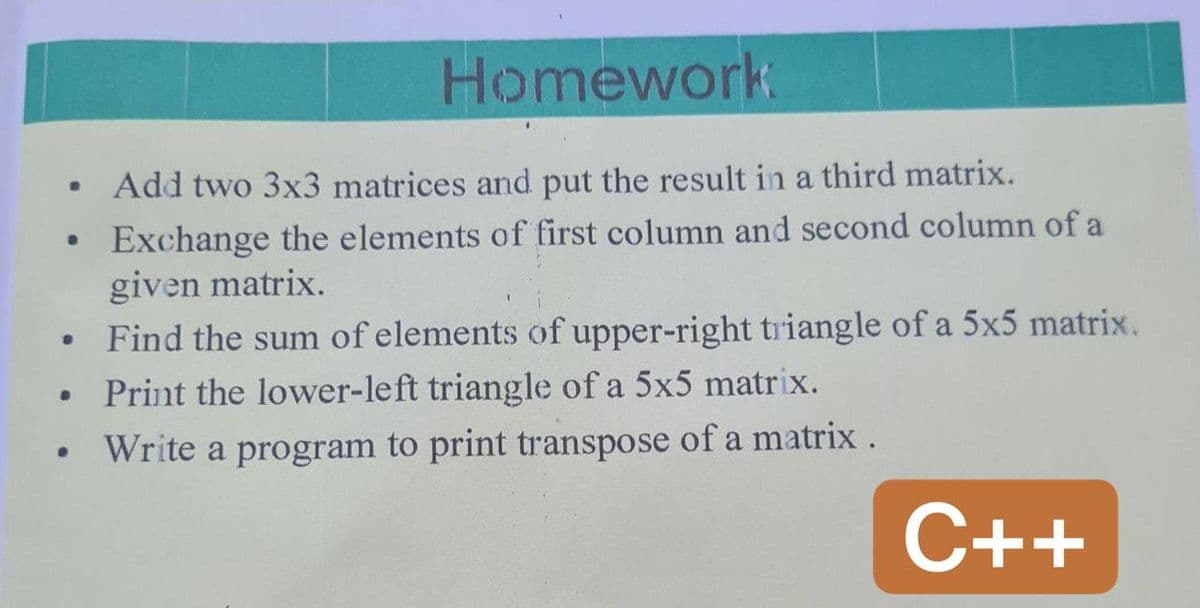
· Add two 3x3 matrices and put the result in a third matrix.
Q: C# application that will capture names and marks of ten students and display on the screen
A: The program is written in C#. Check the program screenshot for the correct indentation. Please check…
Q: Write a Technical Report on how Active Directory and Domain Name Systems can be used to manage Users…
A: Active Directory (AD) is a Microsoft-related directory service. Works on Windows Server and enables…
Q: What wireless networking standards, topologies and trends are out there to discover?
A: Internetworking through wireless: Wireless local area networks are often inexpensive to construct…
Q: The internet is seen as an excellent example of ICT in what ways? It's easy to explain and…
A: Please find the answer below
Q: Build a C program to enter 5 numbers. Determine and display for the following: a) the sum of all 5…
A: #include <stdio.h> int main(){ int ctr=1,sum=0,sneg=0,x,pctr=0; do{…
Q: Consider the following snapshot of a system: Allocation Max…
A: Answer in step 2
Q: A list of any three programming languages that are often utilised in the development of web-based…
A: JavaScriptJavaScript and Python are consistently in a close contest. Throughout the course of recent…
Q: 5) Design a 3-Bit (fixed reference) comparetor to compare a level of 100. Using; a. MUX b. Logic…
A: Design a 3-Bit (fixed reference) comparetor to compare a level of 100. Using
Q: For application-level proxies, end-to-end encryption might be a concern. Make a suggestion on how an…
A: End-to-end encryption: End-to-end encryption might affect application-level proxies. Proxy-based…
Q: Based on the services they deliver, operating systems may be categorize
A: There are five categories of operating system: 1) Interactive OS are the ones in which we can…
Q: 2. The goals scored in a soccer match may be input as a sequence of "1"s and "2"s, terminated by 0.…
A: Given that The goals scored in a soccer match may be input as a sequence of "1"s and "2"s,…
Q: at of the following is true abo
A: Introduction: An operating system is the software that controls the hardware and resources of a…
Q: Talk about the benefits of creating an application that has numerous processes.
A: The need to separate the application into various processes has become evident as websites and web…
Q: A network intrusion might occur if malicious traffic is rerouted from one VLAN to another. The…
A: Given: A VLAN is a logical grouping of devices on one or more LANS that are configured to…
Q: Windows Service Control Manager will be described in detail
A: Answer:
Q: However, there is still a problem with defining exactly what we mean when we talk about 4G or 5G…
A: Networks using either 4G or 5G: In a nutshell, the transition from the 4G network to the 5G network…
Q: Build PDA to generate all strings of the form 0n 1 3n+2, where n is greater or equal to 0.
A: We are going to draw a PDA for the language: 0n13n+2 , n>=0. I have uploaded image for the…
Q: Write a c++ program function to check if a given input number is a jumping number. A number is…
A: Code: #include <iostream> using namespace std; int jumpingNum(int n){ int check=1; int…
Q: What is routing, exactly, and how does it work in practice? In this paper, we'll look at and compare…
A: SOLUTION: Routing is the process of selecting a path for traffic inside a network, or between or…
Q: The relative benefits of synchronous data replication and partitioning should be discussed.
A: The synchronous data replication is denoted as the process which stores the duplicate of the similar…
Q: What is SIEM solution, cyber threat intelligence, open-source? -Why do companies need this kind of…
A: Answer:
Q: 3. MOV AX, 11A1H; MOV [1233H], AX; How does the data store in memory location? ODS: 1233 = 11 H, DS:…
A: MOV instruction is used to transfer the content from one location to another. The two instructions…
Q: An organization's Windows Server 2012 installation and configuration procedure might be the subject…
A: Start: Windows Server 2012's IP address management role may discover, monitor, audit, and manage a…
Q: What steps must you take to become a ggod programmer?
A: Introduction: A set of instructions to perform a specific task is defined as programming.…
Q: As a direct result of the qualities that are inherently associated with them, wireless networks face…
A: Wireless Networks Wireless networks are the communication networks that connects various devices and…
Q: What are the purposes of design patterns in software development, and how might they be most…
A: Design Patterns: Design patterns are a set of guidelines used by experienced object-oriented…
Q: Define "TOR network" and explain what it is.
A: We are required to define and explain " TOR network".
Q: Make a comparison of the cellular, wireless, and wired options for data transmission. Distinguish…
A: Data links through cellular phones, wired data connections, and wireless data connections Data is…
Q: In HCD, there are many design concepts. For each of the following scenario, give the appropriate…
A: The Answer is in step-2.
Q: In poor nations, what function do wireless networks play? LANs and physical cabling are becoming…
A: Introduction: Multiple electronic devices, such as PC, laptops, and other mobile devices, are…
Q: Explain why the interactive model is superior than the waterfall model in terms of the amount of…
A: Answer: The following are the differences between the waterfall model and the interactive model:…
Q: What's the link between software development and putting the user first?
A: Software Development and UCD: The Software Development Life Cycle is a method followed by a software…
Q: Talk about the many purposes for which data mining may be used.
A: Data mining is a process used by companies to turn raw data into useful information.
Q: What exactly is the TOR NETWORK?
A: Answer in step 2
Q: Do you plan to include programming principles into your program?
A: Programming is a difficult yet alluring field that draws engineering students and professionals with…
Q: Talk about the benefits of creating an application that has numerous processes.
A: Given: As websites and online apps get increasingly sophisticated, the necessity to separate them…
Q: tem to be more cautious when acce
A: Introduction: The supervisor programme, which runs the operating system, spends the majority of its…
Q: Let's have a look at the compiler and talk about the testability tip, shall we?Let's have a look at…
A: Answer to the given question Testability test is a specialized means to decide if the framework or…
Q: No programing language needed! Question: John and Diane want to have $376,000.00$376,000.00…
A:
Q: What makes utilizing a virtual private network (VPN) more secure than using the public internet…
A: A virtual private network, or VPN, is an encrypted connection over the Internet from a device to a…
Q: Both preemptive and nonpreemptive scheduling are two distinct approaches to scheduling.
A: Given: When the CPU is allocated to a nonredemptive process, the process maintains the CPU until it…
Q: It's a good idea to sum up the kernel components of an operating system in a single statement.
A: Introduction: The kernel is a computer: The kernel is a piece of computer software that runs at the…
Q: please codee in python Write a script that prompts the user for two words (two, one-word strings).…
A: I give the code in Python along with output and code screenshots.
Q: Write a program to ask the user to input an integer, and then display the according pattern.…
A: In your questions some part are not specified I have just mention the program how to enter name…
Q: According to the Data Mining Systems, what are the steps we must do before we apply the data mining…
A: The Process of discovering interesting patterns and knowledge from large amount of data is known as…
Q: there an advantage to utilizing the Vector Space Model (VSM) instead of the Latent Semantic Analysis…
A: Please find the answer below :
Q: A major focus of this talk will be on the critical role that software architecture plays throughout…
A: Given: Program architecture outlines the concept and operation of the software. It enables you to…
Q: Question 5 What is an example of an unmanaged best effort public network? Ⓒintranet Ⓒindere Select…
A: An unmanaged network is a special kind of network in which all things under the network are managed…
Q: There have been numerous technological advances in the previous several decades, and what are the…
A: The degree to which technology has prompted innovation: In its present form, the globe has become an…
Q: What happens if numerous separate processes all have the same priority levels when it comes to…
A: Given: The scheduler will enable each process to run in its own time so long as it detects that the…
Step by step
Solved in 2 steps with 2 images

- code for this in C: Write a program that reads two matrices of integers. It then generates the sum and difference of the two matrices. The sum of the two matrices of the same size is a matrix with elements that are the sums of the corresponding elements of the two given matrices. Addition is not defined for matrices of different sizes. If A and B are matrices of the same size, then we define subtraction as follows: A – B = A + (-B). Thus, to subtract matrix B from matrix A, we simply subtract corresponding elements.write a c++ code to read the elements of a martix, the number of rows = 4 and the number of column = 3, read the emenets by the user, find the sum of all elements in the matrix and then print the sum, find the maximum number in row = 3 and then print it?23. Can we compare two vectors in C++ using the == operator? If yes, then write a program taking two sample vectors.
- I just want to Find the minimum path sum in matrix. The minimum path is sum of all elements from first row to last row where you are allowed to move only down or diagonally to left or right. You can start from any element in first row.Program should be in C language. First we ask the user for the number of rows and columns of the matrix, and then we generate a matrix of random numbers between 0 and 9 according to this number of rows and columns, and we find the smallest total path in this matrix. The rules are stated above. Example outputs : Enter number of rows (0 to exit): 3Enter number of columns: 5 9 7 8 [3] 88 6 [1] 2 34 7 5 [0] 8 Minimum sum:4 Enter number of rows (0 to exit): 5Enter number of columns: 7 6 4 8 9 1 [0] 33 0 5 9 [3] 4 23 0 8 1 [1] 3 34 2 0 7 [0] 9 37 5 9 9 3 [0] 3 Minimum sum: 4 Enter number of rows (0 to exit): 5Enter number of columns: 10 5 1 6 4 9 8 [0] 3 0 18 4 7 2 8 4 [2] 5 3 76 7 7 2 9 6 6 [0] 8 43 2 2 6 1 9 4 [2] 6 72 8 0 7 6 6 6 [1] 2 9 Minimum…Q5. Write a program that reads from the user an integer matrix with 10x10, and then rotate that matrix 180° (UPSIDE DOWN) after that, calculate the sum and the average of the main diagonal. Print the matrix after the rotation and the values of the sum and the average of the main diagonal.Write a menu-driven program to read and display a p¥q¥r matrix. Also, find the sum, transpose, and product of the two p*q*r matrices
- Use C Language Write a program that reads two matrices of integers. It then generates the sum and difference of the two matrices. The sum of the two matrices of the same size is a matrix with elements that are the sums of the corresponding elements of the two given matrices. Addition is not defined for matrices of different sizes. If A and B are matrices of the same size, then we define subtraction as follows: A – B = A + (-B). Thus, to subtract matrix B from matrix A, we simply subtract corresponding elements.Write a code that would be able to perform matrix operations of variable size depending on user to input operations should include matrix addition,multiplication,and transpose. If the user wishesh to perform a transpose operation the program should accept a single matrix only. In python.Write a program in C++ which takes two 4 x 4 matrices as input from the user and displaysthe matrices in tabular form. Then ask user to make a choice:1. Press 1 for matrix addition2. Press 2 for matrix subtraction3. Press 3 for matrix multiplication4. Press 4 for matrix transposeUse 2D arrays to save matrix values and use functions to perform addition, subtraction,multiplication and transpose. Refer below examples to understand the concept of matrixoperations.
- Write a program in C++ which takes two 4 x 4 matrices as input from the user and displays the matrices in tabular form. Then ask user to make a choice: 1. Press 1 for matrix addition 2. Press 2 for matrix subtraction 3. Press 3 for matrix multiplication 4. Press 4 for matrix transpose Use 2D arrays to save matrix values and use functions to perform addition, subtraction, multiplication and transpose.Write a C++ program that read 12 integer values from user, store values in Matrix of 4 X 3. Create another Matrix of 4 X 3, divide each element of Matrix1 by five, and store the result in the Matrix2. Print Matrix A, with heading shown, correctly spaced.Print Matrix B, with heading shown, correctly spaced.Your Program should display output as follows:Let A be a ’matrix’ in Python containing randomly assigned values, belongs to custom created matrix class, an instance of customly designed class named ’matrix’. Write a Python3 program to rotate A clockwise (the 1st column becomes the 1st row) n times and prints it to the screen. If n = 4 then the result is the initial matrix A, if a negative number given for n then rotate the matrix counterclockwise.

