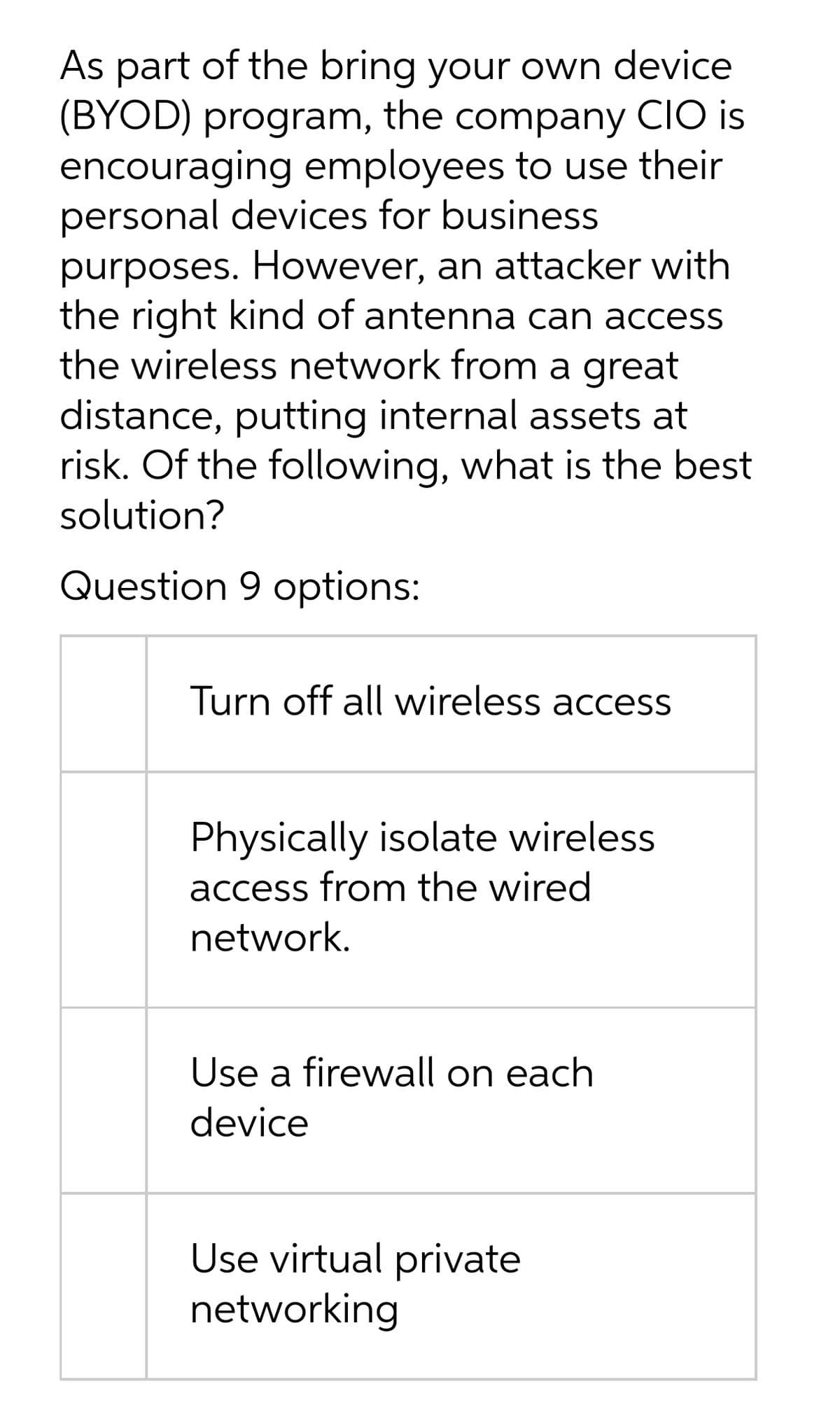
As part of the bring your own device (BYOD) program, the company CIO is encouraging employees to use their personal devices for business purposes. However, an attacker with the right kind of antenna can access the wireless network from a great distance, putting internal assets at risk. Of the following, what is the best solution? Question 9 options: Turn off all wireless access Physically isolate wireless access from the wired network. Use a firewall on each device Use virtual private networking
As part of the bring your own device (BYOD) program, the company CIO is encouraging employees to use their personal devices for business purposes. However, an attacker with the right kind of antenna can access the wireless network from a great distance, putting internal assets at risk. Of the following, what is the best solution? Question 9 options: Turn off all wireless access Physically isolate wireless access from the wired network. Use a firewall on each device Use virtual private networking
Chapter7: Microsoft Edge
Section: Chapter Questions
Problem 3EYK
Related questions
Question
DO NOT COPY FROM OTHER WEBSITES
UPVOTE GUARENTEED
Transcribed Image Text:As part of the bring your own device
(BYOD) program, the company CIO is
encouraging employees to use their
personal devices for business
purposes. However, an attacker with
the right kind of antenna can access
the wireless network from a great
distance, putting internal assets at
risk. Of the following, what is the best
solution?
Question 9 options:
Turn off all wireless access
Physically isolate wireless
access from the wired
network.
Use a firewall on each
device
Use virtual private
networking
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage