assembly language
Q: Thank you but it does not the lemgth of the string. I want the out as len(aabbaa)
A: #Modified the code, so that it outputs, the length of the returned string : len(aabbaa)
Q: Find out how other businesses handle their information and the tactics they utilize.
A: Introduction: - Business has several information some of them are very much confidential, so they…
Q: Think about the key distinctions between a firewall and a data flow that is packetized.
A: Introduction: The best response is selection 1. Crucial Points to Bear in Mind By providing a route…
Q: Search for Linux-ready computers from major manufacturers. How about operating system support—does…
A: Major computer manufacturers such as Dell, HP, Lenovo, and Acer offer a range of computers that can…
Q: Why do some database managers dislike denormalization?
A: A strategy for optimizing databases known as denormalization involves the addition of duplicate data…
Q: What are the most recent advancements in technology that have been made in the fields of information…
A: Dear Student, The most recent advancements in technology that have been made in the fields of…
Q: Draw the "internal" view of memory for each step of the following code sequence: ArrayBndQueue q =…
A: Dear learner, hope you are doing well. I will try my best to answer this question. Thank You!!
Q: Provide some reasons why companies have begun utilizing cloud computing.
A: A corporate strategy known as cloud adoption tries to reduce costs and risks while increasing the…
Q: Is it an issue that there are so many distinct kinds of computer networks at work? How do we go…
A: Dear Student, The detailed answer to your question with required explanation is given below -
Q: What is the value of g and p for a standard size AOI gate that implements: (ABC + DEF)’? Write the…
A: The term "AOI" stands for "AND-OR-Invert" gate, which means that the gate has two stages: first, an…
Q: How to input the following code # Open the input file and read the dictionary with…
A: The solution is given in the below step I am using OnlineGDB to run the code
Q: What exactly is IP spoofing, and how does it function? If that's the case, how exactly does it…
A: Introduction Hackers may get access to computers using spoofing in order to mine them for sensitive…
Q: For what reasons is the World Wide Web held up as a paragon of modern ICT? There has to be proof and…
A: According to the information given:- We have to define the World Wide Web held up as a paragon of…
Q: How can wireless Internet contribute to the development of cyber police?
A: Wireless Internet can contribute to the development of cyber police in several ways, as it provides…
Q: How crucial is software development? Four more characteristics, in your opinion, should be…
A: Introduction: Software development's ability to create and provide value to its users cannot be…
Q: Data structures such as arrays, lists, stacks, queues, and trees are all examples of abstractions;…
A: Data structures are meaningful collections of data components. Data structures organise computer…
Q: Complete the following arithmetic operations in two's complement representation. What are the values…
A: Given that, 9 + (-19) = ? We are using six bit system, that means each number is represented in 6…
Q: Is there anything special about the internet that makes it a great illustration of ICT? Be sure to…
A: Dear Student, The detailed answer to your question with required explanation is given below -
Q: What percentage do you think the internet is a great example of ICT?? There has to be proof and…
A: The internet is a prime example of Information and Communications Technology (ICT). ICT refers to…
Q: Certain databases may not make advantage of the magnetic disks' interior tracks because they prefer…
A: Radis is short for "frequently used identical key." Within a partition as a hot spot key. Hot spots…
Q: What's the best approach to store users' backup data? Assess the cost of implementation, as well as…
A: We have to explain the best approach to store users' backup data? Assess the cost of implementation,…
Q: What are some of the newest technological developments in the field of information technology?
A: Dear Student, Some of the newest technological developments in the field of information technology…
Q: Output "Fruit" if the value of userltem is a type of fruit. Otherwise, if the value of userltem is a…
A: Below is the complete solution with explanation in detail for the given question in Java Programming…
Q: For the incremental development of a software product with a team of seven to nine individuals…
A: IntroductionDeveloping a software product involves a significant amount of effort and coordination…
Q: Popular methods for mining images and texts include computer vision, face recognition, and sentiment…
A: Robotic eyeballs Information extraction from digital pictures is the primary focus of computer…
Q: how to draw a physical level 0 data flow diagram of a syste
A: Drawing a physical level 0 data flow diagram (DFD) requires identifying the main external entities…
Q: In what ways has the internet of things evolved, and what are some of the novel applications that…
A: The Internet of things (IoT) depicts genuine products (or groups of such articles) with sensors,…
Q: Craps is a classic casino game in which players bet on the outcome of rolling 2 six dice (2d6).…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: When it comes to the structure and regular operations of a business, what role does cloud computing…
A: We have to explain When it comes to the structure and regular operations of a business, what role…
Q: What do you know about VMware's cloud services?
A: Virtual machines are what VMware provides. By the use of a virtual machine, we are able to install a…
Q: What measures should be followed to assure the stability and availability of a local area network?
A: Introduction: In computing, a local area network (LAN) collects small computers or other…
Q: Transfer Infix regular expression (a*.b| (a.b)*) into Postfix regular expression, '.' is catenation.
A: To convert the infix regular expression (a*.b|(a.b)*) into postfix notation, we can use the Shunting…
Q: It's possible that you'd be interested in learning about the most widely used applications for…
A: A host software firewall is a kind of firewall that is installed on a single computer that filters…
Q: Staff mployee_number: Integer sition: String 0. + id: Integer Airport Person +fullname: String…
A: Here we can see the sequence diagram for the Airport structure. Airport has airline. Airport need…
Q: In what ways are mobile applications unique?
A: The following are the distinguishing characteristics of a mobile app: It is essential to find out…
Q: How do I write a c++ code on microchip studio to control an ADC 0808 with an atmega328p to light up…
A: To control an ADC 0808 with an ATmega328P microcontroller and light up 8 LEDs connected to the ADC…
Q: Does cloud computing really fix all of a business' IT issues?
A: Dear Student, The detailed answer to your question with required explanation is given below -
Q: Describe the motivations for the recent increase in cloud computing use by enterprises
A: The term "cloud computing" describes the Internet-based distribution of computing resources…
Q: What is Onion network?
A: Here is your answer....
Q: You are free to pursue more education on the metrics that are used throughout the software…
A: Introduction The software development process is an intricate process that requires a lot of metrics…
Q: To be more specific, what exactly are the deliverables for the software development project?
A: IntroductionSoftware development projects encompass a wide range of tasks and processes. The…
Q: What is the key distinction between direct DDoS attacks and reflector/amplifier assaults?
A: The key distinction between direct DDoS (Distributed Denial of Service) attacks and…
Q: What steps can you take as the administrator of your system to make sure that your data is kept…
A: Information that has been transformed into a more efficient form for movement or processing is…
Q: Why do so many people think the internet is the most cutting-edge medium of communication and…
A: Yes, that's correct to say that the internet is the most cutting-edge (most recent) medium of…
Q: Get expert knowledge on cloud computing and social networkin
A: In this question we have to understand cloud computing and social networking Let's understand and…
Q: IEEE 754-2008 contains a half precision that is only 16 bits wide. The leftmost bit is still the…
A: The IEEE 754-2008 floating point format is a standardized representation of floating point numbers…
Q: Describe virtual memory in detail.
A: Virtual memory is described below with explanation
Q: A cybersecurity expert discovers several users with administrative rights during a security review.…
A: Introduction: A cybersecurity expert recently conducted a security review of a company’s system and…
Q: Internet technology is one of the best examples of ICT since... Detailed examples and explanations…
A: Explanation: Why is the internet among the best examples of ICT? Each point should be backed up with…
Q: question 1 . PMI has been shown to be very sensitive to window size. Suggest reasons why this model…
A: Language models like BEAGLE and Pointwise Mutual Information (PMI) rely on a predetermined window of…
Please solve for the following in assembly language MASM (x86 porcessors) (Please use visual studio for this)
Step by step
Solved in 2 steps with 1 images

- Write a program named GuessingGame that generates a random number between 1 and 10. (In other words, in the example above, min is 1 and max is 11.) Ask a user to guess the random number, then display the random number and a message indicating whether the users guess was too high, too low, or correct.Write a program that prompts the user to enter apoint (x, y) and checks whether the point is within the circle centered at (0, 0) withradius 10. For example, (4, 5) is inside the circle and (9, 9) is outside the circle, asshown in Figure (Hint: A point is in the circle if its distance to (0, 0) is less than or equal to 10.The formula for computing the distance is __________________√(x2 - x1)2 + (y2 - y1)2. Test your program to cover all cases.) Two sample runs are shown below: Enter a point with two coordinates: 4 5 ↵EnterPoint (4.0, 5.0) is in the circleSuppose you have a thermometer in a lab that displays temperaturesin Fahrenheit. You would like to convert the reading into Celsius andconnect a digital screen to display a message. If the temperature is 40 o Cor more, the screen would display “hot temperature”, between 39 o C and30 o C would display “warm temperature”, between 29 o C and 11 o C woulddisplay “good temperature”, and anything from 10 o C or lower would display“Winter is here…”. Write a program in python that would get the unit converter anddisplay screen working.
- Write a VB.net program that will ask the user to input your favorite color, and display it as Your favorite color (inputted color)Write a program that prompts the user to enter a sequence of numbers until a -999 is entered. It will print the numbers the user entered, five number in a row,with a before the first number and after the last number in each row. For example, Enter a number (-999 to stop): 23Enter a number (-999 to stop): 15Enter a number (-999 to stop): 1Enter a number (-999 to stop): 7Enter a number (-999 to stop): 9Enter a number (-999 to stop): 21Enter a number (-999 to stop): 17Enter a number (-999 to stop): 33Enter a number (-999 to stop): -999[23 15.17 9] [21 17 33]Write a program that generates a random number in the range from 1 through 100 After generating the random number, the user is to guess the number. If the user’s guess is higher than the random number, the program should display “Too high, try again” If user’s guess is lower than the random number, the program should display “Too low, try again”. If the user guesses the number, the program should congratulate the user and then generate a NEW random number so the game can start over. Make the game menu driven with these options Main Menu ______________ 1)Play Game 2)Exit written in python
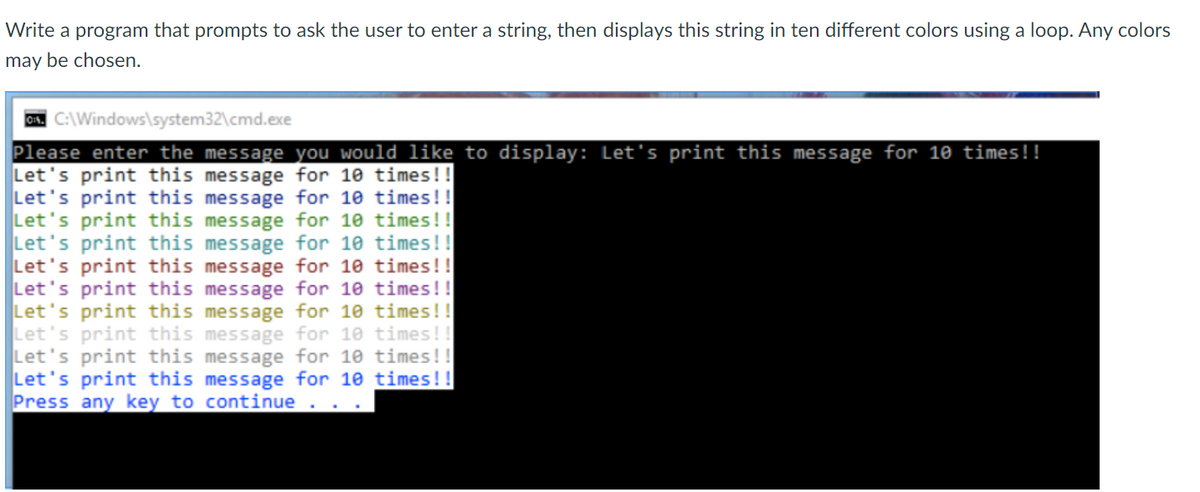
- Write a program that prompts a user to enter a year between 1 and 2499 and prints its century in the format such as 1st, 2nd, 3rd, 4th, etc. please use a switch statement. for what we have done in class so far we have only used #include <iostream> <fstream> <cmath> <string> <iomanip>, so if possible if this can be done using that so I can understand for my next assignment that would be great thanks! Test Run 1:Enter a year between 1 and 2499 -- 19231923 is in the 20th century Test Run 2:Enter a year between 1 and 2499 -- 22022202 is in the 23rd century Test Run 3:Enter a year between 1 and 2499 -- 2630Wrong year!Write a program that gets a string from the user and reports whether or not there are repeated characters in it based on the following program. loop ask the user to input one of the characters a, b, c, d, e, q read in a character from the keyboard if the character is'a' output your name and your tutor's name (hard-coded)'b' input 3 double numbers x, y, z and output the largestand the smallest of the three numbers'c' input 2 integer numbers m and n, and display all thenumbers between m and n (both inclusive) with fivenumbers per line (note that the last line may have lessthan 5 numbers). At the end, display the sum of all theodd numbers between m and n (both inclusive)'d' input 3 integer numbers representing the sides of atriangle and display the numbers together with amessage indicating whether or not the numbers form atriangle (Note: for the numbers to form a triangle, thesum of any two sides must be greater than the thirdside)'e' input an integer number n and determine whether or…Write a program that randomly chooses between three different colors for displaying text on the screen. Use a loop to display twenty lines of text, each with a randomly chosen color. The probabilities for each color are to be as follows: white = 30%, blue = 10%, green = 60%. Hint: generate a random integer between 0 and 9. If the resulting integer is in the range 0-2, choose white. If the integer equals 3, choose blue. If the integer is in the range 4-9, choose green.
- Write a program that prompts the user to enter threepoints, (x1, y1), (x2, y2), and (x3, y3), of a triangle then displays its area.The formula for computing the area of a triangle iss = (side1 + side2 + side3)/2; _________________________________ area = √s(s - side1)(s - side2)(s - side3)Here is a sample run: Enter the coordinates of three points separated by spaceslike x1 y1 x2 y2 x3 y3: 1.5 -3.4 4.6 5 9.5 -3.4 ↵EnterThe area of the triangle is 33.6Write a program that reads the user's first name and last name, and then use them to create a UPM email for the user. If the total number of characters in the user's full name, (first name + last name), is less than 10 letters, you should use the full name to create the user’s email. The general format of the user’s email should look like this: firstName.lastName@upm.edu.sa For example: First name = Ali Last name = Omar Total number of letters in both first and last names = 7 letters (<10 letters) Output = omar.ali@upm.edu.sa If the number of characters in the user's full name, (first name + last name), is greater than or equal to 10 letters, you should only use the first character in the user’s first name, and the whole last name to create an email. For example: First name = Abdullah Last name = Omar Total number of letters in both first and last names = 12 letters (>=10 letters) Output = a.omar@upm.edu.sa Note: you can assume the user will always enter lowercase lettersWrite a program that prompts the user to enter two primary colors as strings: “red”, “green”, or “blue”. Once entered, the program outputs the resulting secondary color. The program should be designed to respond to invalid colors or duplicate colors such as blue mixed with blue.

