and c.
Programming Logic & Design Comprehensive
9th Edition
ISBN:9781337669405
Author:FARRELL
Publisher:FARRELL
Chapter7: File Handling And Applications
Section: Chapter Questions
Problem 6PE
Related questions
Question
Please provide the formula to be entered for a, b, and c.
Transcribed Image Text:A
E
G
1
Instruments Collection
Instrument Manufactur Condition Purchase Da
Est. Value - Colum
Price
Bass drum
Baijan
Good
4/4/2020
$45
$105
4
Bassoon
Rossellini
Good
8/14/2020
$300
$510
5
Bugel
McFerrin
Good
3/1/2020
$30
$60
6.
Cello
Celestia
Good
4/14/2019
$100
$255
7
Cello
Cellini
Excellent
6/12/2020
$145
$450
8.
Clarinet
Yamamoto
Excellent
9/27/2021
$200
$350
9
Clarinet
Yamamoto
Fair
10/14/2018
$55
$190
10
Cornet
Diehl & Berne Excellent
4/20/2019
$120
$250
11
Cymbals
Cymbals
Yamamoto
Excellent
6/12/2019
$35
$175
12
Yamamoto
Fair
6/12/2019
$35
$90
13
Baijan
Baijan
Sousa
Didgeridoo
Excellent
8/2/2021
$30
$55
14
$45
$170
Djembe
Drum kit
Excellent
8/2/2021
15
Needs repair
1/14/2019
$150
$150
16
Flute
Sousa
Needs repair
1/14/2019
$106
$106
17
Flute
Wagner
Good
7/11/2020
$245
$290
18
French horn Kutter Davison Good
8/14/2020
$105
$275
19
French horn McFerrin
Needs repair
9/27/2021
$195
$195
$170
$100
20
Guitar
Behred
Good
9/4/2020
$70
21
Guitar
RJ Cohen
Fair
9/4/2020
$35
22
Oboe
Sousa
Good
9/4/2020
$130
$255
23
Piccolo
Wagner
Good
8/1/2019
$85
$125
24
Recorder
Abalone
Good
11/10/2020
$27
$50
25
Recorder
Baijan
Excellent
6/12/2019
$35
$85
26
Saxophone
Rossellini
Fair
10/14/2018
$35
$100
27
Singing bowl Kayho
Good
7/11/2020
$10
$15
$130
$275
$25
28
Snare drum Sousa
Good
4/4/2020
29
Tambourine Ruby Klein
Good
4/4/2020
$10
30
Trombone
Yamamoto
Excellent
8/11/2019
$250
$625
31
Trumpet
Rossellini
Good
7/11/2020
$140
$250
32
Tuba
Diehl & Berne Needs repair
7/11/2020
$90
$90
33
Upright bass Celestia
Excellent
3/9/2021
$500
$800
34
$480
$480
Upright bass Yamamoto
Viola
Needs repair
12/1/2020
35
Cellini
Needs repair
8/1/2019
$120
$120
36
Violin
Wagner
Good
11/10/2020
$78
$172
37
Violin
Yamamoto
Excellent
6/12/2019
$150
$425
38
Violin
Yamamoto
Fair
4/14/2019
$100
$160
39
40
Total
36
$4,416
$7,998
41
Documentation
Brass
Percussion
Strings
Wind
All Instruments
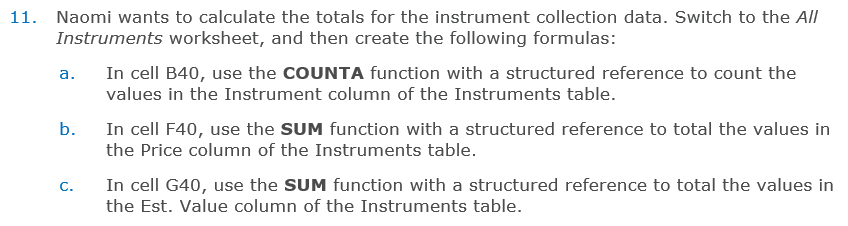
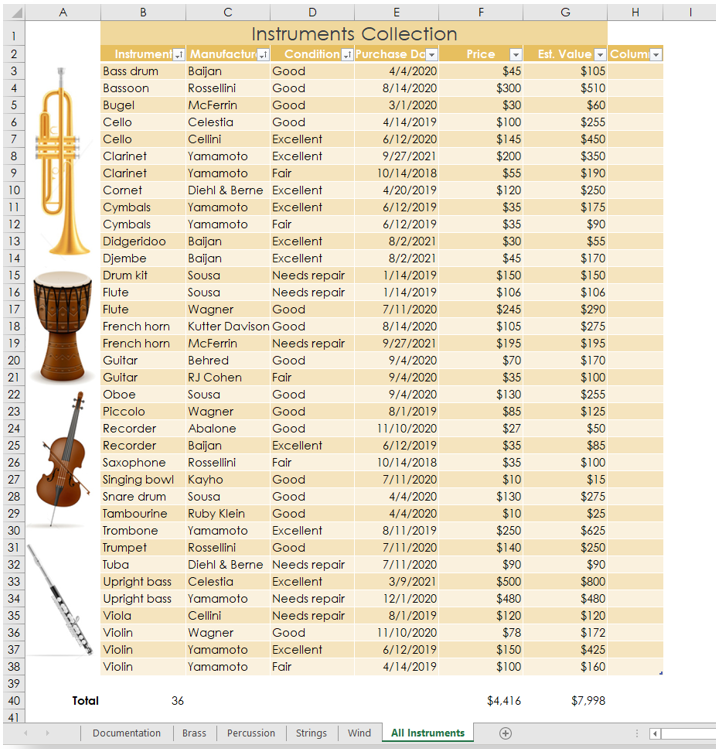
Transcribed Image Text:11. Naomi wants to calculate the totals for the instrument collection data. Switch to the All
Instruments worksheet, and then create the following formulas:
In cell B40, use the COUNTA function with a structured reference to count the
а.
values in the Instrument column of the Instruments table.
b.
In cell F40, use the SUM function with a structured reference to total the values in
the Price column of the Instruments table.
In cell G40, use the SUM function with a structured reference to total the values in
C.
the Est. Value column of the Instruments table.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 6 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage