administrator account password which is not on a domain. Which of the following is the BEST way for the tester to complete this task with physical access to the PC? A. Boot into a Linux OS via CD-ROM and reset the SAM database administrator password. B. Boot into a Linux OS via USB and delete the SAM database so the system recreates a new one.
administrator account password which is not on a domain. Which of the following is the BEST way for the tester to complete this task with physical access to the PC? A. Boot into a Linux OS via CD-ROM and reset the SAM database administrator password. B. Boot into a Linux OS via USB and delete the SAM database so the system recreates a new one.
Chapter11: Compression, System Backup, And Software Installation
Section: Chapter Questions
Problem 3DE
Related questions
Question
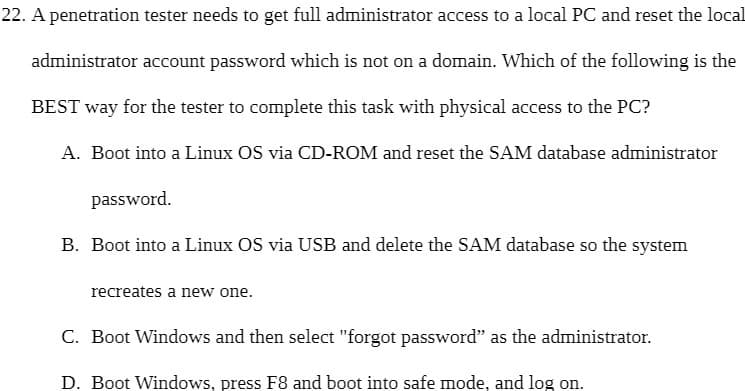
Transcribed Image Text:22. A penetration tester needs to get full administrator access to a local PC and reset the local
administrator account password which is not on a domain. Which of the following is the
BEST way for the tester to complete this task with physical access to the PC?
A. Boot into a Linux OS via CD-ROM and reset the SAM database administrator
password.
B. Boot into a Linux OS via USB and delete the SAM database so the system
recreates a new one.
C. Boot Windows and then select "forgot password" as the administrator.
D. Boot Windows, press F8 and boot into safe mode, and log on.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L