(ADD D,S) INSTRUCTION IS THE SAME AS THE FOLLOWING INSTRUCTIONS COMPILATION Select one: a. mov al.1 add al.1 ADC D.S
(ADD D,S) INSTRUCTION IS THE SAME AS THE FOLLOWING INSTRUCTIONS COMPILATION Select one: a. mov al.1 add al.1 ADC D.S
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter10: Pointers
Section10.1: Addresses And Pointers
Problem 11E
Related questions
Question
Please solve quickly
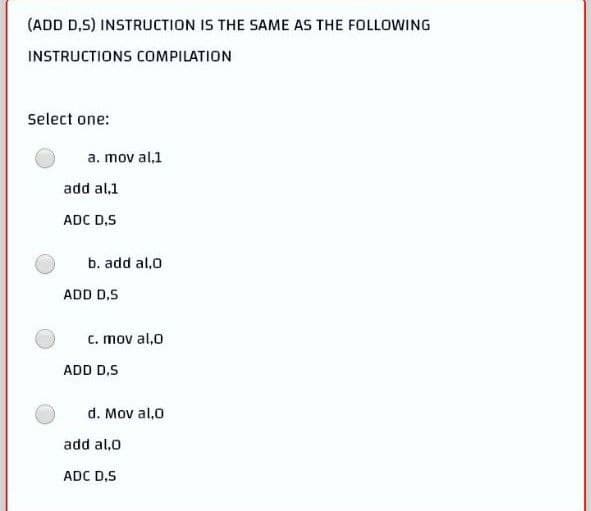
Transcribed Image Text:(ADD D,S) INSTRUCTION IS THE SAME AS THE FOLLOWING
INSTRUCTIONS COMPILATION
Select one:
a. mov al,1
add al.1
ADC D,S
b. add al,0
c. mov al,0
d. Mov al,0
ADD D.S
ADD D.S
add al,0
ADC D,S
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr