of characters only…
Q: dont post copied content answer only know
A: A microprocessor is a computer processor that contains data processing logic and control on a single…
Q: What is 60 seconds in a decimal format?
A: 60 seconds as a decimal - Time to Decimal Calculator
Q: The application layer is the fifth layer to receive data at device B when data is sent from device A…
A: When data is delivered from device A to device B via the Internet protocol stack, the "Application…
Q: How many acknowledgements would the recipient need to receive before they could no longer receive…
A: Related to Acknowledgement of Recipient: The term "acknowledgment of receipt" refers to the process…
Q: Best First Search algorithm needs code in python for following image graph
A: create a queue Q mark v as visited and put v into Q while Q is non-empty remove the head u of…
Q: 4. What is clock synchronization? Synchronize the network given below when the server advances 10…
A: SOLUTION:- The Berkeley algorithm is a method of clock synchronization in distributed computing…
Q: nking Output of sm
A: Introduction: The process of developing and launching a successful mobile product is complicated,…
Step by step
Solved in 2 steps

- Please use C Program In order to discourage excess electric consumption, an electrical company charges its customers a lower rate of P75 for the first 250 kilowatt-hours and a higher rate of P8.5 for each additional kilowatt-hour. In addition, a 10% surtax is added to the final bill. Write a program that calculates the electrical bill given the number of kilowatt-hours consumed as input. At the end, print the number of kilowatt-hours consumed and the computed bill.-Program C 2. Not my Favorites by CodeChum Admin We've already done looping through a series of numbers and printing out its squares, so how about we level it up and go with cubes this time? I have a condition though; I don't want to be associated with numbers that are divisible by 3 or 5 so if an integer is divisible by either of the two, don't make their cube values appear on the screen, please. Care to fulfill my request? Instructions: Print out the cube values of the numbers ranging from 1 to 1000 (inclusive). However, if the number is divisible by either 3 or 5, do not include them in printing and proceed with the next numbers. Tip: When skipping through special values, make use of the keyword continue and put them inside a conditional statement. Output Multiple lines containing an integer. 1 8 64 343 512 . . .-Program C 5. Even Out by CodeChum Admin You know, I was lying when I said the last time that numbers associated with 3 are my favorite, because the one I actually like the most in the world are even numbers! But to make things harder for you, you have to pick the even numbers from a range of two given numbers. Ha! Now, let's try this one more time! Instructions: Input two integers in one line, separated by a space. The first integer shall represent the starting point, and the other, the ending point. Print out all even numbers that are within the range of the starting and ending point (inclusive or including the ending point). Input 1. The starting point 2. The ending point Output The first line will contain a message prompt to input the starting point. The second line will contain a message prompt to input the ending point. The last line contains the integers within the range. Enter·the·starting·point:·5 Enter·the·ending·point:·10 6·8·10
- Write programs for the following problem statements.a) Write a postcondition, event-controlled loop (i.e., a while loop), using a break statement,that prints the numbers 8, 14, 20, 26, 32, and 38 to the terminal (one per line). b) Write a postcondition, event-controlled loop (i.e., a while loop), using a flag variable, that prints the numbers 8, 14, 20, 26, 32, and 38 to the terminal (one per line). c) Write a counter-controlled loop (i.e., a for loop), that prints the numbers 8, 14, 20, 26, 32, and 38 to the terminal (one per line). d) Re-write a), b) and c) so that they print the numbers 38, 32, 26, 14, and 8 to the terminal (one per line). e) Re-write a), b), c), and d) so that they print the numbers to the terminal on the same line separated by spaces.8. Write a C++ code snippet to input a whole number from the user and output double the number to the screen.Please modify the C++ data structure program below to detect and display multiple candidates with the same number of votes: multiple winners, multiple candidates with the second highest number of votes, multiple candidates with the third highest number of votes, and so on. Please have output show first, second, third and fourth place winners asked in instructions below. The candidate names are attacked. Please provide screen shot of multiple candidates with the same number of votes. Suppose the candidates are A, B, C, D, E, F, G and H and their votes are: A 100 B 200 C 200 D 400 E 100 F 400 G 300 H 300 Then your program should display, A Fourth Place B Third Place C Third Place D First Place E Fourth Place F First Place G Second Place H Second Place votes.txt A = Johnson B = Miller C = Robinson D = Duffy E = Asthon F = Sampson G = Adams H = Williams My code to be modified according to instruction #include <array> #include <cassert> #include…
- -Program C 3. Loading… by CodeChum Admin I wanna experiment on looping through a range of numbers that will be randomly inputted by the user. However, I don't want to let them see the loading percentage that is divisible by 4, so please exclude those for me when printing it out. Thank you! Instructions: Input two integers in one line. The first inputted integer will be the starting point, and the second one shall serve as the ending point. Use the power of loops to loop through the starting point until the ending point (inclusive), and print out each number within the range with the corresponding format shown on the sample output. However, skip the printing of statement if the integer is divisible by 4. Tip: Utilize the continue keyword to complete the process. Input 1. The starting point 2. The ending point Output The first line will contain a message prompt to input the starting point. The second line will contain a message prompt to input the ending point. The…Write for statements that print the following sequences of values:a) 1, 2, 3, 4, 5, 6, 7b) 3, 8, 13, 18, 23c) 20, 14, 8, 2, –4, –10d) 19, 27, 35, 43, 51PROBLEM 5. Write a C++ program that would output the following series numbers. OUTPUT: 1, 2, 4, 7, 11, 16, 32, 39, 47, 56, 66
- 2. State the values of the control variable x that are printed by the following “for” statement. Then change the code to C++ syntax, and write a complete program in C++ syntax using the code block shown below, run the program, then capture the screen and submit it. for (x = 5; x <= 22; x += 7) { printf("%u\n", x); }QUESTION: If the second input is higher than the first input but lower than the third input, what will be the output results? Write on the space provided the input values and the results. A young boy wants to create a program in block of code that will compute for the quadratic equation then print the result. The main function composes of the input variables.The formula is given below: -B ± √ B ^2 – 4AC--------------------------------- 2AIf the user inputs zero (0), the program will display “Invalid Entry” and return to main menu to input another valid numbers.2.1.1: Reading multiple data types Type two statements. The first reads user input into person_name. The second reads user input into person_age. Use the int() function to convert person_age into an integer. Below is a sample output for the given program if the user's input is: Amy 4In 5 years Amy will be 9Note: Do not write a prompt for the input values.



