anguages home > 10 14 LAB Warm up Contacts TIn main.prompt the user tor three contacTS and outpuT me users mpUT are reco list (2 pts) Ex Pernon 1 Enter name: Hoxanne Hughes Enter phoneo numbor: 443-555-2864 You entered: Roxanne tughes, 143 555-2864 Person 2 Enter nama: Juan Alberta Jr. Enter phone number: 410-555-9385 You entered: Juan Alberto r., 410-555-9385 Person 3 Enter nane: Rachel Phillips Rnter phone number: 310-555-6610 You entered: Rachel Phillips, 310-555-6610 (4) Output the linked list (2 pts)
anguages home > 10 14 LAB Warm up Contacts TIn main.prompt the user tor three contacTS and outpuT me users mpUT are reco list (2 pts) Ex Pernon 1 Enter name: Hoxanne Hughes Enter phoneo numbor: 443-555-2864 You entered: Roxanne tughes, 143 555-2864 Person 2 Enter nama: Juan Alberta Jr. Enter phone number: 410-555-9385 You entered: Juan Alberto r., 410-555-9385 Person 3 Enter nane: Rachel Phillips Rnter phone number: 310-555-6610 You entered: Rachel Phillips, 310-555-6610 (4) Output the linked list (2 pts)
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter17: Linked Lists
Section: Chapter Questions
Problem 18SA
Related questions
Question
I need some help and i need it in c++ for zybooks
Transcribed Image Text:14-CS 210 Prograx
Anewered Vou will be building
Home
ok/SNHUCS210v2/chapter/10/section/14
Mail - Eddy, Matthe
g Languages home > 10 14 LAB Warm up Contacts
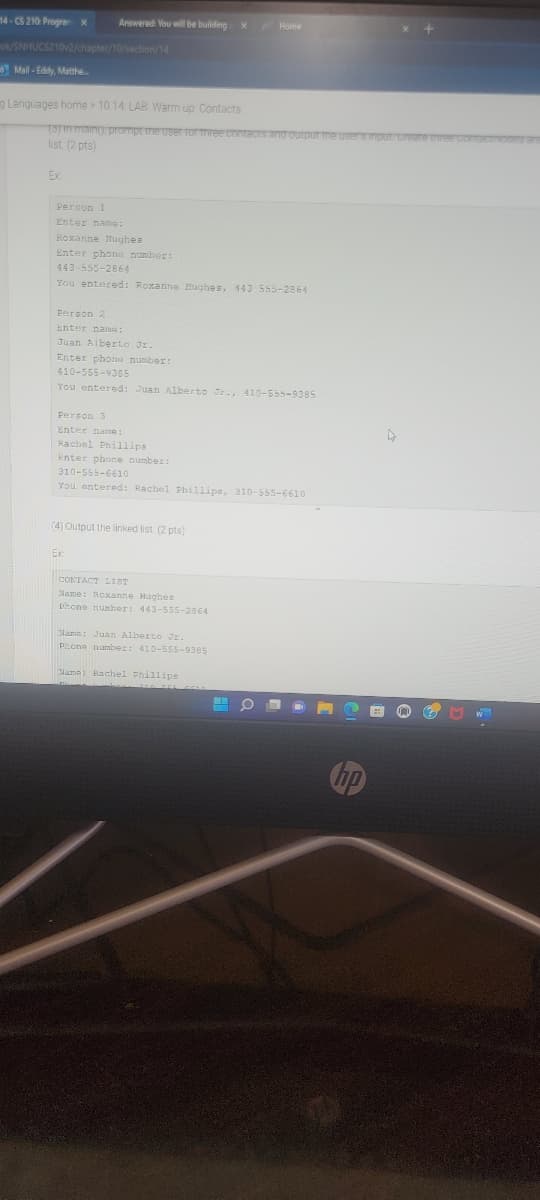
3) in main) prompt the user for three contacts and outpur me users input rere tnree CoOCITV
list (2 pts)
Ex
Person 1
Enter name:
Roxanne lughes
Enter phone number:
443-555-2864
You entered: Roxanne Hughes, 143 555-2864
Person 2
Enter nama:
Juan Aiberto Jr.
Enter phone number:
410-555-9385
You entered: Juan Alberto Jr., 410-555-9385
Person 3
Enter name:
Rachel Phillips
Enter phone number:
310-555-661o
You entered: Rachel Phillips, 310-555-6610
(4) Output the linked list. (2 pts)
Ex
CONTACT LIST
Name: Roxanne Hughes
Pone number: 443-555-2864
Mama: Juan Alberto JE.
Pone number: 410-555-9385
Nama: Rachel Phillips
hp
Transcribed Image Text:CS 210 Progra
SNHUCS210v2/chapter/10/section/14
Mal - Eddy, Matthe
anguages home > 10.14. LAB Warm up Contacts
10 13
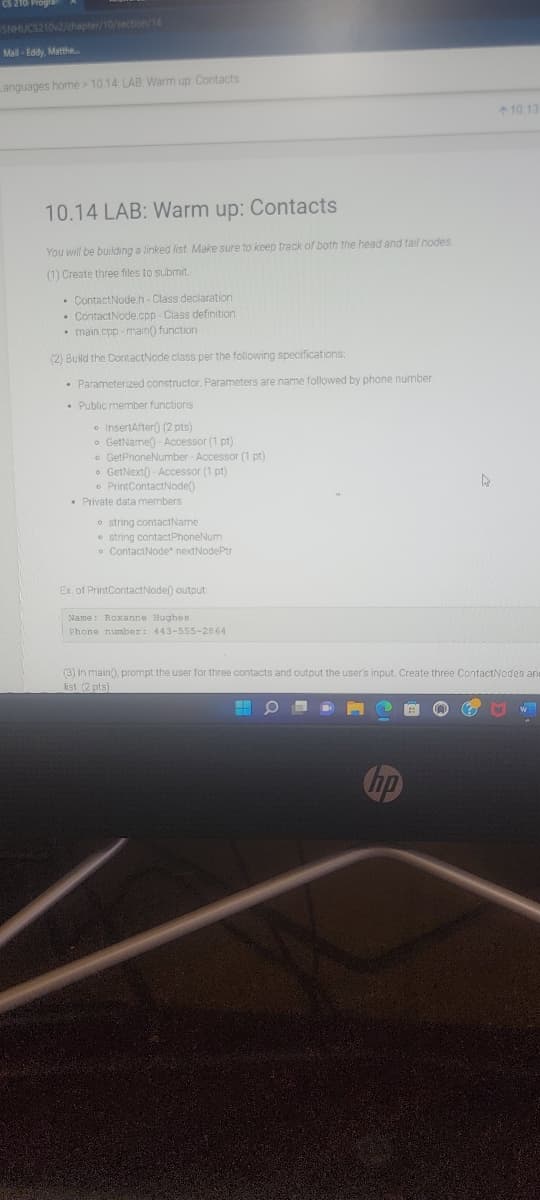
10.14 LAB: Warm up: Contacts
You will be building a linked list Make sure to keep treck of both the head and tail nodes
(1) Create three files to submit.
• ContactNodeh-Class declaration
• ContactNode.cpp Class definition
• main.cpp - main() function
(2) Build the ContactNode class per the following specifications:
• Parameterized constructor. Parameters are name followed by phone number
• Public member functions
• InsertAfter() (2 pts)
o GetName() - Accessor (1 pt)
• GetPhoneNumber - Accessor (1 pt)
• GetNext() - Accessor (1 pt)
• PrintContactNode()
• Private data members
o string contactName
• string contactPhoneNum
• ContactNode* nextNodePtr
Ex, of PrintContactNode() output
Name: Roxanne Hughes
Phone number: 443-555-2864
(3) in main), prompt the user for three contacts and output the user's input. Create three ContactNodes an
list (2 pts)
hp
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

Follow-up Questions
Read through expert solutions to related follow-up questions below.
Follow-up Question
LAB ACTIVITY
10.14.1: LAB: Warm up: Contacts
Solution
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning