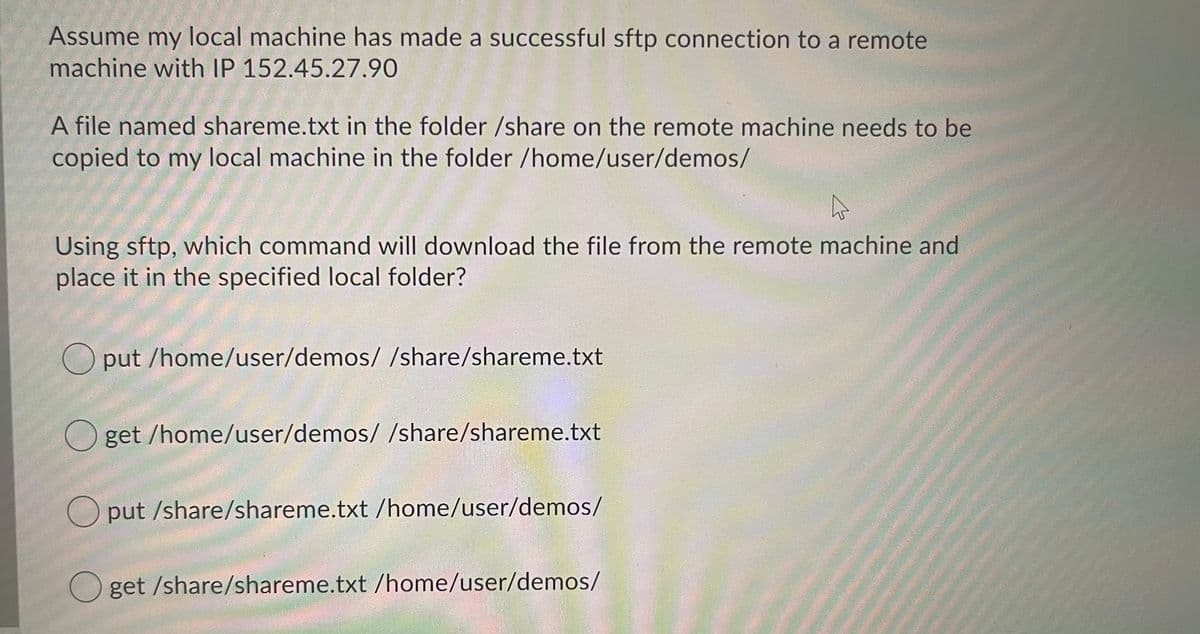
Assume my local machine has made a successful sftp connection to a remote machine with IP 152.45.27.90 A file named shareme.txt in the folder /share on the remote machine needs to be copied to my local machine in the folder /home/user/demos/ Using sftp, which command will download the file from the remote machine and place it in the specified local folder? O put /home/user/demos/ /share/shareme.txt
Q: If a word is defined as 16-bit and given a 64-bit data: 0xABCDEF1234567897 Least significant bit:…
A: Given HEX No - 0xABCDEF1234567897 Equivalent Binary - 1010 1011 1100 1101 1110 1111 0001 0010 0011…
Q: What is corporate data modeling and how does it work?
A: A data model is a summary and analytical model that organizes and standardizes relevant data items.…
Q: many bits would be wasted in the single block used for the inode bitmap on a VSFS-formatted disk…
A: It is defined as a virtual simple file system (VSFS) known as an abstract layer on top of a more…
Q: How secure was computers in its infancy in terms of security? Explain
A: Computer security, often known as cybersecurity, safeguards computer systems and information against…
Q: program will display the largest humber between 2 to 4 numbers. Use the UML diagram below as a…
A: Please refer below code and output: Language used is JAVA: import java.util.*;public class Main{…
Q: Write a program that checks matching words - First asks the user to enter 2 String variables word1…
A: Note: The program has been provided in Java. Java has two methods to compare strings.…
Q: Using two instances, describe the reason behind cryptography and the fundamental concepts of the…
A: Fundamental Concepts: In your mind's eye, a notion is a means of categorizing the universe. The…
Q: Give examples of how the three qualities of big data (volume, velocity, and diversity) relate to the…
A:
Q: Describe five devices that may be used to shift windows while using a laptop in detail.
A: The following is the answer: When using a laptop, there are a variety of devices that may be used to…
Q: Executive modules are components of the Windows operating system that are intended to perform…
A: Definition: The executive modules of the Windows operating system -Windows NT executive is a series…
Q: Obtain a DFA strings of 0's and 1's having exactly one 0.
A: HI THEREI AM ADDING ASNWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: What are some of the drawbacks of moving to an enterprise-level analytics solution for end users who…
A: Answer:- Benefits of moving to an enterprise-level analytics solution for enterprises and end users…
Q: Is it possible to restore damaged data using a backup?
A: Encryption: Backups are a frequent means of preventing or mitigating data loss. When we consider…
Q: Provide your thoughts on "time-variant" and "time-invariant" Data Base systems, as well as some…
A: Time Invariant Database Structures: If the properties of the inputs and outputs of a system do not…
Q: int i = 10; while (i >= 0) { System.out.println("Hi"); i--;
A:
Q: Write a C++ program that determines if an integer array is a palindrome. Declare two pointers to the…
A: Palindrome Palindrome is a number or word that can be read same from backward and forward direction.…
Q: What is system engineering for? In what ways can we use system engineering to enhance our results?…
A: Introduction System Engineering is a transdisciplinary and integrative way to deal with empower the…
Q: Discuss the many types of real-time scheduling methods available to the group for -he proiect
A: Mathematical analysis The Critical Path Method (CPM) and the Program Evaluation and Review Technique…
Q: What makes paperwork so crucial in a successful criminal investigation? List the bare minimum of…
A: The Importance of Documenting Criminal Investigation Procedures While a crime scene is handled,…
Q: List and briefly describe the several layers of methods by which the operating system treats a…
A: RAID- Redundant array of independent disks: It is a technology for storing data in numerous…
Q: Demonstrate the corresponding output for the given program. Give your analysis for results of the…
A: Explanation for logic:- A variable sum is assigned with 0 at the start. Then a loop is used for…
Q: What are some of the reasons why hacking websites is a serious problem?
A: Please find the detailed answer in the following steps.
Q: What are the four main reasons why people collaborate? Name and define them, as well as their…
A: Collaboration System - In this case, the computer system that is used by many or a lot of businesses…
Q: What is the structure of a telecommunications network?
A: Introduction: Most telecommunications networks include three key network components: a data plane, a…
Q: (b) When designing file systems, what are the practices that we should consider to avoid chaotic…
A: (b) when designing file systems, what are the practices that we should consider to avoid chaotic…
Q: let f is bijective and so is invertible. Describe the inverse function f-1 in your own words. What…
A: A function is invertible if and only if it is injective which means that it has an one-to-one, or…
Q: Make brief notes on the following topics: a. optical fiber b. satellite communication
A: Start: Satellite communications based on radio frequencies are already supplemented by optical…
Q: Describe five devices that may be used to shift windows while using a laptop in detail.
A: let us see the answer:- Introduction:- When using a laptop, there are a variety of gadgets that can…
Q: What is the requirement for storage in a computer?
A: Answer the above question are as follows:
Q: What efforts are made to reduce network traffic noise?
A: Given: Using earplugs to reduce noise pollution is a cost-effective approach. Earplugs can be used…
Q: Give examples of how the three qualities of big data (volume, velocity, and diversity) relate to the…
A: Big Data: Big data is a term that refers to a collection of data from several sources and is often…
Q: Lab Exercises: 1. Write a C++ program which reads a list of numbers from file numbers.txt, then…
A: Please take the number.txt file as per you in the code: #include <iostream>#include…
Q: write the differences between voice voders and wave coders .Give the names and proterties of the…
A: Speech coding Speech coding is a process of obtaining compressed form of speech signal. It allows…
Q: Is it strange that a little firm like Sunny Delight has so many analytics tools? How has Sunny…
A: Given: We have to discuss Is it strange that a little firm like Sunny Delight has so many…
Q: Consider the difference between pure ALOHA and slotted ALOHA under low load. Which is the smallest?…
A: Aloha is the Hawaiian word for love, affection, peace, compassion, and mercy. Although it is…
Q: Construct a DFA that accepts all strings from the language L = { string of size devisable by 6 }
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: Observing the minimart in your area, you've come to the conclusion that it stores its records on…
A: SQL LANGUAGE: SQL is a domain-specific programming language created for managing data included in a…
Q: Consider two strings A and B. Take string A as your First name and Last name without space…
A: Longest Common Subsequence can be defined as the longest subsequence is the common to the given…
Q: Describe five devices that may be used to shift windows while using a laptop in detail.
A: When using a laptop, one may use numerous devices to move windows; the following are some examples:…
Q: Discuss the many types of real-time scheduling methods available to the group for the project.
A: Some commonly used RTOS scheduling algorithms are: The planning framework's scheduling algorithm…
Q: Discuss the many types of real-time scheduling methods available to the group for the project.
A: The planning framework's scheduling algorithm describes how projects are prepared. Each undertaking…
Q: What is corporate data modeling and how does it work?
A: Data modeling: What is corporate data modelling and how does it work? Image result At many degrees…
Q: (a) Explain connection-oriented demultiplexing in the context of the transport layer. (b) What is…
A: DEMULTIPLEXING: The signals received at the demultiplexed nodes are split and sent to the…
Q: What is Database as a Service (Daas) and how does it work? What are the benefits and drawbacks of…
A: Database as a Service: A cloud computing service is database-as-a-service (DBaaS). Users do not need…
Q: In a workplace with shared resources like a printer, how do you handle security?
A: Security: Confidentiality, integrity, and availability are three fundamental security principles…
Q: Write a program to reverse the elements present in the queue. Make a reverseQueue() function. Use a…
A:
Q: Make brief notes on the following topics: a. optical fiber b. satelite communication
A: 1) An Optical fiber is a technology that transmits information as light pulses along a glass or…
Q: Briefly explain an embedded system and advise the group on embedded operating system design needs.
A: An Embedded Operating System: An embedded operating system (OS) is a customized operating system…
Q: Construct NFA for reguler expression (aab)* (aUaba)*
A: Here is the solution for this:
Q: write a pseudocode to the find the summation of this sequence: Sum = 1/N+1 + 2/N+2 + 3/N+3 + 4/N+4 +…
A: Pseudocode to the find the summation of this sequence: Input: Number of terms m Output: Sum of 1/N+1…
Step by step
Solved in 2 steps

- The following program sets up a single client/server connection. When the client connects, the server reads any incoming data as text and prints it out one line at a time. If the server receives the string “shutdown”, then it closes the socket and exits. Download this program Download this program into GCC and run the code. Then update your code to allow for the server to manage concurrent connections on the same port. Use IP address 127.0.0.1. Page of 3 ZOOM /* Server code */ #define BUF_SIZE 1024 #define LISTEN_PORT 8080 int main(int argc, char *argv[]) { int sock_listen, sock_recv; int i, addr_size, bytes_received; int incoming_len; int recv_msg_size; struct sockaddr_in my_addr, recv_addr; int select_ret; fd_set readfds; struct timeval timeout={0,0}; struct sockaddr remote_addr; char buf[BUF_SIZE]; /* create socket for listening */ sock_listen = socket(PF_INET, SOCK_STREAM, IPPROTO_TCP); if (sock_listen < 0) { printf("socket() failed\n"); exit(0); } /* make local address…Assume Host C is the owner of a Web server that can be accessed via port 80. Assume that A and B are the concerned web hosts. Is the same Host C socket used to forward each and every request? All of the sockets will utilize port 807 by default if the server employs persistent connections and requests are split across two different sockets. How about a discussion and an argument?Assume Host C has a Web server on port 80. Assume this Web server accepts requests from Host A and B and allows persistent connections. Is Host C sending all requests over the same socket? Do they both have port 80 if they're sent over separate sockets. It's worth discussing.
- On a basic Linux server following services are required Assign a dynamic IP address to a client on interface eth0 Find out the path of the packet to the server on (172.16.10.19), put your system in promiscuous mode. Apply forsetgid and sticky permissions on /home/Ali/programming Rename file present on Desktop from “file.txt” to “newfile.txt” Find out the number of IP addresses used by google.com Display all user accounts and groups in a Ubuntu system Display all files in /opt/ starting with s and have a .txt extension.Step 1: Write a script to find and print your local IP address Use the following code: import socket hostname = socket.gethostname() local_ip = socket.gethostbyname(hostname) print(local_ip) Step 2: Write a script to find and print your OS platform and release (for example, "Windows version 10") Use the following code: import platform print(platform.system ()) print(platform.release ()) Step 3: Write a script to find and print a "ping sweep"? Use the following code: import os my_ip="192.168.10.103" # sub your ip address os.system('ping -n 4 {}'.format(my_ip)) Step 4: Write a script to find and print current day and time import time now = time.localtime() print(time.strftime("%m/%d/%Y %I:%M:%S %p", now)) Extra Credit: Add code to Step#4 which prints a greeting, either "good morning", "good afternoon", "or good evening", depending on the current time.1. Persistent HTTP requires?a. 2(round trip times) + file transmission timeb. as little as two RTT for all the referenced objectsc. one file transmission timed. as little as one RTT for all the referenced objects 2. UDP has no connection between client & server?a. RCVR extracts sender IP address and portb. sender explicitly attaches IP destination address and portc. three other answers are incorrectd. no handshaking before sending data 3. A socket in computer networks is correctly defined as?a. A combination of IP address and port number, connected by a "/" symbolb. sender explicitly attaches IP destination address and portc. RCVR extracts from the socket, sender IP address and portd. A combination of IP address and port number, connected by a"." symbol 4. The data link layer provides?a. the functional and procedural means to transfer data between network entities and the means to detect and possibly correct errors that may occur in the link layer.b. the functional and procedural…
- 14. Which of the following fields in a TCP header is used to determine the available capacity of areceiver in bytes?a. Receive bufferb. Receive windowc. Sender cannot know the available capacity of the receiverd. Congestion windowe. Sliding windowCreate 2 new virtual machines and perform clean installation of CentOS 7 Linux Server with GUI on both machines. Your local Subnet number is Subnet# 192.168.200. ………. /28 The first Linux Server will have the following characteristics: Host Name: linuxsrvXX (where XX is two last digits of student1 number) Static IP Address: For server’s IP Address, use the first number from available range of hosts addresses Connect first Linux Server to Internet Install a DHCP Package from Internet using yum command. Disconnect Linux Server’s Internet access. Set Static IP Address: For DHCP server’s IP Address, use the first number from available range of hosts addresses Create a DHCP Pool for 10 Computers/Client PCs from the given Subnet Number The second linux Computers will have the following characteristics: Host Name: Linuxclient-XX (where XX is two last digits of one student2 number) IP Address: It will obtain IP Address from DHCP ServerLet's pretend Host C is running a Web server on port 80. Suppose this Web server allows both Hosts A and B to make persistent connections. Is it possible that Host C is sending several requests over the same socket? Does port 80 exist in each of these connections if they are being sent through separate sockets? You should discuss and elaborate on this.
- Assume Host C runs a Web server on port 80. Assume that this Web server accepts requests from Hosts A and B and that persistent connections are enabled. Is Host C sending all of the requests through the same socket? Do they both have port 80 if they're broadcast via distinct sockets? It's something you ought to discuss and explain.Assume that Host C's Web server operates on port 80. Assume this Web server allows requests from A and B and persistent connections are enabled. Does Host C deliver all requests using a single socket? If they're broadcast over different sockets, do they both have port 80? It is something you should discuss and clarify.n this assignment, you will develop a simple Web server in Python that is capableof processing only one request. Specifically, your Web server will(i) Create a connection socket when contacted by a client (browser)(ii) Receive the HTTP request from this connection(iii) Parse the request to determine the specific file being requested(iv) Get the requested file from the server’s file system(v) Create an HTTP response message consisting of the requested filepreceded by header lines(vi) Send the response over the TCP connection to the requesting browser.If a browser requests a file that is not present in your server, your server shouldreturn a “404 Not Found” error message.Your job is to code the steps above, run your server, and then test your server bysending requests from browsers running on different hosts. If you run your serveron a host that already has a Web server running on it, then you should use a differentport than port 80 for your Web server. Make sure to test your program…

