Answer the given question with a proper explanation and step-by-step solution. Please I want a flow chart for this program.
Q: Please offer a brief explanation as well as a definition for microcontrollers.
A: Answer: Introduction Microcontroller is a single Integrated Circuit that is typically used for the…
Q: Web Vulnerabilities Assessment Instructions Protecting e-commerce, social media, and email…
A: Web application security is crucial for protecting sensitive information, maintaining user trust,…
Q: context of operating systems, what precisely does the phrase "partitioning" refer to? Think about…
A: Partitioning in the context of operating systems refers to the division of a physical hard drive…
Q: Explain what is meant by the word "cybersecurity," and talk about why it's so important to put into…
A: We have to explain the term: Cyber Sercurity
Q: What sets a hashtable distinct from a hashmap, and how are they both used?
A: The Hashtable and Hashmap. Both HashMap and HashTable are among the most used classes in Java's…
Q: Which fibre is utilised to protect the inner core and prevent the cable from straining in fiber-…
A: Introduction: Fiber optic cable is a form of network cable that is commonly used to carry data. It…
Q: Imagine that your database management system is broken. Describe the process of restoring a…
A: In reality, info is stored in a computer. When a database becomes corrupted, recovery is the process…
Q: What are the two main advantages of layered protocols? Give evidence.
A: The transfer of files, for example, requires numerous protocols. It's common to see a series of…
Q: In this grammar, "S" is the starting symbol, which generates a sentence by combining a noun phrase…
A: Let's first go through the fundamentals of parse trees and context-free grammars. A set of…
Q: What exactly does it mean when we talk about the conceptual framework of cybercrime? Provide…
A: Introduction:- Many people, businesses, and governments rely heavily on the Internet to function. It…
Q: What are the four main benefits of employing continuous event simulation, and could you elaborate on…
A: Continuous event simulation is a type of computer simulation that models the behavior of complex…
Q: Explain "matching in algorithms."
A: Matching in algorithms refers to the process of identifying pairs of elements in a set that satisfy…
Q: You may want to think about using the WAN, or wide-area network, as your primary wireless…
A: Given: Contemplate WAN wireless access. Why is this option better? Is your method safe? Provide…
Q: You, as CISO, are in responsible of creating a comprehensive information security plan supported by…
A: Introduction: Protection plan: An organisation's documented security programme or policy lays out…
Q: Please provide a succinct explanation of the calling protocol.
A: In this question we have to understand explanation of the calling protocol. Let's understand and…
Q: Shown below is a rundown of the three stages that comprise the physical design process, along with a…
A: Physical design is an important process in the field of electrical engineering that involves…
Q: ) Circuit switching; (b) Virtual circuit and datagram packet switching. The stations are separal…
A: The answer is
Q: When someone says they utilize "propositional reasoning," what exactly does that mean? What exactly…
A: What is the definition of "propositional logic"? What function does propositional logic serve inside…
Q: The following is an 8051 instruction: CJNE A,#'Q',AHEAD a. What is the opcode for this instruction?…
A: The CJNE A,#'Q',AHEAD instruction is a command used in the 8051 microcontroller to compare the value…
Q: The question is, given two strings, str1 and str2, how many minimal operations on str1 may be…
A: Answer: Algorithms: Step1: we have create the function and takes the arguments two string s1 and s2…
Q: Please provide a succinct explanation of the instruction pointer.
A: A register inside the CPU's control unit that is used to store the address of the current or next…
Q: You may describe the function of each component of a typical operating system in a single sentence…
A: An operating system (OS) is a software program that manages a computer's hardware and software…
Q: In the context of the administration and monitoring of a network, what role does logging play?…
A: The answer to the question is given below:
Q: Walk me through the inner workings of predictive analytics and give me an example of its potential…
A: Predictive analytics is a technique that leverages historical data, statistical algorithms, and…
Q: What is the key difference between BLOB and CLOB data types when working with JDBC?
A: Answer: BLOB: A blob is a binary large object of variable length used to contain several bytes of…
Q: Included in this document need to be a description of the five most common network topologies. Which…
A: Bus Topology: In a bus topology, all devices are connected to a single cable called a "bus." Data is…
Q: Indices can speed up query processing, but it's usually a terrible idea to index every attribute,…
A: Indices play an essential role in speeding up query processing in databases. They help in quickly…
Q: Please provide a succinct explanation of the XMM registers.
A: The XMM registers are a set of registers in the x86-64 architecture that are specifically designed…
Q: Walk me through the stages involved in the process of reading and writing files.
A: Given, Walk me through the stages involved in the process of reading and writing files.…
Q: Can You draw the digital circuit? I do not understand it the way you presented it.
A: As per the given question, we need to find the minterm expansion of the given truth table and then…
Q: Given the following truth table, abc F 000 1 001 1 010 0 011 1 100 1 101 0 110 0 111 0 a) Find the…
A: To find the minterm expansion of the truth table, we need to find the minterm for each row where F…
Q: What kind of mobile and wireless employee network would you suggest to others?
A: Required: How would you advise them to network while on the go? Devices connected to a wireless…
Q: If you were trying to figure out what was wrong with a computer, what steps would you take?
A: Computers are essential tools in today's world, and they can be frustrating when they stop working…
Q: What three conditions must a network fulfill for proper and effective operation? Take a moment to…
A: Networking refers to the process of creating and maintaining connections between various devices and…
Q: When a web client requests access to a web server's protected resources, show how native…
A: Given: Show how a web client may utilise the web server's built-in authentication and authorization…
Q: Written in C) Create a payroll program to store and calculate the payroll for a small company as…
A: We have to give implementation of the payroll program in C: Below is the code:
Q: What precisely is meant by the term "network topology"? It is necessary to determine and then…
A: Network Topology : In computer networking, network topology refers to the physical or logical…
Q: Where exactly can you find the ImageList control when using the Toolbox?
A: The Image List component can be found in the Toolbox, which is situated under the Components…
Q: tput This exercise uses sub-algorithms. Trace it for when input value is 6 and complete the trace…
A: Sub algorithms are algorithms that are used as part of a larger algorithm to solve a complex…
Q: Briefly describe the changes that occurred throughout the agricultural revolution.
A: Agricultural Revolution: From the middle of the 17th century and the end of the 19th century,…
Q: 3. What will be the output of the following program? Note the use of to_character() and to_ascii()…
A: As per the given information, we need to provide the output of the given program. The given program…
Q: Please provide a succinct explanation of the XMM registers.
A: XMM register:- XMM registers are an entirely separate set, introduced with SSE, and still commonly…
Q: When it is beneficial to do so, processes and programs that are executed on a big computer should be…
A: Introduction: Hardware and software are the two major divisions of a computer system. The first and…
Q: Think about how important wireless network infrastructure is in today's underdeveloped countries. In…
A: You can maintain local area networks (LANs') effective operation with the help of an exemplary…
Q: What's an organization's information security limit? What are an organization's earliest and latest…
A: By using information security, organisations are able to protect both digital and analogue data…
Q: What are the two main advantages of layered protocols?
A: What is use the use of layered protocol?
Q: Do in-depth analysis of the characteristics of massive data sets and categorize the many forms these…
A: Massive datasets are characterized by their volume, velocity, variety, veracity, and value. These…
Q: What kind of impact does the blockchain have on the process known as "Systems Analysis and Design"?
A: The "disruptive" nature of blockchain technology may be linked to the fact that it introduces a…
Q: As the number of computing devices available to users continues to grow, personal computing…
A: A multi-device-friendly website is a website that is designed and developed to provide a seamless…
Q: Part 1: Write a program that tracks employee information. The program should use classes for…
A: Managing employee information is an essential task for any organization. Keeping track of employee…
Answer the given question with a proper explanation and step-by-step solution.
Please I want a flow chart for this program.
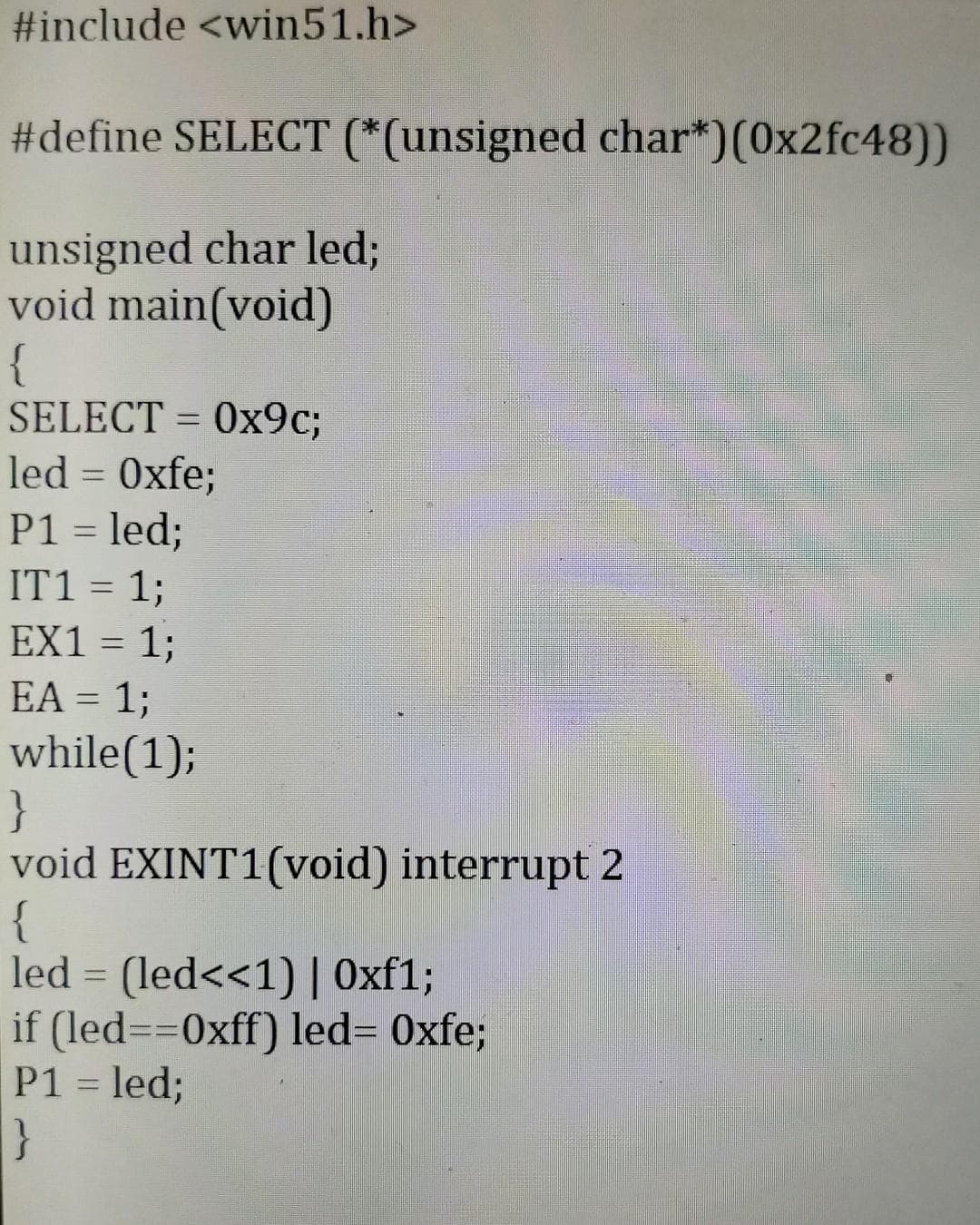
Step by step
Solved in 3 steps with 1 images

- write in C for a STM32F446RE microcontroller Write a source library that contains the with the following public functions: void keypadInit(void); /Initiallized the GPIO to read the keypad. uint16_t readKeypad(void); //Returns the state of all of the keypad buttons in the return value at the moment the function is called. void decodeKeypad(uint16_t, char *); //Takes the state of the keypad and returns (by reference) an array of the key's pressed. The library should work with the following main: int main (void) { uint16_t key; char carray[17]; keypadInit(); while(1) { while(!(key = readKeypad())); /*Get which keys pressed*/ decodeKeypad(key, carray); /*What are those keys*/ printf("%s\n",carray); /*Print those keys to screen*/ while(readKeypad() == key); /*Wait for the keypad to change*/ }} Problem 1: Write a library that works with the following pin assignments Row 0 -> PC0 Row 1 -> PC2 Row…please code in pythonthe below code has alot of errors .. please make it error free import numpy as np import randomimport sys import osfrom datetime import datetimeimport string import subprocess from subprocess import callfrom subprocess import check_output if len(sys.argv) < 3: print('Usage: maintest.py Nm Ns R \n') exit() Ns = sys.argv[1] #sort size R = sys.argv[2] #number of repetitions w = open('BubbleSortResult.txt', 'w')#BubbleSort1: No Split Input = np.random.rand(Ns) Itmp = list (Input) def sort (numbers): sorted = False while not sorted: sorted = True for i in range (len (numbers)-1): if numbers [1] > numbers [i + 1]: sorted = False numbers [i + 1], numbers [i] = numbers[i], numbers [ i + 1]Te = datetime. now () for i in range (R): #Run R-time Itmp = list (Input) # Get fresh Input #print (Itmp) sort (Itmp) # This is in-place sort. Input will be altered. Te = datetime. now () - Te Totalus…Question:- 1 Recreate the following C program in x86-64 and aarch64 assembly manually: #include <stdio.h> typedef struct _v2d {long x;long y;} v2d_t; static long dot(v2d_t a, v2d_t b){return a.x * b.x + a.y * b.y;} static long dot_ptr(v2d_t *a, v2d_t *b){return a->x * b->x + a->y * b->y;} int main(void){v2d_t a, b; scanf("%ld %ld %ld %ld", &a.x, &a.y, &b.x, &b.y); long res1 = dot(a, b);printf("%ld\n", res1); long res2 = dot_ptr(&a, &b);printf("%ld\n", res2); return 0;}
- extern "C" int f(int *,int,int); int a[2][2] = {{11,12},{21,22}}; void setup(){ Serial.begin(115200); while(!Serial); delay(500); int *arr = (int*)a; Serial.println(f(arr,2,2)); } void loop(){ } .global f f: ldr r3,[r0] // get first element mov r2,#0add r2,r3 mov r1, #3 lp: add r0,#4 // add next elementldr r3,[r0]add r2,r3sub r1,#1 bgt lp mov r0,r2 bx lr Describe what operation is being performed in this code* Assignment: Word operations * * Description: * This assignment asks you to implement common word operations that are * not available in the Scala programming language. The intent is to practice * your skills at working with bits. * */ package wordOps /* * Task 1: Population count (number of 1-bits in a word) * * Complete the following function that takes as parameter * a 32-bit word, w, and returns __the number of 1-bits__ in w. * */ def popCount(w: Int): Int = ??? /* * Task 2: Reverse bit positions * * Complete the following function that takes as parameter * a 16-bit word, w, and returns a 16-bit word, r, such that * for every j=0,1,...,15, * the value of the bit at position j in r is equal to * the value of the bit at position 15-j in w. * */ def reverse(w: Short): Short = ??? /* * Task 3: Left rotation * * Complete the following function that takes two parameters * * 1) a 64-bit word, w, and *…1. Put the following code into a complete C program: int i = 0; void func(char *str1, char *str2) { char *ptr = malloc(sizeof(int)); char buf[1024]; int j; static int y; } 2. Compile the program using gcc in Linux. 3. Use gdb to debug and print the addresses of variables in the code. 4. Draw the stack frame of func() and point out the addresses of related variables. 5. Document your steps for each question
- Write in c language please, The Fibonacci sequence begins with 0 and then 1 follows. All subsequent values are the sum of the previous two, for example: 0, 1, 1, 2, 3, 5, 8, 13. Complete the Fibonacci() function, which has an index n as a parameter and returns the nth value in the sequence. Any negative index values should return -1. Ex: If the input is: 7 the output is: Fibonacci(7) is 13 Note: Use a for loop and DO NOT use recursion.Assignment for Computer Architecture You are to write a program in MIPS that computes N! using recursion. Remember N! is the product of all the numbers from 1 to N inclusive, that is 1 x 2 x 3 x (N – 1) x N. It is defined as 1 for N = 0 and is undefined for values less than 0. The programs first requests the user to input the value of N (display a prompt first so the user knows what to do). If the input value is less than 0, the program is to display “N! undefined for values less than 0” and then requests the user to input the value of N again. If the value input is non-negative, it is to compute N! using a recursive function, that is one that calls itself. You are to have your name, the assignment number, and a brief description of the program in comments at the top of your program. Since this is an assembly language program, I expect to see comments on almost every line of code in the program. Also make the code neat: line up the command fields, the register fields, and the comment…C++ Programming, Stack queue and dequeImprove the error code below, you can also create custom methods in the main class. See attached photo for the instructions.main.cpp: In function ‘int main(int, char**)’: main.cpp:17:15: error: expected primary-expression before ‘char’ stack<char> s; ^~~~ main.cpp:21:17: error: ‘s’ was not declared in this scope s.push(x[i]); ^ main.cpp:22:37: error: ‘s’ was not declared in this scope else if (x[i]==')' and !s.empty()) ^ main.cpp:44:16: error: ‘s’ was not declared in this scope return (s.empty()); ^ main.cpp:47:14: error: jump to case label [-fpermissive] case 1: ^ main.cpp:16:16: note: crosses initialization of ‘std::__cxx11::string x’ string x=str; ^ main.cpp:56:14: error: jump to case label [-fpermissive] case 2: ^ main.cpp:16:16: note: crosses initialization of ‘std::__cxx11::string x’ string x=str; ^ main.cpp:74:14: error: jump to case label [-fpermissive] case 3: ^ main.cpp:16:16: note: crosses initialization of ‘std::__cxx11::string x’…
- Write a C++ program that takes a char array (char *) that take your name as input, a char pointer point it and convert lower to upper and vice versa.PROGRAMMING LANGUAGE: C++ // vectors: overloading operators example#include <iostream>using namespace std;class counter{private:int count;public:counter():count(0){}counter(int c):count(c) {} int get_count(){return count;} counter operator++ (int){return counter(count++); } counter operator-- (int){return counter(count--);}};int main(){counter c1, c2, c3;c1++;c2--;cout<<'\n'<<c1.get_count();cout<<'\n'<<c2.get_count();cout<<endl;c3 = c1++;cout<<'\n'<<c1.get_count();cout<<'\n'<<c3.get_count();getch();return 0;} Go through the above code and write the output of the given code segment. counter c1(5), c2(10), c3;c3=c1++;c2=--c3;;cout<<”\n”<<c1.get_count();cout<<”\n”<<c2.get_count();cout<<”\n”<<c3.get_count();1.Put the code into a complete C program int i = 0; void func(char *str1, char *str2) { char *ptr = malloc(sizeof(int)); char buf[1024]; int j; static int y; } 2. Compile the program using gcc in Linux. 3. Use gdb to debug and print the addresses of variables in the code. 4. Draw the stack frame of func() and point out the addresses of related variables.



