Answer the questions given in the picture about UML and Java
Database Systems: Design, Implementation, & Management
11th Edition
ISBN:9781285196145
Author:Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Chapter2: Data Models
Section: Chapter Questions
Problem 3P
Related questions
Question
Answer the questions given in the picture about UML and Java
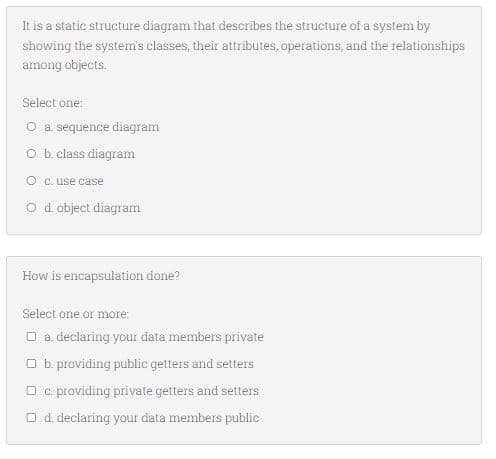
Transcribed Image Text:It is a static structure diagram that describes the structure of a system by
showing the system's classes, their attributes, operations, and the relationships
among objects.
Select one:
O a sequence diagram
O b. class diagram
O c. use case
O d. object diagram
How is encapsulation done?
Select one or more:
O a declaring your data members private
O b. providing public getters and setters
O c. providing private getters and setters
O d. declaring your data members public
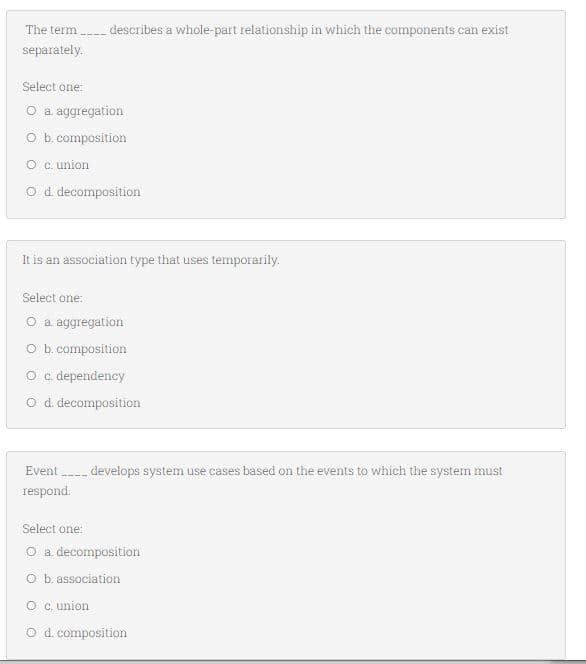
Transcribed Image Text:The term - describes a whole-part relationship in which the components can exist
separately.
Select one:
O a. aggregation
O b. composition
O c. union
O d decomposition
It is an association type that uses temporarily.
Select one:
O a. aggregation
O b. composition
O c. dependency
O d decomposition
Event develops system use cases based on the events to which the system must
respond.
Select one:
O a decomposition
O b. association
O c. union
O d. composition
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr