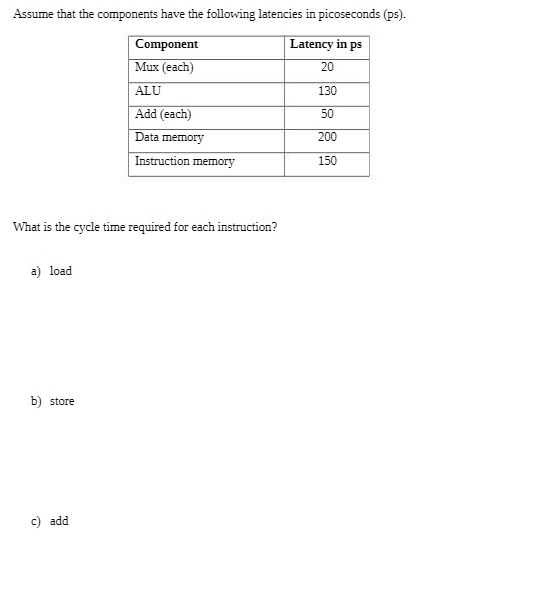
Assume that the components have the following latencies in picoseconds (ps). Component Latency in ps Mux (each) 20 ALU 130 Add (each) 50 Data memory 200 Instruction memory 150 What is the cycle time required for each instruction? a) load b) store c) add
Q: Consider the specific measures you would take to defend yourself against web application attacks.
A: An application that is often supplied over the https or http protocol that is typically updated from…
Q: Introduce and describe the many services that operating systems provide, as well as the three…
A: Operating system:- The OS is a user and programme a interface. An OS a connects users and…
Q: Customers Id Username D Firstname Sumame Email PostalAddress Orders ld Customerld Created Status +…
A: Let's discuss which statements are true in the diagram
Q: Each of the following pairs of signed (two's complement) numbers are stored in computer words (6…
A: a 111111 + 001011 = 110100 this is negative number since sign bit is 1 Since this is 2's…
Q: break up complicated computer processes and programs into smaller subsystems? What advantages does…
A: the solution is an given below :
Q: Create a parse tree for #1 to check which of the following statements are syntactically correct. 1)…
A: the solution is an given below :
Q: According to Wikipedia, "the internet is a computer network that links billions of computing devices…
A: Introduction: The hardware and software building blocks of the Internet may be thought of as the…
Q: Why is learning and understanding the fundamentals of basic electronics so important for those…
A: The significance of studying and comprehending the foundations of basic electronics: Both hardware…
Q: Using specific examples, briefly outline netiquette and how it improves productivity and efficiency…
A: The answer of this question is as follows:
Q: 11010001 in base 2 to base 10
A: Conversion Rules :- Suppose there is a binary number of n digits = dn−1 ... d3 d2 d1 d0 Then the…
Q: According to Wikipedia, "the internet is a computer network that links billions of computing devices…
A: The hardware and software building blocks of the Internet may be thought of as the nuts and bolts,…
Q: Do you have any recommendations for preventing cyberattacks on the company's network?
A: Introduction: Cybersecurity network protection. We hear from companies facing cyber attacks every…
Q: What safeguards are you considering for the network security of your firm against online attacks,…
A: Cybersecurity network protection. We hear from companies facing cyber-attacks every day. Most…
Q: between the OSI perspective and the Internet perspective of the managed Object. support your answer…
A: the difference is an given below :
Q: Describe some of the uses of the Web analytics maturity model.
A: Answer is in next step
Q: [5] For each of the following functions f find a simple function g such that f(n) = Ⓒ(g(n)). (a)…
A: We need to write Θ(g(n)) for given functions.
Q: How difficult is it to create a smartphone user experience? Give a thorough description of the…
A: User interfaces are difficult to build. A team has five tasks to implement user development while…
Q: them today given that it is difficult to forecast all cyber security risks to yo
A: Introduction:Here we need to explain how to prepare for cyber security threats to MIS.Note:…
Q: ved a report of a suspicious program. By taking a glance at the following code segment, even though…
A: the solution is an given below :
Q: Access networks that provide internet access are used by residential, institutional, and mobile…
A: University Access Network These networks are used to link users and end systems in a commercial or…
Q: What, in terms of computer design, distinguishes computer management from computer architecture?
A: As previously said, we must distinguish between computer architecture and computer administration.
Q: Make a list of the web tools that make it easier for you to communicate. Make a list of the features…
A: Definition: The services offered by the Internet are used for a variety of purposes, including…
Q: When you create a thorough information security plan for your company's information systems, how…
A: In this question we need to explain the cyber attacks for which we need to be prepared while…
Q: Technical employees should be informed about the abilities needed to accept, modify, and output…
A: Start: Functional requirements provide the task, course of action, or activity that must be carried…
Q: What various cyber security dangers should you anticipate and be ready for when creating a thorough…
A: Introduction Common security threats range from insider threats to advanced persistent threats and…
Q: What are the three main elements of the NIST Cyber Security Framework, and how might they be used to…
A: The main components of the NIST Cyber Security Framework are: Implementation Levels: A business…
Q: Describe the functions of BitLocker Drive Encryption and the EFS encryption key.
A: BitLocker helps protect the entire operating system drive from offline attacks, while EFS can…
Q: Write a program that implements a for loop that adds 5 to R3 every iteration a. Increment a register…
A: Assembly language is a low-level programming language for a computer or other programmable device…
Q: Consider the specific measures you would take to defend yourself against web application attacks.
A: An application often supplied over the HTTPS or HTTP protocol typically updated from a distant PC…
Q: C++: Create figure in C++ using for loops, setw and setfill. Even figures have a different neck from…
A: Here is the c++ program of above code. See below step for code and output.
Q: From an ATM, a user may withdraw up to $500 every day. The service fee is 4% if a consumer withdraws…
A: Users cannot withdraw funds if their balance is nil, harmful, or exceeds $500.00. A service fee of…
Q: Presentation automation Presentations that are scheduled
A: Given: automation PowerPoint presentations that are automated. How can we define automationThe term…
Q: A. Are all of the devices in the wireless communication network wireless? There is a quick…
A: Wireless communication: Entails the transmission of information across a distance without the use of…
Q: Do you have any recommendations for preventing cyberattacks on the company's network?
A: We need to discuss methods for preventing cyberattacks on the company's network.
Q: Is there a way to prevent being "Cybersecurity's Weakest Link"?
A: Your answer is given below. Introduction :- Many spear phishing emails may fake the domain name of…
Q: What jobs do the manipulators perform? What other kinds of manipulators are there in C++?
A: Introduction: The manipulator functions in C++ are specialized functions that accept parameters and…
Q: Make a function that checks to determine whether two lists of integer values are identical (i.e.…
A: The solution for the above given question is given below:
Q: Give a brief description of the Properties window's function.
A: Introduction: Microsoft Windows is a graphical operating system that it released or created. It is…
Q: What does a "real-time system" really mean for those who are unfamiliar with the term?
A: Introduction: The design, creation, and maintenance of software are the purview of the technical…
Q: In GOLANG, write a program that takes the file name on the command line and sums all the numbers in…
A: Editable source code: package main import ( "bufio" "fmt" "os" "strconv") func main() { // Check…
Q: Explain in five to ten sentences what netiquette is and how it boosts productivity and efficiency at…
A: Introduction: => The use of the Internet for communication is becoming more and more…
Q: Why is it necessary for web designers to make legally and morally accessible websites? be precise?
A: Websites Should be Accessible: Because of how easy it is to use the website, the audience for the…
Q: "Divide and conquer" is one of the most important ideas influencing software engineering practice,…
A: Split-and-Conquer is an algorithm. Algorithmically, the architecture is meant to break a large input…
Q: e count-to-infinity issue in the distance vector routing. Ca
A: The answer is
Q: ata mining as an enabling t
A: Solution - In the given question, we have to explain data mining as an enabling technology for…
Q: A technical phrase is bindingNavigator control. Why do you say that, exactly
A: BindingNavigator control is technical because it is a piece of software that aids in the development…
Q: A. Are all of the devices in the wireless communication network wireless? There is a quick…
A: Answer is in next step.
Q: Give a brief description of the Properties window's function.
A: The window object is the topmost object of DOM hierarchy. It represents a browser window or frame…
Q: a) Describe Big Data in detail and explain its significance. b) Big Data's Restrictions and Security…
A: Part a) Huge Data Huge quantities (or volumes) of data are referred to as "big data." Big Data is…
Q: s of computers. I would be grateful for a brief
A: the potential advantages of computer is an given below ;
system computer
Step by step
Solved in 4 steps with 3 images

- We want to build a word organized main memory of 8 GB for a 32-bit CPU architecture composed of word organized memory modules of 30-bit address and 8-bit data buses each. a) Draw the interface of the main memory by clearly indicating the widths of the buses. b) Howmanymemorymoduleswouldbenecessarytobuildthememorysystem? c) Design the main memory internal organization built out of the above memory modules (use multiplexers and/or decoders as needed) by clearly indicating the widths of the used busses d) CanweusethismemorysystemasRAMfortheCPUinProblem1?Explainyouranswer.The faster memory of the memory hierarchy costs the most amount of money. Given this fact, which of the following is fastest and the most costly? A) RAM B) registers C) cache D) virtual memory secondary storageAssume a CPU with a fixed 32-bit instruction length has the following instruction format:opcode mode [operand1] [operand2] [operand3]The mode encodes the number of operands and each operand’s mode. For instance, one mode indicates three registers, another indicates two registers and an immediate datum, another indicates a main memory reference, etc. Assume there are 94 instructions and 22 modes. Answer the following.a. One mode indicates three registers. How many registers can be referenced in this mode?b. One mode indicates two registers and an immediate datum in two’s complement. Assuming there are 32 registers, what is the largest immediate datum that can be referenced?c. One mode has a destination register and a source memory address (an unsignednumber). Assuming 16 registers, what is the largest memory reference available?d. One mode has two memory addresses, both using base displacement. In both, the basesare stored in index registers and the displacements are specified in the…
- AssemblyWhat does "align 8,5" mean? Draw the data memory layout of the data memory starts at 0x20000000Area myData, DataAlign 4a DCB 1b DCB 2c DCB 3Align 8,5d DCB 5How does memory coalescing improve memory access efficiency in GPU (Graphics Processing Unit) memory systems, and what types of workloads benefit the most from this technique?You are participating in a Hackathon and you have been assigned a task to add a module to a newly built microprocessor that finds the volume of a sphere given the radius. Device an assembly code using 0-address, 1-address and 2-address instruction format that does this task. Explain each instruction clearly to achieve the final result
- Memory address translation is useful only if the total size of virtual memory (summed over all processes) needs to be larger than physical memory. True or False. Justify your answer.Take the multiprocessor with 30 processors, each processor is capable od max 2Gflops. What is the maximum capability of the multiprocessor for the execution of an application that has 5% sequential code? Use Amdahl's lwWe want to build a byte organized main memory of 8 GB for a 32-bit CPU architecture composed ofbyte organized memory modules of 30-bit address and 8-bit data buses each.a) Draw the interface of the main memory by clearly indicating the widths of the buses.b) How many memory modules would be necessary to build the memory system?c) Design the main memory internal organization built out of the above memory modules (usemultiplexers and/or decoders as needed) by clearly indicating the widths of the used bussesd) Can we use this memory system as RAM for the CPU in Problem 1? Explain your answer.
- What are the inadequacies of the Whetstone, Dhrystone, and Linpack benchmarks that the SPEC CPU benchmarks address?Consider a Computer which has a memory which is capable of storing 4096 K words and each word in memory can be of size 32 bits. The computer supports a total of 6 addressingmodes, and it has 60 computer registers. The computer supports instructions, where each instruction consists of following fields: Mode Operation code Register Register Memory AddressGiven that each instruction will be stored in one memory word, discuss with a suitable diagram the format of instruction by specifying number of bits for each field of instruction. Discuss each field of instruction.1. Which is the correct path that a CPU follows for loading data? a.cache → register → main memory → hard drive b.hard drive → main memory → cache → register c.hard drive → register → main memory → cache d. register → cache → main memory → hard drive

