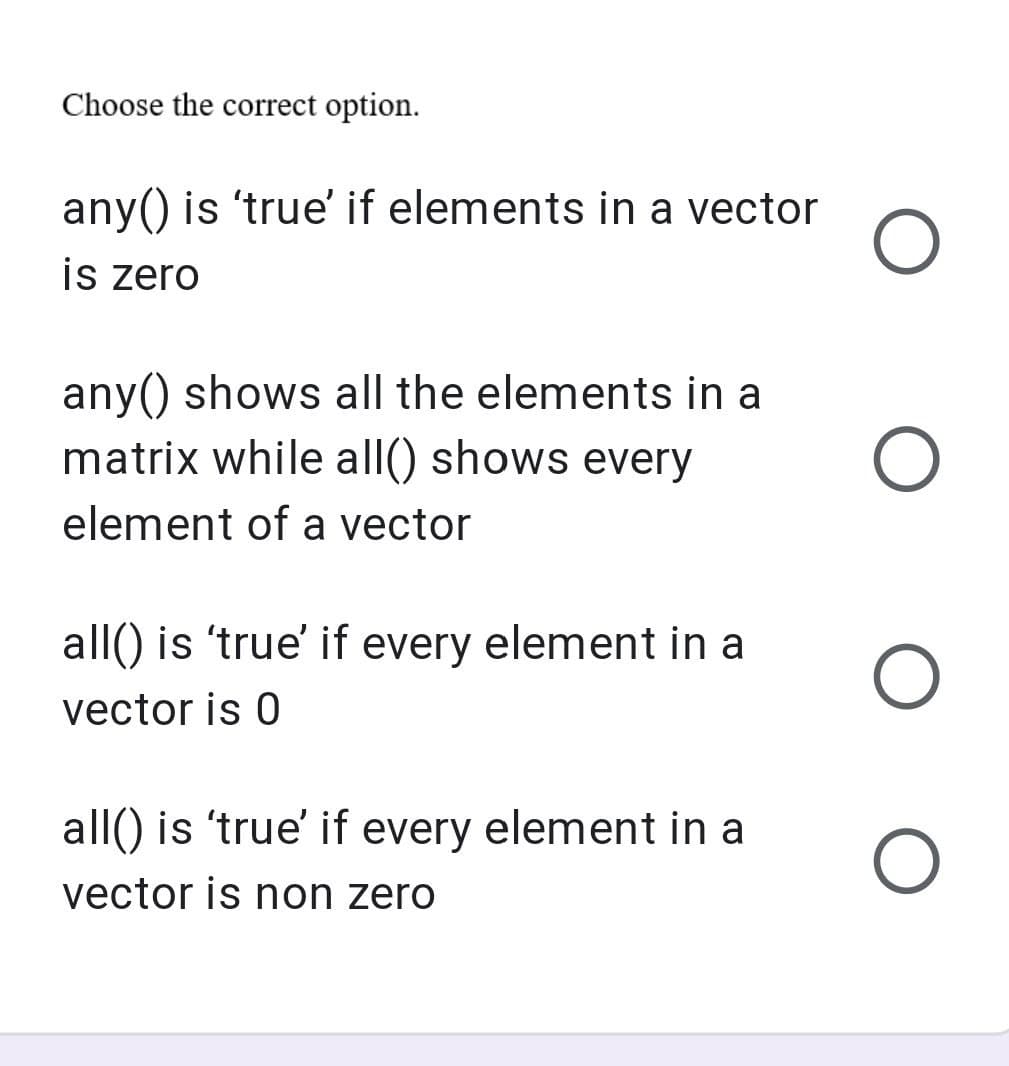
any() is 'true' if elements in a vector O is zero
Q: In the given i-v characteristic below, which load line represent the given circuit? I-V curve for a…
A: Load line: The load line is generally a straight line. The load line is drawn on the characteristic…
Q: A fingerprint reader, rather than a username and password, is the new way that your organization…
A: Reader of fingerprints: Instead of typing a user name and password, a fingerprint scanner is a…
Q: mmarise the Waterfall Systems Development paradigm as follows: What is the difference between this…
A: Introduction: Below describe the difference between Waterfall Systems Development and the Agile…
Q: een the differences between DOS and Windows 98, the two major operating systems released in the…
A: Introduction: Below the Distinguish between the differences between DOS and Windows 98 and Window…
Q: Please explain why the interactive method is better than the waterfall model in terms of the amount…
A: The interactive and waterfall models have different maintenance responsibilities: Animated Models:…
Q: What are the numerous inputs and outputs of the software system design process that should be…
A: System design is the most common way of designing the elements of a framework, for example, the…
Q: When comparing wireless and wired networks, wireless networks have a lesser throughput.
A: Introduction: When properly configured, wired networks offer more longevity and stability than…
Q: What is type casting? Explain implicit and explicit type conversion with example.
A: Typecasting Typecasting, or type conversion, is a method of changing an entity from one data type to…
Q: Write a program that determines if the input letter is a VOWEL or CONSONANT. Your program must be…
A: The five letters A , E , I , O and U are called vowels. All other alphabets except these 5 vowels…
Q: Do you have an opinion on which high-availability DHCP solutions are best for your company and why?…
A: DHCP is a network technology that automatically assigns a unique IP address to each host, allowing…
Q: There are concerns about privacy while using social networks like Facebook, which already have so…
A: INTRODUCTION As indicated by studies, numerous youths accept that social media and social systems…
Q: Write a complete Java program in a class named TwoRockets that generates the following output. Use…
A: Java program for the given problem is: public class TwoRockets { public static void main(String[]…
Q: What are the most important considerations for programmers as they go through the stages of creating…
A: A program is a set of step-by-step instructions given to computer to perform a specific task. A…
Q: Explain if...else... with example and draw flowchart.
A: If else Statement in programming language, when we need to execute a block of statements that too…
Q: If someone tried to get into your computer, where would you look?
A: Given: Windows Task Manager, you may see whether any programmes have been installed on your computer…
Q: Write SQL Statements of the followings (Make sure the syntax is correct) - Create a new database…
A: The question has been answered in step2
Q: 7. The following demonstrate show data can be stored in the data segment and the program rewritten…
A: The following address show the data can be stored in data segment and the program rewritten so…
Q: What are some ways that dynamic scoping can be utilised more efficiently, and what are some ways…
A: Dynamic scope: A global identifier is dynamic scope refers to the identifier associated with the…
Q: Find the answer on the given sets below corresponding the operations (union, intersection and…
A: Complement of a set: The complement of any set is represented as A', B', C' etc. In other words, we…
Q: 13. if AX= 84; what is the result of executing the instruction CWD AX
A: This instruction (Convert signed Word to signed Doubleword) copies the sign bit of a word in AX to…
Q: In terms of information security and risk management, what are the distinctions between the…
A: A network perimeter is the safe border between a network's private and locally controlled side,…
Q: It is vital to prepare and discuss a detailed set of criteria for determining if a project will be…
A: Given: Make a list of the many sorts of project feasibility considerations and discuss them. Is…
Q: Provide a succinct explanation of what the implication of memberwise assignment is.
A: Encryption: In a member-wise assignment, any member of one object may be assigned to another object…
Q: Why do we have to go to the trouble of building a circular array stack? The implementation of queues…
A: Stack: A "circular stack" is technically a circular buffer or ring buffer, rather than a stack. A…
Q: 10110 о о 1011 13 о 11 оо ооооо ооо ооо о о о 12 о ооо о ceil(12.5) Fix(12.5) length('oil and gas')…
A: ceil(N) is a pre-defined MATLAB function that rounds each element of N to the nearest integer…
Q: 14. Assume that AL= 1010 1111, CF=0, Here is how the rotate instruction affect AL and CF. After ROL…
A: After ROL AL, 1AL= 1101 1111, CF=1, After ROR AL, 1AL =1101 0111, CF=1, After RCL AL, 1AL = 0101…
Q: In comparison to a waterfall method, what are the three benefits of incremental development?
A: Given: What are the three benefits of incremental development over waterfall development Incremental…
Q: Where can you get reliable information on the Internet
A: Types of resources Three types of sources exist: Primary, secondary, and tertiary
Q: Describe how a wireless network may help in the event of a crisis.
A: The main goal of network: Disaster recovery is to enable customers to access services even if the…
Q: In this type of digital circuit, its output is dependent of the new input, previous state and clock…
A: in this type of digital circuit, its output is dependent of the new input, previous state and clock…
Q: What are the most pressing considerations for system developers at every stage of the process?
A: The question has been answered in step2
Q: What are the advantages of making use of pure functions?
A: What benefits can pure functions offer: The benefits of pure functions The most significant benefit…
Q: here do you think information security starts and ends in a business? The control of the…
A: One of the most valuable assets in any company is information. Information is essential to a…
Q: You've been given the duty of reviewing an online reservation and ticketing system for trains. What…
A: Overview: A project management strategy that breaks down the processes required in a project's…
Q: (spend, need, laugh, fall, find, break, lose, celebrate, save, leave, take, can) med Ali last week…
A: BELOW:
Q: a network protocol that provides name- .to-address translation IP DHCP NAT DNS O O O O
A: IP stands for "Internet Protocol. The rules defining the format of data sent over the internet or a…
Q: Consider transmitting a packet from a source host to a destination host through a fixed route.…
A: Computer Networks referred as the data network which means the series of the computers that are…
Q: Describe the differences between the three most popular desktop operating systems in as much detail…
A: Given: Describe the differences between the three main desktop operating systems in as much detail…
Q: Write a java program that will validate user given password with following conditions a. length of…
A: As per the question statement, We need to write JAVA program.
Q: firewalls are critical for network security and cybersecurity, thus it's important to understand…
A: The significance of a firewall First and foremost, what is the purpose of a firewall? I have a pc…
Q: Take a look at the advantages and disadvantages of the various picture formats. Which format would…
A: Image representation consists of two components: Vector Picture Raster Image Scalability is a great…
Q: Five - B/ Give the meaning of the full term for each of the following. for only five CLI, VGA…
A: Find the required answers given as below :
Q: In the column vector (f)to add last element (7) we use: a) f(end+1)=7 O b) [f;7] O c) a&b O d)…
A: Answer:- c) a&b Explanation:- f(end+1) = 7here, "end" is a special keyword in MATLAB that…
Q: The IRS, your state's BMV, and Equifax, a consumer reporting agency, undoubtedly have databases with…
A: Capturing data in each database: The Federal Internal Revenue Service (IRS) is an organisation of…
Q: Ques, exxplain Germic claus. with multiple type parameter by a jour programe?
A: Generic class: A generic class declaration looks like a non-generic class declaration, except that…
Q: what will be displayed when you run the code ? a=0;while a<10; value = %2.2f',a) a=a+3;…
A: The while loop evaluates an expression, and repeats the execution of a group of statements in a loop…
Q: lain how teardown delay can affect the total delay in Virtual-Circuit Netw
A: Introduction: There is a one-time setup delay and a one-time tear down delay in a virtual-circuit…
Q: How do you address the issue of internet and social media addiction in a speech?
A: Today's social media is a highly stimulating and speediest media ever seen, and it has recently been…
Q: In the operations portion of the business plan that you are currently drafting for your firm, how…
A: Answer: The following are five methodologies to assist managers with actually settling clashes with…
Q: a process that is used only when the .dynamically learned route has failed subnetting O static…
A: A floating static route is a backup route to any static route or a dynamically learned route. This…
Step by step
Solved in 2 steps with 2 images

- Help please! Dan holds his CSC108 lectures in a rectangular N x M lecture hall. In other words,this lecture hall has N rows of seats, each of them containing exactly M seats.Here’s my attempt at drawing this layout when N = 3 and M = 5:lecture hall layout with 3 rows and 5 seats perrowThe rows are numbered from 1 to N starting from the frontrow. Similarly, thecolumns are numbered from 1 to M starting from the leftmostcolumn. We write(r, c) to denote the c-th seat in the r-th row.When Dan walks into the lecture hall this morning, some of the seats are alreadytaken (this is the initial layout of the lecture hall). Afterthat, the studentscome inone group at a time. From experience, Dan knows that when a group of K studentsenterthe lecture hall, they look for K consecutive empty seats. That is, they try tofind an empty seat (r, c) such that for all integers i in [0, K-1], the seat (r, c +i) exists and is empty. If they can’t find K consecutive empty seats, they leave thelecture hall…Write a program that enables the user to addor remove points by clicking the left or right mouse button and displays a noncrossedpolygon that links all the points, as shown in Figure a. A polygonis crossed if two or more sides intersect, as shown in Figure b. Use thefollowing algorithm to construct a polygon from a set of points:python How to convert the first and the last character of each element n _student to uppercase? Hint :use the function map0 that return a map object(which is an iterator) of the results after applyingthe given function to each item of a qiven iterable (list, tuple etc.) Syntax : map(a function towhich map passes each element of given iterable, terable which is to be mapped)n_student=pd.Series(['Justine', 'nora', 'Ugur', 'lana', 'hiba', 'lola'])
- PLEASE REFER TO THE IMAGES FOR INSTRUCTIONS PLEASE USE STARTER CODE - CODE IN PYTHON3 ### starter code import random def spider_web(web_map, starting_place, destination): pass def spider_web_rec(web_map, starting_place, destination, visited): pass def make_spider_web(num_nodes, seed=0): if seed: random.seed(seed) web_map = {} for i in range(1, num_nodes + 1): web_map[f'Node {i}'] = [] for i in range(1, num_nodes + 1): sample = random.sample(list(range(i, num_nodes + 1)), random.randint(1, num_nodes - i + 1)) print('sample', i, sample) for x in sample: if i != x: web_map[f'Node {i}'].append(f'Node {x}') web_map[f'Node {x}'].append(f'Node {i}') return web_map if __name__ == '__main__': num_nodes, seed = [int(x) for x in input('Input num_nodes, seed: ').split(',')] the_web = make_spider_web(num_nodes, seed) print(spider_web(the_web, 'Node 1',…Using GNU Octave, create a row vector that has following elements: 3, 4*2.55, 68/16, 45, nthroot (100,3), cos(25) and 0.05You will also have to write Student Tests that test the following in the provided file.i. Adding element(s).ii. Get elements at index – (1) with a valid index and (2) with an invalid indexiii. Test equality of two StringArrayLists (of size 0, 2)iv. Test if a StringArrayList contains a String (test both true and false cases)v.Test removing a String from a StringArrayList.
- How would you access all elements in this vector 'mountain <- c("tree", "rock", "dirt", "dolphin", "waterfall")' except 'dirt'? a. mountain[3] b. mountain[-3] c. mountain(3) d. mountainWrite a Javascript program with explaination Use Bootstrap to style the table. The trip data needs to begin as an array literal of object literals, where each trip is an object with 3 properties. The button must have an id property, and using getElementById('id') you must assign the function that displays the table to the button using an anonymous function in your JavaScript code. You should concatenate the table elements as shown in the examples in the notes for JavaScript objects. Before being inserted into a table cell, the mpg must be calculated and not be part of the data objects. round the calculation to 1 decimal placeYou have been provided with the following elements:• Sifiso• Ayanda• Andries• Tshegofatso• MarianneWrite a Java program in NetBeans that creates a TreeSet. Your Java program must use themethods in the TreeSet interface to do the following:• Add the above elements into the TreeSet• Display all the elements in the TreeSet• Get the last element in the TreeSet• Display elements that are greater than or equal “R” in the set
- Please can you tell me if this is true or false? The map(callback [, thisArg]) method returns the index of the first element in the array that passes a test in thecallback function. True FalseWe have a vector, A, with the following integers: 22, 17, 8, 11 How does the following change those integers? A[1] <- 13 Question 2 options: no change 22, 13, 8, 11 13, 17, 8, 11 13, 13, 13, 13Need help with the parts that say TODO in images , This may be needed scoresheet code below package edu.vtc.cis2271.yahtzee; import java.util.ArrayList;import java.util.HashSet;import java.util.List;import java.util.Set; public class Scoresheet{ private static final int SMALL_STRAIGHT_SCORE = 30;private static final int LARGE_STRAIGHT_SCORE = 40;private static final int FULL_HOUSE_SCORE = 25;private static final int YAHTZEE_SCORE = 50;private static final int TOP_HALF_BONUS = 35;private static final int TOP_HALF_BONUS_LEVEL = 63; @SuppressWarnings("javadoc")public enum Category {Ones,Twos,Threes,Fours,Fives,Sixes,SmallStraight,LargeStraight,ThreeOfKind,FourOfKind, FullHouse, Yahtzee,Chance} public Scoresheet(){_scores = new int[Category.values().length];_listeners = new ArrayList<>();for (int i = 0; i < _scores.length; i++)_scores[i] = -1;} public void addScoreSheetListener(ScoreSheetListener listener){_listeners.add(listener);} public void…











