Apply external styling to the form the diagram below building up on the code
Q: What are the advantages of having a company-wide incident response strategy?
A: company-wide incident response strategy: In the event of an emergency, an incident response plan is…
Q: What methods can be used to deal with massive data sets, which can be terabytes in size and are…
A: Computer Clusters: A computer cluster is a collection of two or more computers, or nodes, that work…
Q: Q2: Interface two of chips 64 K X8 EPROM and two chips of 64K X8 RAM with 8086. Select a suitable…
A: The Answer is in Below Steps
Q: Describe how third-party cookies are made in your own words.
A: Third party cookies Explained: A third-party cookie is placed on a website by someone other than the…
Q: Find three paradigms for software development that don't strictly conform to the waterfall process.
A: The software development life cycle encompasses a number of methodologies and models for monitoring…
Q: Interruptions are described using the following terms: Explain their types and why no hardware…
A: Introduction: An interrupt is a signal that the processor receives to interrupt the current process…
Q: Write an application that allows a user to input customer records (ID number, first & last name,…
A: public class Customer { int idNumber; String firstName; String lastName; double balance;…
Q: Why do active attacks pose a greater threat than passive attacks? Use real-life examples to back up…
A: Active Attack: Active attacks are type of attack in which and the attacker efforts to change or…
Q: What are the difficulties associated with implementing mobile technology? Are the savings comparable…
A: What are the difficulties associated with implementing mobile technology? Are the savings comparable…
Q: The five most frequent network topologies should be outlined. Which one do you consider to be the…
A: Given: We have to discuss The five most frequent network topologies should be outlined. Which one…
Q: It is suspected that out of a set of 64 50p coins one of the coins is fake (i.e., lighter in weight…
A: The answer is as follows.
Q: Discuss the many types of protocols and why they are necessary. (Information technology)
A: Network Protocol: An Overview There are billions of individuals, millions of apps, millions of…
Q: Identify the topologies of five common networks. Which do you believe to be the most reliable source…
A:
Q: Interruptions are described using the following terms: Explain their types and why no hardware…
A: Hardware Interrupts: An interrupt is a signal received by the processor that causes the program to…
Q: Super@WUDOL MINGW64 ~/Desktop/cse1001/lab23 $ java Countdown.java Enter a number: 10 10 9 8 3 2 1…
A: Here I have defined the method named recursiveCountdown(). In this method, I have printed the…
Q: What is a typical TSR software like?
A: The TSR is also known as terminate-and-stay-resident program.
Q: Explain what a trojan horse is and express if it is compositing of other malicious malware. (A1,…
A: Trojan horse is a downloaded and installed computer program that seems harmless, but actually…
Q: as well
A: Antivirus software, or antivirus software (truncated to AV software), otherwise called enemy of…
Q: What are the characteristics of a social networking site like Pinterest?
A: Introduction: We define social network sites as web-based services that enable people to (1) create…
Q: Q7: The hash value of the password is not enough to protect the password without salting. Explain…
A:
Q: Due to a cyber assault on the network system, the protocol has been disrupted.
A: Any form of an offensive attack that is intended to target the computer network for the purpose of…
Q: What are the four most basic elements of software development? Please let us know which of the other…
A: Introduction: These are the four primary process tasks that are organized differently in different…
Q: Given the following two methods from the List interface draw the final state of an initial empty…
A: ArrayList is a data structure present in List interface of util package in java. ArrayList is a…
Q: What are the advantages of having a company-wide incident response strategy?
A: An incident response strategy is a collection of recommendations for identifying, responding to, and…
Q: We'll go through the most significant information system issues to be aware of, as well as the most…
A: Here are the 5 most common IT problems and how to solve them.1. Lack of Staff (Internal) Security…
Q: So why is software development vital? .. How do you think the software development process may…
A: Software development vital: Software engineers have aided society by making our lives easier,…
Q: So why is software development so vital? .. In order to increase software performance, add four…
A: Software development can enhance client experiences, introduce more feature-rich and new products to…
Q: What are the difficulties in putting mobile technology into practice? Are the savings comparable to…
A: What are the difficulties in putting mobile technology into practice? Are the savings comparable to…
Q: pologies can b
A: Topology characterizes the design of the organization of how every one of the parts are…
Q: Find out what constitutes a mission-critical information system and its basic components.
A: Mission-critical system: A mission-critical system is a computer, electrical, or electromechanical…
Q: Is there a correlation between software development's cohesion and coupling?
A: NOTE :- Below i explain the answer in my own words by which you understand it well. Coupling…
Q: Your boss has asked for your input on how to increase the possibility that personnel of the…
A: Information System: Computers, tablets, smartphones, hard drives, and other types of information…
Q: When creating an MS-DOS directory entry, what are the seven most important fields?
A: Structure of the MS-DOS Directory In Microsoft Disk Operating System (MS-DOS), a directory entry is…
Q: If you are a bank IT manager, what would be your advice / best practice on: How to achieve highest…
A: To Avoid Below 1. Keylogger 2.Phising 3.Sware and Adware 4.Chip secrets
Q: Six components of an information system should be recognised, outlined and specified.
A: Six components of an information system should be recognised, outlined and specified. Answer: The…
Q: As far as I'm concerned, what is the difference between the two types of cryptography?
A: Cryptography studies secure communication mechanisms that restrict access to a message's contents to…
Q: Python Create a function named Triangle(a,b,c) which can take in three floats as inputs (a, b, and…
A: Step-1: Start Step-2: Declare three variable a, b, c and take input from user Step-3: Call function…
Q: Consider how reporting systems, data mining systems, and Big Data systems differ. What do they have…
A: mining systems and big data systems: The following are the distinctions between reporting systems,…
Q: A control's attribute determines whether or not it is shown on the form during runtime, much like…
A: User Interface Programming (GUI): Attribute Control Charts are a set control charts designed…
Q: It is important to explain how the spiral model of software development can handle both Waterfall…
A: Start: The Spiral Model is a risk management system development life-cycle (SDLC) strategy that…
Q: As far as I know, metrics are used in the software development process, but I'd want to know more…
A: Software Development: A software metric is a quantifiable or countable representation of a program's…
Q: Give a situation in your life where you are using proper netiquette and proper ethics in digital…
A: let us see the answer: Introduction:- Netiquette is a term that combines the words "network" and…
Q: What are the four components that make up the industrial Internet?
A: The industrial internet is composed of four primary components:
Q: expression of (Z2) is .. when realizing the following ASM- chart by using traditional- technique…
A:
Q: How are websites and webpages different?
A: The answer of this question is as follows:
Q: Exactly what is the difference between the "system" and "user" areas?
A: System and user Space: User space is the area of memory in a computer operating system that contains…
Q: Which of the following shows the correct syntax for an if statement? O if expression O expression if…
A: if block is used to specify a block of Java code to be executed if a condition is true. The syntax…
Q: Choose an information system and explain the differences between the functional and non-functional…
A: The functional and non-functional : Functional testing includes API testing, system testing, and…
Q: JAVA PROGRAMMING HELP ME! PLEASE MAKE THIS PROGRAM RUN, I' HAVING HARD TIME TO FIX IT PLEASE. I…
A: As per the requirement I have executed the program, while executing I found two errors while…
Q: Examples of what kind of website may be found on Twitter and LinkedIn:
A: Start: When it comes to searching and interacting, the difference between Twitter and LinkedIn is…
Apply external styling to the form the diagram below building up on the code
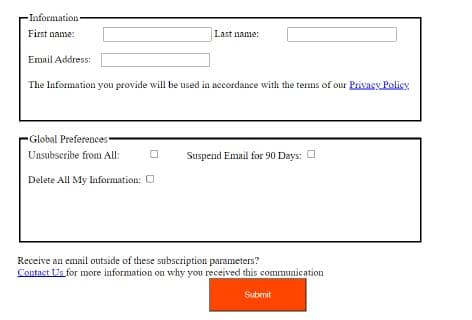
Step by step
Solved in 5 steps with 8 images

- Create your personal opinion about Intrusion Detection and Intrusion Prevention. Don't copy paste please.(Security) Discuss appropriate security patterns and anti-patterns (including password policies) we should apply to security on future versions of our student webserver (currently: Loki).For the Agent Tesla malware, please write a short paragraph based on the given background and website info: Agent Tesla is a RAT that targets Windows operating systems. It is available for purchase on criminal forums as Malware-as-a-Service (MaaS). It has various capabilities depending on the version purchased, including capturing keystrokes and screenshots, harvesting saved credentials from web browsers, copying clipboard data, exfiltrating victim files, and loading other malware onto the host. https://www.cisecurity.org/insights/blog/top-10-malware-december-2022 Agent Tesla is an extremely popular spyware Trojan written for the .NET framework that has been observed since 2014 with many iterations since then. It is used to steal sensitive information from a victim’s device such as user credentials, keystrokes, clipboard data, credentials from browsers, and other information. This information can then be traded or used for business intelligence or ransom. Agent Tesla is most commonly…
- Describe a privacy problem that is so severe that it would cause you to discontinue your use of Facebook.dont dont post copied content sure sure strict reportManvi-CS What are the steps involved in using PGP (Pretty good privacy) to set up your own public-key encryption system? Where are the private and public keys stored?
- There are multiple ways to prevent from this spyware. There are some that should always keep in mind like disabling cookies, javascript for mail and news, use alternative tools of Internet Explorer, configuring personal firewalls or installing anti-virus. [ your answer goes here ] What may it mean if the deleting of these file were not recorded in the audit log? Provide at least 3 items with reasons. [ your answer goes here ] What is the impact/cost of auditing events? [ your answer goes here ] What is the impact/cost of not auditing events? [ your answer goes here ]5) Which of the following statement(s) is/are FALSE? (i) The common security strategies are: encryption, antivirus, access control, and authentication. (ii) To detect and prevent malware attacks, we should install firewallsoftware. E.g. McAfee, Norton, Kaspersky, MS Word, MS Excel, etc. (iii)To decrypt is to scramble and convert the original data or information into an unintelligible and meaningless form. (iv)For an infected computer, antivirus can scan viruses and other malware, then remove them, or quarantine the infected files. A. (i) only B. (ii) only C. (i) and (iv) only D. (ii) and (iii) only E.None of the aboveHi, I need to answer this question. The name of the book is "Computer Security and Penetration Testing, 2nd Edition". Thank you. Question: What are some consequences of spoofing? Would any be deemed illegal? Explain.
- Can you read this and correct errors if you see them please thank you for some reason bartleby write not working and I need it edit please? Thank you for your time I chose cybersecurity specialist as my career for several reasons. The main reason is I can provide for my family. I will be able to hire assistants, and we can live more comfortably. Cybersecurity is a technology equipped to protect programs, network, system, and data from cyber-attack. Since the introduction of new technology, adjustment of cyber threats and risk is accumulating for cybercriminal. Today cybersecurity is important because the world uses more technology, and when you use your device more likely cyber-attack can affected. Cybersecurity protects electronic data and information. For my career I desire to stop cybercriminal who are escalating their attacks with advancement from technology. Taking cybersecurity, I would love to fix cyber-attack, yet also protect your device before cybering comes in. The types of…Describe a privacy issue so serious that it would case you to stop using Facebook.You are asked to do some research, and write a report that answers the following questions about Digital Fingerprinting: You should tackle the following points: What is Digital Fingerprinting and for what purposes is it used? How does the fingerprinting algorithm work? Describe its principle of operation. Certain steps are followed to reach the desired result- either block, delete or authorize usage of content. Some cybersecurity experts say that fingerprinting is abusive and exposes the privacy issues of users. Certain solutions were done by some browsers for blocking browser fingerprinting. Describe the measures taken by any of the browsers as a fingerprint defense mechanism. List two common Fingerprinting Algorithms. Report Writing: You should follow the following guidelines while writing your report: Your report should be between 400 and 500 words in length. Ensure that your report has an appropriate structure and writing style. Your report…



