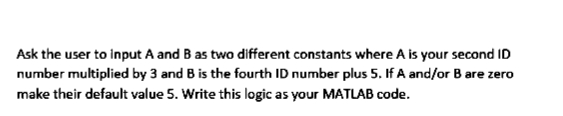
Ask the user to input A and B as two different constants where A is your second ID number multiplied by 3 and B is the fourth ID number plus 5. If A and/or B are zero make their default value 5. Write this logic as your MATLAB code.
Q: Please describe how a company can prevent hackers from accessing its accounts and defining hacks and…
A: Introduction: Here we are required to explain how a company can prevent hackers from accessing its…
Q: Write a program that plays a guessing game with the user. The program should generate a random…
A: Required code for the Java program is given in the next step using a while loop for continuous…
Q: Justify the role of traffic analysis in network defense and cybersecurity.
A: Explanation: Justify the relevance of traffic analysis as a critical component of network defence…
Q: 23. For the following code what will be the output: def thing(): print (Hello') print (There) a.…
A: def things(): print('Hello') print('There') Answer: c. There
Q: 1. The causal sequence x(n) in z- transform means the limited of summation taken from n= -o0 to n= 0…
A: Answer : False In case of causal sequence x(n) in z - transform limited of summation taken from n=0…
Q: If a "WORM" assault is used against a content delivery network, what are the ramifications? What can…
A: Define: A computers a piece of code that may propagate from one framework to another. An infection…
Q: What measures should be followed to assure the stability and availability of a local area network?
A:
Q: Explain the importance of firewalls in network security and cybersecurity. Explain the term and…
A: Definition: We must describe the importance of network scanning and evaluation as a crucial activity…
Q: In digital certificates, the sender and the recipient are distinct parties. Do you know how to…
A: Given: What is the distinction between the sender and the digital certificate holder? How can you…
Q: xactly does it sig
A: identyfing strong nodes on complex organization is trying because of the huge data and organization…
Q: Apex Assignment: Create a apex class called addition and then create a method to add the 2 integer…
A: As per the question statement, We need to create the addition class having add method which does…
Q: Assume there are three small caches, each consisting of four one word blocks. One cache is fully…
A: Assume there are three small caches, each consisting of four one word blocks. One cache isfully…
Q: So, what exactly is data mining? What are some data mining jobs you can think of?
A: Given: The work of a data mining expert is analysing information in order to discover links, trends,…
Q: Discussion and overview about Division algorithm in the use of Computer Architecture
A: Introduction: Here we are required to explain about Division algorithm in the use of Computer…
Q: What can a corporation do to avoid being hacked or infected?
A: Solution: In order to obtain sensitive information about your corporation while also protecting your…
Q: QUESTION 2 What is the Complexity (Big O) of the following function? 4n2 + 123n²logn +100000…
A: The answer to the following question:-
Q: code in Java Write a spring boot project with jpa(Java) for association of one-to-one,…
A: It is defined as a high level, robust, object-oriented and secure programming language. It can be…
Q: Put another way, what does wavelength division multiplexing do?
A: Wavelength division multiplexing (WDM): Wavelength division multiplexing (WDM) is a technique for…
Q: 24. What will the following code print out def func(x): print (x) func (10) func (20) b. func 10 d.…
A: Python is a very famous programming language these days, It is an Object oriented programming,…
Q: What's the difference between scripting languages and programming languages, exactly?
A: Scripting Languages and Programming Languages: A programming language is a sort of computer language…
Q: What is the purpose of forensic software in investigations, and how does it provide specific…
A: Answer:
Q: 2. First Even Road by CodeChum Admin I've been newly assigned as the city's road planner but this…
A: Logic:- read number of rows, columns iterate from i=0 to i<rows Iterate from j=0 to…
Q: What measures should be followed to assure the stability and availability of a local area network?
A:
Q: What Makes up a Computer System's Components? Give a short summary of what you're trying to achieve.
A: DRAM: DRAM is a kind of semiconductor memory that stores data or programme code needed by a…
Q: How will the Internet of Things (IoT) affect us? Give an example of a smart device or app.
A: Answer: The Internet of Things is still in its early stages as a peculiarity. Notwithstanding this,…
Q: (c) The memory structure in a microcontroler is represented in figure 1-2. Explain why "Register" is…
A: Flash Flash is basically an Erasable Read Only Memory(EROM). Flash is a type of non-volatile memory…
Q: Which approach of elicitation was utilized to collect the functional requirements for the…
A: Solution is given below :
Q: What role do Digital Certificates and Certificate Agencies play in PKI?
A: PKI: PKI (or Public Key Infrastructure) is the encryption and cybersecurity architecture that…
Q: Write a complete interactive program that displays the alphabet on the canvas. • Each time the user…
A: ANSWER:-
Q: on, what is the dif
A: Solution - In the given question, we have to find the difference between Symmetric and Asymmetric…
Q: Wireless networks are prone to flaws that cause issues. Describe three of these concerns and their…
A: Security issues include protecting data from unauthorized access and viruses. For a Wireless…
Q: What precisely is "Big Data"? What differentiates big data from traditional data?
A: Big Data entails: Big data refers to a large amount of data that grows rapidly over time. This…
Q: With the use of authentication, which of our objectives can we achieve? What are the advantages and…
A: List the advantages and disadvantages of different authentication systems. Advantages: For big…
Q: Exactly what are the aims of the verification process? Do you know the pros and downsides of…
A: Verification Process: Authentication is the process of ascertaining whether someone or something is…
Q: What is the conceptual framework when it comes to cybercrime? Please provide sources in your…
A: Introduction: According to internet theorists, cyberspace provides for near-instant connections…
Q: Make a python code with this flowchart
A: # import sqlite3 import sqlite3 import csv import os # create a new database if the database…
Q: Common Multiple (LCM) to schedule? lability of these tasks using RMS and confirm whether or 1 e the…
A:
Q: The SNMP management primitives and protocol message structure may be explained in what way??
A: SNMP is also known as Simple Network Management Protocol.
Q: What is the purpose of authentication? Is it possible to compare and contrast the advantages and…
A: Start: Authentication is the process of identifying users who want to access a system, network, or…
Q: III. The figure below shows synchronous TDM, the data rate for each input connection is 1 Mbps. If 1…
A:
Q: Describe how the three characteristics of big data apply to the data collected by healthcare…
A: Given that, Describe the relationship between the three characteristics of big data and the data…
Q: What is the connection between firewalls and traffic analysis and alert?
A: - We must discuss the link between Traffic Analysis and Traffic Alert, as well as firewalls. -…
Q: ication serve a specific purpose? What are the advant
A: Below are the advantages and disadvantages of different authentication methods
Q: Scripting vs. programming languages: what's the difference?
A: Scripting languages convert high-level instructions into machine language.
Q: What are the applications of subneting?
A: Subnetting - Subnetting is basically doing partitioning of a network into two or more networks. The…
Q: In order to get a digital certificate for a single public key, how do you keep the private key…
A: The fact that RSA is a trapdoor permutation means that you are not required to reveal the private…
Q: What are three (3) computer crime remedial measures?
A: Computer crime: Cyber crime is the term used to refer to computer-related crimes. Cyber crime is…
Q: Face-to-face classes have been suspended in Hong Kong due to the coronavirus outbreak, forcing…
A: Define: Due to the coronavirus pandemic, students in Hong Kong must study through cloud computing.…
Q: Network sniffing and wiretapping seem to be connected in your mind. They're passive risks, so what…
A: Sniffers for network sniffing: Sniffers examine data packet streams that pass between computers on a…
Q: Determine the present network's advantages and drawbacks.
A: Introduction: A network is a collection of independent distributed systems that exchange and…
Step by step
Solved in 3 steps with 1 images

- Which logical operators perform short-circuit evaluation? A. or, and B. not, and C. or, not D. and, or, notWhich of the following logic expression represent the logic diagram. For the following logic expressions, create a corresponding truth table. Note that some terms in the logic expression may map to more than one place in the truth table. Note: The Boolean expression may need to be modified do to missing letters. Now that you understand the mechanics of converting from a truth table to a logic expression (and vice-versa), let’s look at a problem that begins with some written specifications. Your new car has an audio alarm that buzzes whenever the door is open and the key is in the ignition or when the key is in the ignition and the seatbelt is not buckled. Using the following variable names and assignment conditions, complete the truth table shown below that captures the functionality of this audio alarm. · D: Door → 0=Door Open / 1=Door Close · K: Key → 0=Key Not in Ignition / 1=Key in Ignition · S: Seat → 0=Not Buckled / 1=Buckled · B:…
- Using the switch, case, · · · , otherwise control structure, write a MATLAB program for calculating individual taxes.Using MATLAB or Octave Prompt the user to enter a positive, non zero number. If the user entered a positive , non-zero number, display " thank you ". If they enter a negative number, display " The number you entered is negative, please try again " .What value is displayed for total at the end of this logic? Write your answer as an integer.
- Assume you have two INTEGER type variables a and b in your Matlab Workspace and the following expression to be executed: >> (not(mod(a, 2) == 1)) & (sqrt(a) ~= sqrt(b)) Which pair of variables a and b values will cause this expression to be evaluated to true? a = 4 and b = 3 a = 0 and b = 0 a = 4 and b = 4 a = -4 and b = -4write a java program with its logic that will accept the radius as input,will calculate the area of circle and display the answer on screen. show usage of functionIn this problem, you are asked to write a single MATLAB code that displays the value for 100*π in a few different formats

