are used to implement access control by defining permissions based on a user's token, or key. ---
are used to implement access control by defining permissions based on a user's token, or key. ---
Management Of Information Security
6th Edition
ISBN:9781337405713
Author:WHITMAN, Michael.
Publisher:WHITMAN, Michael.
Chapter8: Security Management Models
Section: Chapter Questions
Problem 17RQ
Related questions
Question
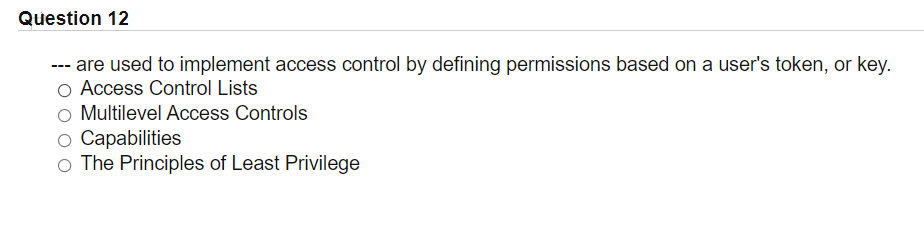
Transcribed Image Text:Question 12
--- are used to implement access control by defining permissions based on a user's token, or key.
Access Control Lists
Multilevel Access Controls
o Capabilities
o The Principles of Least Privilege
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Management Of Information Security
Computer Science
ISBN:
9781337405713
Author:
WHITMAN, Michael.
Publisher:
Cengage Learning,

Management Of Information Security
Computer Science
ISBN:
9781337405713
Author:
WHITMAN, Michael.
Publisher:
Cengage Learning,