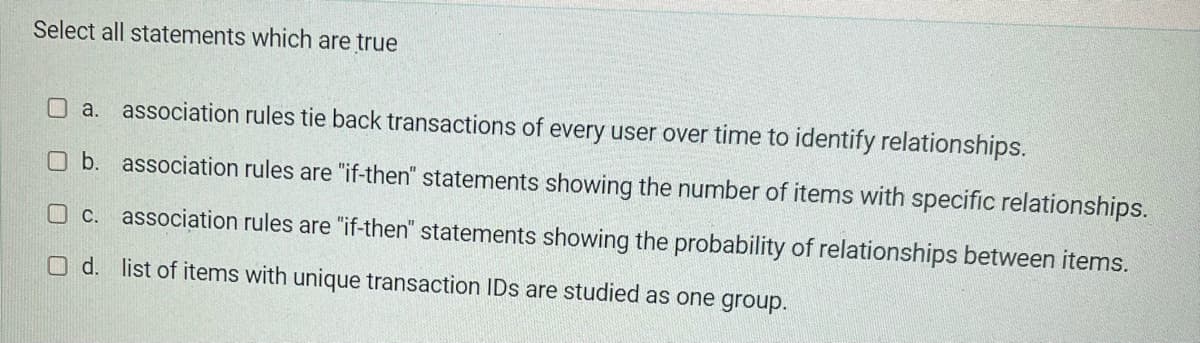
association rules
Q: Concurrent chunks of a file are attempted to be saved on successive drives. Is there a reason why…
A: Given: Magnetic discs are quite important. An operating system's file system ensures that each file…
Q: Take into consideration the benefits as well as the drawbacks of using wireless technology. At a…
A: Launch: This high-speed solution is used to transfer information quickly or develop secure social…
Q: Black box testing procedures like as stress and volume testing have been taught to you by your…
A: Given: Performance testing is a software testing process used to determine the speed, response time,…
Q: Is it necessary to emphasize the need of data backup in organizations while emphasizing the…
A: Is it necessary to emphasize the need of data backup in organizations while emphasizing the…
Q: Is it possible to encrypt the connection as well as the data from beginning to end? What benefit…
A: Introduction: Link encryption is a type of communication authentication in which all data at both…
Q: Examine the use of information systems in a variety of different companies and businesses.
A: Functional Information System depends ont thedifferent business capacities, for example, Production,…
Q: Problem 2. Given the following linear programming problem: max 2x1 + x₂ + 4x3 s.t. ₁4x2x3 ≥ 2 -…
A: Answer a) Figure:
Q: When it comes to Information and Communication Technology, the internet is one of the best examples.…
A: Information and Communication Technology: Internet is an excellent instrument for social movements.…
Q: Explain the four P's of effective software project management with appropriate examples?
A: Introduction: Effective software project management depends on the following four factors: 1.…
Q: 24. TCP provides the following services a. reliable data transfer b. flow control c. congestion…
A: Here 2 MCQs Related to TCP is given, Provide answers in detail below.
Q: T began as a method to connect devices, and what are some of th
A: Introduction of IoT began as a method to connect devices.
Q: The internal tracks of magnetic disks may be left unused by certain databases, which utilise only…
A: It is not uncommon for us to come across hot spots when working with a database with many users.…
Q: When it comes to the use of computers, what are the primary distinctions between the use of…
A: Design of the building: Architecture design is the process of combining physical components to…
Q: 15. Image derivative information of grayscale. And. edge and other abrupt information, and gradual…
A: 15. Image derivative enhances edge and other abrupt information, and gives gradual information of…
Q: How exactly can you use netstat to determine whether or not you have been infected?
A: The netstat can be denoted as a command-line network utility that prints network connections for…
Q: 9x11 Z=1- X3 5X7 + 32 7² - ·+... 112 Write the code program so that the value of (X) is entered into…
A: Form Design :
Q: Develop a deep grasp of social networking blogs and cloud computing.
A: In addition to storing data, social networks are increasingly performing a variety of additional…
Q: Explain the difference between class system and a case system?
A: Introduction: The term "social stratification" refers to the "organization of any social group or…
Q: First Name: Juan Carlo Middle Name: Romero Last Name: Dela Cruz Character Details: Name: Juan Carlo…
A: The above question is solved in step 2 :-
Q: Wireless networks are plagued by errors, which may lead to catastrophic outcomes. There are three of…
A: Introduction: "With all of these findings, I realize it may look that we're merely bringing concerns…
Q: As a consequence of ICT, what extra advantages and downsides have we experienced?
A: Given: Information and Communications Technology. Innovative apparatuses and properties…
Q: You may wonder why it's so important for business. What actions should be taken before starting a…
A: Software quality: Software quality is defined as a discipline of study and practise that identifies…
Q: Throughout the whole of this session, an in-depth conversation will be held on the significance of…
A: Architecture fills in as an outline for a framework. It gives a reflection to deal with the…
Q: What are the many components of a computerised system made up of? Include a brief explanation if…
A: Intro Five key components make up a computer system. On the motherboard, CPU spasms SSD or HDD…
Q: When it comes to technology, why is the internet considered to be one of the finest examples? Give…
A: The acronym "ICT" refers to - information and communication technology. When you visit a website,…
Q: What precisely is meant by the term "virtual drive"? When does it occur, and how does it take place?…
A: Given: [6/2/2022, 2:15] shaikmabula163: Virtual drive question. A virtual drive emulates an optical,…
Q: When and where did the concept of the internet of things first emerge, and what applications can it…
A: The "Internet of Things"- (IoT) is a network of devices connected to the cloud. This network is…
Q: What function does architecture serve within the larger context of society? In order to get a…
A: Start: As is common knowledge, the process of translating strategic requirements to architectural…
Q: When it comes to technology, what distinguishes architectural design from computer-based…
A: Answer to the given question: In 3D PC illustrations, 3D demonstrating is the most common way of…
Q: Help me find the value/s of x and y using R programming. a = 17.5 b = 12
A: As per the question statement, We need to find values of x and y.
Q: A computer-based organization is distinct from architectural design in that computers, rather than…
A: Computer architecture: Computer architecture is a functional description of section needs and design…
Q: So that we can do what, everyone in the software development team should be involved in the planning…
A: Given: The process through which computer programmers generate new computer programmers is known as…
Q: Wireless networks bring with them a whole host of issues that need to be resolved before they can be…
A: Wireless network: In a "wireless network," it is a computer network that uses wireless data…
Q: "Is it risky to utilise the Referential Integrity Constraint with the Cascading option for the…
A: Intro Encryption: Constraints are a crucial component of a relational model. In reality, the…
Q: When it comes to technology, architecture and organization based on computers are two quite distinct…
A: Start: Architectural designThe process of putting together a computer system is known as…
Q: What are the major differences between the ARM and Core i3 architectures?
A: The above question is answered in step 2 :-
Q: Identify the several design models that we use throughout the analysis phase of the software…
A: Software development: Software development include the creation, design, implementation, and…
Q: What's wrong, if anything, with the following code? class Kitchen { private: double kit_sq_ft;…
A: We need to find the problem(s) with the given code.
Q: Under what conditions will the compiler supply a definition of the default constructor?
A: Answer the above question are as follows
Q: What exactly is the difference between cloud storage and backup when it comes to the realm of online…
A: Cloud capacity is characterized by IBM as a: "[service] that permits you to save information and…
Q: Think about the wide area network (WAN) wireless connection technique you choose. Why is this choice…
A: Encryption: A wide area network, or WAN, is a communication network that may span a large…
Q: For workers that work remotely or wirelessly, what type of network configuration would you…
A: Introduction: Computing devices that are linked together and can exchange data and resources. A…
Q: This section covers the most pressing information technology issues and the best techniques for…
A: Problems of Information Technology: Information technology difficulties are recurrent technological…
Q: Throughout the course of this presentation, you will get an understanding of the significance of…
A: Software architects must: Software architecture is vital for all stakeholders' understanding,…
Q: Define what is meant by the Principle of Information Hiding, and briefly describe why it is so…
A: Information hiding is one of the basic principles in Object-oriented Programming (OOP); the main…
Q: As a consequence of ICT, what extra advantages and downsides have we experienced?
A: Encryption: Information and Communications Technology. Innovative apparatuses and properties…
Q: How can cloud computing assist you? Cloud computing poses a threat or hazard to users in what ways?…
A: It is perhaps the most prevalent hazard to cloud computing that data leaks or data loss occurs due…
Q: Name: Be Anne Nickname: Reese Phone: +63298612345 Fav Film: Doctor Strange Hobby: Collecting Stamps…
A: Answer:
Q: In this section, a concise explanation need to be provided for the two functions of an operating…
A: operating system: The term "operating system" refers to the software that enables a computer to…
Q: Both wireless access points and bridges belong to separate categories of technology.
A: Launch: such that wireless access points and wireless bridges may be distinguished from one another.…
Step by step
Solved in 2 steps

- Which of the followings describe the relationship between “super key” and “candidate key”?(a) A super key is also a candidate key.(b) A Super key K is a candidate key, if K is minimal(c) A candidate key K is a super key, if K is minimal(d) A candidate key is also a super keyWhat precisely do you mean when you say that a dependence is transitive?Please do not give solution in image formate thanku Following 4 questions are based on the transactions listed as follows Transaction 1: Bread, MilkTransaction 2:Bread, Diapers, Beer, MilkTransaction 3:Milk, Diapers, Beer 1. List all item combinations and their support (in percent) 2.List all possible rules (in the form {X} -> {Y} meaning if set {X} is purchased then set {Y} is also purchased) and their confidence. Note that {X} -> {Y} and {Y} -> {X} are two different rules. 3.What is the lift ratio for the rule {Beer} -> {Diaper}? Briefly interpret it. 4.What is the lift ratio for the rule {Beer} -> {Milk}? Briefly interpret it
- if you have three conditions, and the condition is true, do you need to evaluate the second OR conditions? (Yes or No)? WhyPlease answer with reason for all why the option is correct and why the other options are incorrectPlease answer correct otherwise skip it A calculated field in the normalisation process requires special treatment. Which of the following is correct? If the borrowing duration is fixed in a library, either of the date-borrowed or the due-date can be kept but not both. If both DOB (Date of Birth) and Age information are available, we will keep the Age information as it is more useful. We can keep either the Starting Time or the Ending Time of a match in a data table regardless of whether the match has a fixed duration or not. None of the other answers are correct.In what circumstances is it acceptable to say that two select statements chosen from the same table both satisfy with the prerequisites that have been set by the union?
- Suppose you are given the following description of a discount policy: An insurance company has a policy of discounting its product to customers under certain circumstances: Discounts of 5% are given only if the customer has excellent credit If the customer has filed less than one claim in the last five years add a discount of 10% If the customer insured multiple products (home, car, boat) etc subtract 4% Represent this situation as a decision table Represent the situation above as a decision tree.Suppose half of all the transactions in a clothes shop purchase jeans, and onethird of all transactions in the shop purchase T-shirts. Suppose also that half of the transactions that purchase jeans also purchase T-shirts. Write down all the (nontrivial) association rules you can deduce from the above information, giving support and confidence of each rule.please help me with question 9 fill all alphabatic latters a to o wiht steps by step to undestand how value came please
- Question 02: Write five examples of each of the following from real life also draw UML of each example.1. Association2. Aggregation3. CompositionSend me correct and original answer from your knowledge but if you'll copy the i'll mark multiple dislikesQ1: All the following statements about weak and strong entity sets are True, Except: Select one: a. The weak entity set depends on the existence of the strong entity set b. PK of the strong entity set is not explicitly stored with the weak entity set c. An entity set that does not have a primary key is referred to as a weak entity set d. In ER-Diagram, the identifying relationship of a weak entity in represented as a double diamond e. The PK of the weak entity set is only formed by the primary key of the strong entity set Below are two pictures, each with a second and third question

