arrange frupts priority 4 3 2 1 RST 7.5 RST 5.5 TRAP INTR RST 6 5
Q: What kind of security system does an IDPS resemble the most? In what respects do these two systems…
A: DPSes purpose as identifying problems with security policies, documenting existing threats and…
Q: a TM Transducer that outputs the following: a. Given the input x ε {1}^+, the TM outputs xx. Use the…
A: It is defined as a 7-tuple (Q, T, B, ∑, δ, q0, F) where: Q : It is a finite set of states T: It is…
Q: List FIVE (5) elements of symmetric encryption scheme.
A: Let us see the five elements of symmetric encryption.
Q: Discuss the link between processes and threads, and how a process is formed in Windows
A: Processes require more time for context switching as they are more heavy. Threads require less time…
Q: Explain ISA (Instruction Set Architecture), Types of ISA (Instruction Set Architecture), R-type,…
A: An Instruction Set Architecture (ISA): An Instruction Set Architecture (ISA) is a component of a…
Q: It's more typical to use multithreading than to have a large number of processes operating in the…
A: Foundation: Within a single process, many threads may be generated, each running independently yet…
Q: a. How many subnets are there in this network?
A: The answer is
Q: Wireless networks face a range of issues because of their intrinsic properties.. Explain how each of…
A: Wireless network: The computer network that are not connected by using cables is called as wireless…
Q: Select one: is a variable supplied to a different module. a. variable b. constant c. global variable…
A: Variable - Variable is the name given to computer memory locations which are used to store value in…
Q: The tree pointer is the first node of the binary tree and has both data and two reference links.…
A: The first node of the tree is called the root.
Q: List and discuss ten worldwide computer science and information technology organizations.
A: Information Technology/Computer Science: In general, computer science is concerned with the design…
Q: What are the benefits and drawbacks of Array?
A: An array is a linear datastructure which can be used to store elements of same datatype in a…
Q: What does it mean to develop an operating system in layers? What are the benefits and drawbacks of…
A: Introduction: It is possible to divide the operating system into layers. Several levels of…
Q: Explain the differences between a monolithic kernel and a microkernel approach to operating system…
A: Monolithic Kernel: This is a sort of operating system architecture in which the complete operating…
Q: What kind of security system does an DPS resemble the most? In what respects do these two systems…
A: Foundation: IDPS technologies use a lot of different ways to look for attacks. The main types of…
Q: What are the criteria for selecting an appropriate SPI approach for the company and project context?…
A: Software Process Improvement (SPI) methodology defines the sequence of actions, tools, and…
Q: ow to use a multidimension
A: Below how to use a multidimensional array
Q: Is Scheme's define primitive an imperative language feature, or is it only a convenience? What's the…
A: Define the term "primitive": It has the primitive type of special form, with the Define is the…
Q: Make a function that determines if a triangle is equilateral, scalene, or isosceles given the length…
A: ANSWER:-
Q: Are there any situations when user-level threads are preferable than kernel-level ones? User-level…
A: Start: It's easier and faster to make user-level threads than it is to make kernel-level threads.…
Q: Question 5 With reference to 8086 Microprocessors Pin Assignment: 1) State the three groups of…
A: The 8086 signals can be categorised in three groups. The first are the signals having common…
Q: If we dont have a lot of data to work with, which model is well suited for that? A. Bootstrap…
A: Lets see the solution.
Q: The following C program requests four string from the user, sorts the four strings alphabetically…
A: #include<stdio.h>#include<string.h>int main(){ int i,j,count; char…
Q: Find the minimum for this list of numbers 65 90 2 3 99 71 64 14 69 28 70 7 9 19 47
A: #include <bits/stdc++.h>using namespace std; int getMin(int arr[], int n){ int res =…
Q: Write a program using do-while loop that: Asks the user to enter a number between 0 and 99…
A: I give the code in Java along with output and code screenshot
Q: Examine the parallels and contrasts between Big Data and classic marketing research ideas.
A: Explanation: Traditional marketing and big dataBigdataBig data is described as a large volume of…
Q: I need help with the following question. Also a visual representation using a Compiler to illustrate…
A: As we know array is a collection of elements of homogeneous datatypes, here an array of doubles is…
Q: What language does the following regular expression represent? Assume the alphabet is {0,1}. a. R3 =…
A: We will generate language here step by step-1. (0+1) - Either 0 or 1 generated strings are either-…
Q: What are the criteria for selecting an appropriate SPI approach for the company and project context?…
A: SPI HAS THE FOLLOWING ADVANTAGES: The primary benefit of employing the SPI is its ease of…
Q: User-level and kernel-level threads differ in what ways? What are the circumstances in which one…
A: Start: User-created threads include: Users are the ones who implement user threads.User threads are…
Q: The following is a list of recent research papers that use machine learning methods.
A: Given: Thousands of research articles on Machine Learning are published each year in prestigious…
Q: Describe the distinction between a traditional database and a data warehouse
A: answer is
Q: What kind of security system does an IDPS resemble the most? In what respects do these two systems…
A: The goal of DPSs is to uncover faults with security policies, document existing threats, and…
Q: w about a rundown of the many types of programming paradigms? Then, why is it that there are so many…
A: Lets see the solution.
Q: A cipher suite is a choice of algorithms for key exchange, authentication and encryption to be used…
A: Save time, costs and maximise site performance with: Instant help from WordPress hosting experts,…
Q: How can an interactive system be designed to be user-friendly? Give an example to ilustrate your…
A: Please find the answer below :
Q: What are the implications for computer scientists of learning Boolean algebra?
A: Intro: Boolean algebra is important for computer scientists because it is a key tool for…
Q: In computer science, what does it mean to "widen conversion" mean?
A: Given Question: What does "widen conversion" mean in the field of computer science?
Q: 4. - Consider the following RISC-V assembly instructions: addi x11, х0, 10 addi x2, x0, 1 addi x3,…
A:
Q: Explain four elements that your organisation should evaluate before (or during) computer hardware…
A: Purchasing computer hardware is an investment, and as such, it should be done with caution.
Q: What are some characteristics of TCP? Reliable Less overhead than UDP Congestion control…
A: TCP is reliable Protocol. so, First Option is CORRECT. TCP has less overhead than UDP . so, Second…
Q: Knowing that we have many multiplexers (MUX) in our processor, how do we figure out which input to…
A: multiplexers in processor
Q: I need a solution to this question quickly -Given the following search tree, apply the Expected…
A: Answer
Q: Explain the differences between network edge, core, access, and physical media.
A: Network Edge: Clients and servers make up the host. Servers are also often seen in data centers. Web…
Q: Explain what a network operating system's fundamental functions are.
A: Generally operating systems with networking abilities were depicted as network operating systems,…
Q: Compare and contrast the scheduling of processes and threads.
A: Given: A process is a dynamic, live programme. Among other things, it contains the programme…
Q: da int noofElements; float avg; public: // define necessary getter and setter method (s) // define…
A: main.cpp #include <iostream> using namespace std; class Array { int *dataPtr; // stores…
Q: What are the benefits and cons of using self-driving cars?
A: Pros of self-Driven cars: Vehicle Collisions Have Decreased The vast majority of car accidents are…
Q: he operating system's data structure has a significant impact on the management
A: Lets see the solution.
Q: Find the 16-bit computer representation of -753.
A: 1. Start with the positive version of the number: |-753| = 753 2. Divide the number repeatedly by 2:…
Step by step
Solved in 3 steps with 1 images

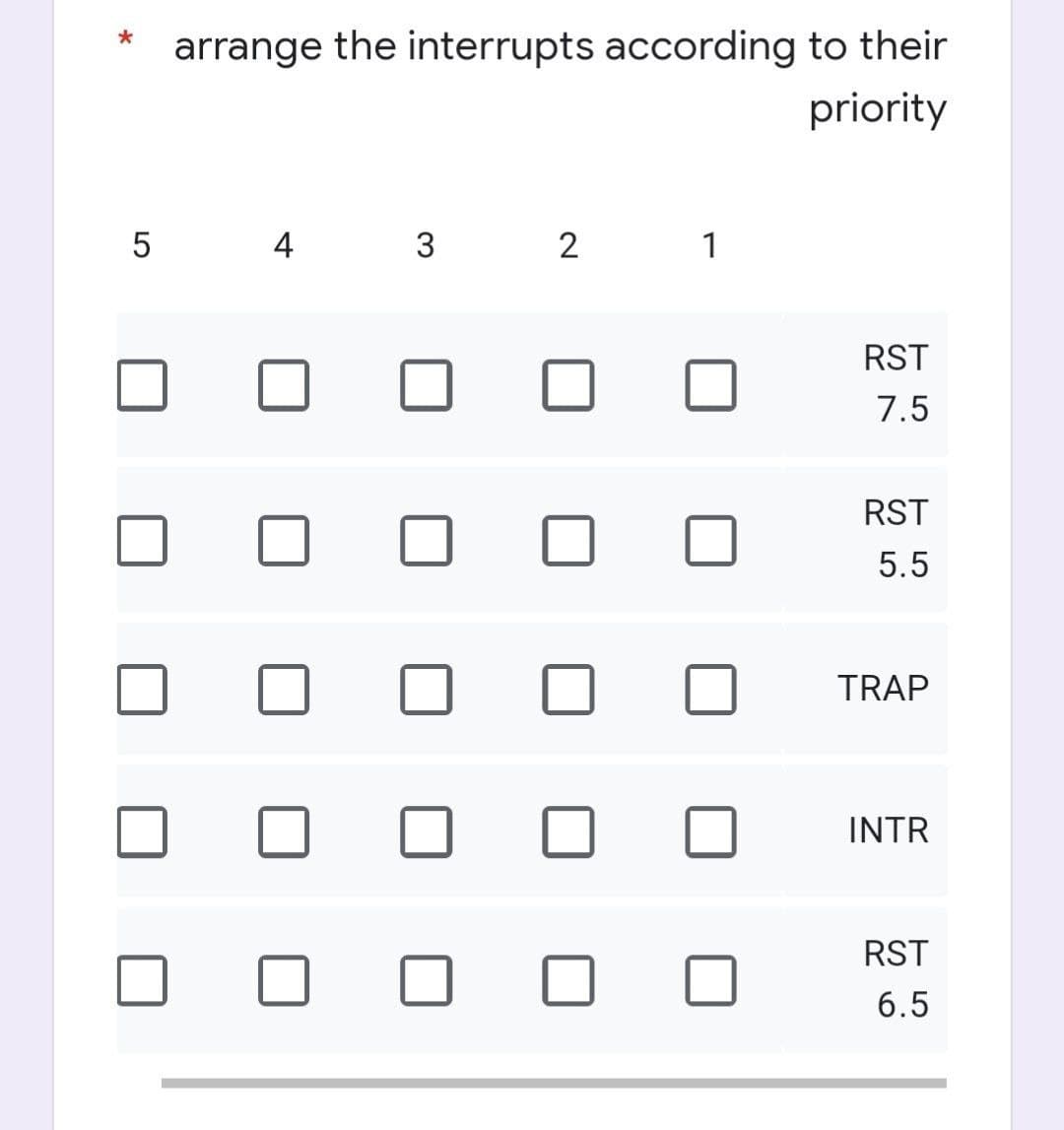
- 6 Non - Masking: interrupt with priority lower than current priority is not recognized until pending interrupt is complete.? الاجابات True FalseThis article provides an explanation of interrupt latency and context switching time.Different kinds of Interrupts need different responses. Find out which Interrupt events occurred first, last, and in the middle of the sequence.
- The FIQ interrupt methods are required to establish a connection and succession at the designated offset within the Interrupt Vector Table. It.?What does it imply if interrupt latency determines how long it takes to switch contexts?When hooking and chaining FIQ interrupt operations, you need to employ an offset called an Interrupt Vector Table (IVT). It.?
- What precisely is interrupt latency, and how does it relate to the time it takes to switch between contexts?When a signal is received, the processor pauses what it's doing to respond to the request. The mechanism used in this case is as follows: A' Signal of Interrupt Spooling B C' Handling of interruptions. D Polling.The concepts of interrupt latency and context switching time are broken down into its constituent elements during the course of this article.



