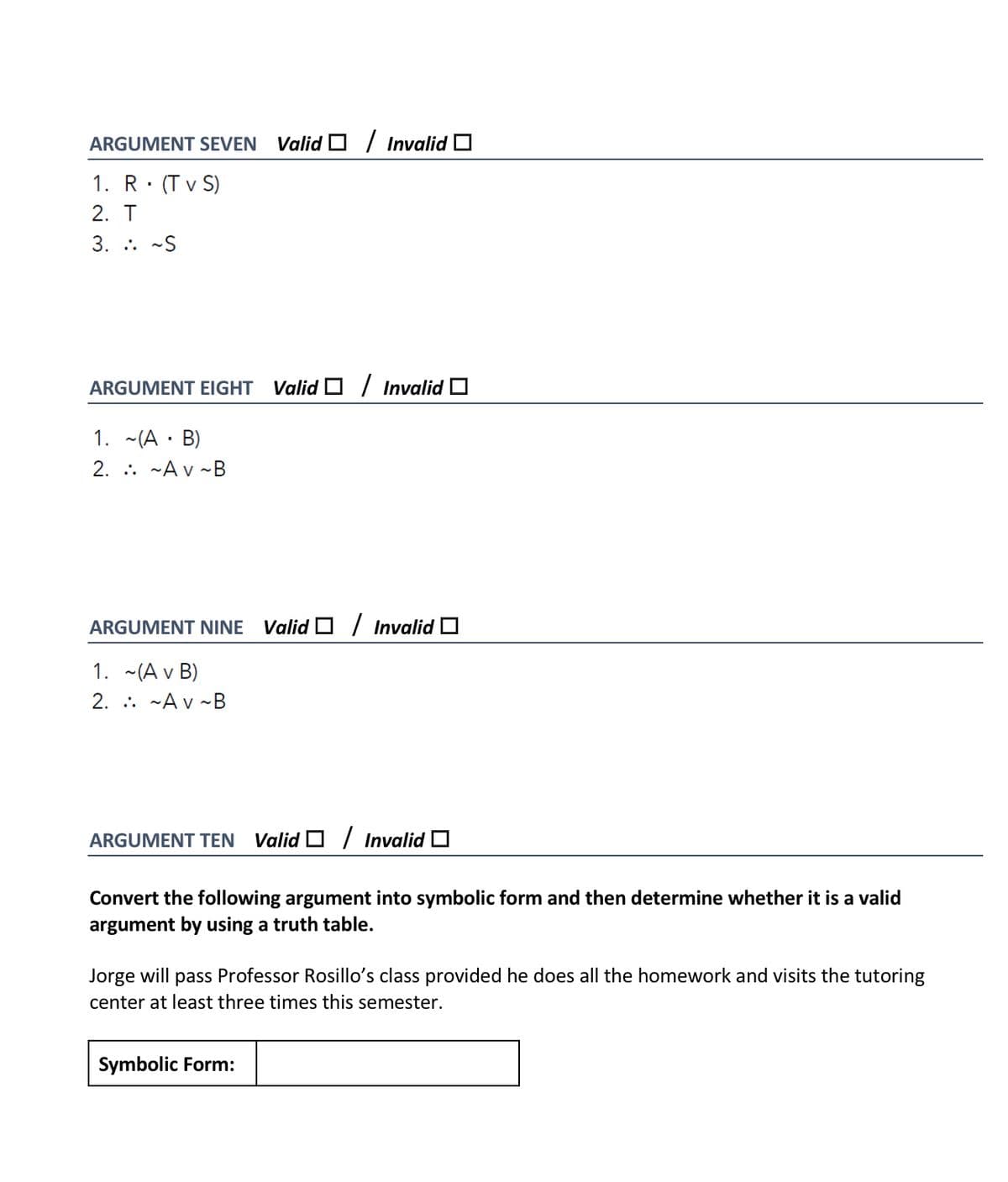
ARGUMENT SEVEN Valid D / Invalid O 1. R (T v S) 2. T 3. .. -S ARGUMENT EIGHT Valid O / Invalid 0 1. ~(A · B) 2. :. -Av ~B ARGUMENT NINE Valid O / Invalid O 1. ~(A v B) 2. . -A v ~B
Q: Using Semaphore, there may be two processes that can execute the wait() and signal() on the same…
A: By using two atomic operations, Semaphores are used to critical section problems, as they are the…
Q: A micro instruction format has micro operation field which is divided into 2 subfields F1 and F2,…
A: Logic , if there are n micro- operation then we can represent it in form of 2n where n will…
Q: What is the difference between a variable value model and a variable reference model? Why is it…
A: Model of Variables: Each variable in the Reference model of variables refers to a memory object;…
Q: what is the minimum number of nodes in a complete binary tree of 8?
A:
Q: Consider the following five instances of graph theory's use in artificial intelligence.
A: Problem Analysis : 5 specific examples in which graph theory is used in AI : Structure Learning…
Q: T Under server security, you can create additional Server Roles. T. In simple recovery model, no…
A: answer is given in next step:
Q: What are the main reasons for using a VPN?
A: Introduction When people hear the term "virtual private network," they usually think of something…
Q: Question 6 What are the possible count outcomes of this pseudo-code: Given count=6 Thread 1(...) {…
A: correct value of count in question 6 is 6 since in last counter stores value of register2 so…
Q: Assume you're going to create a computer to meet your working needs, since it's becoming more of a…
A: Characteristics: The explicit inclusion of user input, iteration, and the application of particular…
Q: Create a database named KCAU. create a table inside KCAU called students, fields should include…
A: Introduction: We can create a database using mysql. Download and Install Mysql. After completing all…
Q: Describe the file handle in detail.
A: Introduction: The file handling procedure refers to how we use a software to save the accessible…
Q: Using the Plan-Do-Check-Act cycle, we discovered a computer hack and a purpose solution.
A: Plan do check is a model used for continuous business improvement. It is also known as deeming…
Q: Computer science What is a computerized decision-making?
A: Introduction: With constantly rising data and machine capabilities, computerised decision making is…
Q: Short answer Computer networking What are the advantages and disadvantages of using gateway on…
A: Introduction: In reality, a network is made up of several devices that connect with one another.
Q: Short answer Only theory Explain in detail the features of pandas library file in Python.
A: Introduction: Python is, in fact, the most user-friendly programming language. It's a programming…
Q: What are the benefits of using a table in a database? write a brief remark regarding the value NULL?
A: Answer. Some advantages of Table in databases are listed below: By using the table, we can easily…
Q: What are the two arguments that you supply to a TryParse method when you are writing code?
A: Justification: If your string is an integer, it returns True otherwise, it returns False. int. There…
Q: A cybersecurity expert discovers several users with administrative rights during a security review.…
A: Please refer to the following step for the complete solution to the problem above.
Q: Discuss the various approaches that can be used in content-based recommendation and in each case,…
A:
Q: Create a python code that calculates which asks what amount of cake in grams from the user. Then…
A: The input will be the amount of cake in grams and the output is the sugar, chocolate and flour…
Q: What exactly is an array? What is the purpose of it?
A: Array: An array is a set of objects stored at memory locations that are contiguous. The aim is to…
Q: Why does the order in which an operator's or function's arguments are evaluated in most languages…
A: The operator precedence and associativity rules by which mathematical expressions are evaluated are…
Q: What are the three generations of advancement in wireless security that have taken place throughout…
A: Introduction: Since the early 1990s, wireless security methods have evolved to provide both…
Q: what are the benefits of 2G,3G and 4G and their relevance in telecommunications
A: Telecommunication Telecommunication is the transmission of data(information) by different types of…
Q: Take your favorite iterative algorithm and demonstrate its correctness. Hint. You may want to find…
A: Algorithm to compute xy. function Pow(x, y) prod = 1 p = 0 while p < y do…
Q: Ensure that the network, security, and virus protection software are up to date. How will you…
A: Auto maintenance and auto updates are used to install latest updates and patches and to optimized…
Q: Explain why professional software generated for a client is not merely the programmes that have been…
A: Start: Professional software must adhere to particular industry standards in order to be used and…
Q: Write the output of the following code: mister_pet = Pet("Master", "Dog") mister_dog =…
A: According to the information given:- We have to find out the output of the mentioned code. In order…
Q: Explain briefly why the advancement of 5th generation cellular telephony is necessary due to social…
A: Because of the configuration of the wireless networks in which mobile phones run, mobile telephony…
Q: Write a C++ program that asks the user for a file name and a word for which to search. The program…
A: Please find the C++ Program which is made easier to implement the above mentioned functionalities:-…
Q: Write an application that throws and catches an ArithmeticException when you attempt to take the…
A: Use an if-else block and if the input number is negative then throw an ArithmeticException This will…
Q: Differentiate and compare accuracy, reproducibility, and repeatability. Describe a situation where…
A: Introduction Bland and Altman, researchers, presented repeatability drills. For repeatability to be…
Q: which manager in a business is responsible for systems risks and privacy risks
A: System risk can be defined as the risk of breaking down of the complete system and not just the…
Q: Define the phrases "managed code" and "unmanaged code."
A: Managed code: It is executed by the common language runtime. All the security issues are handled by…
Q: For the following NFA M. 1 start 90 q2 From the list below, select all computations of M on the…
A:
Q: What are the benefits of paging?
A: Introduction: Paging is a type of memory storage that allows sections of processes to be recovered…
Q: What exactly do you mean when you say "computer applications for business"? What is the difference…
A: Computer and different computer applications are used by the business in their day-to-day life.…
Q: How does the MMU perform this mapping using the page table?
A: Memory management unit : A memory management unit (MMU), sometimes known as a paged memory…
Q: Explain the cycle of instruction execution in simple terms.
A: The instruction cycle (otherwise called the get interpret execute cycle, or basically the bring…
Q: Discuss how attackers may be able to exploit your system as a massively distributed attack platform.
A: Justification: A distributed denial-of-service (DDoS) attack is a malicious effort to interrupt a…
Q: What is an IP address and what role does it play in a computer network system?
A: Introduction: A computer's internet protocol (IP) address allows it to send and receive data over…
Q: What is the SCSI (small computer system interface)? What role does it play in providing interface to…
A: Standard parallel bus interface for connecting peripheral devices to a PC It can connect up to 16…
Q: Select the function that is ?theta(nlogn) . a. 5n + 17logn b. 6nlogn + n^1.1 + 2 c. 23nloglogn +…
A:
Q: In Symbian, Android, and iPhone, what impact has the file deletion algorithm had?
A: Given: In Symbian, Android, and iPhone, what impact has the file deletion algorithm had?
Q: what is the advantage and disadvantage of overloading operators? ( please tell in simple language…
A: Solution : Operator Overloading Operator overloading occurs when an operator operates on a…
Q: In Symbian, Android, and iPhone, what impact has the file deletion algorithm had?
A: Introduction Deletion algorithms are a set of rules and instructions, or a formula, for erasing…
Q: Write a Java program that implements both Linear Search and Binary Search. The program will take a…
A: So let here we start writing the complete java code and inside the code, I also provide the comments…
Q: What services does the transport layer provide?
A: Introduction The network consist of several layers that aid in the communication . Each layer is…
Q: When does a string of characters become a collection of tokens?
A: Hey there, I am writing the required solution based on the above-given question. Please find the…
Q: Compile a comparison study of at least four of the many search engines that we have available for…
A: There are many search engines available over the internet, however some of them become very popular…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- 30 Suppose a, b, and sum are int variables and c is a double variable. What value is assigned to each variable after each statement executes? Suppose a = 6, b = 3, and c = 2.2. (14) a b c sum sum = static_cast<int>(a + b + c); __ __ __ __ b += c * a; __ __ __ __ c -= a; __ __ __ __ a *= 2 * b - c; __ __ __ __(1) Prompt the user for a string that contains two strings separated by a comma. (1 pt) Examples of strings that can be accepted: Jill, Allen Jill , Allen Jill,Allen Ex: Enter input string:Jill, Allen (2) Print an error message if the input string does not contain a comma. Continue to prompt until a valid string is entered. Note: If the input contains a comma, then assume that the input also contains two strings. (2 pts)Ex: Enter input string:Jill AllenError: No comma in string. Enter input string:Jill, Allen (3) Extract the two words from the input string and remove any spaces. Store the strings in two separate variables and output the strings. (2 pts)Ex: Enter input string:Jill, AllenFirst word: JillSecond word: Allen (4) Using a loop, extend the program to handle multiple lines of input. Continue until the user enters q to quit. (2 pts)Ex: Enter input string: Jill, Allen First word: Jill Second word: Allen Enter input string: Golden , Monkey First word: Golden Second word:…Need help having code going past 21 hours on 24-hour clock and changing over to AM after 00:00! Thanks in advance #include <iostream>#include <ctime>//Had trouble with the variable localtime#pragma warning(disable : 4996) using namespace std; time_t now = time(0);tm* local = localtime(&now); int hour = local -> tm_hour;int minutes = local -> tm_min;int sec = local -> tm_sec; // Function to display the 12-hour clockvoid Clock12() { // Converts 24-hour clock to 12-hour if (hour > 12) { hour -= 12; } cout << "*****************************" << " " << "*****************************\n"; cout << "* 12-Hour Clock *" << " " << "* 24-Hour Clock *\n"; cout << "* " << (hour < 10 ? "0" : "") << hour << ":" << (minutes < 10 ? "0" : "") << minutes << ":" << (sec < 10 ? "0" : "") << sec <<…
- Assume the followingString s,t,h,a,n,e;int i;h = “Hello”;s = “How are you?”a = “abc”;n = null;e = “”;Give the values of the following expressions, or illegal1. h.length()2. h.substring(1)3. h.toUpperCase()4. h.toUpperCase().toLowerCase()5. h.indexOf("H")6. h.startsWith("ell")7. "Tomorrow".indexOf("o")8. "Tomorrow".indexOf("o", 3)9. "Tomorrow".lastIndexOf('o')10. "a = \"" + a + "\""11. (a.length() + a).startsWith("a")12. a.length() + a.startsWith("a")13. ">>>" + a.length() + a.startsWith("a")14. a.substring(1,3).equals("bc")15. a.substring(1,3) == "bc"16. "a".compareTo("c")17.…8. Write a program that allows the user to enter two integers and a character If the character is A, add the two integers If it is S, subtract the second integer from the first if it is M, multiply the integers Display the results of the arithmetic The following problems requires nested if-statements9. Write a console-based application that asks a user to enter an IQ score. If the score is a number less than 0 or greater than 200, issue an error message; otherwise, issue an “above average”, “average”, or “below average” message for scores over, at, or under 100, respectively.10. Write a console-based program that prompts a user for an hourly pay rate. If the user enters values less than $7.50 or greater than $49.99, prompt the user again. If the user enters an invalid value again, display an appropriate error message. If the user enters a valid value on either the first or second attempt, display the pay rate as well as the weekly rate, which is calculated as 40 times the hourly rate.…int a = 9; int c = 6; int d = 6; boolean m; if (a==c && c != d) { m = true}; What is the value of m? True False 6 9
- 2.15 LAB: Musical note frequencies On a piano, a key has a frequency, say f0. Each higher key (black or white) has a frequency of f0 * rn, where n is the distance (number of keys) from that key, and r is 2(1/12). Given an initial key frequency, output that frequency and the next 4 higher key frequencies. Output each floating-point value with two digits after the decimal point, which can be achieved as follows:print(f'{your_value1:.2f} {your_value2:.2f} {your_value3:.2f} {your_value4:.2f} {your_value5:.2f}')Print "user_num1 is negative." if user_num1 is less than 0. End with newline. Assign user_num2 with 1 if user_num2 is greater than 12. Otherwise, print "user_num2 is less than or equal to 12.". End with newline. My code: user_num1 = int(input())user_num2 = int(input()) if user_num1 < 0: print("user_num1 is negative.") if user_num2 > 12: user_num2 == 1 else: print("user_num2 is less than or equal to 12.") print('user_num2 is', user_num2) When the input is 0 and 13 my output for user_num2 is 13 and it should be 1. I don't know what I'm doing wrong.If, A = {3, 5, 7, 9} B = {2, 4, 6, 8, 10} C = {12, 14, 18, 20, 24} D = {21, 26, 31, 36} A. State whether TRUE or False: 1. 13 ∈ C 2. 6 ∉ A 3. 31 ∈ D 4. 20 ∉ B B. Fill in the blanks to make each statement true: 5.) 3 ∈ ___ 6.) 4 ___ B 7.) 26 ___ C 8.) 8 ∈ ___
- In Chapter 4, you created a program that generates a random number, allows a user to guess it, and displays a message indicating whether the guess is too low, too high, or correct. Now, create a modified program called GuessingGame2 in which the user can continue to enter values until the correct guess is made. After the user guesses correctly, display the number of guesses made. Recall that you can generate a random number whose value is at least min and less than max using the following statements: Random ranNumber = new Random(); int randomNumber; randomNumber = ranNumber.Next(min, max);If int x = 10;, int y = 7;, double z = 4.5;, and double w = 2.5;, evaluate each of the following statements, if possible. If it is not possible, state the reason. (3, 4) (x + y) % x x % y + w (z - y) / w (y + z) % x (x % y) * z x % y % 2 (x + y) % z (x % y + z) / wAssuming the following code: int x = myfunction1(); /* arbitrary value */ int y = myfunction2(); /* arbitrary value */ int z = myfunction3(); /* arbitrary value */ //convert to double double dx = (double) x; double dy = (double) y; double dz = (double) z; unsigned ux = x; unsigned uy = y; The following statement always evaluates to 1 (True or False): (dx + dy) + dz == dx + (dy + dz) True False





