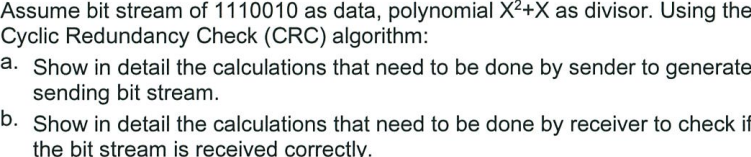
Assume bit stream of 1110010 as data, polynomial X²+X as divisor. Using the Cyclic Redundancy Check (CRC) algorithm: a. Show in detail the calculations that need to be done by sender to generate sending bit stream. b. Show in detail the calculations that need to be done by receiver to check if the bit stream is received correctly.
Q: Thanks to multitasking, switching between different programmes is a breeze. Can I use this computer…
A: Hello student Greetings Multitasking is a feature that allows users to switch between different…
Q: Does the current state of internet safety make it appropriate for children under the age of 16? Is…
A: In today's cardinal age, internet safety is a fundamental concern that raises concerns, particularly…
Q: What technological features set software engineering apart from its counterparts in the engineering…
A: Software engineering stands out as a distinct discipline within the broader field of engineering due…
Q: There are a variety of approaches to evaluate and contrast various back-end compiler architectures.
A: The backside end of a compiler refers to the phase that takes the halfway representation (IR) of the…
Q: Before a programme is run, space in memory (also called address space) is allocated to store its…
A: In computer programming, memory allocation plays a crucial role in executing programs efficiently.…
Q: Modern computers pack quite a punch. Why did the use of computers in classrooms suddenly explode?
A: Modern computers, with their powerful processing abilities and vast range of applications, have…
Q: Just like electricity, the CPU's clock speed cannot be changed after it has been printed. What, if…
A: 1) Contrary to the statement, the clock speed of a CPU can indeed be changed while the system is…
Q: What metrics are used to evaluate a network's efficiency, and how are they applied?
A: Network efficiency is a critical limit in evaluating a computer network's recital. The metrics used…
Q: To what end is the database secured by a foreign key? Why does this matter?
A: A database is secured by a foreign key primarily to maintain data integrity and enforce referential…
Q: Is it acceptable, in your opinion, for app creators to ask for personal details from users before…
A: In app development, asking for personal details from users can be a nuanced topic. Officially, it's…
Q: Know the importance of database backups. Recovering The next step is to examine the current state of…
A: Database backups are a critical aspect of data management and protection. They play a vital role in…
Q: In RSA, given that the primes p and q are approximately the same size, approximately how big is (n)…
A: RSA (Rivest-Shamir-Adleman) is a widely used asymmetric encryption algorithm in cryptography. RSA…
Q: Computer Science Selection sort Algorithm (Assembly language - masm in 32 bits) Write a program…
A: Sorting algorithms play a crucial role in organizing data efficiently. One commonly used algorithm…
Q: Get people talking about the potential benefits of using mobile devices in the workplace, such as…
A: In workplaces, mobile devices such as smartphones and tablets offers many benefits that helps to…
Q: When a computer malfunctions, how do you go about fixing it? To what means do you resort in order to…
A: What is Information: Information refers to knowledge or data that is communicated, received, or…
Q: Get people talking about the potential benefits of using mobile devices in the workplace, such as…
A: Given the widespread use of these devices in today's culture, it should not surprise that more…
Q: Part I Create a Student class that implements Comparable interface from java.lang.Comparable.…
A: Sure! Here's the solution for Part I, creating a Student class that implements the Comparable…
Q: Which kind of bus between the central processing unit and the memory should we use? Should we choose…
A: Random Access Memory (RAM) Is a form of computer data storage that stores data and machine code…
Q: Both registers and random-access memory (RAM) fall within the category of memory.
A: Registers and RAM are both forms of reminiscence critical to a computer process. While they have a…
Q: Justify the need for database access control over flat-file methods. How do DBMSs control the…
A: The era of big data has accentuated the importance of effective data management. Flat-file methods,…
Q: When compared to competing IDEs, what makes Compiler Phases so special? Explain your meaning in…
A: Compilers are instrumental in translating human-readable source code into machine-executable code.…
Q: When you state the parts of a process header that fall inside the brackets are "informally" ordered,…
A: When I mention that the parts of a process header inside the brackets are "informally" ordered, it…
Q: Can we obtain a rundown of the compiler and an explanation of the value of testability?
A: A compiler is a software program that translates source code written in a high-level programming…
Q: rogramme is run, space in memory (also called address space) is allocated to store its components…
A: In computer science, the process of executing a program involves multiple stages, from loading the…
Q: In what ways is the GSM MSC anchor helpful?
A: As a key element of the GSM network, the GSM MSC anchor is crucial in guaranteeing the effectiveness…
Q: Networked computers When many senders seek to share the same medium, a data collision occurs. Where,…
A: Network impacts occur in a shared network nature when two or more devices go to transmit data…
Q: Assume that you are tasked with the job of writing a context-free grammar for Java variable…
A: A context-free grammar (CFG) is a formal notation used to describe the syntax of a language. It…
Q: Use TABLE 7 Logical Equivalences Involving Conditional Statements. For every of 9 statements prove…
A: Here is to ask to prove the correctness of each logical equivalence one by one.
Q: Do you think app developers should get permission to release their product to the public before…
A: Introduction: It is necessary to ask the personal information before making their product…
Q: When compared to competing IDEs, what makes Compiler Phases so special? Explain your meaning in…
A: When evaluating different Integrated Development Environments (IDEs), it is essential to consider…
Q: Justify your stance on the usage of informal software development approaches in domains such as…
A: The term "software development" describes a wide range of computer science disciplines concerned…
Q: # Reverse the order of elements in the list y [18, 5, 2, 4] print(y) Complete the code to return the…
A: I have used Python 3 for showing the correct answer for the given input and output conditions.
Q: A database crash is assumed. Write-through and deferred-write database recovery?
A: A database which refers to the one it is an organized collection of structured data that can be…
Q: What kinds of technological systems exist, and how have they developed over the last several…
A: Technological systems refer to devices and infrastructures that apply facts for practical point.…
Q: Defend the use of firewalls to secure networks. Give a description of the term and give some…
A: Firewalls are network security devices designed to protect networks from unauthorized access and…
Q: 37. What is the output of the following segment of code if 4 is input by the user when asked to…
A: Start the program. Declare variables num and total and set total to 0. Output the message "Enter…
Q: In software development, what are the three most important steps?
A: This is the initial phase of software development. The progress team workings in my opinion with the…
Q: Multiple relational database characteristics may be encrypted if security is implemented. There…
A: Relational databases are widely used for storing and managing structured data in various…
Q: Clients with little means really must use cloud-based database services. The software, hardware, and…
A: As more businesses use cloud-based database services, the requirement for data protection and…
Q: Know the importance of database backups. Recovering The next step is to examine the current state of…
A: Database backups are vital to protecting an organization's data. They arrange a safety net for…
Q: Immensely popular in embedded systems, why do microcontrollers rule?
A: Embedded systems rely profoundly on microcontrollers because they compress a lot of processing…
Q: What effect does the foreign key have on the security of the database? Why?
A: Foreign keys are critical to maintain the referential honesty of relational database. They create a…
Q: I'd want you to name the six most important reasons why it's important to learn about compilers.
A: Understanding compilers is critical to mounting a robust knowledge of how CPU system functions at a…
Q: What kind of Big O notation does database execution time fall into? Sure, I'll take care of it. If I…
A: The Big O notation is a mathematical notation used to describe the efficiency or complexity of…
Q: about the Primary indexes with a neat diagra
A: Describe about the Primary indexes with a neat diagram.
Q: To make the TAL Distributors database run more efficiently, the DBA denormalized part of the data,…
A: In relational databases, Third Normal Form (3NF) is a property of a relative that is convinced when…
Q: How do you compute and plot two confidence intervals in excel?
A: To compute and plot two confidence intervals in Excel, you can follow these steps:
Q: There are a variety of data storage mechanisms available in React Native. Discuss the merits of your…
A: React Native offers various options for storing data within mobile applications. These data storage…
Q: Modern, high-tech computers are to blame. How many classroom computers have been added over the last…
A: The proliferation of modern, high-tech computers has had a significant impact on the number of…
Q: The powers of modern computers are mind-boggling. Do computers have any precedent in shaping the…
A: Computers have had a profound impact on shaping the modern classroom and revolutionizing education…
Step by step
Solved in 4 steps

- 4-The following block is sent: 0110111 0101010 1101010 1010101. Using a 2-dimensional parity check, what will be received by the receiver without the block being corrupted in transmission. put a space after each frame (8 bits). your final answer shoule be 5 frames. 5-Given: Original message : 110101010; Generator: 1010 Perform a CRC Calculation: 6-The symbols M and N are transmitted. Show the transmission of this data (at the sender and receiver) using Checksum Method.2) Compute data sent for a bit stream of 101011 with CRC using a generator 1010 Randomly assume any bit to have been corrupted, Illustrate how the receiver can detect if the data was corrupted.Suppose Alice and Bob are going to communicate using AES in CBC mode. Unfortunately Alice's message length (in bytes) is not a multiple of 16. Suppose the last block of her message is just a single zero byte. How can she pad out the last block so that she can use CBC mode? Since this needs to be a reversible operation, how does Bob recognize the padding and remove it?
- q5- How the CRC (Cyclic Redundancy Check) checksum can be applied for detecting data transmission errors? Calculate 3-bit CRC checksum for a message string 11010011101 and show the steps involved. Use 1011 as divisor and show your working.Suppose the DES Mangler function mapped every 32-bit value to zero, regardless of the value of its input, what function would DES compute? Solve this question by answering the following 3 sub-questions. What is the result of each round? What is the result after the 16 rounds? Remind DES = Initial permutation + 16 rounds + swap halves + final permutation? Assume the original message is a 64-bit message, i.e., 1 2 3 4 … 64. Specify the bit positions by then end of these 4 operation. Must provide detailed explanation of the calculation steps.Suppose the DES Mangler function mapped every 32-bit value to zero, regardless of the value of its input, what function would DES compute? Solve this question by answering the following 3 sub-questions. What is the result of each round? What is the result after the 16 rounds? Remind DES = Initial permutation + 16 rounds + swap halves + final permutation? Assume the original message is a 64-bit message, i.e., 1 2 3 4 … 64. Specify the bit positions by then end of these 4 operation. Use 8x8 matrix for this. Must provide detailed explanation of the calculation steps.
- Computer Science With the CBC/OFB/CFB/CTR mode: (a) if there is a single bit transmission error in block C3 of the ciphertext, which plaintext blocks are affected? CBC and CTR (b) Suppose that there is a bit error in the source version of P1. Through how many ciphertext blocks is this error propagated? What is the effect at the receiver?Suppose that a binary message – either 0 or 1 – must be transmitted by wire from location Ato location B. However, the data sent over the wire are subject to a channel noise disturbance,so to reduce the possibility of error, the value 2 is sent over the wire when the message is1, and the value −2 is sent when the message is 0. If X, X = {−2,2}, is the value sent atlocation A, the value received at location B, denoted as R, is given byR = X + N ,where N is the channel noise disturbance, which is independent of X. When the message isreceived at location B, the receiver decodes it according to the following rule:if R ≥.5, then conclude that message 1 was sentif R < .5, then conclude that message 0 was sentAssuming that the channel noise, N, is a unit normal random variable and that the message0 or 1 is sent with equal probability, what is the probability that we conclude that the wrongmessage was sent? This is the probability of error for this communication channelGiven are the following codewords for an error control coding scheme data 000 011 100 codeword 00011000 00000111 10101000 . a.What is the minimum Hamming distance? b. What is the coding rate for this scheme? c. what raw data rate would be required if we need a throughput of 6 Mpbs? d. in a different situation, the number of data bits to transfer is 5, and the minimum hamming distance is dmin=5. find the maximum coding rate for this situation
- 4. Suppose we have to transmit a list of five 4 bit numbers that we need to send to a destination. Show the calculation using checksum method at the sender and receiver side if the set of numbers is ( 3, 7, 9, 11, 13).With the use of a Checksum Method, show the transmission of “m” and “n” from the sender to destination side. The following block is sent: 00001111 11110000 11001100 10101010. With the use of a two-dimensional parity check and assuming that no single/multiple-bit or burst error have occurred, what will be received in the receiver side? NOTE: Put a space after each frame.The following bit stream : 0111110001010011111111100101111111111110 represents data that needs to be framed by the link layer on the sender’s side. Derive the resultant bit stream by adding necessary flag bits and performing bits stuffing. assume that the link layer uses the flag bits with bit stuffing approach for framing, with the following details: The beginning and end of a data frame are indicated by the special flag bits 01111110 (i.e., 0x7E). To handle accidental occurrence of the flag bits within the data, a 0 bit is stuffed every time 5 consecutive 1s are found in the data. For simplicity, assume that no other header/trailer information is added to the data. I got this answer below but it is wrong. 0111111001111100001010011111011110010111110111111011001111110

