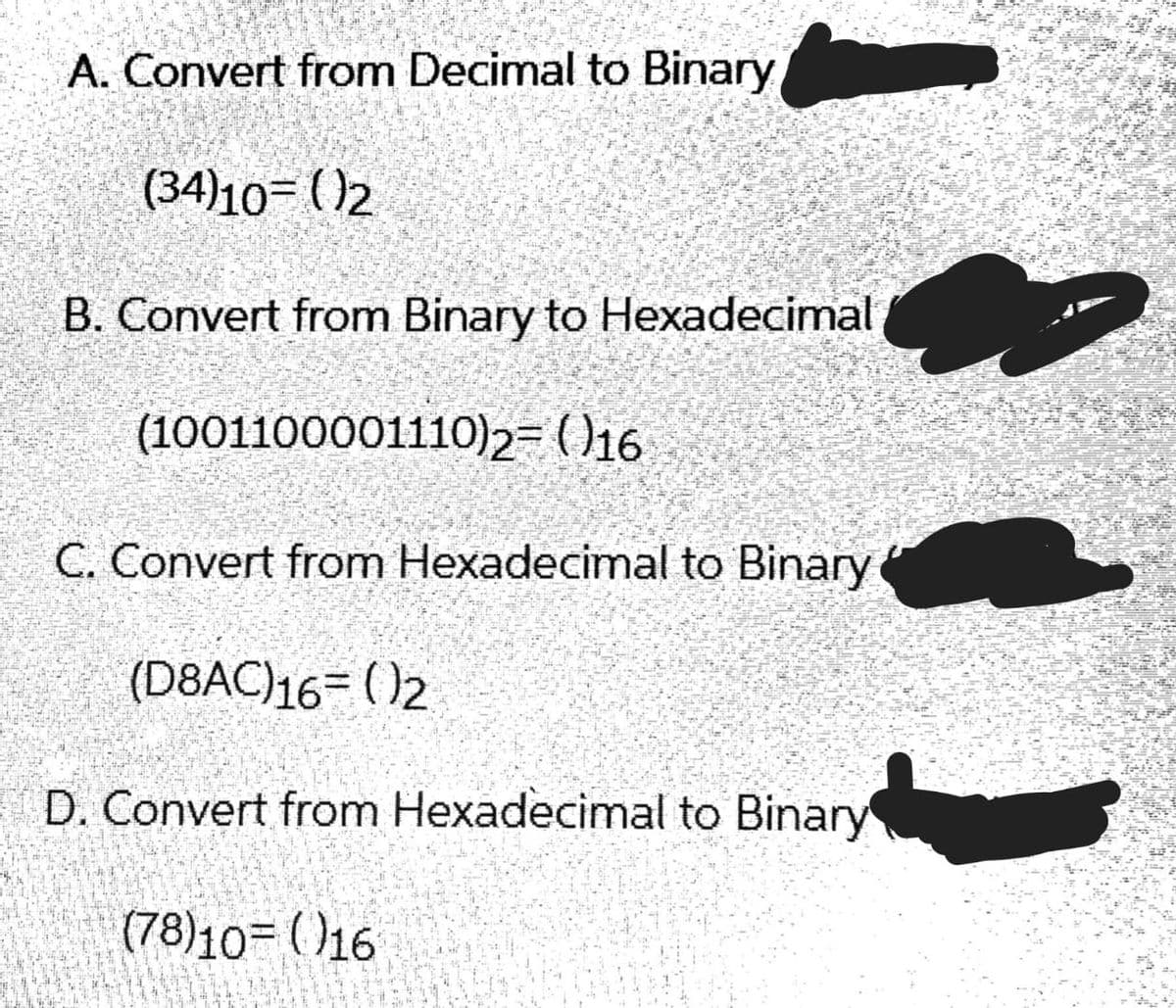
A. Convert from Decimal to Binary (34)10= ()2 B. Convert from Binary to Hexadecimal (1001100001110)2= )16 C. Convert from Hexadecimal to Binary (D8AC)16= ( )2 D. Convert from Hexadecimal to Binary (78)10= ()16
Q: In the computer realm, what is a system changeover
A: In the computer world, system changeover refers to switching from one operating system to another.…
Q: Differentiate the advantages and disadvantages of virtualization and network storage options.
A: Advantages and disadvantages of virtualization and network storage options: Virtualization is a…
Q: Computer science What was the first functional language?
A: Introduction: Functional languages are essentially languages in which procedures are carried out…
Q: In order to avoid data loss or a computer malfunction, what are the most important reasons for doing…
A: we are doing backups mostly for the following result.
Q: What is the role of technology in education?
A: Presentation: Technology has a huge influence in schooling. As technology advances, pupils' learning…
Q: What was Ada Lovelace's contribution to computing?
A: Lady Ada Lovelace was an early twentieth-century computer programmer. Ada Lovelace, an English…
Q: What is computer science
A: Computer: Computer is an electronic device which can take data as input process is according to…
Q: What's the difference between DLL and EXE in.NET?
A: DLL and EXE in.NET: DLL stands for dynamic link library, which includes code and data that may be…
Q: Project management ethics is important.
A: Start: According to the Project Management Institute, "honesty, responsibility, respect, and…
Q: Discuss how to distinguish between the network core and the network edge in terms of network design…
A: Introduction: The difference between a network core and a network edge:
Q: a) Why is a test program's specified behaviour different from its implemented behaviour? b) What…
A: Introduction: Boundary Value Analysis (BVA) is a Black-Box testing approach for detecting faults at…
Q: te a simple python program that ash r for his Marks in Five courses, then user the result if he…
A: Lets see the solution.
Q: What is Machine Language, in a nutshell? Also, please explain why electronic devices do not…
A: The language that only consists of 0's or 1's is called a machine language and also called as…
Q: e description language (HDL) is
A: Design: Description: Descriptive language counts motive, aesthetic price, and emotion to…
Q: What exactly is a pattern? Why is SCRUM referred to as a pattern?
A: Software development: Software development undergoes various phases and the lifecycle. The life…
Q: What are the core ideas of software engineering that are ignored? explain?
A: Introduction: Fundamental concepts of software Software is a set of computer instructions that are…
Q: What happens to a wireless signal when it comes into contact with a large object?
A: Introduction: According to the question, different barriers, such as physical objects and multiple…
Q: 3. Write the First Order Logic of the following: (Hint: you may need to use these symbols: Vx, 3x,…
A: As per answering guidelines solving the first three subquestion A) Let the predicate be L(x, y) :…
Q: How the Adhoc Network nodes are aware of the changing network topology.
A: Intro How do the nodes in the Adhoc Network know about the changing network topology.
Q: f all electronic doc
A: Introduction Encryption is a method of encrypting data so that it can only be deciphered by…
Q: Identify one desirable user experience connected to an online meal ordering company that allows…
A: Introduction: Interaction with the system is absolutely important and required in order to complete…
Q: What information must be included in an instruction set? Give an overview of the SRC.
A: Answer:- Information must be included in an instruction set: The instruction set is basically the…
Q: What Is an Object Server, Exactly?
A: Intro the question is about What Exactly Is An Object Server and here is the solution in the next…
Q: Suppose you are contacted by a software developer to create a hospital patient management system.…
A: GIVEN:
Q: Give two real-world examples of how to use menus in an application and why you'd prefer to use a…
A: Answer Instance 1:- For stock market if we have a application then menus are the most important…
Q: Why do we talk about data structures and algorithms at the same time? What is the relationship…
A: The Answer is in step2
Q: Instructions A local biologist needs a program to predict population growth. The inputs would be: 1.…
A: We need to write a Python code to model the biological behaviour as mentioned.
Q: rtualization simplifies the use of resou olates users from one another, suppor plication and…
A: Lets see the solution.
Q: Examine this list of questions: When it comes to data backup and recovery, what are the most…
A: In the event of data loss or destruction, backup and recovery are duplicating that data and storing…
Q: What information must be included in an instruction set? Give an overview of the SRC.
A: In the instruction set, there is a specification that says: The instruction set is the section of…
Q: According to us, Flynn's taxonomy should be expanded by one level. What is it about today's…
A: Start: Michael J. Flynn proposed the Flynn taxonomy, which is a classification of computer…
Q: What's the Distinction Between Triggers and Rules?
A: Introduction: What Is the Difference Between Triggers and Rules is the query, and the answer is in…
Q: What are some of the advantages of an electronic govern
A: Lets see the solution.
Q: What exactly do you mean when you say "local variable"? Local variables are used in a few…
A: Ans:) Please find the answer below.
Q: Consider utilizing the Go-Back-N and selective-repeat methods if the sequence number space is k-bit…
A: Analyze the issue: Given Information: k bits is the number of bits used for sequence numbers.…
Q: What exactly is a Binary Search Tree and how does it function?
A: Introduction: Binary Search Tree is a twisted binary tree in which the node scanned to the left or…
Q: When it comes to data backup and recovery, what are some of the most crucial factors to keep in…
A: The most important thing is the speed and accuracy: To maintain track essential data and restore it,…
Q: Computer science What are the concepts and causes of overflow and underflow?
A: Introduction: Simply explained, overflow and underflow occur when we assign a value that is outside…
Q: When users travel between VLANs, which VLANs need the least amount of administrative effort?
A: Introduction: VLANs that are dynamic:
Q: Calculate the Bresenham's circle drawing algorithm's decision parameter p. Bresenham's circle…
A: Bresenham's Circle Drawing Method is a circle drawing algorithm that finds the closest pixel…
Q: What difference does it make whether computers are ordered or designed architecturally?
A: Introduction: Computer systems are divided into two distinct types. The first is the desktop…
Q: Subject - Data Communication Networks Q4) 4. In TCP, ECE and CWR flags are used for congestion…
A: let us see the answer:- Introduction:- TCP (Transmission Control Protocol) is a network protocol…
Q: What are the differences between decision structures and sequence structures?
A: Introduction: A decision structure is designed to allow for conditional execution. It is intended to…
Q: The way a user interacts with mobile and desktop operating systems?
A: Introduction: Prism is a software application used by the United States National Security Agency…
Q: Explain how a processor executes a programme.
A: Introduction: The required answer is presented in the following step.
Q: Is Windows 7 compatible with version of Ubuntu Linux is the r
A: Ubuntu is a Linux distribution in view of Debian and made for the most part out of free and…
Q: What are the most critical factors to keep in mind while doing data backups and recoveries?
A: Introduction: The following are the most important considerations to bear in mind when doing data…
Q: When is a typedef statement necessary? a. It's never necessary, it's just a good tool to use O b.…
A: Typedef: The typedef feature of the programming language allows us to establish an alias or new name…
Q: What parts of computer system documentation, file security, and retention control methods are…
A: Documentation control procedures - aspects : It will set framework for how the documents are…
Q: Computer science the distinctions among concurrent, parallel,and distributed.
A: Introduction: Parallel computing allows for more concurrency while also saving time and money.…
Step by step
Solved in 4 steps with 4 images

- A(n) __________ is an integer stored in double the normal number of bit positions.Calculate (4.41762275 *10-3 + 6.34225625 *10-3) * 1.05225 * 102 by hand, assuming each of the values are stored in the 16-bit half precision format described in in the textbook. Assume 1 guard, 1 round bit, and 1 sticky bit, and round to the nearest even. Show all the steps, and write your answer in both the 16-bit floating point format and in decimal.8) Obtain the 1’s and 2’s complements of the following binary numbers correctly:(a) 10010000(b) 00000000(c) 11011010(d) 10101010(e) 10100101(f) 11111111 9) Convert decimal +49 and +29 to binary, using the signed-2’s-complementrepresentation and enough digits to accommodate the numbers. Thenperform the binary equivalent of (+29) + (-49), (-29) + (+49), and (-29) + (-49). Convert the answers back to decimal and verify that they are correct.
- a) Use the two’s complement binary representation to represent each of the following integers as 10-bit binary numbers. i) -13710 ii) 14510 iii) -15810 iv) 16710 v) -11510 b) If an 8-bit binary number is used to represent an analog value in the range from 0 to 100kg, what does the binary value 011001002 represent?Calculate (3.41796875 *10-3 * 6.34765625 *10-3) by hand, assuming each of the values arestored in the 16-bit half precision format described in in the textbook. Assume 1 guard, 1 roundbit, and 1 sticky bit, and round to the nearest even. Show all the steps, and write your answer inthe 16-bit floating point format.Calculate (3.41700875 *10-3 + 6.34005625*10-3)* 1.25625* 102 by hand, assuming each of the values are stored in the 16-bit half precision format describedin in the textbook. Assume 1 guard, 1 round bit, and 1 sticky bit, and round to thenearest even. Show all the steps, and write your answer in both the 16-bit floating point format and in decimal.
- Perform the following operation for the binary equivalent of the decimal numbers (-14) 10+ (-15) 10 The solution in 8 bit representation ?Represent the following numbers to its 6-bit binary representation and perform binary subtractionusing 2’s compliment representation 50-30?A. How many bits are needed to represent 214(octal) in binary?B. Show the 2’s complement binary (10 bits) representation of (-246)(10)C. Convert the following 2’s complement binary number to decimalrepresentation:10010010
- Using a “word” of 4 bits, list all the possible signed binarynumbers and their decimal equivalents that are representable in:1. a) Signed magnitude2. b) One’s complement3. c) Two’s complement9) Convert decimal +49 and +29 to binary, using the signed-2’s-complementrepresentation and enough digits to accommodate the numbers. Thenperform the binary equivalent of (+29) + (-49), (-29) + (+49), and (-29) + (-49). Convert the answers back to decimal and verify that they are correct.Find the binary representation for each of the following decimal represented numbers: 4, 8, 16, 32

