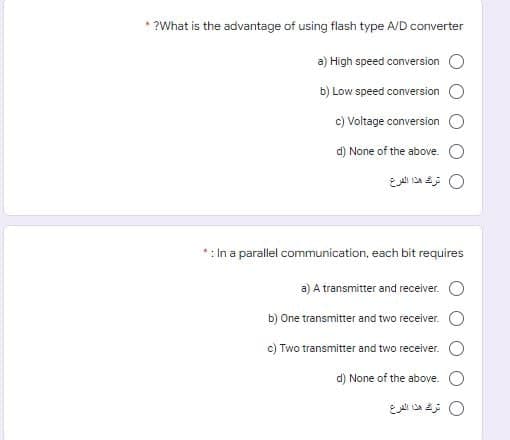
antage of using flash type A/D converter a) High speed conversion O b) Low speed conversion O c) Voltage conversion O d) None of the above. O EA DA O
Q: What is the origin of the three-tier database architecture?
A: A 3-tier application architecture is a modular client-server architecture that consists of a…
Q: Compare between the different Input-Output control techniques: programmed I/O, interrupt, DMA, and…
A: Introduction: Compare the different Input-Output control techniques: programmed I/O, interrupt, DMA,…
Q: lk about the
A: IntroductionAlthough random access memory (RAM) is the most popular type of computer memory, there…
Q: When it comes to the scheduling of the CPU, what happens if multiple different processes have the…
A: Introduction: The scheduler permits each process to run for its own time as long as the procedures…
Q: For procedures that aren't addressed by a systems analysis, consider using Structured English
A: A human (or individual) will study a system to carry out a process known as systems analysis. This…
Q: Explain what the term "input device" means to you using your own words.
A: Input device: Input device. a computing device that is attached to the outside of a computer and…
Q: As a student, Is it important to memorize the number of the connection or the contacts? Why? Prove…
A: As a student, Is it important to memorize the number of the connection or the contacts??
Q: 8 The turing machine is as follows, (1,0,1,2.R), (1,1,0,2.R), (2,0,0,2,L), (2,b,b,1,R), (2,1,b,1.R.)…
A: ANSWER:-
Q: Demonstrate digital forensics' ad hoc structured and enterprised stages.
A: Introduction: Digital Forensics identifies, acquires, processes, analyses, and reports…
Q: what are The Effects of Emerging Technology on Healthcare and the Diffifficulties of Integration
A: In this question we have to discuss the effects of technology on healthcare and difficulties to…
Q: potential advantages as well as the potential disadvantages of artificial intelligence
A: Introduction of the potential advantages as well as the potential disadvantages of artificial…
Q: What is a DNS forwarder, and how does it work?
A: Having one forwarder is typically more cost-effective than having numerous forwarders from a network…
Q: The figure shown below is the output of: Three functions change with x 100 -Square data -Square-root…
A: In a MATLAB graph, one can draw many functions together as well as separately. Here in the given…
Q: Does anybody know how the DNS works, including how iterated and non-iterated queries, authoritative…
A: The Domain Name System (DNS) is the Internet's telephone directory. Humans often utilize domain…
Q: raw the discrete Hopfield neural networks block scheme
A: The answer is given below.
Q: Could you explain the concept of cloud scalability and how it works? What characteristics of cloud…
A: Answer: cloud scalability is expanding or descending the IT resources as per requirement. This…
Q: write DQL statement to do the following (and a screenshot of the result): 2. Find products that have…
A: SELECT DISTINCT(P.ProductName) FROM OrderDetails O, Products P WHERE NOT (P.ProductID =…
Q: How do you determine the error detection and error correction capabilities of a given code with…
A:
Q: 1. Create a class named Cat. Declare two (2) empty instance variables: catType (String) and…
A: In this question we have to create a java class and create some constructor methods which will set…
Q: Assuming two processes are currently running; deferring execution till one of them completes. For…
A: The operating system is what links the machine's hardware to the programmes that run on it. State of…
Q: Describe both the potential upsides and potential downsides of artificial intelligence.
A: AI's Advantages: 1. Artificial intelligence shortens the time it takes to finish a job. 2. It…
Q: write DQL statement to do the following (and a screenshot of the result): 1. Find cities that exists…
A: SELECT * FROM Customers, Suppliers WHERE Customers.City = Suppliers.City;
Q: Assignment 4- Arrays Write C++ program that do the following: 1- Ask the user to enter size of the…
A: Given: To write a C++ program to find average of array elements and print the elements that are…
Q: An explanation of the Address Resolution Protocol is required (ARP).
A: Protocol for Address Resolution ARP is a communication technique used to determine the MAC address…
Q: JavaScript
A: Given :- In the above question, the statement is mention in the above given question Need to…
Q: in any five downsides of cloud comp
A: Introduction: Below five downsides of cloud computing that are often neglected.
Q: 1. Consider the following P = (P1, P2, P3, P4, P5) R = (R1, R2, R3, R4) E = (P3>R1, P2 R2, R4 P4, R2…
A:
Q: In the field of computer science, discuss both the benefits and the drawbacks of using EDI.
A: An Electronic Data Interchange is electronic interchange of business information using a some…
Q: A CPU interrupt causes the processor to halt what it's doing and respond to the signal. Why should…
A: Introduction: When a process or event demands immediate attention, interrupts are generated by…
Q: What are your thoughts on the trustworthiness of root certificates generated by web browsers?
A: As a result, talk about the trustworthiness of browser-provided root certificates. The reliability…
Q: What is the normal location of the devices that make up a LAN?
A: A local area network, more commonly referred to as a LAN, is a network that connects computers that…
Q: Implement HTML code that displays the table below. 00 00 00 00 00 0 00 00 00 00 00 00 00 00 00 00 00
A: The HTML code to display the given table is as follows.
Q: What makes a CPU (Central Processing Unit) different from a GPU (Graphical Processing Unit)
A: The main difference between CPU and GPU architecture is that a CPU is designed to handle a…
Q: Identify which documents should be sent to the developer at the end of a project.
A: Answer:
Q: a) Show that R irrational numbers are uncountable. b) A= {n²|n E N}, discuss either A or N is the…
A: Answer
Q: Provide a rundown of the primary technical components that make up a typical Hadoop system, along…
A: Hadoop is a free and open-source software framework for storing and executing data on commodity…
Q: Run the Bellman-Ford Algorithm on the graph below to find the shortest path distances from the…
A:
Q: As a software engineer, how do you come up with an accurate cost estimate for the project you're…
A: Estimating software costs is inherently challenging because people are bad at predicting absolute…
Q: What hurdles does the organization experience in hiring a diverse workforce? Extend the notion with…
A: There are many challenges that might arise with various workforces: 1. Communication problems…
Q: Explain in great detail the many forms that digital signatures might take.
A: Given: We have to discuss in detail the many forms that digital signatures might take.
Q: Can you tell me about the storage structure that the Android operating system uses?
A: Introduction: We use a certain form of storage in Android to permanently store the data (not…
Q: Show, through examples, that interrupt-driven operating systems outperform non-interrupt-driven…
A: Introduction: Interrupt-driven operating systems outperform non-interrupt-driven operating systems,…
Q: When it comes to scheduling the CPU, what happens if multiple different processes have the same…
A:
Q: Are you in favor of or opposed to violence? In network communication, end-to-end congestion control…
A: end-to-end congestion control is used efficiently to regulate congestion. End-to-end congestion…
Q: uishing characteristics of time-sharing and distributed operating systems, and how do these two…
A: Below are the distinguishing characteristics of time-sharing and distributed operating systems
Q: What are the four most important things that happen throughout the course of a software development…
A: The following are the four basic activities in software development: Specification of software…
Q: CREATE A C++ PROGRAM THAT THE USER WILL INPUT 4 NUMBERS AND THE OUTPUT IS TO ARRANGE IN ASCENDING…
A: doing this program with the if-else statement, there are many statements that need to be checked.…
Q: An answer to the question "What is the purpose of the WLC-Virtual Interface?"
A: Introduction: An answer to the question "What is the purpose of the WLC-Virtual Interface?"
Q: Instructions: 1 #include 2 #include 1. In the code editor, you are provided with a…
A: As per the requirement c++ program is developed. Note: As per our guidelines we are suppose to…
Q: When it comes to operating systems, what is the difference between real-time and non-real-time? In…
A: Differences between real-time and non real-time operating systems: Real time operating systems focus…
Step by step
Solved in 2 steps

- Answer the following short questions briefly. Convert the following decimal integers into binary, octal, and hexadecimal:(a) 23, (b) 107, (c) 1238 (d) 92 (e) 173 Convert the following BCD numbers (assume that these are packed numbers) to decimal numbers:(a) 10001001, (b) 00001001(c) 00110010, (d) 00000001 Convert the following decimal numbers into both packed and unpacked BCD forms:(a) 102, (b) 44(c) 301, (d) 1000 Convert the following decimal numbers into 8-bit signed binary numbers:(a) +32, (b) -12 (c) +100 Convert the following binary numbers to the two’s complement form:(a) 1000 0001, (b) 1010 1100(c) 1010 1111, (d) 1000 0000 Find the memory address of the next instruction executed by the microprocessor, when operated in the real mode, for the following CS:IP combinations:(a) CS = 1A00H and IP = B000H(b) CS = 2300H and IP = 1A00H(c)…C) How many bytes are contained in each of the following data types?I) wordII) doublewordIII) quadwordIv) double quadwordQ1 \ Convert the following infix expression into postfix one: (A+B^D)/(D-F)+G PS: you have to illustrate the different steps of this conversion one by one.
- Please answer in C++ Your country is at war and your enemies are using a secret code to communicate with one another. You have managed to intercept a message that reads as follows: :mmZ\dxZmx]Zpgy The message is obviously encrypted using the enemy's secret code. You have just learned that their encryption method is based upon the ASCII code. Appendix 3 shows the character set. Individual characters in string are encoded using this system. For example, the character "A" is encoded using the number 65, and "B" is encoded using the number 66. Your enemy's secret code takes each letter of the message and encrypts it as follows : if (orginalChar + key > 126) then encryptedChar = 32 + ((orginalChar + key) -127) else encryptedChar = (orginalChar +key) For example, if the enemy uses key = 10 then the message "Hey" would be encrypted as: Character ASCII code H 72 e 101 y…Character devices are frequently more efficient than block devices when it comes to transmitting data. True or untrue, is this statement??c++ How do I correct this into the correct format: The input begins with the number of locations. Each location is entered x and then y and then name. Output the name of the closest locations. Here is my code: #include <bits/stdc++.h>#include <cmath>using namespace std; //Compute the distance between two points (x1, y1) and (x2 y2)double getDistance(double x1, double y1, double x2, double y2){ return sqrt ((x2 - x1) * (x2 - x1) + (y2 - y1) * (y2 - y1));} struct Location{ string name; double x; double y;}; int main() { int y = 0; int locationName = 40; const int NUMBER_OF_POINTS = 5; // Each row in points represents a location Location location[NUMBER_OF_POINTS]; // make sure to enter the name of the location so like // longview 237.89 46.68 // dallas 373.62 47.0 cout << "Enter " << NUMBER_OF_POINTS << " points: "; for (int i = 0; i < NUMBER_OF_POINTS; i++) cin >> location[i].name >> location[i].x >>…
- Character devices are often more efficient in transmitting data than block devices. Will this prove to be a true or untrue statement?It's common for character devices to transfer data more quickly than block devices. Is that statement true or false?Communication between character devices is often faster than that between block devices. Could you please tell me whether this statement is true or false?
- // Task 3 // For this function, you must return the largest power of 2 that // is less than or equal to x (which will be positive). You may // not use multiplication or some sort of power function to do this, // and should instead rely on bitwise operations and the underlying // binary representation of x. If x is 0, then you should return 0. unsigned largest_po2_le(unsigned x) { return x; }Rewrite the following statement using a number in scientific notation. My new music player has a capacity of 260 gigabytes.( Recall that giga means billion) My new music play has a capacity of........ bytesFor each of the following modes, write the numeric equivalent (e.g., 777):a. rw-r--r- -b. r--r- -r- -c. ---rwxrw d.-wxr-xrw e.rw-rw-rwxf. -w-r-- - - -

