(a)Find an appropriate algorithm for the given problem. (b)Draw the graph. (c)Find the maximum speed. (You need to show the necessary steps of the simulations)
(a)Find an appropriate algorithm for the given problem. (b)Draw the graph. (c)Find the maximum speed. (You need to show the necessary steps of the simulations)
Fundamentals of Information Systems
8th Edition
ISBN:9781305082168
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter3: Database Systems And Applications
Section: Chapter Questions
Problem 2.1DQ
Related questions
Question
(a)Find an appropriate
(b)Draw the graph.
(c)Find the maximum speed. (You need to show the necessary steps of the simulations)
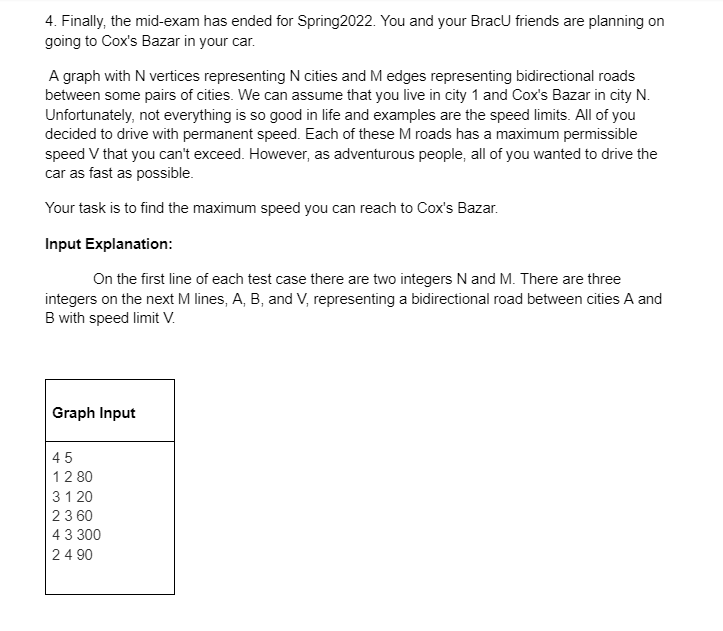
Transcribed Image Text:4. Finally, the mid-exam has ended for Spring2022. You and your BracU friends are planning on
going to Cox's Bazar in your car.
A graph with N vertices representing N cities and M edges representing bidirectional roads
between some pairs of cities. We can assume that you live in city 1 and Cox's Bazar in city N.
Unfortunately, not everything is so good in life and examples are the speed limits. All of you
decided to drive with permanent speed. Each of these M roads has a maximum permissible
speed V that you can't exceed. However, as adventurous people, all of you wanted to drive the
car as fast as possible.
Your task is to find the maximum speed you can reach to Cox's Bazar.
Input Explanation:
On the first line of each test case there are two integers N and M. There are three
integers on the next M lines, A, B, and V, representing a bidirectional road between cities A and
B with speed limit V.
Graph Input
45
12 80
31 20
23 60
43 300
24 90
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning