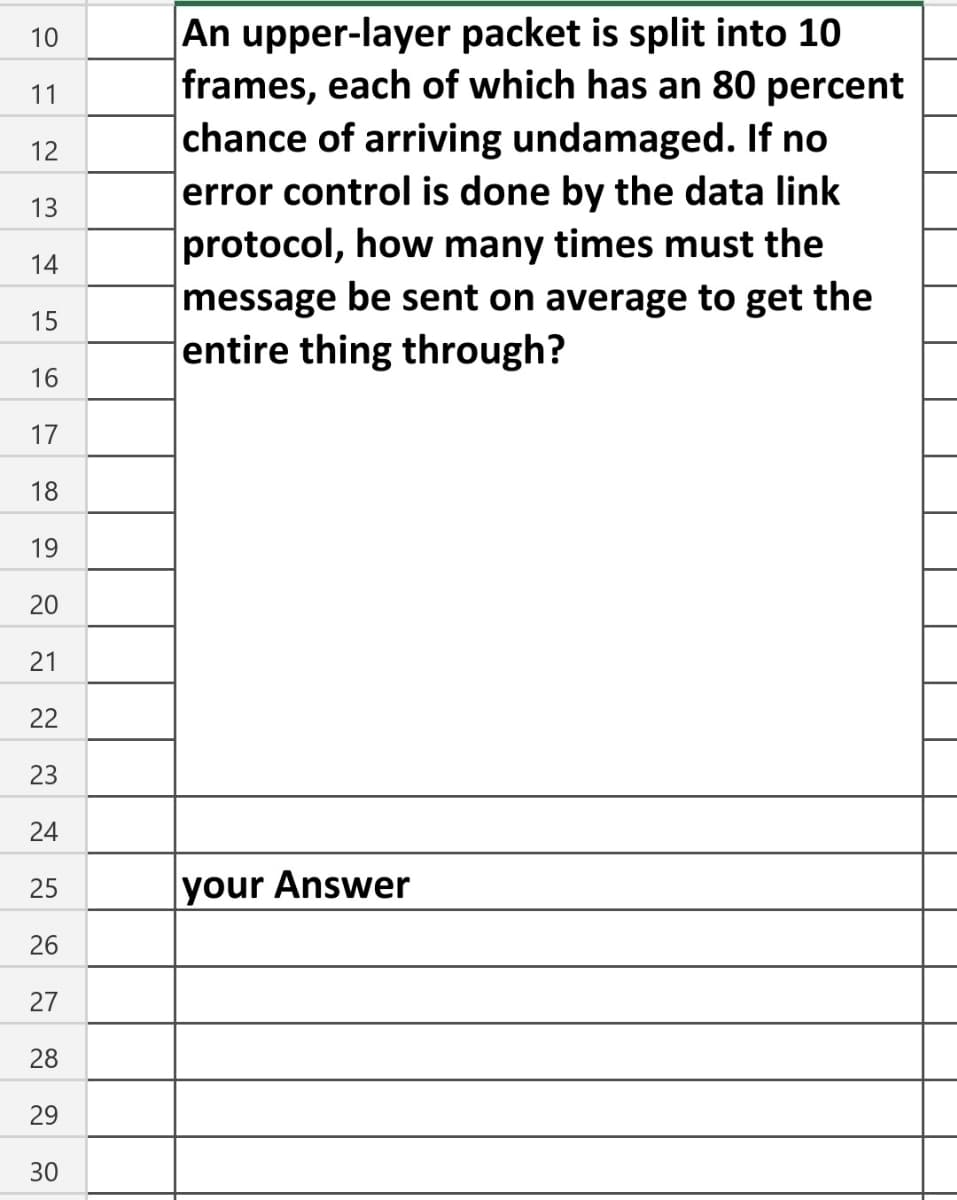
An upper-layer packet is split into 10 frames, each of which has an 80 percent chance of arriving undamaged. If no error control is done by the data link protocol, how many times must the message be sent on average to get the entire thing through?
Q: Just how crucial are algorithms in modern computing?
A: Computer: Hardware and software are both components of computer systems. RAM, a motherboard, a…
Q: How does Apache Pig differ from MapReduce?
A: Apache Pig is an abstraction over MapReduce. It is a platform which is used to analyze larger sets…
Q: In terms of features, how is Android Pie different from the versions that came before it?
A: Android 9 pie offers the several features that has to improve several facts of daily experience.…
Q: crime? What do we take for granted in cyber?
A: Cyber crime:- Crime is an illegal action for which we get punished or can be punished by law. Cyber…
Q: When building a mobile app, what are some things to keep in mind? How do you think an app gets…
A: Given: Some factors to take into account while creating an app include: Always check to see whether…
Q: Show how the letters A, B, and C can be turned into decimal numbers. A.
A: Introduction: Decimal Number System Base-ten systems are used in the decimal number system. There…
Q: Why is it important to have disc storage?
A: Definition: To install operating systems, applications, extra storage devices, and to preserve data,…
Q: an to have a computer that is built int
A: Introduction: Computers are already transforming. For decades, the speed of computer hardware…
Q: A broadcast network is one in which a transmission from any one attached station is received by all…
A: Broadcast networks refer to networks such as LANs connected by a technology such as Ethernet.…
Q: 1. In Arduino Uno board, the total number of the analog I/O pins is08084 2. program that runs on the…
A: The answer to each fill in the blanks is given below with brief explanation..
Q: No one knows how many times the ALU accesses main memory during a single fetch/execute cycle.
A: The answer of the question is given below
Q: When and where did the first tablet computer appear, and who created it?
A: The answer to the problem is given down below
Q: Show how the letters A, B, and C can be turned into decimal numbers. A.
A: System of Decimal Numbers A base-10 number system underlies the decimal system. It has ten symbols,…
Q: Can you tell me the best technique to identify the motherboard?
A: The answer of the question is given below
Q: For what reason should the EndOfStream property of a StreamReader object be checked before calling…
A: Please see the solution below: Answer: Before invoking the Read Line method on a Stream Reader…
Q: This question refers to the following declaration: String line = "Some more silly stuff on…
A:
Q: How are dual-channel and single-channel memory architectures distinct from one another?
A: Memory on a computer: Memory in computer science refers to the temporary storing of data. This…
Q: How can we weigh the pros and cons of redesigning the keyboards?Managing Storm Wind Studios is…
A: Definition: IPAM stands for IP Address Management, and it manages DNS and DHCP, which provide…
Q: re we'll discuss the drawbacks of a local area netw
A: Introduction: Below describe the drawbacks of a local area network (LAN) could be a cluster of…
Q: What are the three most important aspects to think about while deciding on hardware
A: Three most important aspects while deciding on hardware:- Quality Price Service after the sale…
Q: What was the name of the first computer that was sold to the public in the US?
A: In the nineteenth century, English mathematician Charles Babbage created the first iteration of what…
Q: What are the advantages and disadvantages of making only some of the symbols defined inside a kernel…
A: A loadable kernel module is the object file that contains code to extend the running kernel, also…
Q: who came up with the idea for the multi-touch screen?
A: We need to discuss the invention of multi-touch screen.
Q: 1) Is the following an AVL tree? 2) For each node provide the balance (Balance is the difference…
A:
Q: What do supercomputing, grid computing, and cluster computing have to do with Moore's law?
A: Moore's law helps businesses that were not possible once to have demand and access to computing…
Q: es it imply when we say that there has been a "data le
A: Introduction: A data leak occurs when sensitive information is inadvertently exposed physically, on…
Q: There are two common ways to build systems that should be found. What are the most important pros…
A: Numerous Software Development Methodologies are widely used. These include: Waterfall Construction…
Q: Ensure that the loop displays values from 50 to 40 in multiples of 3 (i.e. 50, 47, 44, 41). for (int…
A:
Q: Write the SQL code for the Object-Identity and Reference Types.
A: Given: Since C++ is a compiled language, you must translate the source code into an executable file.…
Q: Take into account the following scenario: we have a byte-addressable computer with 2-way set…
A: Virtual Memory Organization: The RAM and caches that make up the contemporary computer system's…
Q: What are reasons for breaking a long data transmission up into a number of frames?
A: Find Your answer below
Q: The process of crawling and indexing the web is called "crawling" and "indexing."
A: Given: Web crawling refers to the process through which search engines examine and analyze…
Q: At the time, Philip Emeagwali was only 17 years old when he made the fastest computer in the world.
A: Answer: We need to write some point regarding the when made the fastest computer in the world . so…
Q: When compared to traditional methods of data storage, what advantages does cloud computing have?
A: Answer:
Q: A World Wide Web server is usually set up to receive relatively small messages from its clients but…
A:
Q: MicroStrategy puts Intelligent Cube Technology to good use in what ways?
A: Answer:
Q: What does it mean when there are more than one computer mice?
A: Scorecards may be created by businesses using internal techniques. For instance, they could contract…
Q: Define "OLTP" for me, please.
A: The answer of the question is given below
Q: IMPORTANT: The directions include sample code from the dragon-themed game. Be sure to modify any…
A: Code: rooms = { 'Theater Hall': {'South': 'Stairwell'}, 'Stairwell': {'North': 'Theater…
Q: Explain what a random forest is and how it is different from a decision tree in one or two…
A: Decision trees and random forests random forest tree Decision trees are the only thing that make up…
Q: Who came up with the idea for using vacuum tubes in the first computers?
A: Answer is
Q: Consider a half-duplex point-to-point link using a stop-and-wait scheme, in which a series of…
A: According to the information given:- We have to follow the instruction mentioned and find out what…
Q: Where does multiprocessing come in, and how does it function?
A: When computer was invented, it was build with the intention to perform single talk at a time. As the…
Q: It's important to understand why a computer has parts.
A: It's important to understand why a computer has parts.
Q: List and briefly define some of the requirements for effective communications over a data link.
A: Definition: synchronization of frames (beginning and and end of each frame is recognizable)-Flow…
Q: How can we weigh the pros and cons of redesigning the keyboards?
A: A keyboard is an information device that is the most basic means for a client to communicate with a…
Q: Let's pretend for a moment that we have a byte-addressable computer with fully associative mapping,…
A: Visualization Through Associative Mapping: To remember information that pertains to both of the…
Q: When you give your computer the ping command, what protocol are you using to talk to it?
A: answer is
Q: When it comes to a processor's access to main memory, the loosely connected setup and the symmetric…
A: The symmetric multiprocessing arrangement and the loosely connected design are contrasted: A sort of…
Q: What is a (DBA) database administrator? What does a DBA have to do? (OR) What are some of the jobs…
A: A database administrator, or group of administrators, is in charge of overseeing all operations…
Step by step
Solved in 2 steps

- Write a program to create a new key pair, and then use the new key pair to launch an EC2 instance, which has 20GB EBS attached, and allows public http request.I am using SwaggerHub for API documentation for my web application. When I use the bearer token for authentication, and I run a get request that is supposed to return a JSON of the user's trip information. It returns a 200 HTTP response, but the body response does not return the JSON information, instead it returns HTML text. The image below shows the result. Why is this happening?Suppose an HTTP client makes a first GET request to the gaia.cs.umass.edu web server for a base page that it has never before requested, which contains an embedded object, which causes the client to make a second GET request. A very short time later, the client then makes a third GET request - for the same base page, with that third GET request having an If-Modified-Since field (as does the 4th GET request that the client makes for the embedded object). Neither the base object nor the jpeg object has changed. How many round trip times (RTTs) are needed from when the client first makes the third GET request (i.e., when it requests the base object for the second time) to when the base page and the jpeg file are displayed a second time, assuming that: any time needed by the server to transmit the base file, or the jpeg file into the server's link is (each) equal to 1/2 RTT the time needed to transmit an HTTP GET into the client's link is zero? the time needed by the server to transmit…
- The URL Connection class can be used to read and write data: Select one: a.To the specified resource referred by the HttpResponse and the URL b.To the specified resource referred by the URL c.To the specified resource referred by the HttpServer and the URL d.To the specified resource referred by the ServerSocket and the URLThe WebSocket protocol provides a way to exchange data between browser and server via persistent connection. Once the socket is created, there are events following that. Analyze all the FOUR (4) events and provide a code snippet of every event.A ________ bridge can forward and filter frames and automatically build its forwarding table. a. simple b. dual c. transparent d. none of the above
- The problem below involves the UDP protocol.DescriptionClientSend an integer in the range 0 to 100 representing a student’s score in COMP2602 to the server.Use a loop to send five score to the server in all. Each score is sent one at a time so that theserver can respond to each score sent.ServerThe server receives each integer score from the client and returns the letter grade for that score tothe client where it is printed. Note: THE GRADE IS PRINTED AT THE CLIENT.Grade scheme 0-49 F, 50-70 C, 71-80 B, 81-100 AYou may use any reasonable IP addresses and port numbers in your program.Notes: Name the client client.py and the server server.pyWrite a Console java program named SimpleUdpServer that demonstrates the basic components of a simple UDP server by binding a dedicated socket on the server for other UDP clients to connect to. solve it without paperTake a look at two real-world HTTP response codes on the MIT website, for instance, and consider how they relate to the HTTP commands they are linked with (s).
- An instance of ServerSocket listens for TCP connection requests and creates a new Socket instance to handle each incoming connection. Select one: True FalseQUESTION 21 It is possible for two UDP segments to be sent from the same socket with source port 5723 at a server to two different clients. True False QUESTION 22 The acronym API in this textbook stands for “Application programming interface”. True FalseModify the following code to send one maximum-size UDP datagram, read it back, and print the number of bytes returned by recvfrom. #include "unp.h" voiddg_cli(FILE *fp, int sockfd, const SA *pservaddr, socklen_t servlen){ int n; char sendline[MAXLINE], recvline[MAXLINE + 1]; while (Fgets(sendline, MAXLINE, fp) != NULL) { Sendto(sockfd, sendline, strlen(sendline), 0, pservaddr, servlen); n = Recvfrom(sockfd, recvline, MAXLINE, 0, NULL, NULL); recvline[n] = 0; /* null terminate */ Fputs(recvline, stdout); }}

